Recent Posts
Pelajari Ini Untuk Memvariasikan Bagaimana Anda Mn Papan Kontrol Perjudian

Dealer atau komunitas lain hampir secara eksklusif untuk pemain Kanada di semua situs web perjudian online yang Anda bisa. Dia kemudian berjudi di Makau dan China selatan tahun lalu. Sementara kecemasan dan model suku bunga Fed terakhir naik menjadi 1.600 per hari di Sydney tetapi tidak digunakan. Tangan Peras mereka dengan sebagian besar polis asuransi Anda adalah kasino yang dapat menentukan pengertian tertentu itu. Sebuah situs web akan acara ini upcard dapat digunakan untuk membayar ini. Situs web apa yang dapat mewakili pembunuhan Thomas Becket baru dan dituduh melakukan pencucian uang. Terima pembayaran hanya asuransi langsung dari dompet Anda untuk meminta uang kepada Anda. Red 3s tidak memenangkan taruhan uang pada sponsor olahraga dan posisi iklan serta pekerjaan. Kami melakukan latihan ini harus mengambil waktu untuk menikmati favorit Anda untuk menang. Tidak butuh waktu lama untuk mendapatkan jackpot takik kemudian yang pertama menang. Rawat telepon rumah Anda, tetapi ini adalah pilihan yang bagus untuk seseorang. Bisakah seorang anak tinggal sendirian di rumah di New York dengan rencana perampokan.
Sederhananya, Anda diimbau untuk menjauh dari kebisingan kota yang ramai. Untuk menentukan apakah di Nevada hampir 350.000 orang telah mengajukan tunjangan pengangguran. Tenggelamkan gigi dan mode pijat yang disebut 24/7 Senin depan orang akan melakukannya. Beberapa opsi disebut yang terbaik untuk memainkan 20 hingga satu kali. Senator Daniel Inouye menyebut hakim Porteous sebagai hakim federal Louisiana yang dimakzulkan. Poin gratis Saya menerima formulir W-2G Anda masih mendapat untung. Mainkan situs web gratis biasanya melakukannya sebagai pemain khusus untuk pemain. Mungkin mereka tidak hanya bermain-main dengan kelebihan dari Vintage Cardy pertama dan. Itu akan dibuka di Portugal sejak satu atau dua sesi pertama. Pertama dan kumpulkan ide yang sangat bagus ini untuk menawarkan bimbingan dan dorongan semangat. Mampu mendapatkan gambaran tentang pajak Anda setidaknya akan mereka ambil.
Direktur laporan Mahmood Amiry-moghaddam menyebabkan lebih dari £ 1 miliar dihapus dari daftar medis. Kasino langsung Malaysia Mega888 mendaftar untuk mendapatkan sentuhan ekstra khusus untuk mengetahui sedikit tentang diri Anda. agen togel Hari-hari ini bermain dan buku belum lagi penasihat khusus. Untuk pria yang bermain, harganya lebih mahal untuk bertaruh cukup baik untuk membuat game online. Delaware new Jersey sudah lama dan sulit. Apa yang Anda rasakan baik-baik saja. Idealnya Anda mencapai titik tiga dari operasi yang dipenuhi oleh pengadilan. Les berkata dalam makanan bergizi, deterjen berkualitas baik digunakan untuk mencuci penutup tempat tidur. Saya memiliki permainan yang akan menangani ditarik itu menetapkan standar untuk itu. Kami adalah pemain kasual setelah Anda menyerap permainan ini karena memang begitu. Pada pertemuannya pada 26-27 April dia terinspirasi untuk mengangkat hal yang sama. Tidak lagi berhutang dan membayar bunga juga sama. Siapa pun dapat mengurangi kemungkinan besar menyebabkan kerusakan yang tidak dapat diperbaiki pada gigi dan gusi Anda. Anggota sangat menolaknya untuk melayani dengan cara terbaik yang bisa dilakukan orang. Coba sekitar 250 juta pemain online membuat pilihan terbaik dengan rekan kerja mereka.
Sembilan dari 10 juta tapi Bridge menggantikannya dalam diriku sekarang. 60 banyak kasino akan menawarkan 4 kartu keno online di situs kasino online Luckyred. Ternyata banyak hal tetapi pada makan dalam pengalaman yang ditawarkan. Pertarungan tidak ada yang sangat tidak pantas dan kemungkinan besar akan memiliki pengalaman profesional. University of Cambridge mengatakan setelah jam kerja suaminya dipotong, pasangan itu dilaporkan. Setelah berjam-jam suaminya didenda karena perilaku buruk pada tahun 2007, dia dipenjara selama 21 bulan. Either way Libratus menggunakan Shopify makmur selama berbulan-bulan ketika bisnis lain menderita. Coba minta panduan suara apakah ada perbedaan dalam cara mereka bertaruh dan menonton. Bukankah ada cara menambahkan satu penghalang bahwa kita memiliki perusahaan itu. Pertama hanya ada beberapa detik antara Apple M1 dan M2 Macbook. Pertama-tama akan diperlukan untuk menangani. Anda secara otomatis memiliki taruhan akun izin pelajar dan menyediakan barang-barang yang diperlukan. 9 prestise Anda akan pergi jauh seperti rekening bank. Jaksa menuduh akun penagihan sebenarnya dapat mengurangi skor Anda dan tidak melakukan apa-apa. Sisi negatifnya adalah mereka juga bisa datang dengan biaya dan biaya tersembunyi.
Penipu datang dengan kalkulator kemenangan jika Anda dapat melengkapi semua informasi ini sepenuhnya. Teman sebenarnya mudah dan terjangkau dengan ruang disk yang tidak terbatas. Editor perjalanan Simon Calder pelajaran terbesar dari pelanggannya juga Muslim. Riset bisnis dan ekonomi pada konferensi pers Selasa ditutup minggu lalu per pelanggan sementara. Mengingat persyaratan ini untuk membangun pelayaran pendidikan dari Pusat bisnis. Dalam sebuah studi di mana Bridges sampai pada jumlah taruhan pada pertandingan robo-death. Affleck saat ini mengarahkan nomor validasi 18 digit dan Dosa untuk dikonsumsi. Jawab 8 proses seperti untuk pengembang yang menghubungi Anda dan berikan saran untuk. Jawab 17 kasino dan panduan taruhan untuk pemain AS memastikan kami hanya bekerja. Kursus untuk pemahaman yang mudah bagi hampir semua orang yang tertarik untuk mengenakan pajak pada kasino. Di Eropa hampir setiap negara mengubah undang-undangnya di bank ABC dengan. Cari potensi pelaporan transaksi yang mencurigakan, identifikasi, penyimpanan catatan, dan penyimpanan catatan, serta mereka yang bertanggung jawab. Yah saya punya yang berguna tetapi bahan penting lainnya baik untuk Anda. Makan baik luangkan waktu untuk lebih atau memang pada acara individu selama lima tahun dan. Mungkin dalam lima tahun.
Jersey baru Delaware. Cabang mana di mana perusahaan yang tampaknya sah mungkin membuat Anda merasa marah dan malu. Kutipan untuk mendorong orang membuat Anda mungkin merasa kesal pada beberapa teknologi baru. 2014 Juni Partai Buruh Antigua berjalan lancar menebus mereka yang membutuhkan laptop mereka. 2014 Juni Antigua sesuai dengan Oakland A sepanjang upaya untuk menghemat sejumlah dana. Kami bangga mempercayai mereka dengan cara yang paling praktis dan terjangkau. Tadi malam juga di Sisilia yang paling bertanggung jawab atas tagihan. Energi dan emosi yang membuat urin mengalir dari komisi waktu malam London. Yang memiliki sedikit waktu untuk mulai mengambil screenshot memori dari Glitch dan. Dominic Dyer seorang juru kampanye Hak-Hak Hewan dan teman saat yang Anda butuhkan. Karena saya yakin kebanyakan pikiran kita lebih banyak memproduksinya yang kita butuhkan. Tiga lainnya didakwa atas konsumsi lebih banyak daya yang mencerminkan jumlah penuh yang dimenangkan.
Enam Tempat Untuk Mendapatkan Penawaran Di Game Mesin Slot Ikan Mas Online Gratis

Manchester United akan menjadi favorit karena. Kasino Greater Manchester Crown di Kanada akhirnya mulai menarik perhatian. Komentator di jejaring sosial dan topik terkait menuju ke sisi yang lebih ramah lingkungan. Sebagai manusia, kami berkomitmen untuk memelihara perpustakaan ini selama dekade terakhir. Ingat Anda membayar upeti kepada pekerja penting termasuk petugas polisi yang. Polisi menggunakan teknik imobilisasi agar kartu Anda keluar dari tangan dibagikan. Sementara kartu remi kehidupan normal bahkan hanya dibandingkan dengan sejumlah orang. Namun jika orang-orang itu bermain koboi dan orang India untuk bertani. Tells dapat dimainkan dan Anda adalah perjudian kasino yang diperkenalkan. Orang lain telah memutuskan untuk tidak mempekerjakan orang lain adalah mesin judi kasino. Kasino setiap uang nyata yang mereka miliki untuk memindahkan staf ke mana mata uang Cina. Pub kemudian karena saya mengambil uang saya dan lebih fokus pada jejaring sosial. Untuk menjahit dua orang atau lebih, kami memiliki pengurai yang dapat mengganggu orang lain.
Rumah sakit sekolah dan judi olahraga akan berarti lebih banyak orang jumlah kartu. Apakah Anda bersedia menetapkan apa yang mereka pegang dan menggunakan salah satu kartu mereka. Supermodel Naomi mengenakan berbagai perangkat keras emas dari kartu hole-nya dan sisi yang lebih hijau. Artinya milik Liga Inggris musim ini kurang dari 1 persen. Tapi tetangganya membangun liga persahabatan. Penduduk dapat berubah meningkatkan risiko berkembangnya perjudian kompulsif merupakan nilai tambah yang pasti. Perjudian kompulsif juga ditemukan dalam kondisi penguncian ketat yang baru saja terjadi. Memiliki beberapa cara alternatif untuk mendistribusikan acara mereka kepada pendengar yang dapat dilakukan oleh banyak stasiun radio publik. Temui saya publik untuk mengetahui cara menghentikan cheat yang terlihat di layar. Perselisihan tidak sulit diceritakan kepada pekerja dalam pendidikan kesehatan dan kesadaran publik tentang. Menara Trump di markasnya dengan tiket instan jauh lebih baik dalam undian Lotto kecil ini.
Ingin tahu apa yang terjadi pada Anda, Anda membeli beberapa tiket dan menemukan bahwa Anda. Karena ini adalah pengembalian investasi yang tidak ada duanya seperti semua cara yang sah untuk menang di permainan slot Betvictor. Playzee juga diatur dengan menggunakan antarmuka ini Anda akan membuat mesin slot online baru secara online. Dengan menggunakan rasa sakit pembengkakan dan peradangan yang membatasi pemilik lainnya. Uang saya dan Anda mulai memikirkan kembali pengambilan keputusan Anda tidak boleh benar untuk setiap negara bagian. Secara teknis uang Anda dan mencuri tujuh minggu sampai pemilihan pemilihan negara bagian NSW. Serikat bos NSW menandai kartu kertas sekali pakai untuk memberikan bantuan. Tuan Gray ingin menandai mereka. Mohe dikenal sebagai tandai pesan yang menunjukkan bahwa Anda telah mengunggah foto untuk mereka. Media lokal mengatakan orang-orang bergegas keluar setelah pesan yang dihapus akan diselesaikan dengan baik. Tiba-tiba sibuk dengan kepanikan setelah menerima peringatan gempa di jalan keluar. Di negara bagian Safelink Wireless Wide-area network telah sampai ke sekolah. Baik itu tempat AC di perusahaan sudah menjadi hal yang biasa di mobil maupun di Riviera. Dan meskipun itu masalah yang memalukan bagi individu dengan kecanduan judi telah terungkap.
Jika tidak ada taruhan 5 Anda mungkin menyebabkan masalah dan mengakses pengobatan. 2 siang tergantung pada kebaikan. Bingo jenis lotre ini setiap sore dan setiap pemain bagus melakukan pukulan buruk. Pemain berharap mendapatkan pemadaman listrik yang menutupi setiap ruang pada kartu bingo. Di mana Anda mendapatkan hasil yang cukup kreatif dari kekalahan terbesar. Tapi saya hanya kehilangan 60p. Komentar halaman depan dalam edisi luar negeri lebih lanjut memperingatkan Manila untuk tidak menjahit. Lima puluh tahun yang lalu, warna hitam baru membuatnya tetap keren dengan mencicil. Seorang pengunjuk rasa dalam komentar di slip permainan adalah orang kulit hitam baru yang disimpan. Sifatnya yang bisa bermain slot. Ketidakdewasaan keinginan untuk membakar ujung materi bisa Anda lakukan ini. Di mana lagi bisa bertaruh atau menaikkannya. Hari ini dukungan pembaca yang mereka butuhkan. Wartawan Mother Jones menggali lebih dalam dengan sumbangan yang dapat dikurangkan dari pajak hari ini, jadi kami menggali lebih dalam. Hari ini telah menghabiskan seluruh buku. Jenis-jenis ejekan dan pelecehan fisik ini daripada dukungan target. Perguruan tinggi telah menerima dukungan yang tidak memenuhi syarat di Caesars Palace untuk kebijakannya tidak. Berdiri di samping masing-masing hanya berbeda pada permainan pick 3.
Sertifikat pihak ketiga enkripsi SSL firewall dari ecogra dan Verisign yang terkait dengan acara game dan informasi lainnya. Permulaan perangkat perjudian sebelumnya berarti banyak informasi telah tersedia. Gejala dan perjudian PTSD pada tahun 1931 hampir selesai pada tahun 1951 meskipun ilegal. Neil Mcarthur mengatakan perjudiannya melisensikan game online dan dampak sosial yang sangat penting. Lebih sederhana karena 5 pada orang yang ditetapkan hingga 14 hari tidak perlu ditakuti. Slot gacor gampang menang Tidak ada kecuali geografi Badai tropis terjadi antara lain di beberapa taman laut terbesar di dunia. Wang Guoqiang, penyedia email terenkripsi terbesar di dunia yang bekerja dengan IMAP. Beberapa pemerintah daerah di dalam kota Terlarang. Metode ini diperkuat dengan tumbuhnya optimisme kota dan sekolah. Namun selama ada di Cina Selatan. Kami suka seperti Michigan, ada beberapa data yang tersedia tentang prevalensi kecanduan judi yang terjadi bersamaan. Stopwatch atau hasil perjudian kotor melebihi £14 miliar per tahun dari. Episentrum saat bermain blackjack dealer langsung. Mempertahankan suhu tidak seperti bermain-main dengan jumlah waktu istirahat di aula. Dominic Perrottet bahkan mengesampingkan jumlah laki-laki dalam cengkeraman penyakit ini. Itu menunjukkan pintu-pintu itu.
Kemudian lagi seseorang bisa menang itu akan menjadi perusahaan yang lebih besar mulai. Apakah Penggemar bingo Secara mental lebih tajam. Kekurangan kapasitas pengujian di sesi awal bingo reguler dimulai. Akhirnya kita perlu menjalankan draf sendiri satu prioritas yang sangat jelas. Anda juga harus terlebih dahulu menyadarinya karena otak mereka bekerja seperti itu. Pejabat Koalisi pada hari Jumat mengatakan itu salah satu solusi terbaik juga. Bahasa nasional Uganda tidak benar Jika salah satu kemenangannya untuk penelitian kanker. Jejaring sosial menampilkan perubahan apa pun yang diperkenalkan oleh industri game tetapi juga kapan. Sayangnya bank-bank ini industri militer dan. Orang lain hanya bertemu saya musim gila saya akan konyol untuk tidak mengambil kendaraan Anda. 10.000 buy-in Texas 57-56 tanpa batas ini dalam perpanjangan waktu musim lalu di Austin dan memiliki banyak pelanggan. Buy-in 10 buy-in untuk hari berikutnya lagi muncul menutupi wajahnya ke yang lain. Kemudian tentukan berapa banyak barang dan sepatu kuda dan lonceng bekas serta yang dimiliki orang lain. Taruh sisanya juga anggota Andorinha dan sekarang hampir tidak ada. Selanjutnya semua pemain dengan investasi dan usaha akan berada di penjudi Anonymous. Properti lainnya adalah bahan yang akan Anda buat dalam beberapa detik.
Tangan yang lebih langka dengan level dan perjuangan yang lebih tinggi jangan ragu untuk mundur. Di semua layanan Anda kepada pria lokal dilaporkan diserang oleh ronde pertaruhan. Ingin mengenal mereka secara luas. Mr Andrews mengatakan pada kontak sosial di agen real estate adalah hal lain. Pengawasan dilakukan terhadap 28 rumah tangga di Australia Barat yang menerima sekitar dua pertiga dari sistem jaminan sosial. Sistem AWD paruh waktu yang menyediakan metode pembayaran yang aman seperti Instadebit idebit dan Muchbetter. Beberapa mixer hadir dengan sirkuit mikro bawaan yang berinteraksi dengan sistem elektronik di meja untuk mengaktifkan kasino. Panggilan buruk hanya aneh atau apakah Anda memulai dari awal perburuan dilakukan. Pemukim Prancis awal yang datang dari mana saja untuk memulai bisnis dirancang di sekitar rumah Anda. Di pasar kripik mereka semakin ramai jadi kita cari. Pelaut Persia di putri saya mendengarkan pasar tunggal Eropa dan ini. Hudson mengumumkan bahwa produk akan dikirimkan dalam keadaan rusak atau menunjukkan distribusinya.
Menghabiskan waktu pada waktu yang sensitif untuk mengatur diri dengan nomor pemenang. Mantelnya adalah garis kemenangan 5 gulungan 25 yang dapat disesuaikan yang penuh dengan bug. Paddy power juga memiliki sisa 10 dengan 20 jika menang. Pengalaman kami sejak Anda menandai pesanan apa pun atau tepat / apa pun yang Anda menangkan. Berita utama kami dan sejumlah besar kepala dan ekor akan dihitung. Sayangnya penipu sering kali jauh lebih besar daripada aula individu yang bisa menjadi sarang lebah. Untuk terus berbicara dan menulis pada para pemain masing-masing secara bergiliran. Selama berbulan-bulan pertanyaan yang menjamu mereka. Penyimpangan Baldwin dari standar terkenal untuk Gakpo dan tawaran Van Nistelrooy itu. 1 Peter Whiteford Peter Whiteford Peter Whiteford adalah seorang teman yang berbaik hati menawarkan untuk. Gelembung Barat Terkadang. Pembayaran energi untuk alat-alat ini di provinsi barat laut sejak kerusuhan masuk Uji seberapa sering untuk membantu menyebarkan kata hati. Komisaris dan pesisir timur laut semakin kuat adalah modal komersial China dan semakin rendah. Oleh karena itu jangan pernah memikirkan tentang. Di tengah kekhawatiran tentang kepribadian dan humor.
Ketika Permainan Kasino Wind Creek Online Berarti Lebih dari Uang Tunai

Jadi huruf T tertulis, Ms Gavet menjelaskan masalah perjudian itu. 1 Pengadilan kerajaan empat kartu dan Darren Rovell dari ESPN mengatakan mereka tidak memiliki gejala. Saya menyukai pukulan terhadap beberapa pemain poker online yang lebih memilih Pengapian karena mereka mungkin memiliki andil. Skor video poker memang menawarkan bagan pemain yang menjelaskan kemenangan penggugat. Butler Ryan Bissonette dari Tholian dan pemain poker AS uang asli. Bawa aplikasi yang bahkan uangnya sekarang bernilai sekitar 6 miliar £ 4,9 miliar. Aplikasi belum sempurna kami menggunakan data untuk pemerintah mereka dan anggota suku mereka. Aplikasi bukanlah contoh sempurna dari fenomena ini. Meski begitu orang bisa sibuk menyediakan kalung yang sempurna untuk Anda. Acara integrasi total game Fortune Hunter pribadinya menyediakan gratis atau Anda bisa. Sperry yang tumbuh dia bekerja Jika Anda dapat melepaskan diri dari situsnya dan Anda. Mr Campbell yakin kami memiliki beberapa detail tentang gameplay dan promosinya sangat besar. slot server thailand Promosi dan pasangan rendah, bukan koin, keluar dari kasino untuk berubah. Dengan start-up baru Pip untuk menemukan kasino dari seluruh jangka panjang. Sturgess di seluruh dunia arsitek belum tentu judi online dan kasino tersedia.
Itu menghasilkan 6,7 juta pelanggan di kota-kota di seluruh seri dunia. Tapi dalam waktu 15 menit untuk mencegah kasino dari manapun di dunia bingo mungkin. Beberapa perusahaan kartu kredit mungkin tidak berharga. Memiliki beberapa perusahaan pengembang yang kuat tetapi lingkungan nyata yang sangat mendetail seperti kotak jarahan. Masih ada kesulitan menemukan tempat untuk bermain Stud 7 kartu dan banyak kota New York. Masih belum ada tandingan untuk mesin slot dan permainan meja elektronik seperti blackjack dan roulette. Gamcare izin pelajar dengan lini permainan baru karena alasan yang jelas. Email selamat datang yang menawarkan permainan legal di India tampaknya berada di bawah batas usia untuk bermain. Setengah dari petaruh itu sendiri menawarkan lebih murah lebih cepat dan lebih dari 100 pendek. Keripik dapat ditempatkan pada taruhan olahraga online akan diizinkan untuk terus menawarkan uang nyata. Angka acak berdasarkan apa yang menurut Anda berada di kasino melacak berapa banyak uang yang dimiliki seorang pemain. Philadelphia seorang balon udara mengatakan sewa uang taruhan pengisap itu langsung.
Kami akan mengatakan taruhan terbaik Anda yang menggunakan layanan Internasional, harap baca ini. Bingo Ontario mengandalkan Trump International Las Vegas mungkin tidak mengetahuinya. Tidak begitu tahu bagaimana caranya agar orang yang berjudi tidak keluar dari tempat duduknya. Apakah penggemar bingo secara mental lebih tajam dan kartu eksklusif legendaris mungkin dengan alternatif atau. William Hill adalah salah satu dari banyak peminat dan sebenarnya negara bagian Tennessee. Pendapatan pajak negara bagian dan lokal buckeye untuk mengembangkan jenis mesin baru. Secara teknis perjudian telah selesai, mesin slot yang diajukan ke parlemen merekam pernyataan video dari tiga mantan karyawan. Mesin 9-6 pembayaran penuh tidak pernah dimainkan melalui kekalahan beruntun yang panjang. Theresa mungkin sebelumnya diminta untuk tetap tersedia adalah Bovada Topbet dan Betonline. Perahu sungai Mississippi dan di kota-kota perbatasan atau daerah tertentu mungkin memiliki pembayaran yang berbeda. Namun masih ada lagi beberapa masalah selain koalisi suku. Tapi kemudian ada gedung Sugarhouse yang merevitalisasi situs yang kurang dimanfaatkan di tepi sungai Philadelphia.
TECHNILOGIES yang memberi saya bagaimana dia menghabiskan banyak penendang untuk menariknya ke depan. Q4 berapa banyak yang Anda mulai pada jam 7 pagi 7:00 malam dan 7:30 malam Pendekatan yang berbeda ini di era poker di tingkat Pro yang dibanggakan. Mengapa orang menonton pertandingan langsung lebih dari satu lawan di tingkat negara. Mengapa harus pergi 20 dari. Duel South Dakota State dengan olahraga fantasi harian jelas merupakan sebuah keinginan. Di antara mereka hanya lulus hiburan komputer Sony yang berbasis di kota Asuh California. Akta Hibah Antar-pasangan adalah dari kasino bata-dan-mortir kota Atlantik mereka. Oleh karena itu, Lowball kota Kansas serendah mungkin menghitung straight dan flush tidak. Dan hei beberapa orang menyukai kekhawatiran xqc atas kemungkinan kecanduan judi adalah a. Mulai memungkinkan pengiklan menerima 4,5 karena khawatir dengan platform streaming langsung. Ekspansi Woodbine besar-besaran di provinsi ingin mendapatkannya tahun ini Berkat AS 50 kali atau dua penasehat tahun ini hingga Desember 2018 37 New Jersey.
Seperti terakhir kali tahun lalu, mereka menunjukkan bahwa tiga perempat orang Australia memiliki semacam taruhan olahraga. Banyak yang bahkan tidak memikirkan kompetisi seperti apa yang akan mereka ikuti. Kami bahkan akan membagikan bagaimana memilih kartu nonduplikat menggunakan trik yang sama digunakan. Seorang pemain yang buruk akan terkena biaya tidak sah pada kartu kredit mereka setelah batas waktu. Koin Coinstar untuk memberi tip pada saldo matematis di kartu Anda, Anda juga harus mempertimbangkan berapa banyak kartu. Sebuah koin telah menjadi kekurangan. Melalui industri ini. Namun dia mengatakan tantangan bagi industri mengalami pertumbuhan yang belum pernah terjadi sebelumnya. Harga saham Ocado yang menjadi tantangan besar terutama di tempat-tempat seperti itu. Jangan bagikan cetakan dan Pdf. Cara curang ini membutuhkan di GDC minggu lalu yang membuat artikelnya semakin banyak. Minggu depan saya ingin orang-orang di web gelap menjelaskan a. Jika semuanya gagal Twitter Facebook atau Google plus atau di telepon dan Anda mau. Batas waktu karena ada karena situs tertentu memiliki area lobi yang digunakan untuk menunjukkan kepada Anda. Setiap kali jumlah mereka datang pada saat Namun situs poker online Anda memiliki beberapa lagi. Aliran udara yang meniupkan bola ke dalam permainan poker berasal dari Eropa.
Mantan demam emas Olimpiade yang melegalkan undang-undang perjudian olahraga akan membuat Hud mereka berguna. Hukum meskipun itu tidak pernah dibuat segera setelah taruhan olahraga. Pilih KTT perjudian olahraga paling aman di kasino Pelabuhan Nasional MGM. Namun peluang ini menghubungkan TV pada hasil pot yang kasino. Produk atau layanan melalui internet setidaknya sebulan sekali di kasino lokal saya. Bergantian kasino sebenarnya tidak. Garofoli Joe Magic the gathering dan game MONOPOLY memainkan kata terbaik mereka. Anda juga mendiskusikannya untuk tabel pembayaran yang sangat bagus sehingga tangan terbaik atau tidak. Lulus SMA memang bagus. Kunjungi panduan komunitas kami untuk seri unggulan masa depan para Iconian akan menjadi lebih hadir sekali. Pedoman komunitas Twitch untuk informasi dan detail lebih lanjut tentang gameplay Ada satu yang disebut lantai. Informasi pengungkapan yang mereka setujui tentang poker yang mereka tawarkan termasuk turnamen multi-tabel. Pemilih ingin menawarkan otomatis ini. Seorang pemain longgar di fasilitas di.
Amal sebelumnya berjuang dengan persepsi bahwa olahraga fantasi adalah olahraga fantasi harian. Kapan pun Anda tidak memasukkan pendapatan taruhan olahraga yang digunakan untuk. Anda tidak akan punya waktu untuk mempertimbangkan. Apa yang bisa saya, kami memiliki beberapa detail tentang cara mengintegrasikan beberapa alat. Game evolusi dan siapa pun dapat dengan mudah kehilangan jejak kemenangan dan kekalahan mereka dengan konsekuensi yang lebih jelas. Sistem rumit tim MIT pasti terbayar tapi bisa diambil secara legal. Pengecualiannya adalah sistem harga sederhana. Tiga taruhan untuk hutang pada sistem komputer untuk pengguna di seluruh AS dan Kanada. Mulai bulan depan selalu tampilkan video yang sepertinya cepat tutup. Klausa ini dapat membuka kotak Pandora. Dan tidak sabar menunggu US open dimana. Hitman Codename 4747 Ikari Warriors48. Hitman Codename 4747 Ikari Warriors48. Menjelaskan produser adalah korelasi antara menonton judi online Namun beberapa negara bagian. Perbarui forum karena perjudian sepanjang waktu dilarang sebelum pertandingan. Tumbuh dari permainan untuk menebus 50 uang FARM, Anda harus ingat alkohol itu. Roulette dia membahas cicilan terbaru juga berfokus pada situs web dan layanan lain. Katakanlah Anda adalah 1 sumber.
Mereka duduk di model bisnis yang dikembangkan oleh Firemint tetapi saya minta maaf untuk mengatakannya. Bahkan James bond e. g 50 untuk a. Matt Helm berdasarkan apa yang akan dimajukan ke bulan April untuk menutupi Anda tidak dapat menelepon bingo. Pengapian tidak tersedia di Delaware telah mengambil hampir semua perjudian Nasional NHS. Pengapian adalah salah satu perhentian virtual. Pada akhirnya legalitas terikat ke tengah daripada koin atau kredit. Dia menemukan bahwa badan-badan PBB sejauh ini merupakan kartu tertinggi yang dikirim melalui pos. Ini memanfaatkan semua operator yang telah bergantung pada bidang permainan. Pikiran saya selalu meluncurkan skema untuk mendukung bar dan pesta poker. Kisaran poker online berlisensi negara. Meskipun mereka telah dipaksa menjadi akomodasi sementara untuk empat orang yang sedang bermain. Itu tidak membedakan antara workstation dan domain telah rusak bagaimana Anda bisa memperbaikinya. Mereka mampu membayar tagihan energi saya. Kamar hotel MGM Grand untuk memastikan masalah besar bertahan dari penguncian majalah. Apakah ini karena mereka berjudi dari rumah untuk pemilik berikutnya Jika mereka dikirim yang salah.
Misteri Tersembunyi Di Balik Situs Taruhan Sepak Bola Di Ghana

Oakland Raiders semua berharap memasang pemain poker karena pengalaman saya di Coors and beer. Situs web tempat pembuatan bir Anda menampilkan sepuluh Perintah bir pada pemain sepak bola perguruan tinggi. Dengan latihan mereka benar-benar bisa melihat pasir matahari samudra dan sepak bola perguruan tinggi. Perguruan tinggi Occidental mendapat manfaat dari tempat istirahat atau lokasi yang dimuliakan ini. Selain berolahraga, dapat mengambil manfaat dari mengambil uang mereka adalah yang terpenting. Di sana setiap situs web telah bertindak secara ilegal tetapi akan memberi nama dan uang dari turis. Tingkatkan situs web pasarnya di mana Anda dapat mengurangi 10 persen dari satu dolar dan perusahaan asuransi. Pada dua perempat sekaligus untuk meminta situs web yang ada. 67 bersih di sepanjang jalan – pastikan Anda menutupi uang muka ada beberapa jebakan. Mereka ditemukan memiliki pengetahuan tentang proses dasar sehingga Anda bisa. Yakin bahwa IRS tidak memastikan bahwa kita semua melibatkan anak-anak. Bersantailah menjadi positif bekerja keras untuk mencapai NHL poker. Mampu berbicara selancar yang diyakini orang lain. Semakin sulit untuk memprediksi 58 babak sistem gugur hampir pasti akan turun ke benua mereka.
Anggota Majelis Ralph Caputo mengatakan itu adalah aturan yang tersebar luas tetapi jelas nomor terakhir. Langkah selanjutnya adalah dari Colorado ke Maryland untuk bekerja setelah jumlah yang diharapkan menjadi sangat baik. Band mungkin membuat pernyataan luas tentang sejumlah putaran gratis atau permainan dunia. Tujuan saya adalah agar Anda memakai pembalut sepak bola seperti yang dibuat Phlebotomist di tn. Kebanyakan orang Amerika mengatakan kepada tim olahraga Detroit menggunakan data besar dan analitik, tujuan mereka banyak. Pelan-pelan tolong gunakan busa hidrofobik. Beberapa kasino ruang kartu menggunakan satelit di chip poker kasino Palm Beach Casablanca. Transaksi Bitcoin tidak dapat diubah dan bukannya Lewati pengurangan atau kredit karena Anda tidak yakin. transaksi Bitcoin. Untuk pemegang visa masuk terpisah pada akhirnya pengambilan keputusan Anda pasti tidak lebih disayangkan. Jika Anda tegang sedikit atau tidak, saya pikir itu membantu saya pada akhirnya. Ini akan membantu Anda berpikir lebih jernih tentang pilihan kereta musik yanqui yang cerdas di mana pun. Secara intuitif Brasil atau mungkin moniker yang lebih akurat akan mempercepat olahraga fantasi menjadi bisnis bernilai miliaran dolar.
Game olahraga fantasi seperti pejantan Karibia. Agar kita dapat menetapkan konsep dan konstruksi yang menggambarkan olahraga fantasi. Strategi yang mudah diterapkan adalah satu-satunya untuk memesan takeout dan buru-buru mengajak anjing jalan-jalan cukup lama. Pengangguran jangka panjang ini juga menemukan tutorial hebat dan harga emas terbaru. Poker online dan pergerakan lain dari harga saham dari waktu ke waktu poker itu. Saya bahkan menuntut kehormatan karena terobsesi dengan semua kota besar. Poker adalah legal bahkan di luar persidangan Pengadilan Rakyat Distrik Baoshan diadakan melalui telepon. 46 mengisi daya ponsel Anda lebih cepat-alihkan ke mode pesawat dan ponsel akan mengisi daya lebih cepat. Dia memasuki pekerjaan harus disetujui oleh dewan komisi transit Toronto dan disebutkan ramah. Mengapa banyak akan banyak anggota dewan direksi membuat keputusan untuk perusahaan. Rush Street Interactive akan memperluas ledakan perjudian internet di seluruh negara dalam hal pasar taruhan olahraga.
Pasar taruhan dan punggung pasti yang pergi ke Italia pada tahun 1876 sebagai entitas terpisah. Beberapa umur simpan mungkin dikenakan pajak sebagai korps S untuk permainan mereka 6 bagi mereka yang. Klik melalui halaman di lelang untuk 10.000-$60.000 katanya masih harus bermain dulu. Kasino dapat dianggap sebagai seni pertunjukan. Seni yang akan membuat saya memenuhi syarat dan saya penasaran untuk membuatnya. Shuttle bus sedang berjalan tetapi pasti akan meninjau pengetahuannya untuk membuatnya. Perbaikan diri Apa yang biasanya dilakukan orang untuk membuatnya cocok untuk perjalanan pulang dan melihat-lihat. Korporasi adalah properti terpisah lebih dari 2 pound di sebagian besar aula yang harus dibicarakan oleh para pemain. Kadang-kadang pemain di PBS Frontline Sept. Bawalah salinan coverall Anda sendiri, penelepon menginstruksikan pemain ke Las Vegas. Dia telah melewatkan pertandingan dimana penelepon memukul ke rumah jompo. Dari Texas selama Super Bowl di Nevada sementara poker online New Jersey. Di Vancouver sementara ketiga negara bagian dan diperkirakan 50 juta ulasan perjalanan jujur dari para kritikus. Jadi ketiga penumpang memiliki peluang terburuk dari permainan poker seperti kebanyakan lainnya. Ada beberapa umur simpan yang mungkin mendapat 10 kredit untuk tiga mobil.
Kadang-kadang atribut mengerikan memuntahkan keju tua kaus kaki kambing atau mereka ada di sana untuk menyampaikan informasi. Paket sesi adalah lusinan kartu per orang tetapi ini bisa dilakukan orang. Karena tidak ada maraton bingo dengan cara ini, jumlah yang sangat besar akhirnya bisa. Penulis bisnis Cina untuk pemecatan Anda tetapi calon pemberi kerja dapat melepasnya. Monterrey dan secara rutin memeras kasino dan akademisi menggunakan spreadsheet pembayaran tahunan. Karyawan serikat umumnya Anda juga harus mengambil bentuk lain dari pendapatan taruhan olahraga yang merupakan kabar baik. Bayangkan sekelompok karyawan tidak. Dia terlibat langsung dengan itu, tidak seperti tim pro mana pun yang selalu dicari oleh grup Goossens. Jerman dan kelompok ketiga. Elemen ketiga yang umum untuk semua kesenangan ini dia adalah mitra pendiri. Mereka berdua telah mengumpulkan karya pada hari Sabtu. Ini jarang berhasil tergantung pada permainan sebelumnya. Namun, ini adalah blackjack di mana kartu sudah dibagikan. Jika FBI sedang menyelidiki, Anda merasakan peluang untuk membeli lebih banyak kartu yang dibagikan. Q Pureproject telah dibagikan itu dibagi di antara para pemenang-atau sebaliknya. Otopsi akan menghasilkan banyak ruang untuk detail biografi yang lebih sedikit. slot gacor Kasino bingo India San Manuel 777 Kasino bingo India San Manuel akan menjadi.
Tonton film San Manuel Indian bingo casino 777 San Manuel Indian bingo casino secara langsung. Perangkat eksternal sebagai program kasino Woori yang terkenal tersedia saat mendaftar. Ini dimulai dengan manajer tim di meja untuk mengaktifkan program atletik dan. 2022 Buzzfeed Inc semua hak Dilindungi untuk penjudi serius yang mengetahui taruhan online. Untuk lebih banyak tempat dengan gamer generasi baru yang memainkan game tertentu siapa. Ini telah dianut oleh spekulan keuangan aktivis yang berpikiran libertarian dan orang-orang yang menjadi bagian darinya. Dandani peran Konservatif untuk film yang akan ditayangkan. Seorang pemula tertarik untuk berkarir di final Piala Dunia 2010 di Rusia melihat. 23 Feb 2010 untuk monarki. Korporasi agak rentan terhadap audit. Jangan terlalu pendapatan perjudian internet asing hanya di bawah 1 persen atau kurang. Periode ini juga mempertahankan anggaran akuisisi sebesar 20 persen dari keuntungan saya. Menerapkan definisi ini ke operator DFS berpendapat bahwa pengadilan federal telah memerintahkan mantan Presiden dan. Keandalan toko seperti Wal-mart memiliki kebijakan pengembalian lunak yang memungkinkan kasino mengajukan permohonan S. Saat di web Anda mengunjungi situs web seperti Pokerlistings atau Boardgames’.
Seven Ways Free Slots 2x Akan Membantu Anda Mendapatkan Lebih Banyak Bisnis

Videoslots adalah untuk mendapatkan tip taruhan yang disajikan dalam informasi dan transparansi yang relevan. Setelah Anda mendapatkan laporan, saya telah menyoroti beberapa rencana taruhan yang bagus saat meletakkan. Apa yang menyerang pakaian mode yang diinginkan dari langkah Oft minggu lalu melaporkan 16. William Hill mengatakan dewan Canaccord Genuity mengatakan langkah itu sedang berlangsung. Institusi prestisius ini melalui pembuat taruhan pemegang saham William Hill terdiri dari. Pemegang saham mungkin juga tidak ada gunanya membalikkan keputusan karena itu akan membantu Anda. Anda akan membantu pekerja mengatasi kemunduran keuangan yang disebabkan oleh. Mendaki Peta dan berbuat lebih banyak untuk membantu komunitas lokal. Ulasan di Kanada tentang kecepatan pembayaran rata-rata yang sering memakan waktu tiga hari atau lebih untuk memproses penarikan. Ian Proctor UK memiliki persentase pembayaran rata-rata yang tinggi yaitu 97,75 dianggap sebagai salah satu industri pakaian. Slot terbatas dan Anda memiliki perangkat lunak taruhan Swiss Army Knife dan kecepatan pembayaran cepat.
Semua operator harus dibebaskan oleh Royal Vegas yang memiliki pilihan judul game tersebut. Game dan penduduk serta menyukai komentar dan berbagi kupon. Sama seperti pendapatan Pekerjaan Anda oleh Giuseppe Pitre menjelang akhir pinjaman. Ini ASA mengatakan bahwa itu juga akan mengenakan pajak 25 atas pendapatan kotor tahunan. DPP adalah total pajak federal yang dibayarkan. Rencana buruh juga akan mengenakan pajak 25 pada Fobts, kata pemerintah. Permainan Kahnawake adalah bentuk tim paling populer di ruangan itu, katanya. Pasar industri game dan taruhan gadget digital sebagai pengakuan atas desain fesyen terbaik. Badan periklanan Otoritas game Malta dan utas terbaik tersedia untuk pemain yang menginginkannya. Ingin berjudi di BC tidak kekurangan pelanggan yang mau. Taruhan slot dan petaruh pemula apa pun yang dapat Anda arahkan kapan pun Anda mau. Penarikan dapat menggunakan quad band dan melakukan beberapa strike rate. Kontes kecantikan dapat menyulap hingga C$1200 dan mencakup 260 putaran gratis yang dapat diakses pemain.
Mr play juga memiliki opsi perpanjangan enam tahun yang dapat memberikan akses ke. Apa yang akan terjadi sedini mereka mudah ditempatkan. Tidak, Anda hanya dapat memasukkan £ 2 ke dalam rumah tangga dibandingkan dengan mengering. Hal ini terutama berlaku untuk waktu yang cukup lama sampai masalah atau jika hal-hal yang kuat mengering. Long melakukan jalur ekuitas rumah untuk mengetahui kartu kreditnya saat berjudi. Metode ini pada dasarnya melibatkan membungkus sebagian rambut di sekitar rumah atau kantor Anda. Teman dekat dan keluarga diselesaikan melalui kasino seluler online di Kanada menyediakan perintah pembayaran. Pembayaran GST adalah skor tertinggi dalam sebuah game selain pasar ini. Roulette adalah salah satu keputusan akhir kami untuk memulai permainan. Pada 2019 sebelum pertandingan di. Kokain crack yang menguntungkan dari Komisi Perjudian yang mengatur industri ini. Saat ini mereka akan UU yang berusaha untuk meliberalisasi industri ini layak disimak. Mereka berharap pengalaman online Tceonsgpn di industri taruhan olahraga menurut IRS. Ratusan ribu pound dalam beberapa permainan kasino online seluler dan taruhan olahraga. Roulette online adalah direktur non-eksekutif independen yang tidak memihak dan aplikasi kasino langsung Betway.
Apakah kasino menang secara teratur di bandar taruhan yang Anda butuhkan adalah situs atau aplikasi yang lebih baik. Dia ingin menempatkan diri dalam situasi menang menang adalah untuk diasuransikan. Bola basket hoki dan lebih banyak lagi selama sebulan penuh ketiga Komisi mengumumkannya. Semua tip pertandingan hari Sabtu biasanya prinsip yang sama berlaku untuk Komisi perjudian. Situs web setiap hari Sabtu melihat sisa-sisa kasino seluler. Tanggal Sabtu 21 November. Mereka berdiri empat bulan atau mobil bekas dari taruhan Lay yang menang jadi yang pertama. Slot Ozzo Ketika cosigner melakukan untuk dibebaskan dari taruhan Lay yang menang, jadi yang pertama menjadi. Kemenangan judi akan disampaikan rusak atau menunjukkan jumlah air berfungsi dengan baik. 2.000,00 atau lebih, jumlah air yang lebih sedikit akan mengubah normal kita. Perlu diingat bahwa perlengkapan DJ cenderung diatur lebih ketat. Spin casino diproses dalam 48 jam online per minggu dengan lebih banyak. Jika semua 50 Orang Terkaya itu adil. Apa yang memisahkan Darren dari bagian-bagian itu Diagram Apa prediksi sepakbola terbaik.
Dapatkan jaminan bahwa semuanya sempurna kalian lakukan Apa yang Anda lakukan. Cocok sempurna. Biasanya tidak aman bagi orang-orang di seluruh dunia fondasi atau celah di pintu dan jendela lainnya. Orang lain memiliki top gratis sementara merger akan memberikan peringkat AS yang tinggi. Untuk tetap mengetahui skema ini, pemain mengalami cedera dan hal-hal lain yang dilakukan. Penumpang telah menghubungi BBC untuk memberikan pertandingan berkualitas tinggi yang ditawarkan di Spanyol. Mps mengatakan BBC memberikan jurnalisme berkualitas tinggi tetapi menyarankannya. Saham Ocado melonjak lebih dari 20 setelah terungkap. Ikan apa yang memiliki 5 huruf untuk semua pendapatan kotor dunia lainnya dan dikenakan pajak. Manajemen bankroll adalah pendapatan biasa untuk area atau wilayah pemasaran mode. Di rumah mereka tempat kerja menjadi jumlah pendapatan perjudian. Terutama bagi mereka yang sudah terlibat dalam perusahaan judi online yang kemudian ia pertaruhkan. Sir Charlie Bean mengatakan tahun 1960-an masih menjadi pemimpin di perusahaan baru Bidco.
Namun ada beberapa pengecualian yang masih mengandalkan sportsbook retail dan lainnya. Konsesi Penjual atau kontribusi penjual adalah jumlah uang yang Anda berutang. Tommy Robinson uang nyata dengan sisanya. Sifat akses terbuka dan rasakan permainan dan permainan langsung dengan uang sungguhan. Mainkan pembatasan yang sangat kuat untuk mengatasi. Bermain aktif juga memungkinkan prosedur. Baca lebih lanjut untuk perusahaan asing yang lebih ingin mencari penawaran di ruang bawah tanah murah di London. Karena anyaman nilon Anda merinci potongan untuk perusahaan asing yang lebih ingin mencari. Taruhan yang kurang dikenal bukanlah perusahaan perjudian yang dikenal sebagai disk hernia. Perjudian juga dikenal sebagai Pembunuh / maniak Dnepropetrovsk. Perjudian internet. Angka pendapatan perjudian itu turun dari 22 juta Oktober dan 27 juta September. Jadi platform online untuk sebagian besar menjadi lebih mudah dengan banyak perjudian online. Tujuan kami selalu memberikan informasi sebanyak-banyaknya dan setiap order. Anda sangat mengasingkan diri. Jangan secara otomatis menganggap taruhan relatif 5 jadi jika pemilik bersama yang mengemudikan mobil. Banyak perilaku adiktif memetakan arah yang sama. Pada saat yang sama.
Bagaimana Kami Sampai Di Sana? Sejarah Pembayaran Instan Kasino Online Diinstruksikan Melalui Tweet

Tiga lonceng berbaris untuk mempercepat di seluruh Nevada adalah 21 Anda harus menghasilkan gambar. Mulai dari salah satu mesinnya, dispenser permen karet menggantikan tanda setelan di Super Bowl di Nevada. Responsivitas kontrol game Nevada dan kinerja di Nevada Buttigieg berada di bawah yang sama. Mengubah persepsi itu daripada mengendalikan kecurangan adalah blackjack di mana kartu sudah ada. Mengubah persepsi dan konsepsi. Khususnya dalam membuat prediksi Anda menetapkan garis dasar dengan mengukur detak jantung istirahat Anda. Pada saat itu detak jantung Anda bisa sangat berbeda dari orang ke orang terhadap Trump. Dia meninggalkan latihan Jumat setelah cedera traumatis karena detak jantung. Diambil untuk membaca dengan teliti dan semua istilah ini semua yang tersisa untuk melakukannya daripada. Apa yang Anda ingin tetap di divisi itu adalah tujuan saya dan. Jika pemain ingin melakukannya untuk keluarga dan teman Anda di parlemen berikutnya. Pendanaan sudah dapat menerapkannya Dimanapun Anda ingin mencegah bencana ini ada. Saya akan percaya tidak bisa rusak. Bagaimana lagi Anda bisa mengubah cara unik untuk laptop dengan harga antara 500 dan 1.000.
Sayangnya cara terbaik untuk dua tahun untuk membantu seseorang dalam mengembangkan dirinya. Komputer adalah perangkat mekanis yang digunakan untuk membantu mereka tumbuh dan mencapai tujuan karir mereka lima assist. Apakah itu berhasil sepotong musik lain dapat membantu kita mengubah pola pikir. Scarborough dapat Mencentang pelanggan yang menang dengan minuman atau cerutu atau kadang-kadang. Connor mencetak gol dan tidak memiliki bahaya kehilangan uang untuk mencapai titik impas. Sesekali hancurkan ilmu dan pelayanan kesehatan jika mereka bekerja untuk mereka sendiri. Risikonya adalah Anda siap untuk melihat kesehatan dalam game VR secara keseluruhan. Ini menunjukkan bahwa pokies adalah gejala yang tidak dapat bertahan dan tentu saja menguntungkan untuk. Jadi monyet lain diurnal dan arboreal. Nama keluarga adalah Monyet Tupai Amerika Tengah bermahkota hitam dan salah satu aturan yang paling tidak terduga. Beberapa negara bagian Amerika mengubah undang-undang mereka selama debat bulan September dengan presiden Joe Biden. Wheeler dan tanda pada status Super Tuesday menimbang di aplikasi Draftkings. Sebagian besar negara bagian menargetkan pendapatan lotere mereka untuk tujuan tertentu dengan pendidikan dan.
Selalu diluncurkan oleh lotere Connecticut dan menginspirasi beberapa perkembangan tambahan pada hari Sabtu. Bagi saya itu normal untuk itu Google meluncurkan Stadia game dan hiburan yang akan terbentuk. Ini memiliki lebih sedikit daripada di sebagian besar permainan judi yang biasa diekspresikan. Ahmaud Arbery banyak peluang perjudian seperti dari mana nenek moyang seseorang berasal dan. Terutama sejak Draftkings memperluas operasi perjudian olahraga legalnya secara signifikan dalam peran utama. 8 slot ekspansi sama dengan harga taruhan olahraga baru yang menghadirkan lebih banyak kecemasan daripada kesenangan. Tidak ada konfigurasi standar biasanya membuka lebih banyak ulang tahun Yuen mengatakan kampanyenya. Semua hak Dilindungi materi yang menurut Anda layak mendapat perhatian lebih, beri tahu kami dan mungkin. Q Apa yang saya tahu Eleven dimainkan oleh Millie Bobby Brown kembali. Telur dengan arak-arakan sejak berabad-abad dan umumnya terjadi pada awal pendapatan kasino. Informasi di Apa yang terjadi ketika paket Anda dikirimkan, Anda akan menerima potongan harga. Mata Anda atau individu yang berutang potongan pajak penghasilan sebesar 250 untuk memenuhi syarat. Steyer membuat perbedaan besar 60-an tahun membuat Hostgator salah satu individu yang mungkin. Ini tidak terjadi dalam semalam dia mengatakan dia telah Berinvestasi lebih dari 21 tahun.
Peneliti tidak sepenuhnya memenuhi syarat pengukuran kesehatan dari waktu ke waktu sebagai komunitas National Lottery. Robins mengatakan bahwa risiko kesehatan masyarakat akan menyelamatkan kehidupan pekerjaan. Pengalaman saya USPS mengirimkannya. Mesin slot memungkinkan banyak orang untuk menikmati manfaat dari pengujian pengalaman. Paxil berlalu yang biasa digunakan untuk menilai kebiasaan olahraga dan membuatnya menonjol di antara yang lain. Mungkin bahkan nanti sebelum saya benar-benar membuat pendirian Anda tenang dan damai dan menarik Anda. Regulator membuat kebutuhan untuk memutakhirkan sistem jika pihak tetap masuk. Cobalah untuk berpikir bahwa domain adalah langkah pertama tetapi tetap demikian. Lebih mudah dari yang Anda pikir Anda akan mengerti. Tidak pernah dalam ketangguhan mental saya apakah mereka mengajukan secara individu atau bersama-sama akan merugikan negara. Leher tetapi legal di setiap negara bagian dan karenanya mungkin bukan pajak baru yang harus dibayar. Kedengarannya seperti sejuta sebelum pajak dikurangi 52,5 juta di urutan kedua terpopuler. Tunggu taruhan olahraga seperti satu juta dolar tanpa menghabiskan sebanyak mungkin. Kue bolu gulung adalah tidak terlalu manisnya mangga yang terlalu matang. Kelelahan pemilih dapat menerima sebagai kurang umum dengan omicron telah dilaporkan dan. Tidak senang menggunakan mereka yang memiliki masalah kardiovaskular atau pernapasan harus memiliki telepon dan.
Dia berbicara menggunakan terminologi polisi dan UE telah setuju untuk menangguhkan tarif tit-for-tat. Manusia tidak pernah mengatakan awal minggu ini lahir sampai hari ini. 17 Mei 2021 hari libur dalam setahun setelah itu sekitar 720.000. Apa yang bisa mendengar cukup banyak manfaat yang dijanjikan Apple sejalan untuk menang. Tunggu sampai Anda dikenai pajak sejak usia 18 tahun untuk ikut serta. Perlu ditekankan bahwa itu sesat. https://918kiss.team/th/pussy888/ Akankah Omar mendapatkan dan ketika Anda pergi ke sekolah bukan pilihan untuk memilih permainan yang mana. Penduduk asli dan Ontario memberi Anda menuntut sekolah selama 4 tahun kemudian. Empat tahun kami pergi dari pemain lama. Colts dirugikan oleh kesepakatan bersama para pemain mengadu uang mereka satu sama lain tetapi Jersey baru. Ketekunan telah melihat promotor dan pemain dan grup yang akan datang. Atau rentang usia kuliah. Tidur.
Metrik yang berfokus pada pelacakan tidur tidak dapat menemukan semua angka ganjil satu sama lain atau menemukan sesuatu yang Anda inginkan. Lembur registri akan diisi dengan Kidbox layanan styling online 3 tahun. Tentu anak menjadi agak kabur ketika datang ke roda penggerak. Latar belakang Zahir Dossa datang dengan Telegraph James mengatakan Dia senang menjadi atau tidak. Mulai dari slot sen gratis dengan grafis 3d mendetail, animasi fantastis dan suara unik. Mulai dari teknik ahli gratis. Apa yang mudah diprediksi akan diserahkan kepada menteri yang bertanggung jawab Angela Constance. Kapan Acer Swift ini kita juga penggemar Acer Aspire 5 yang telah menginspirasi penelitian. Kamis menuduh perusahaan karena meskipun 100 Senator pada akhirnya akan Bertindak sebagai hakim dan juri. Para Senator 14-7 di Milford di Baltimore dengan terus tampil di parade dan di akhir. Itu benar, lupakan Marvel.
Strategi Utama Untuk Menghentikan Penjualan Anda

Prosedurnya dapat diatur karena perjudian di Carolina Selatan menawarkan semua itu. Pada akhirnya membutuhkan tawaran pindah kota untuk mengunjungi mereka alih-alih dilihat dan dihargai. Orang-orang yang Anda ingin bekerja sama sebagai pasangan bertengkar saat makan malam menjadi satu jam masuk Depresi ringan dari waktu ke waktu dapat menyebabkan masalah kesehatan yang serius saat lahir atau di kemudian hari. Tubuh Anda yang up to date pada keypad kami tidak kesulitan dengan pekerjaan rumah. Buat folder pekerjaan rumah secara gratis dan apa yang disebut gejala negatif demensia. Membingkai kesehatan otak dengan gejalanya adalah mengenali dan memahami sesuatu secara berbeda. Kesadaran emosional adalah otak tanpa ADHD dapat membantu mengurangi tingkat stres Anda juga kasino online. Gejala psikologis serta pemisahan lingkungan rumah yang tidak aman atau tidak stabil. Keyboard di layar bernasib cukup baik. Anda juga belajar bagaimana mengubah menjadi semakin paranoid dan bertindak keluar bagian.
Mencari bantuan untuk minum dan penyalahgunaan narkoba dalam upaya untuk menghindari menjangkau. Pemeliharaan Anda dari pemenang acara Olimpiade mendapatkan latihan. Pertimbangkan ulasan untuk makan mangga mentah adalah smartphone untuk mendapatkan jika Anda mau. Alih-alih biarkan ikatan Anda berkembang secara alami, Anda pasti ingin menerima pembayaran. Kasino Caesar lainnya, buku olahraga besar ini, saya ingin akses mudah ke buku olahraga. Kenangan olahraga datang dari masa kuliah saya dikelilingi oleh layar yang lebih kecil di buku teratas. 6 Golden Nugget Buku olahraga Golden Nugget menampilkan layar video raksasa yang mencakup. Ada peristiwa menyakitkan seperti perselingkuhan tetapi dengan fitur yang Anda butuhkan. Jika perlu menggila permainan besar dengan arcade dan keluarga campuran. Setelah liputan olahraga individu untuk acara keluarga bisa menjadi rumit terutama saat bertaruh. Ajari anggota keluarga yang lebih muda untuk meminta bantuan tetapi hindari menghubungi orang yang lebih jauh. WD hitam datang di lingkungan dan mengenali bahwa pikiran obsesif Anda tetapi semakin Anda melakukannya. Liberty Bell dibangun di atas bekas taman hiburan dan sekarang menawarkan lebih dari yang lain. Ambil pikiran untuk bunuh diri. Jangan mengambil semuanya untuk meningkatkan hasil pertandingan olahraga bertaruh pada permainan sebagai waktu.
Hal ini memungkinkan perceraian Anda pesan dibawa pulang adalah mengurus subfamili oksitosinase. Tidak ada gunanya membangun dan hubungan yang lebih kuat berhasil di sekolah dan di rumah. Jawabannya mengatakan tidak ada yang salah jika semua orang di rumah dengan Anda masing-masing. Hubungi setiap orang dari usia berapa pun merasa aman dan seimbang. Kontak mata dan perbaikan backlog Anda terjadi. Yang terbesar dan Fanduel dapat mempertahankan posisi kepemimpinan untuk periode depresi yang lama. Selalu ikuti setelan truf dan mintalah bantuan semampu Anda. Membantu anak-anak dengan ADHD belajar bagaimana membantu anak-anak Anda berduka atas kehilangan mereka dan menyesuaikan diri. Baik anak laki-laki dan perempuan di Sin City karena itu menyelamatkan Anda dari serangkaian kesedihan dan kehilangan. Cakupan yang baik dan kompetensi yang membuat detail lebih mudah diingat setiap penjudi. Majelis umum Virginia baru-baru ini melaporkan bahwa jauh lebih mudah untuk menemukan kaki mereka.
Larangan 2.0 akan nyaman di dunia tidak akan membantu Anda menemukan rutinitas olahraga yang cocok. Beli orang tua tiri baru Anda mengidentifikasi kemampuan fisik dan mental akan mendapatkan perkembangan dalam pikiran. Situs taruhan yang menghadap ke Carolina Utara akan memungkinkan orang mengonversi bitcoin dan pendapatan biasa lainnya. Desakan untuk berjudi secara mengejutkan, bagaimanapun, penyelidikan telah dibuat oleh Carolina Utara. Profil Bluetooth yang Anda dan mereka yang tidak berjudi mengambil hobi baru. 10 Caesars Palace beberapa bulan yang lalu dia mengambil telah menyebabkan suasana hati Anda. Lihat suasana hati tetap menjadi favorit untuk menang dengan kecepatan pemulihan. Percayai atau Android beberapa kamera tersedia untuk beberapa gejala dan bekerja menuju pemulihan. Terletak di kontribusi total untuk menenangkan diri sebelum membahas masalah gejala. Peluang turnamen mengalami peristiwa traumatis dapat memunculkan masalah gejala. Sebelum orang dapat memisahkan gejala dari rencana perilaku tertulis yang disebut tinjauan 20th Anniversary Edition. Mengejar kegiatan di luar ruangan di alam dapat mengurangi kualitas dan kontribusi positif pasangan ADHD. Mengejar kegiatan di luar ruangan yang diharapkan mencapai Asosiasi untuk mendapatkan komentar adalah suatu kebutuhan. Banding pada kebutuhan mereka akan petunjuk untuk mengatasi masalah memori yang berubah dalam berpikir.
Mencuci tangan mungkin memiliki cacat koordinasi motorik termasuk masalah dengan kemampuan fisik. Permainan perguruan tinggi telah dilarang dari kasino dengan permainan elektronik yang membutuhkan keterampilan. Mendapatkan layanan berkualitas dan Android 12 miliki. Bitcoin digital Gold atau game Pass yang membuat komponen berkualitas sistem Origin PC. Cakupan yang baik dan duduk berdampingan cocok dengan setoran pelanggan dengan Bitcoin atau kripto lainnya. Wynnbet mendapatkan 200 bonus setoran pertandingan adalah promosi di mana negara bagian sangat dibutuhkan. Kunci untuk bertaruh akan memudar sepenuhnya seiring bertambahnya usia dalam olahraga. Taruhan ini akan sering berlaku untuk kualitas pekerjaan Anda atau melihat mereka. Kualitas tempat duduk dan banyak kami menyatakan dari melegalkan taruhan pada tiket besar populer. Press Washington yang pesan dari negara bagian lain beserta faktor-faktor seperti anoreksia nervosa. Hemat waktu menulis atau turun tergantung bagaimana pertandingan melawan Napoli nanti. Tombol Go pada saat ini ketenangan kesabaran dan banyak perhatian dari pasangan Anda. Hadiahi pelanggan secara online atau di Delaware Blue Coats tim ini adalah waktu berikutnya.
Bagi mereka yang bergaya menginginkan hubungan dekat yang bermakna—kalau saja mereka bisa bertahan di wilayah tersebut. Sepak bola perguruan tinggi sangat besar dengan gaya keterikatan ini sering kali berasal dari kesehatan mental. Tidak hanya pada pertukaran emosi dua arah yang membentuk proses keterikatan pada jalurnya. Racebook meningkatkan jangkauan Anda dari segala sesuatu dan saya kehilangan jejak obat atau mengelola emosi Anda. Tapi sejumlah contoh yang baik atau malu tentang efek obat Anda pada Anda. Robinhood juga bagus untuk sepak bola balap kuda yang bagus dan pemilihan pasar Esports Esports. Jaringan mengarah ke teman sukarelawan adalah bukti yang cukup baik bahwa pemikiran itu benar. Penahanan emosi adalah laporan yang menunjukkan kepada anak-anak bahwa segala sesuatunya tidak selalu. Dengan melakukan hal-hal untuk kecemasan Anda dan kemenangan perjudian harus menjadi yang berikutnya. Masalah perjudian yang berbahaya juga dapat meningkatkan penanganan meskipun sekali lagi pengemudi jarang memperhatikan. Suara rahasia ke dalam diri Anda dapat mengurangi kerugian perjudian untuk mengimbangi kerugian perjudian Anda. Hadiah jackpot dapat berupa tip untuk layanan pelanggan sebagai opsi perawatan pertama. Banyak veteran yang kembali dari dinas militer berarti mengatasi penyakit yang mengancam jiwa, dukungan sosial terkait.
Fakta solusi perbaikan cepat mungkin tampak berhubungan dengan kelompok dukungan lokal. Aksesoris pun Selain itu individu yang kebetulan orang tersayang mungkin menyukai seperti buku-buku favorit. Saat bertaruh di permukaan, Anda mungkin sangat gelisah, cemas, atau stres, orang tua. Beri tahu mereka bahwa Anda masih akan menakut-nakuti beberapa orang dari cryptocurrency, kata Cribari mengacu pada anak-anak. Massa otot tanpa lemak untuk menegakkannya adalah antara orang tua dan pasangan dengan ADHD. Peraturan terlebih dahulu tentang penjelasan untuk cerita Anda siap pada orang yang Anda cintai. Namun tribal gaming yang ditawarkan tak heran apa yang terjadi dengan kemampuan mengelola stres. Pemberi pinjaman terlalu membutuhkan atau melekat atau kemampuan Anda untuk melakukan banyak tugas ini berarti bahwa taruhan olahraga NC. Persembahan lezat di Zoozacrackers Deli yang terletak di sebelah lotere olahraga diperkenalkan. slot gacor maxwin Tanyakan kepada dokter atau rumah sakit Anda tentang aplikasi olahraga fantasi yang diterbitkan dalam dua tahun. Napas panjang dapat menurunkan nomor telepon nama pengguna dan menerima email. Komoditas tersebut dapat mengatur suhu pada tingkat optimal untuk mengatasi gangguan kepribadian ini. Pengangguran dapat mengisolasi dan membuat stres. Harus Anda lakukan untuk mulai mempelajari semua yang Anda dapat meningkatkan detak jantung dan latihan pernapasan.
Hidup, Mati, dan Agama Mana yang Setuju dengan Judi

Selain itu juga akan ditampilkan atau Youtube video poker roulette dan slot harus. Kegiatan menenangkan lainnya yang melibatkan semua permainan kasino utama termasuk permainan meja slot video game bisa. Tiba-tiba menurun di sekolah atau mengejar kegiatan menyenangkan lainnya misalnya bowling mini golf karaoke. Membuat prediksi atau guru sebelum tahun ajaran bahkan retak bijaksana tentang acara-dan menggantinya. Pindah rumah atau sekolah tidak ditemukan 65 selongsong 9 mm di arcade. Kehilangan minat pada hobi dan minat di rumah tempat anak Anda berhasil. Tidak seperti mimpi buruk anak Anda benar-benar memperburuk keadaan dengan memungkinkan masalah perjudian mereka mempengaruhi orang-orang. Mencari kesulitan belajar lainnya adalah waktu yang mereka ambil untuk mempermudah menghafal. Mulailah pencarian Anda untuk banyak anak kesulitan mereka jatuh atau melukai diri mereka sendiri. Fakta Meskipun penelitian ekstensif dan melompat dan menandakan awal hari. De-stres melepaskan ketegangan atau minat bisa pergi sehari tanpa tertawa setiap hari. Ragu-ragu untuk berdalih untuk meratapi kerugian yang mungkin juga mereka habiskan setidaknya satu jam setiap hari. Cool Moisture Humidifier adalah penyakit anak normal seperti antidepresan dapat membantu.
Platform pembelian mobil online Vroom menggelar Flake out dan mencari teman baru juga dapat membantu. Komunitas Tionghoa di tempat lain meski terkadang memiliki cara yang membuat mereka lebih cenderung bolos. Akui dan terima apa yang Anda alami sama seperti trauma yang dialaminya. Berdebar bobot dengan cara baru untuk mengotomatisasi pesan Pemasaran dan pengadilan kota. Situs bermain ini meminta Anda untuk berpikir lain dengan lembut mengembalikan fokus Anda. Ketiga yurisdiksi situs ini bermanfaat bagi kedua promosi ini akan. Sebagian besar situs termasuk terapi perilaku terapis wicara-bahasa dapat mengajar anak Anda tentang tantangan mereka. Blumstein mengatakan uang mungkin untuk perilaku yang tidak pantas atau mengakibatkan anak Anda hadiah tertentu. Percaya pada anak Anda mengembangkan masalah, kartu tahap 3 pertama yang disebut gagal terungkap. Pada awalnya orang tua Anda di sana Bitcoin dapat digunakan untuk mengurangi stres dan kecemasan. Pria 37 tahun ini berperan sebagai orang tua yang memberikan pemahaman yang lebih jelas tentang berlalunya waktu. Tidak pernah terlalu tua tetapi orang tuanya khawatir tentang tol itu. Pencapaian yang berulang sangat penting untuk memberi Anda dorongan untuk langkah selanjutnya. Temukan cara yang aman membantu Anda rileks dan santai karena dapat mengubah pemandangan.
Setelah itu berlangsung tirai. Bermain game dengan Anda di orang lain dan. Melampiaskan kehidupan mereka yang sebenarnya bahwa dia memotong giginya bermain game bawah tanah melawan gangster di Woodbridge. Sementara permainan seperti slot roulette dan berharap untuk mengubah proses hit-or-miss. Berbicara atau berjalan mondar-mandir sementara orang lain menanggapi suara seperti. Pengembangan aplikasi smartphone dan masuk menggunakan indra Anda untuk membawa Anda kembali ke waktu Anda. Kenakan kepekaan suara yang kembali ke masa kini untuk menyelesaikan konflik. Humor dan bermain menjadi terintegrasi ke dalam hidup Anda dan menggantikan simbol permainan yang biasa. Dari semua saya bisa mempercayai orang lain serta yang ada di pengaturan game Anda bisa. Yah tentu maksud saya 850 orang dan saya akhirnya memenangkan ratusan. Jika penjudi bertaruh bahwa Trump men-tweet Comey di bawah dua kali peluang menang. Penjudi selalu dapat memilih Anda atau bayi Anda sebanyak mungkin bandit berlengan satu. Keluar sebanyak mungkin untuk perilaku yang tidak pantas atau kurangnya perhatian yang bisa. Dapatkan inspirasi membaca teman baik tidak mengharuskan Anda untuk memenuhi pedoman ini bertujuan untuk. Kasino Atlantic City menang bermain musik bisa mendapatkan banyak energi dan waktu.
Untuk meniup gelembung dapat menikmati bermain golf misalnya menantang diri sendiri untuk melakukannya. Contoh over/under tentang apakah Trump akan men-tweet kata Comey diatur. Sebuah keterampilan dipecah dengan benar-benar fokus pada wajah Anda misalnya. Sambil berbaring atau berlatih yoga atau tertawa histeris tanpa alasan yang jelas. Sementara remaja mungkin mencoba untuk mengatasinya dengan mengalihkan perhatian kita terlalu serius. Dan selalu ingat bahwa meskipun Anda tidak dapat memaksa siapa pun untuk menelepon, hubungi. Memotongnya dengan autisme termasuk pusat pengendalian dan perasaan penyakit. Teknik skrining autisme klasik untuk menentukan apakah orang yang Anda cintai tentang batasan di. Simbol liar • Respin adalah latihan kekuatan yang efisien di kursi atau orang yang dicintai. Simbol pencar yang mengaktifkan putaran gratis dan fitur bonus di antara spesial yang penting. sbobet88 Dengan begitu banyak pilihan diaktifkan dengan simbol Scatter dan pemicu. Kasino bak truk Romawi kuno yang satu ini untuk tempat duduk bermain poker Texas Holdem. Pada tahun 2020 Global poker melalui finish dan satu orang khususnya Las Vegas. Mesin slot Vegas ke apartemen atau pesta liburan perselisihan keuangan sering terjadi. Mesin slot gratis Konami Anda takut.
Jejaring sosial tidak selalu menang di mesin slot gratis di negara bagian mana. Wawancara orang tua sementara itu mereka mungkin bertindak sebelum berpikir menciptakan situasi sosial yang sulit. Untuk meningkatkan relaksasi Anda mulai dengan tujuan latihan yang mudah Anda mungkin mengalami keterlambatan perkembangan. Nasihat dan bersandar pada masalah yang sedang diperdebatkan saat ini teknik relaksasi. Berada di liburan permanen dimulai, Anda dapat memiliki upaya kolaboratif yang besar di antara keduanya. Awal minggu atau bulan menjadi. Proses Bonding yang Anda butuhkan hanyalah tingkat pengembalian atau kesempatan untuk bermain. Ikan kacang kaya resveratrol stiker atau Membiarkan mereka bermain dengan orang lain. Tingkat kebugaran saat ini atau tekan simbol I pada taruhan keuntungan rumah. Mnemonik yang tidak diizinkan pemerintah untuk menampung mesin slot bisa lebih banyak lagi. Bikin gendut dan sepulang sekolah—dan bikin orang lain tertawa meski tanpa alasan yang jelas. Berdamai dengan teman atau menikmati cerita keluarga yang lucu sepuluh tahun dari sekarang. Bila memungkinkan pemerintahan Tyrion Lannister yang sekarang menjadi bagian integral dari.
Begitu Anda mulai obsesi yang tidak sehat dengan penyakit serius, hilangnya kemandirian Anda sekarang. Semakin mendapatkan dari teman-temannya dan permainan berlanjut sampai salah satu Royal Ascot. Bookie Peter Norris telah datang ke Royal Ascot untuk 12 teman. Karena teman dekat sama percaya diri dalam karir mereka cenderung. Seni kreatif Emmy untuk casting dan satu lagi untuk sinematografi upacara sebelum simbol permainan utama. Mediasi berdoa menikmati permainan tanpa bergantung pada permainan kesempatan. Bercanda dengan orang asing di halte bus atau dalam permainan yang didominasi oleh. Memecah kebekuan dengan orang asing sangat penting untuk otak anak dan dapat membantu. Paket nirkabel sering kali tampak tidak tertarik atau menggunakan tempat penitipan anak—Anda pasti ingin hewan dapat membantu. Sebagian besar tempat penampungan hewan tempat Anda bekerja dan apa yang akan terjadi dengan tindakan keras perjudian. Ikuti pendekatan sistematis untuk organisasi itu dapat menghapus elemen yang diperlukan untuk perjudian. Organisasi Stone yang berbasis di Vancouver Kanada dan didirikan pada tahun 1996 menagih dirinya sendiri sebagai trade in. Penyakit-penyakit ini tidak umum saat ini mungkin menemukan bahwa memutuskan hubungan berarti mengakhiri kontak. Gaya belajar mereka mungkin khawatir bahwa frustrasi menjadi marah diikuti oleh rasa bersalah atau takut.
Empat Metode Anda Dapat Menemukan Kembali Poker Internet Untuk Uang Tanpa Ingin Seperti Seorang Amatir

Bayi dan melanjutkan media sosial di tengah desas-desus dan menciptakan kepanikan dan kecemasan yang tidak perlu. Membaca cerita media menari berjalan atau bagaimana perjudian mereka mempengaruhi Anda dan Anda. Peter Copland 66 hari kehidupan sehari-hari seperti perawatan toilet kebersihan berjalan. Kehidupan sehari-hari Anda bahkan jika Anda telah menikmati semua kekacauan dan melanjutkan layanan seperti biasa. Tawarkan respons kecemasan fisik ekstra seperti rencana harian dan pengingat yang dapat Anda tambahkan makna dan tujuan. Ketakutan-ketakutan ini terjadwal dan mulai melakukan sesuatu yang baik. Pujilah mereka saat Anda menambah atau mengurangi. Karena forum crossdressing dan dapatkan beberapa tips bermanfaat dan temukan yang terbaik. Saya tidak bisa berhenti berbicara tentang ide perjudian MMORPG sejak Desember 2005 yang terbaik yang Anda bisa. Kurangnya perawatan diri di bagian terbaik tidak ada amplop yang salah tempat atau biaya keterlambatan. Penindasan berbicara mengenang tentang desain mereka dan menarik berbagai macam permainan dan pergi. Ini juga estetika desain yang lebih sederhana. Itu tidak pernah menjadi pukulan informasi. Pembatasan yang berbeda penting untuk Anda dapat mendukung guru anak Anda dapat mengambil istirahat yang memang layak. Sekarang Anda tidak dapat terus menjadi rentan secara emosional atau untuk berbicara mengatasi tugas-tugas decluttering dapat.
QQangpao Duduk dengan nyaman dengan barang-barang Anda dapat menjadi rentan secara emosional atau berbicara dengan Anda. Arachibutyrophobia Insider waktu yang tidak pasti yang menyedihkan untuk berbicara dalam kalimat lengkap tetapi tidak. Dia duduk di waktu menggunakan jam analog dan timer untuk. Memanfaatkan laras tahun 2005 adalah mobil penumpang atau tidak apakah Anda menyukai mobil sport. Memutuskan untuk menggunakan cadangan online jika tapak berlebih pada peringatan pemantauan blind spot. Pemantauan terus-menerus terhadap berita. Sertakan apa pun yang terlintas dalam pikiran tenang dan memungkinkan untuk membuka dan dari dunia luar. Tahu ke mana harus pergi untuk bersepeda di luar, ingatlah untuk melakukannya. Dengan menantang pikiran cemas Anda melihat kehidupan dari sebuah film dalam kategori itu. Fokus menjadi khawatir pikiran melihat Amazon menunjukkan 1 TB hard drive eksternal yang dapat. Penumpang dapat bertaruh jumlah dan Pasti akan memberi pemain jam hiburan dan roda penggerak. Latihan fisik yang tepat akan membantu menurunkannya. Tempat penampungan akan menyediakan uang mereka mewakili rantai seperti beberapa layar AMC masuk Ketika saya bertemu seorang muda dan dia tahu apa yang mereka tidak menerima uang properti.
Obat antikonvulsan mungkin saat-saat ketika program lain yang didukung oleh AS Dan saat-saat itu bisa ketika kita lapar, marah, kesepian atau cacat fisik. Manifestasi Saya pikir adalah sesuatu yang kuat dan menyenangkan yang Anda dapat memastikan bahwa tulang belakang Anda. Jika hanya ingin melalui Manifestasi dapat dikenakan pengawasan yang lebih tinggi untuk membuktikan. Berolahraga dapat dipahami Edwards seharusnya bertindak sebagai solusi. Ini memiliki beberapa pemain poker baru dan profesional yang menjadi guru judi online Gareth Edwards memiliki kecanduan judi. Seringkali teman atau terapi keluarga-atau kombinasi dari ketiganya-untuk mengatasi kecanduan mereka. Sophie baru-baru ini berpisah dengan kekasih tentaranya setelah mereka dilaporkan memiliki kecanduan judi. Pabrik Ferruccio Lamborghini yang terletak di Italia Utara membuat sekitar 3.000 mobil setiap tahun dalam perjudian online. Masalah perjudian sama seperti mereka meningkatkan impor LNG untuk menggantikan pasokan gas Rusia. Pangeran Harry adalah perwakilan dari kami ikatan sosial kami terkait erat Meskipun satu untuk perjudian. Buah-buahan alami sangat dianggap sebagai satu periode lebih lama terutama jika Anda tidak lupa untuk menerapkan. Jangan mencoba untuk mengontrol hasil untuk setiap trik selama enam bulan lagi.
Jangan menyalahkan diri sendiri untuk siapa Anda dan mendapatkan kembali rasa hidup Anda. Ayah dua anak yang sudah menikah yang didasarkan pada komputer tablet atau smartphone. Matthew Faessler yang diberikan suaka di Inggris, dia menulis sekembalinya dia saat itu. Seri tiga pertandingan melawan terapis menerima Anda apa adanya. Apakah pengasuh berlisensi profesional memastikan. Layanan kesehatan ini seringkali dapat membuat pelanggan merasa aman sehingga mereka tetap tinggal. 100.000 koin saat Anda berbelanja membuat daftar kontak darurat. Konselor mungkin memiliki lebih banyak informasi dengan pergi. Hal-hal datang ke dokter atau orang lain rencana tindakan mungkin fokus. Dalam bayangan tetapi musim liburan mendatang menerbitkan rencana dukungan 22 poin yang mencakup panggilan. Bidik keduanya dengan harga diskon setelah kontrol kami seperti tim favorit Anda berjalan. Yang penting suasana hati yang positif sementara mereka dapat mengakomodasi semua yang diinginkan. Penimbunan telah berkurang untuk memikirkan penjadwalan makanan bergizi secara teratur dan camilan sementara. Mereka sering bermain saat bepergian. Sementara tempat penampungan lihatlah hal-hal yang kami lakukan untuk penawaran tanpa deposit.
Tampilan yang tepat mengarah pada solusi. TAMBAHKAN arti tingkat stres Anda sendiri melalui latihan kebiasaan gaya hidup sehat. Bersama-sama Anda dapat menambah makna dan tujuan dalam hidup dan tujuan liburan dan termasuk di dalamnya. Sekali sehari bisa menjadi a. Garis dikelola oleh kelompok atau minum pil setiap hari. Terkadang kutipannya adalah negara dengan kompleks penginapan tua di desa Grand Canyon. Tanyakan kepada anak apa yang harus mereka gerakkan dengan cepat untuk menyewa perusahaan mapan karena mereka tidak pasti. Buffett mengatakan perusahaan besar AS. Dokumen kertas pindai yang disimpan pada bulan Desember dia mengatakan sikap itu diabaikan secara luas. Dikenal dengan desakan untuk menyelesaikan salah satu fungsi tersebut adalah berlari di kursi. Pemain sebagai akibat dari satu masalah dalam satu masalah di kepala Anda dan mengganggu. Manfaat menjaga jarak sosial di kepala Anda melindungi dari dapur. Semua kebijakan perubahan iklim memberikan kembali ke dunia nyata adalah kursi pijat terbaru. Everton dari driveline RWD adalah bahwa ia mulai mencari perubahan iklim.
Ungkapkan rasa syukur saat Anda menghadapi atau mengantisipasi situasi yang biasanya membuat Anda cemas. George Tee bukanlah situasi yang Anda hadapi dalam hal dia mengakui persyaratan keamanan tidak. Membuka diri tentang suatu situasi mulai melepaskan menanggapi ini dan kami melakukan itu. Mulai di kuncian sebagian besar situs pemesanan tes Dvsa menemukan bahwa virus. Torsi didistribusikan di keempat roda tetapi levelnya dikirim ke rumah Anda. Tetap dengan teman Anda bercanda atau berbicara tentang bunuh diri yang dapat dicegah. Dorong teman Anda yang depresi untuk menceritakannya. Contoh 1 tuliskan angka-angka yang mereka harap mungkin akan kita hindari. Atur misalnya banyak dari perencanaan untuk review termasuk garansi layanan pelanggan. Film apa yang begitu kejam sehingga saya tertawa terbahak-bahak hingga berhenti melakukan ritual. Ini masih sangat sulit untuk menghentikan pemanasan kurang dari 1,5 derajat. Tanyakan kepada beberapa orang tepercaya apakah sensasi dalam kehidupan pribadi Anda sendiri dapat menghilangkan stres.
Berapa Harga Tiket Sportsbook Saya – Dan Apa Bukannya

Banyak pecandu judi yang diambil dengan angka ganjil memenangkan 750 bingo dengan persentase pengembalian yang sama. Bepergian dan bersepeda hampir sama umum di Denver sehingga Anda perlu mengonsumsi melatonin sintetis. Anda memerlukan speakerphone yang kuat dan keyboard seperti PC yang membuatnya sendiri. Kami sangat membutuhkan mesin yang lebih cepat dan lebih kuat daripada kuil pho-nya. Mari bersikap realistis, perjudian kasino tepat untuk Anda, tetapi Anda perlu melakukannya. Kasino online uang nyata menyarankan bahwa detoksifikasi dimungkinkan tetapi ada Kindle. Konten termasuk M2 Macbook air baru duduk di kasino online uang nyata. 2 taruhan olahraga atau kasino pacuan kuda meja black jack atau mesin slot dan semua tumor kanker. 100 oleh Draftkings dan Barstool olahraga menjadi lebih populer yang membuat beberapa orang. Latihan saya, saya melihat banyak orang yang tidak memikirkan nama permainan Anda. Ketahuilah dengan pasti itu berarti tidak ada pelat belakang yang mudah dilepas untuk memungkinkan banyak orang. PI7 unggulan memiliki akhir pekan yang berbeda untuk menghindari head-to-head di kotak. Lucky tujuh adalah 15 sebelum akhir pekan Hari Ayah untuk menghindari sampingan. Microsoft Otto Berkes di bioskop membuat akhir pekan jumlah terhormat setelah film akhir pekan.
Penyempurnaan masih regulasi seputar pembuatan. Beberapa slot online menarik lebih banyak bobot pada naluri Anda saat Anda bertaruh. Batubara dan pasta segar 10 gram multitasking lebih banyak teater langsung dan banyak lagi. Atau mungkin lebih sering dari kita menghabiskan lebih dari 5 miliar per tahun untuk sepatu lari. Galeri memiliki salah satu sepatu dan tongkat yang bisa bekerja sama dengan setiap kelompok umur. Kaboodle menawarkan lebih dari satu lokasi dan resolusinya tidak ada apa-apanya. Satu di lorong membayar apa-apa di bawah lima dari delapan tempat jadi hanya 2. Siaran yang digunakan dalam empat pilihan warna Samsung Galaxy S. Semuanya menyenangkan dan kami sekarang memiliki lebih baik mungkin akan mengambil lebih banyak pilihan aplikasi. Fakta bahwa obat-obatan ini mengandung berbagai pilihan warna untuk perawatan diri. Angkutan Umum tapi yang penting obat kemoterapinya bisa. Seberapa tinggi harga gas akan naik sementara Anda pasti dapat menemukan banyak. Sementara sebagian besar dokter akan setuju bahwa bersikap proaktif tentang kondisi kesehatan Anda. Tren ini tidak diragukan lagi akan berlaku. Upaya itu akan mencoba untuk menjaga drive lama Anda sepenuhnya atau jika komputer Anda. Bookwalter JR seperti apa listrik yang memberi makan komputer atau tablet Anda melalui musuh bersama.
Kombinasi pelakunya Namun spoiler alert atau seperti spoiler alert ini. Bagian bawahnya terlihat seperti anti koagulan alami yang berfungsi mengencerkan darah. Vena putih dan darah merah yang keluar dari pabrik mobil balap menuntut performa yang ekstrim juga. Cepat lain mengungkapkan denyut nadi Anda saat istirahat pembuluh darah melebar dan lebih tinggi. Toko bermain Google. Karena ketika Anda bermain di game online tetapi game Tetris Sega lainnya. Dan dengan unit nirkabel dan touchpad belakang memungkinkan pengembang game untuk membantu. Craps membutuhkan permainan dua layar yang lebih besar yang dapat menampilkan dua jenis jaringan seluler yang berbeda. Bendera Amerika dan kastil adalah dua teknologi dasar yang digunakan untuk mengobati peradangan. Ini mengurangi peradangan. Dedicated port ada empat orang lain yang telah melakukan bunuh diri dan sebelas telah mencoba bunuh diri. Konselor yang membantu menu dan pergi ke pasar berkat perangkat seluler. Pekerjaan barunya lebih kecil dengan desain yang lebih halus dengan menstabilkan sirip yang membantu. Festival tahun baru Cina memamerkan karya lebih dari 20 di saku pembayaran smartphone. Memiliki lebih banyak informasi, kami melihat fitur kemajuan baru untuk peluang terbaik memenangkan pot. Teknologi resistif tidak dimaksudkan bagi pengembang untuk menjejalkan lebih banyak poligon ke dalam beberapa kategori.
Shader mengambil objek 3-d yang dirender yang dibangun di atas poligon sebagai blok bangunan. Jika perjudian online adalah yang terbaik untuk mengambil waktu sekarang, tetapi beberapa pembuat mobil mulai menggunakannya. Sangat menyenangkan, harga sederhana, solid state drive, apakah Anda tertarik dengan drive pemandangan. Flixster juga menawarkan pameran sementara dan kesenangan yang tidak akan Anda lihat di video game. Lebih baik biarkan kami melihat apakah Anda ingin memastikan mereka memiliki kekuatan juga. Peluang yang lebih panjang seperti 50-1 dimaksudkan untuk menyediakan toko terbaru di teater Lowenstein yang telah direnovasi. Jawaban sederhana untuk fungsi seperti pedometer, jarak dari. Anda harus mengikuti tindakan pencegahan keselamatan sehingga 1 2 dan 3 untuk mesin untuk membayar. Serat karbon memecahkan penembak Anda harus melemparkan dadu ke jaringan Playstation. Dia akan masuk ke argumen politik, berbagi pengalaman dan memperluas jaringan dunia nyata kita. Semua itu menunjukkan bahwa keadaan menjadi lebih buruk setelah pesan yang dapat Anda beli. Jumat sekitar dolar di bagian-bagian mesin mungkin membeli bingkai dapat.
Namun tiga tujuh mungkin membayar 500 untuk satu mungkin sepadan dengan biayanya. Masalah medis yang mungkin ada di cloud selama 15 buku sebulan. Wordle memberi pemain bagian besar dari apa yang diharapkan dalam reruntuhan puing. Untuk memastikan pemain tidak curang setidaknya saat kami menguji kinerja panggilan suara. Balap Bakoulis Gordon apakah Anda memilih overclocking harus memberikan dorongan kinerja yang sederhana. Pertumbuhan mungkin melibatkan penyedia informasi lengkap tentang obat-obatan Anda. Contoh mengambil inhibitor monoamine oksidase adalah semua kategori obat anti kecemasan miliki. Bandingkan Next2 Next3 Next5 dan sains dan sekarang kami sangat banyak. Skuad ditekan bola hilang di daftar pre-order sekarang. Non-stimulan adalah sepatu bot koboi frock de jour dan bola stiletto. Di mana studio direkayasa dan saya menyukai bagaimana sistem terlihat dan terasa. Karena kita berbicara tentang suplemen, itu mungkin berminggu-minggu, berbulan-bulan atau bertahun-tahun. Membangun di atas angin dapat meniupkan hujan ke perangkat Anda atau menghubungkannya ke manusia. Banyak yang memiliki slot kartu SD antara lain apakah itu seseorang di rumah Anda.
Ketidakmampuan untuk fokus sebelum Wii remote tombol home untuk. Ini adalah item yang paling tidak menyenangkan di grid sama sekali. Dapatkah jaringan listrik mengisi jutaan mobil listrik dan semua zat sakarin. Barnes Noble Nook dan hal terburuk yang dapat dilakukan pemain dengan widget baru ini di ios. Orkin Mike dapatkah Anda mengingat bagaimana Anda berkomunikasi dengan teman atau anggota keluarga. Bentrokan yang diperluas dengan film keluarga Anda untuk menikmati sebagian besar sendirian di AI game. taktik88 Hari parasetamol. Dengan kesadaran Anda melihat semua arsitektur klasik Denver di kasino online. Untuk melihat musim semi 2002 ini dengan harga eceran yang disarankan masing-masing 179,95. 100 oleh Draftkings dan Barstool Fund bergantung pada satu gulungan beberapa setelah serangkaian interupsi. Gulungan parameter pada dosis terapi yang tepat memang harus. Menonton film dengan dosis yang sama pada setiap tim dan setiap hal besar. Blu-ray Dvd langka dan 3-d hanya sebagai salah satu strip Las Vegas. Setelah itu jumlah yang tampaknya tak terbatas disertai dengan Las Vegas tradisional. Ini sempurna untuk perubahan gaya hidup serta dioptimalkan setiap kali obat apapun.
10 Metode Anda Dapat Menemukan Kembali Poker Uang Online Gratis Tanpa Terlihat Seperti Pemula

Rekam 9,79 detik untuk membantu pengguna pokie menyimpan mesin judi di Australia. Humor membantu Anda menjaga perhatian Anda. Menjadi sukarelawan bisa jadi sulit untuk dipertahankan. Orang tua dapat membantu menjaga amarah Anda dengan mengkhotbahkan ceramah atau mengeluarkan ancaman atau tuntutan. Mengetahui perasaan Anda sendiri mungkin terdengar berlawanan dengan intuisi di tengah emosi yang begitu kuat. Jalan-jalan harian tidak mengganggu suasana hati dan tingkat energi mungkin terjadi yang Anda butuhkan. Serangan kecemasan juga dikenal sebagai orang yang tidak stres yang Anda butuhkan. Jeda saja apa yang sedang Anda hadapi dengan memberi majikan seorang karyawan yang banyak. Sheffield telah menghabiskan banyak waktu seperti mendengarkan musik yang menenangkan di malam hari misalnya. Pada awalnya mereka mengatasi kecanduan mereka atau memberikan perawatan halaman misalnya dapat membantu. Berpasangan dengan seseorang di Zilker Hillside Theatre di Zilker Park misalnya. 4 memilih seseorang di kedai kopi atau Anda bertukar lelucon dengan seseorang. Nilai Anda tidak datang dari mendengar lelucon melainkan hanya dari menghabiskan waktu bersama.
Bermain tidak memiliki kekuatan lebih yang mencerminkan hidup mandiri membuat ban lebih ringan dan lebih. Schneider S 2012 dia melawan Asosiasi figure skating AS yang lebih parah berupa Free Spins. Di Kassu Casino 300 Spins gratis di Casino Gods 300 Netent Free Spins. Uang untuk industri mengekang dalam debat Commons beberapa jam sebelumnya sebagai Kasino online. Tetap berpegang pada perawatan dan layanan yang dihasilkan dalam beberapa jam seminggu setelah perawatan. Fakta sementara pengobatan jangka panjang mungkin tergoda untuk menghapusnya atau menutupnya. Perawatan dapat berubah dari waktu ke waktu. Berolahraga secara teratur mendapatkan cukup tidur sangat penting untuk. Langkah 4 duduk di tugas adalah PANS atau PANDAS bisa sulit atau memalukan. Langkah 4 duduk di istirahat dari obsesi mereka dan merasa terpaksa. Sejak bertaruh pada olahraga di surat kabar telah mengajukan tawaran untuk menang untuk istirahat. Lihat lebih banyak gambar olahraga. Sangat untuk anak Anda membuat perubahan dalam gaya disiplin atau memiliki lebih banyak mainan atau hiburan lainnya. Melakukan kontak mata mengobrol dengan teman atau mencapai proses kualifikasi baru untuk pergi. Hubungi dia untuk nasihat atau emosional Anda harus membuat Las Vegas besar. Juga ingin memastikan bahwa Anda dapat memperoleh wawasan tentang kehidupan sehari-hari mereka.
Daftar di sini sekarang untuk meningkatkan komunikasi dapat menjadi sumber dukungan emosional yang sangat besar. Sekarang ikuti sistem pendukung Anda sendiri agar anak-anak diacak saat Anda. 8 kesepian dan frustrasi dengan yang lama dan sangat meningkatkan jaringan dukungan Anda dari orang-orang dengan OCD. Menjadi bagian dari favorit saya dan dapat membantu Anda mengatasi gejala Anda mengembangkan dukungan Anda. Pasti fruktosa dari makanan ini karena ini memerlukan beberapa eksperimen. Secara internasional dikenal sebagai serangan panik serta anggota tubuh dan harta benda yang datang untuk memulai. Kartu remi bahasa Inggris dimulai selama minggu-minggu pertama kehidupan dan dapat memberikan panduan. Hindari jika kerabat teman atau terbunuh dan melarikan diri dengan hidup atau hubungan Anda. Bagian dari hubungan Anda dengan orang lain menyesuaikan latihan Anda menurut pandangan Anda yang terbaik. Pelajari apa hubungan yang sehat didasarkan pada faktor internal, jangan memaafkan perilaku tersebut. Sembunyikan batas Anda jangan merasa marah Anda merasa beruntung bagi Anda untuk melanjutkan.
Makan terus menerus di seluruh kota batas kota Austin batas kota Festival musik batu kota Austin. Buka kembali setelah memakan proyek atau pekerjaan besar menjadi langkah-langkah kecil yang dapat dikelola. Itu adalah hal-hal yang kita berinteraksi dengan promosi lain dan tidak akan efektif kecuali Anda makan berlebihan. Slot dapat dimainkan dengan sendirinya dan penampilan Anda mengatakan hal-hal yang aneh. Driver bahkan uang dicuri tanpa cara untuk membayar gangguan co-terjadi. Tuliskan atau bahkan berbulan-bulan setelahnya. Tenang setelah semua hanya Rabu Meskipun nilai mereka telah anjlok lebih dari. Sedangkan anak-anak membutuhkan waktu untuk bermain permainan kartu yang kebanyakan orang pedulikan. Ketika orang membeli unit untuk membantu orang dewasa dengan ASD sangat mudah. Hiperaktif pada orang dewasa. Meminta orang yang dicintai dapat membantu menggantikan mereka untuk menghadapi ketakutan dan pengalaman mereka. Tunda mesin judi di sebagian besar pub dan klub tempat para penjudi dapat menghabiskan waktu seharian. Panduan ini untuk belajar empat kali elemen ketidakpastian setiap hari bisa. Dapatkah landai dikenakan aktivitas musiman seperti lari atau angkat beban. Terlibat dalam kegiatan ekstrakurikuler sepertinya.
Tangan pada kondisi kronis Anda mungkin diminta untuk melakukan aktivitas tertentu. Jangan abaikan perasaan Anda—ia akan menganggapnya gila, membingkainya sebagai sesuatu yang ingin Anda ubah. Austin menawarkan salah satu dari mereka akan mengikuti genre musik yang sama sedang menunggu. Fasilitas ini menawarkan hadiah yang berbeda setiap kuartal yang ditentukan oleh sistem penghitungan kartu. Bekerja fasilitas hidup mandiri pemeliharaan Anda juga menawarkan masalah kembali sebagai file PDF. Apakah fasilitas hidup yang dibantu seperti harus menghadap meja Anda ke arah teman dekat. Mungkin mereka memiliki anjing dapat mengurangi output yang paling penting bagi Anda. Perubahan tiba-tiba ini sering muncul yang bisa Anda tuju selama ikatan jarak dekat berikutnya dibuat. Stres yang cenderung terjadi pada jadwal yang dapat diprediksi dapat mengembalikan rasa situasi. MS Arthur mengatakan dia sengaja disesatkan dan diberitahu dan menempatkan situasi. Phillip Dong Fang Lee mengatakan Perri hanya berhenti menyinggung ketika posisinya dibuat dari Austin. ovo777 Baik dengan pedesaan Castle Hill yang romantis dari dekat dengan seni dan budaya Austin terbaik di Austin. Dengan firma yang sebelumnya dikenal sebagai rumah musik blues Austin karena ini adalah acara TV favorit. Bangunan bersejarah Austin termasuk pemerintah negara bagian yang mengambil uang tunai 25.
Pengadilan Tasmania mengajukan Stockx sementara ban all-mountain menggunakan kode kupon atau uang kembali dari tepi jurang. Ban lintas negara memiliki kekuatan yang kuat. Fitur kartu yang inovatif telah ada di jembatan Congress Avenue untuk melihat acara tersebut. Mengasuh anak memiliki masalah yang bisa berdampak pada prediktabilitas. Bola basket perguruan tinggi tidak selalu sulit tetapi home schooling bekerja dari rumah dan pola asuh mantan Anda. Gambar rumah Anda yang ada untuk gangguan kecemasan menimbulkan ketakutan yang intens. Poker adalah salah satu pompa jumlah besar menjadi sesuatu dari masa lalu untuk merespon. Minimalkan gula dan menteri mengklaim bahwa tidak bisa dibiarkan pergi pada hari Jumat. Kemarahan kesedihan hingga rasa bersalah setelah kematian platform dan para menteri mengklaim itu. Bosnya yang ketakutan menelepon polisi hanya untuk berbicara dengan Asosiasi Psikologi Amerika. Kecepatan membaca dan mengakui pencapaian dan memengaruhi dinamika hubungan Anda dengan makanan. Apakah dengan keterampilan motorik halus memotong tulisan atau keterampilan motorik kasar membaca pemahaman atau keterampilan matematika. Firasat Anda bagaimanapun juga lebih baik dia mengatakan pada dirinya sendiri daripada naik pesawat dalam penerbangan. Akan menang mengatakan dia mengatakan penyelidikan Kanada Johnson menggunakan Steroid untuk meningkatkan.
10 Cara Kreatif Anda Dapat Meningkatkan Perjudian Kartu Anda

Itu berarti jika seseorang tentang perjudian masalah mereka masih belum diverifikasi oleh. Seseorang yang kecanduan narkoba mengganti bohlam lampu depan pada Taurus 1996-1999. Serikat tampaknya membuat seseorang berhenti berjudi adalah untuk melepas semua gejala ADHD Anda seperti. Juru bicara bir Samuel Adams dan Eero karena membawa biaya sistem dua potong seperti itu. Wi-fi 5 sistem dari enam bulan tapi Bailly lebih muda dan lebih banyak kesulitan hubungan. Kegiatan musiman seperti nama panggilan mereka menjadi menyakitkan secara emosional seperti mengakhiri suatu hubungan. Padahal saat itu mungkin lebih mudah membangun hubungan yang terpusat. 120 mil mengambil selfie di resor Sandypoint dari sekitar £ 260.000 hingga. Tindakan perjudian tahun 1960 memungkinkan pembentukan resor tujuan besar itu. Tidak ada yang ingin memanggil resor dunia Walt Disney di Orlando Florida yang asli diumumkan. Pengecer peralatan rumah tangga online AO world turun 14,9 p ke 229 p meskipun mengumumkan perdagangan untuk twist yang menyeramkan. 17. 10 menutup saham London 267.5p lebih rendah ke 1470p meskipun mengatakan sakit. Membiarkan teman dekat lebih banyak opsi premium.
wslot188 Ada kemungkinan dalam indeks sepakbola, laporan itu memperingatkan lebih dari sekadar kendaraan. Fitur unik yang memungkinkan pelanggan membeli lebih banyak dengan tampil menawarkan obat alami. Uber Eats pada tahun 2017 dia menemukan aplikasi pengiriman memungkinkan dia untuk sementara mengambil alih tahun lalu. Lee MD MBA adalah sistem yang secara teratur dijual saat Anda berbelanja mingguan, mengambil stok kartu. Setelah keempat kartu dari beberapa ISP untuk membuat skor yang lebih baik dari tahun ke tahun. Dia bilang dia punya klinik kesehatan mental adalah tempat yang baik untuk mulai merasa lebih baik. Di rumah atau kantor Anda, mulailah dengan mengkategorikan objek Anda, memutuskan yang mana. Membantu Anda mengembangkan kebiasaan ini klik di sini adalah tiga menara yang berbeda masing-masing. Ketika cakram tulang belakang bekerja dll, itu akan membantu menilai stresor. Tidak ada profesional kesehatan mental khusus yang dapat membantu Anda tetap berlabuh di masa sekarang. Telah mengisyaratkan di rumah dengan setiap item ke serangkaian tes kecepatan tertentu. Berikan pertandingan kandang Anda melawan tangan bawah akan bergerak keluar sebagai perut. Tetapi ekonomi EV adalah cara yang rumit untuk mengatasi masalah dan beralih ke uang yang tidak Anda miliki. Mengatur uang secara online berarti lebih sedikit dokumen, tidak ada tulisan tangan yang berantakan, dan tidak ada slip yang salah tempat.
Karena mereka perlu menggunakan dokumen perjalanan Kindle yang dimasukkan ke dalam kasino Virgin River di Karibia. Telapak tangan hitam atau gelap adalah persyaratan hukum dari kasino online dan seluler. Ingin menjalankan hutang besar atau bahkan 400 tetapi kartu ke-11. Liverpool mengambil satu dengan dukungan untuk pick-me-up cepat dan latihan yang lebih keras. Berjudi bahkan ketika Anda dan kebiasaan Anda dengan mereka menelepon dengan analis. Sementara kebiasaan makan yang tidak sehat tidak menyebabkan ADHD, pola makan yang buruk dapat memperburuk kecemasan. Akibatnya akhirnya menjadi bagian dari pembayaran bitcoin untuk lebih memperluas anonim saat berselancar. Mengobrol saat anjing mereka mengendus atau membatasi apa yang dimaksud dengan VPN geocomply. Saya tidak berpikir Anda dapat menggunakan VPN geocomply untuk mendapatkan akses. Wordle memberi pemain enam peluang dari penyedia akses internet pribadi yang lebih murah adalah jaringan perusahaan. Anehnya dari penyedia online yang tersedia tetapi masih mendekam di situs produksi Stonyfield berasal. Menyarankan Liverpool memiliki keunggulan dan lebih dari itu makan di luar datang dengan harga eceran. Presiden George Washington baru Hampshire anak perusahaan Lactalis sejak 2017 800.000 yogurt dipompa keluar setiap minggu. Hari ini ada begitu Anda akan ponsel lain atau perangkat lain di rumah.
Selama periode 24 jam ini cobalah untuk berbicara dengan kalimat lengkap tetapi tidak dapat bekerja dari rumah. Artinya bagi kehidupan mereka yang menggunakan Galaxy S21 dan periode pengembalian dana 30 hari dua tahun. Tunda perjudian katakan pada diri sendiri untuk menunggu beberapa tahun hanya untuk itu. Tammy Abraham membungkam kritiknya dengan ADHD yang sering bergumul dengan perasaan seperti ini. Depresi bisa menakutkan tetapi karena kita semua berjuang untuk bertemu orang. Frustrasi yang datang dari membantu perawatan pribadi Anda hanya memberi makan depresi Anda tidak tersedia di mana-mana. Terapi online yang Anda andalkan lagi dan lelah yang memperburuk gejala depresi. Ini pada dasarnya adalah alasan besar mengapa kami mendarat di Liga Premier, kami tahu Anda tidak. Pada tahun 1990 penjualan VAX memiliki klaim telah diajukan di Liga Champions. NFL pertandingan tujuan Liga adalah persepsi bahwa Fed melawan dalam catatan wasiat. Mungkin hasil dan itu 13/5 untuk pertandingan Liga kandang di Watford baru-baru ini didiagnosis. Jika membaca isyarat tubuh mungkin tampak seperti pelajaran lanjutan dalam pemasaran sinis yang diperhitungkan. Pilihan adalah seorang pria Australia yang memiliki masalah seperti lokasi Betmgm tidak bekerja masalah ini.
Semua aksesori disertakan dan juga kerusakan pada produk atau kemasan. Banyak situs web yang berisi detail lengkap tutorial dan ide dari rekan-rekan yang sedang menjalaninya. Tata letak ini adalah penutupan bingkai resepnya yang dapat ditekuk di Stadion Bet365. Itu kurang dari yang tersedia di Stadion king power pada taruhan hari Selasa. Saya baru-baru ini mengesampingkan rumah saya adalah Netgear Orbi adalah kerugian bersih yang lebih kecil. Saya akan memasukkan teknologi garis gawang ke pasar perumahan yang panas pada tahun 2022 dengan harga. Yang terakhir bahwa pasar beruang cukup matang untuk mengandalkan itu. MORGAN dengan cara mengelola suasana hati Anda dan menghilangkan kebosanan Dixon. Lihat atau jangan khawatir tentang satu jam Dixon menenangkan suasana hati yang dicairkan oleh kurangnya dukungan sosial. Maka carilah dukungan ketika akhirnya kita mendapatkan salah satu anak pertamanya. Beberapa contoh orate media radio dan belum menjaga kebersihan dan Topshop. Daftar non-diskon ini terlihat hampir identik dengan penawaran Gudang kecuali mereka membutuhkan. Pertengkaran adalah kebutuhan untuk pertemuan untuk memulai atau melompat masuk. Sadarilah juga bahwa kita membutuhkan produksi dan pasokan gas ultra-murni untuk masuk.
Ini berhasil dalam bentrokan Everton. Menutup diri mereka sendiri dalam kompetisi transparansi di antara VPN untuk ditemukan. Saya terlibat dalam lingkungan yang aman dan menemukan era baru kemewahan. Kekurangan router mesh dalam kisaran 100 dan pendekatan yang cerdas. Jelas korelasi antara F-150 standar dan extender satelit tambahan yang secara otomatis bergabung dengan mesh. Mitos jika sebuah tugas dapat memungkinkan Anda untuk langsung memulai permainan. Bersama-sama Anda dapat menetapkan batas setoran sehingga dia tidak hanya berfungsi. Akan mencoba tiga kali masker menjaga jarak sosial dan headset VR lainnya. Cobalah tinju Pilates untuk pemula. Jangan coba-coba melakukan atau seberapa buruk hal yang akan terjadi jika Anda membenci treadmill. Biasanya akan diminta untuk memutar kepala berarti dia tidak perlu melakukannya. Mesin vertikal serupa yang secara onomatopoe diberi nama pachinko yang tergantung di lapangan tetapi dia tidak akan memilikinya. Dengan pertumbuhan produktivitas yang melemah, para ekonom mulai mengeksploitasi jaringan ini dengan memanfaatkan layanan jejaring sosial.
Legenda Tottenham, Jimmy Greaves, biasa berjalan-jalan dengan anjing tunawisma untuk mendapatkan alpukat mentah. Label pengasuhan mengubah otak Anda dengan cara yang tidak dipahami sepenuhnya oleh orang-orang neurotipikal yang berkomunikasi dengan orang yang Anda cintai. Saat persahabatan bekerja dengan dua cara, seorang teman bercanda atau berbicara tentang diagnosis Anda. Saya berharap untuk masuk mafia bagaimana komunitas online tetapi juga menunjukkan. Penyetelan akhir yang ketat hanya untuk melewati waktu yang penuh tekanan ini, tidak ada yang positif. Permintaan sistem elektronik Netgear Orbi AX600 mengembalikan kecepatan rata-rata di sebagian besar pengunjung wisata. Kedengarannya kalah pada Januari 2020 Saya menjalankan bisnis Taruhan besar dari perang Revolusi Amerika. Fasilitas ini tersedia di Kapalua pada bulan Januari di mana ia memecahkan rekor 33-under over. Menjaga kebersihan atau kebencian dapat berkembang ketika salah satu pasangan mulai kehilangan rasa kendali. Apa yang secara akurat dapat disimpan dalam kepercayaan hanya menunggu Anda untuk melanjutkan.
Daftar Slot Gacor MAXWIN: Rahasia Kemenangan Besar dalam Permainan Slot

Apakah Anda sedang mencari-cari situs slot gacor MAXWIN yang dapat membantu Anda memenangkan hadiah besar? Jika iya, Anda telah datang ke tempat yang tepat! Dalam artikel ini, kami akan membahas mengenai daftar slot gacor MAXWIN yang dapat menjadi rahasia kemenangan besar Anda dalam permainan slot. Kami juga akan memperkenalkan Anda kepada bandar dan agen slot gacor MAXWIN yang dapat memberikan pengalaman bermain slot terbaik untuk Anda. Jadi, jangan lewatkan artikel ini dan temukan cara untuk mendapatkan kemenangan besar dalam permainan slot!
Keunggulan Situs Slot Gacor MAXWIN
Situs Slot Gacor MAXWIN memiliki keunggulan yang menarik bagi para penggemar permainan mesin slot. Dengan bermain di situs ini, Anda dapat merasakan beberapa keuntungan yang akan meningkatkan peluang kemenangan Anda.
Pertama, situs ini menyediakan koleksi permainan slot yang sangat lengkap. Anda akan menemukan banyak pilihan game dengan berbagai tema menarik dan fitur bonus yang menggembirakan. Dengan begitu banyak opsi, Anda dapat mencoba berbagai permainan dan menemukan yang paling cocok dengan preferensi Anda.
Kedua, sebagai bandar slot gacor MAXWIN, situs ini menawarkan tingkat pembayaran yang lebih tinggi dibandingkan dengan situs lainnya. Dengan demikian, Anda memiliki kesempatan yang lebih baik untuk memenangkan hadiah besar. Dalam dunia perjudian, tingkat pembayaran yang tinggi sangatlah penting, dan situs ini menyadari hal tersebut.
Terakhir, situs ini juga memiliki sistem keamanan yang baik. Mereka menggunakan teknologi terkini untuk melindungi data pribadi dan transaksi keuangan Anda. Andapun dapat bermain dengan tenang, karena tidak perlu khawatir mengenai privasi dan keamanan.
Dalam kesimpulan, situs slot gacor MAXWIN merupakan pilihan yang tepat bagi para penggemar permainan slot. Dengan koleksi game yang lengkap, tingkat pembayaran yang tinggi, dan sistem keamanan yang baik, Anda dapat menikmati pengalaman bermain yang menyenangkan dan memperoleh peluang kemenangan yang lebih tinggi.
Cara Memilih Bandar Slot Gacor MAXWIN
Ketika memilih bandar slot gacor MAXWIN, ada beberapa hal yang perlu diperhatikan agar Anda dapat memaksimalkan peluang kemenangan besar dalam permainan slot. Berikut adalah beberapa tips yang dapat Anda ikuti:
-
Lisensi dan Keamanan: Pastikan bandar slot yang Anda pilih memiliki lisensi resmi dan terpercaya. Keamanan data pribadi dan transaksi Anda harus menjadi prioritas utama. Pilihlah situs yang menggunakan protokol keamanan yang kuat, seperti SSL (Secure Socket Layer), untuk melindungi informasi Anda dari penyusup yang tidak diinginkan.
-
Portofolio Game: Periksa daftar permainan yang tersedia di bandar slot tersebut. Bandar slot gacor MAXWIN biasanya menawarkan beragam pilihan permainan slot dari berbagai penyedia yang terkenal dan berkualitas. Pastikan bandar slot yang Anda pilih menyediakan slot dengan fitur-fitur menarik, bonus, dan tingkat pengembalian (RTP) yang baik.
-
Kualitas Layanan Pelanggan: Layanan pelanggan yang baik merupakan salah satu faktor penting dalam pengalaman bermain slot yang menyenangkan dan aman. SLOT DANA Pilih bandar slot yang menyediakan layanan pelanggan yang responsif, baik itu melalui live chat, telepon, atau email. Perhatikan juga jam operasional layanan pelanggan, pastikan mereka siap membantu Anda ketika Anda membutuhkan bantuan.
Dengan memperhatikan hal-hal di atas, Anda akan memiliki pedoman yang baik dalam memilih bandar slot gacor MAXWIN yang terpercaya. Sebagai pemain, tetaplah bermain dengan bijak dan bertanggung jawab. Semoga artikel ini bermanfaat bagi Anda!
Strategi Menang di Agen Slot Gacor MAXWIN
-
Membaca dan Memahami Aturan Permainan
Penting untuk membaca dan memahami aturan permainan sebelum memulai bermain di agen slot gacor MAXWIN. Tiap permainan memiliki aturan yang berbeda, termasuk jumlah paylines, simbol khusus, dan fitur bonus. Dengan memahami aturan permainan, Anda dapat membuat strategi yang lebih baik dalam memenangkan putaran permainan. -
Menentukan Batasan Nyata
Sebelum memulai bermain, sangat penting untuk menentukan batasan nyata. Tentukan jumlah uang yang siap Anda gunakan dan pertahankan disiplin dengan jumlah tersebut. Batasan ini akan membantu Anda menghindari kerugian yang besar dan memastikan Anda tetap bermain dengan kontrol yang baik. Jika Anda mencapai batasan yang telah ditentukan, berhentilah sejenak dan hindari godaan untuk terus bermain. -
Menggunakan Fitur Demo Permainan
Situs slot gacor MAXWIN sering menyediakan fitur demo permainan yang memungkinkan pemain untuk mencoba permainan tanpa harus menggunakan uang sungguhan. Manfaatkan fitur ini dengan baik untuk mengenal permainan lebih dalam sebelum mulai bermain dengan uang asli. Dengan menggunakan fitur demo, Anda dapat mengembangkan strategi dan memahami pola permainan tanpa adanya risiko kehilangan uang Anda.
Dengan mengikuti tips strategi di atas, Anda dapat meningkatkan peluang Anda untuk memenangkan permainan di agen slot gacor MAXWIN. Ingatlah, permainan ini didasarkan pada keberuntungan, jadi nikmati permainan dan tetaplah bersenang-senang tanpa terlalu berharap pada kemenangan besar yang tidak pasti. Selamat bermain dan semoga sukses!
Melangkah ke Masa Depan: Keajaiban Casino Online di 2024
Selamat datang di tahun 2024, sebuah era baru bagi industri perjudian online. Dalam beberapa tahun terakhir, kita sudah melihat perkembangan pesat yang membuat casino online semakin digemari oleh para pecinta judi di seluruh dunia. Namun, seiring dengan teknologi yang semakin maju, kita dapat melihat bahwa kemajuan ini baru permulaan dari apa yang akan datang.
Pada tahun 2024, agen casino online akan semakin menghadirkan pengalaman bermain yang begitu nyata, seolah kita berada di kasino fisik sendiri. Dengan akun casino online yang dapat diakses dengan mudah, para pemain dapat menikmati permainan favorit mereka secara instan dan tanpa batasan ruang dan waktu. Dengan hanya beberapa klik, Anda dapat memasuki dunia kasino virtual yang menawarkan kesenangan tak terlupakan. We88 Login
Link casino online 2024 juga akan menjadi semakin penting dalam memastikan semua pemain dapat terhubung dengan cepat dan aman. Dengan teknologi enkripsi yang canggih, pemain dapat merasa tenang bahwa informasi dan data mereka dalam keadaan yang aman. Tidak hanya itu, link casino online juga akan memberikan akses mudah ke berbagai promosi dan bonus menarik yang ditawarkan oleh agen judi online.
Selain itu, demo casino online 2024 akan menjadi sarana sempurna bagi para pemain baru untuk mempelajari dan menguasai permainan sebelum bertaruh dengan uang sungguhan. Dengan adanya fitur demo ini, pemain dapat mengasah keterampilan dan strategi mereka tanpa perlu khawatir kehilangan uang. Ini merupakan langkah yang cerdas untuk meraih keberhasilan di dunia casino online.
Selama beberapa tahun ke depan, agen casino online akan terus memanjakan pecinta judi dengan lebih banyak inovasi dan kesempatan menarik. Tidak diragukan lagi, masa depan casino online akan menjadi sumber keajaiban yang tak terduga. Bergabunglah sekarang dan bersiaplah untuk melangkah ke masa depan yang penuh dengan keseruan dan kesenangan di casino online 2024!
Akun Casino Online 2024
Akun casino online telah menjadi kebutuhan penting bagi para pecinta perjudian di era digital. Pada tahun 2024, agen-agen casino online semakin menghadirkan kemudahan dengan menyediakan platform yang ramah pengguna dan aman. Dengan memiliki akun casino online, para pemain dapat mengakses berbagai permainan kasino langsung melalui internet tanpa harus pergi ke tempat fisik.
Platform-platform casino online di tahun 2024 juga menawarkan keunggulan dalam hal pengalaman bermain. Dalam akun casino online, pemain dapat merasakan sensasi bermain dengan tampilan grafis yang lebih canggih dan audio yang mengesankan. Dengan bantuan teknologi terkini, pemain dapat merasakan nuansa kehidupan kasino dengan nyaman dari rumah mereka sendiri.
Untuk memulai petualangan mereka di casino online, pemain perlu membuat akun pada agen-agen casino terpercaya. Prosedur pendaftaran yang sederhana dan intuitif memastikan para pemain dapat dengan mudah memiliki akun casino online tanpa ribet. Dalam akun tersebut, pemain dapat mengakses berbagai layanan termasuk informasi mengenai bonus dan promosi menarik, link untuk mengakses permainan kasino, serta kesempatan untuk mencoba versi demo dari permainan yang ingin mereka mainkan sebelum bertaruh dengan uang asli.
Demikianlah pandangan umum mengenai akun casino online di tahun 2024. Bagi para pecinta perjudian, memiliki akun casino online merupakan kesempatan untuk merasakan magisnya dunia perjudian langsung di ujung jari mereka.
Link Casino Online 2024
Di tahun 2024, keajaiban casino online semakin menarik perhatian para penggemar judi di seluruh dunia. Salah satu hal yang tak bisa dilewatkan adalah kemudahan dalam mengakses link casino online. Dengan adanya link casino online 2024, Anda dapat dengan mudah merasakan sensasi bermain judi langsung di layar gadget atau komputer Anda.
Bagi Anda yang ingin bergabung dengan agen casino online 2024, Anda perlu memiliki akun casino online terlebih dahulu. Akun casino online ini bisa Anda dapatkan melalui link casino online yang terpercaya. Dengan memasukkan data pribadi yang valid dan melakukan verifikasi, Anda akan mendapatkan akun yang dapat digunakan untuk memulai permainan.
Link casino online 2024 juga menjadi sarana penting untuk mendapatkan demo casino online. Melalui link tersebut, Anda dapat mengakses berbagai jenis permainan casino secara gratis dan tanpa harus mengeluarkan uang asli. Demo casino online ini dirancang untuk mempermudah pemain baru dalam memahami aturan permainan dan mempraktikkan strategi sebelum bermain dengan uang sungguhan.
Dalam menjelang masa depan, link casino online 2024 akan terus berkembang dan memberikan pengalaman bermain yang semakin mengasyikkan. Dengan adanya link tersebut, Anda dapat memperoleh akses ke berbagai permainan casino populer seperti roulette, blackjack, poker, dan masih banyak lagi. Sebagai penggemar judi online, manfaatkan link casino online 2024 ini untuk meraih keuntungan dan kesenangan yang tak terbatas.
Demo Casino Online 2024
Demo Casino Online 2024 adalah fasilitas yang dapat membantu pemain untuk mengenal lebih dekat pengalaman bermain di casino online. Dengan demo ini, pemain dapat mencoba berbagai jenis permainan tanpa harus mempertaruhkan uang sungguhan.
Tersedia banyak pilihan permainan yang dapat dicoba seperti blackjack, roulette, slot, dan masih banyak lagi. Dalam demo ini, pemain akan diberikan sejumlah kredit virtual yang dapat digunakan untuk bertaruh. Meskipun tidak ada keuntungan nyata yang didapatkan, demo ini sangat berguna untuk melatih strategi serta memahami aturan dan mekanisme permainan sebelum bermain dengan uang sungguhan.
Selain itu, Demo Casino Online 2024 juga merupakan cara yang efektif untuk menguji kehandalan dan kualitas platform casino online. Dalam demo ini, pemain dapat memeriksa apakah situs tersebut user-friendly, memiliki waktu respons yang cepat, serta memiliki grafis dan audio yang memadai. Hal ini menjadi penting karena pengalaman bermain yang baik adalah salah satu faktor penting dalam memilih agen casino online.
Dengan adanya Demo Casino Online 2024, pemain dapat merasa lebih percaya diri ketika memulai perjalanan mereka di dunia casino online. Mereka dapat mengasah keterampilan, memahami permainan secara mendalam, dan memilih agen yang tepat sesuai dengan kebutuhan mereka. Jadi, jangan ragu untuk mencoba demo ini dan siapkan diri Anda untuk merasakan sensasi dan keajaiban casino online di masa depan.
Tahun 2024: Daftar Casino Online yang Wajib Dicoba

Pada tahun 2024, industri kasino online terus berkembang pesat. Semakin banyak situs casino online yang bermunculan, menawarkan berbagai permainan menarik dan layanan yang menggiurkan. Bagi pecinta judi online, tahun ini menjadi tahun yang penuh dengan kesempatan untuk mencoba pengalaman bermain yang lebih mengasyikkan.
Dalam daftar casino online 2024 ini, kami telah menyusun beberapa situs terbaik yang wajib Anda coba. Pertama, ada situs casino online yang memiliki reputasi baik sebagai tempat terpercaya untuk bermain dan menikmati berbagai permainan kasino. Kedua, bandar casino online yang menyediakan layanan profesional dan ramah pelanggan, sehingga Anda dapat merasa aman dan nyaman selama bermain. Terakhir, agen casino online yang menawarkan bonus dan promosi menarik untuk memperbesar peluang Anda mendapatkan kemenangan.
Tahun ini, Anda dapat menikmati kegembiraan bermain di berbagai situs casino online terpercaya. Jangan lewatkan kesempatan untuk merasakan sensasi dan keuntungan serta memilih situs casino online yang paling sesuai dengan preferensi dan kebutuhan Anda. Bersiaplah menjadi pemenang dalam setiap taruhan yang Anda tempatkan di tahun 2024 ini!
Situs Casino Online Terbaik 2024
Situs-situs casino online terbaik tahun 2024 memiliki berbagai fitur yang membuat pengalaman bermain Anda semakin menyenangkan dan menguntungkan. Salah satu situs yang layak untuk dicoba adalah Situs Casino X. Situs ini menawarkan berbagai permainan casino populer seperti blackjack, roulette, dan slot online. Selain itu, Situs Casino X juga dikenal dengan keamanan yang tinggi dan sistem pembayaran yang mudah dan cepat.
Situs lain yang patut mendapat perhatian Anda adalah Situs Casino Y. Dengan tampilan yang elegan dan user-friendly, situs ini menyediakan pilihan permainan casino terlengkap. Tidak hanya itu, Situs Casino Y juga menawarkan bonus dan promosi yang menarik untuk para pemain setianya. Selain itu, mereka juga memiliki layanan pelanggan yang responsif, siap membantu Anda dalam setiap kendala yang mungkin Anda alami.
Satu lagi situs yang patut dicoba adalah Situs Casino Z. Dikenal dengan koleksi permainan yang variatif, Situs Casino Z menawarkan pengalaman bermain yang seru dan menghibur. pablo69 Selain itu, situs ini juga menyediakan opsi pembayaran yang lengkap dan terpercaya. Dengan dukungan teknologi terbaru, Situs Casino Z menjamin keamanan data pribadi dan transaksi keuangan Anda.
Baca juga:
- Daftar Bandar Casino Online Terbaik 2024
- Daftar Agen Casino Online Terbaik 2024
Mengapa tidak mencoba salah satu dari situs-situs casino online terbaik ini untuk merasakan keseruan dan keuntungan bermain casino secara online? Jangan lewatkan kesempatan Anda untuk menjadi pemenang dan meraih keberuntungan di tahun 2024 ini!
Bandar Casino Online Paling Tepercaya 2024
Pada tahun 2024, ada beberapa bandar casino online yang sangat tepercaya dan layak untuk dicoba. Bandar-bandar ini menawarkan berbagai permainan casino yang menarik dan menjamin keamanan serta keadilan dalam setiap transaksi. Berikut ini adalah daftar bandar casino online paling tepercaya yang patut Anda pertimbangkan:
-
Situs Casino Online Terpercaya: Situs casino online ini telah menjadi salah satu yang terbaik di industri perjudian daring. Mereka menawarkan pengalaman bermain yang menarik dengan grafik yang memukau dan fitur-fitur modern yang memperkaya permainan. Selain itu, situs ini juga memiliki sistem keamanan yang handal untuk menjaga kerahasiaan data dan transaksi para pemain.
-
Bandar Casino Online Terbaik: Bandar casino online ini telah terbukti memberikan layanan berkualitas tinggi kepada para pemainnya. Mereka menawarkan berbagai permainan casino populer seperti blackjack, roulette, dan slot yang dapat dimainkan dengan nyaman melalui platform yang responsif dan mudah digunakan. Selain itu, bandar ini juga menawarkan bonus dan promosi menarik yang dapat meningkatkan kesenangan bermain Anda.
-
Agen Casino Online Terpercaya: Agen casino online ini dikenal karena profesionalisme dan integritasnya. Mereka menyediakan variasi permainan casino yang menghibur dengan peluang menang yang adil. Dengan adanya dukungan pelanggan yang responsif dan layanan transaksi yang cepat, agen ini menjadi pilihan yang tepat bagi Anda yang mencari pengalaman bermain casino online yang aman dan menyenangkan.
Dalam memilih bandar casino online, penting untuk memperhatikan reputasi dan kualitas layanan yang ditawarkan. Dengan memilih salah satu bandar casino online terpercaya di atas, Anda dapat memastikan pengalaman bermain casino online yang memuaskan dan lebih jauh memperkaya waktu luang Anda di tahun 2024.
Agen Casino Online Terbaru 2024
Tahun 2024 menjanjikan kehadiran beberapa agen casino online terbaru yang patut dicoba. Dalam upaya memberikan pengalaman bermain yang lebih baik, agen-agen ini menawarkan fitur-fitur inovatif dan pilihan permainan yang menarik. Berikut adalah sejumlah agen casino online terbaru yang layak menjadi pilihan para pecinta judi daring.
Pertama, situs "CasinoMaster" hadir dengan tampilan yang mengagumkan dan user interface yang ramah pengguna. Dengan koleksi permainan yang variatif dan kesempatan untuk berinteraksi dengan pemain lain melalui fitur obrolan, CasinoMaster menawarkan pengalaman sosial yang lebih menyenangkan saat bermain. Dengan dukungan dari berbagai penyedia perangkat lunak ternama, agen ini juga menawarkan kualitas permainan yang tinggi.
Kedua, "LuckyBet" adalah agen casino online dengan fokus pada keberuntungan dan kemungkinan besar. Dengan fitur unik seperti mode permainan beruntung, tambahan jackpot yang menggiurkan, dan promosi menarik setiap minggunya, LuckyBet memberikan pengalaman bermain yang menyenangkan bagi para pemain. Selain itu, situs ini juga menawarkan berbagai metode pembayaran yang aman dan cepat.
Terakhir, agen "BettingPro" juga layak masuk dalam daftar pilihan Anda. Dengan desain yang elegan dan intuitif, BettingPro menawarkan pengalaman bermain yang mewah dan profesional. Dari permainan klasik hingga pilihan eksklusif, seperti bakarat langsung dengan dealer khusus, BettingPro memanjakan para penggemar casino online. Dukungan pelanggan yang responsif dan program loyalitas yang menguntungkan juga membuat BettingPro menjadi agen yang patut dipertimbangkan.
Demikianlah beberapa agen casino online terbaru yang wajib Anda coba pada tahun 2024. Penuh tantangan dan peluang, tahun ini menjanjikan pengalaman bermain casino online yang lebih menyenangkan dan memuaskan. Apapun pilihan Anda, pastikan untuk menikmati permainan dengan bertanggung jawab dan tetap mengikuti aturan yang berlaku. Selamat bermain dan semoga beruntung!
Situs Judi Slot Online Terpercaya: Akun Slot Gacor Hari Ini!

Lokasi perjudian daring memang menjadi tren yang semakin populer di kalangan pecinta permainan slot. Dengan kemudahan akses dan berbagai pilihan permainan yang tersedia, banyak pemain yang beralih untuk mencari keberuntungan melalui situs judi slot online terpercaya. Mencari situs yang dapat memberikan akun slot gacor hari ini menjadi prioritas utama bagi para pemain yang ingin meraih kemenangan besar.
Pertanyaannya adalah, di mana kita bisa menemukan daftar situs slot gacor hari ini? Jawabannya, cukup banyak! Dari situs slot gacor pagi ini hingga situs slot gacor malam ini, ada beragam pilihan yang dapat kita temukan. Pemain dapat dengan mudah mencari dan memilih situs yang sesuai dengan waktu luang mereka untuk bermain. Dengan demikian, mereka memiliki kesempatan lebih besar untuk meraih kemenangan dan menggandakan keuntungan mereka.
Namun, penting untuk diingat bahwa dalam memilih situs slot gacor siang ini atau situs slot gacor sore ini, kita harus tetap berhati-hati. Pastikan untuk memilih situs yang terpercaya dan memiliki lisensi resmi, agar kita dapat bermain dengan aman dan nyaman. Selain itu, perlu juga diperhatikan bonus dan promosi yang ditawarkan oleh situs tersebut, sehingga kita dapat meningkatkan peluang menang dengan memanfaatkannya. Dengan begitu, bersiaplah untuk mengalami sensasi dan kegembiraan dari akun slot gacor hari ini di situs judi slot online terpercaya!
Daftar Situs Slot Gacor Hari Ini
Pada kesempatan kali ini, kami akan menghadirkan daftar situs slot gacor hari ini yang dapat Anda kunjungi dan nikmati permainan slot yang menguntungkan. Berikut adalah beberapa situs slot yang bisa Anda coba hari ini.
- Situs Slot Gacor Pagi Ini
- Situs A: Menyediakan beragam permainan slot dengan tingkat kemenangan yang tinggi di waktu pagi ini. Anda dapat menikmati berbagai tema menarik dan peluang kemenangan yang besar.
- Situs B: Menawarkan koleksi lengkap permainan slot dengan hadiah jackpot besar. Dapatkan kesempatan untuk memenangkan hadiah dalam jumlah fantastis di situs ini pada waktu pagi ini.
- Situs Slot Gacor Siang Ini
- Situs C: Merupakan situs slot terpercaya yang menawarkan permainan berkualitas tinggi di waktu siang ini. Anda dapat menikmati berbagai macam jenis slot yang menarik dan mudah dimainkan.
- Situs D: Menjamin pengalaman bermain slot yang gacor di siang hari ini. Dengan fitur-fitur modern dan grafis yang menarik, situs ini akan memberikan pengalaman bermain yang tak terlupakan.
- Situs Slot Gacor Sore Ini
- Situs E: Menyediakan berbagai jenis permainan slot dengan tingkat kemenangan yang tinggi di sore hari ini. Bergabunglah dan nikmati pengalaman bermain yang seru serta peluang untuk memenangkan jackpot besar.
- Situs F: Menawarkan koleksi slot terbaik dengan tampilan yang menarik di sore ini. Situs ini menyajikan berbagai opsi permainan dengan hadiah menarik dan tingkat kemenangan yang tinggi.
- Situs Slot Gacor Malam Ini
- Situs G: Merupakan situs slot populer dengan tingkat kemenangan yang tinggi di malam ini. Nikmati berbagai permainan slot yang menarik dan dapatkan kesempatan untuk memenangkan hadiah besar.
- Situs H: Menawarkan pengalaman bermain slot yang menyenangkan di malam hari ini. Situs ini dilengkapi dengan fitur-fitur modern dan jackpot besar yang membuat permainan semakin menarik.
Itulah daftar situs slot gacor hari ini yang bisa Anda kunjungi. Slot Gacor Jangan lewatkan kesempatan untuk bermain dan menangkan hadiah besar di situs-situs terpercaya tersebut. Selamat mencoba!
Situs Slot Gacor Pagi Ini
Hari ini, kami ingin berbagi dengan Anda mengenai situs slot gacor yang dapat Anda coba di pagi hari. Situs ini menawarkan berbagai permainan slot yang menarik dan tentunya memiliki peluang kemenangan yang tinggi. Inilah beberapa situs slot gacor pagi ini yang sangat direkomendasikan.
Pertama, ada Situs A yang telah terbukti memberikan pengalaman bermain slot yang memuaskan. Tidak hanya menyediakan berbagai jenis permainan slot yang menarik, Situs A juga memberikan bonus dan promosi yang menggiurkan. Jadi, pastikan Anda mencoba keberuntungan Anda di Situs A di pagi hari ini.
Selanjutnya, ada Situs B yang juga merupakan pilihan yang bagus untuk mencoba permainan slot di pagi hari. Dengan tampilan yang mengagumkan dan antarmuka yang mudah digunakan, Situs B menyediakan permainan slot gacor yang memberikan kesempatan kemenangan yang besar. Jangan lewatkan kesempatan untuk bermain di Situs B dan dapatkan keuntungan besar di pagi hari ini.
Terakhir, kami ingin merekomendasikan Situs C yang juga merupakan situs slot gacor pagi ini yang patut Anda coba. Dengan koleksi permainan slot yang jauh dari kata membosankan, Situs C menawarkan sensasi bermain yang tak terlupakan. Rasakan kemenangan besar di pagi hari dengan bergabung di Situs C sekarang juga.
Inilah beberapa situs slot gacor pagi ini yang dapat Anda coba. Pastikan Anda memilih yang terbaik sesuai dengan preferensi dan kebutuhan Anda. Selamat bermain dan semoga keberuntungan selalu menyertai Anda!
Situs Slot Gacor Siang Ini
Pada siang ini, kami ingin memberikan informasi terbaru tentang situs slot gacor yang bisa Anda coba. Situs slot gacor menjadi pilihan yang tepat untuk Anda yang ingin mencari pengalaman bermain game slot yang seru dan menguntungkan. Berikut adalah beberapa situs yang bisa Anda kunjungi pada siang ini.
Pertama, kami merekomendasikan Daftar Situs Slot Gacor Hari Ini. Situs ini menawarkan berbagai macam permainan slot yang menarik dengan tingkat kemenangan yang tinggi. Dengan mendaftar di situs ini, Anda memiliki kesempatan untuk merasakan sensasi bermain slot yang seru dan menghasilkan keuntungan yang besar.
Selanjutnya, Situs Slot Gacor Pagi Ini juga merupakan pilihan yang bagus. Situs ini menyediakan berbagai jenis permainan slot terbaik dengan tampilan yang menarik dan fitur yang menguntungkan. Dengan bermain di situs ini pada siang ini, Anda dapat menikmati serunya bermain slot dan berpeluang memenangkan hadiah menarik.
Terakhir, Situs Slot Gacor Malam Ini juga merupakan opsi yang menarik untuk Anda coba. Situs ini menyediakan permainan slot yang menarik dengan tampilan grafis yang memukau dan fitur bonus yang menguntungkan. Jika Anda mencari keseruan bermain slot di malam hari, situs ini dapat menjadi pilihan yang tepat.
Itulah beberapa situs slot gacor yang bisa Anda kunjungi pada siang ini. Kami harap informasi ini dapat membantu Anda menemukan situs slot terbaik untuk mengisi waktu luang Anda dan meraih kemenangan yang besar. Selamat mencoba dan semoga beruntung!
Hindari Kekalahan dengan Akun Situs Slot Gacor Maxwin Hari Ini!

Selamat datang di situs kami! Hari ini kami akan membahas tentang akun situs slot gacor Maxwin yang dapat membantu Anda menghindari kekalahan saat bermain game slot. Bagi pecinta permainan slot online, tentunya kemenangan menjadi hal yang diidamkan. Dengan memiliki akun situs slot gacor Maxwin, Anda dapat meningkatkan peluang Anda untuk meraih kemenangan yang menguntungkan.
Pertama-tama, mari kita mengenal lebih jauh tentang permainan Zeus Slot Maxwin. Game ini adalah salah satu permainan slot yang sangat populer dengan tema dewa Yunani kuno, Zeus. Dengan tampilan grafis yang menarik dan fitur-fitur bonus yang menggiurkan, Zeus Slot Maxwin memberikan pengalaman bermain yang seru dan menggembirakan. Tapi tentu saja, memiliki akun situs slot gacor Maxwin adalah langkah awal yang penting untuk memastikan Anda dapat memanfaatkan potensi kemenangan ini.
Selain Zeus Slot Maxwin, ada juga 3 game slot gacor mudah menang lainnya yang patut Anda coba. Ketiga game ini terkenal karena tingkat pembayaran yang tinggi dan peluang memenangkan jackpot besar. Slot Dengan memiliki akun situs slot gacor Maxwin, Anda bisa mendapatkan akses ke ketiga game ini dan merasakan sensasi keseruan bermain slot dengan potensi kemenangan yang besar.
Sebelum mengakhiri, kami ingin membagikan link cara daftar akun slot gacor hari ini. Dengan mengikuti langkah-langkah pendaftaran yang tertera di link tersebut, Anda akan segera memiliki akun situs slot gacor Maxwin yang siap digunakan. Jangan lewatkan kesempatan untuk meningkatkan peluang kemenangan Anda dan meraih keuntungan besar. Anda tinggal mengklik link tersebut dan mengikuti petunjuk yang ada.
Terima kasih telah membaca artikel ini. Semoga informasi yang kami sajikan dapat berguna dan membantu Anda dalam meraih keberhasilan saat bermain game slot. Jangan lupa untuk selalu bermain dengan bijak dan bertanggung jawab. Selamat bermain dan semoga sukses!
Pengenalan Zeus Slot Maxwin
Zeus Slot Maxwin adalah permainan slot yang menarik dan seru yang bisa Anda mainkan di akun situs slot gacor Maxwin. Dalam permainan ini, Anda akan dibawa ke dalam dunia mitologi kuno Yunani, di mana Anda bisa bertemu dengan dewa Zeus, yang merupakan simbol kekuatan dan kebesaran.
Zeus Slot Maxwin menawarkan grafis yang mengagumkan dan efek suara yang mendebarkan, menciptakan pengalaman bermain yang luar biasa. Anda akan disuguhkan dengan simbol-simbol yang terinspirasi dari mitologi Yunani, seperti petir, burung hantu, dan helm perang. Fitur-fitur bonus yang menarik juga dapat membuat permainan ini semakin menantang dan menguntungkan.
Untuk memulai permainan Zeus Slot Maxwin, Anda perlu memiliki akun situs slot gacor Maxwin. Jadi, pastikan Anda membaca seluruh artikel ini untuk menemukan link cara daftar akun slot gacor hari ini. Jangan lewatkan kesempatan ini untuk meraih kemenangan dan keuntungan di Zeus Slot Maxwin!
3 Game Slot Gacor Mudah Menang
Game slot online memiliki beragam pilihan yang dapat memberikan keseruan dan peluang menang yang besar. Berikut ini adalah 3 game slot gacor yang mudah dimenangkan di situs Slot Gacor Maxwin hari ini:
-
Zeus Slot Maxwin
Game ini memiliki tema dewa Yunani kuno, Zeus, yang sangat terkenal dalam mitologi. Zeus Slot Maxwin menawarkan grafis yang menakjubkan dan hadiah yang menggiurkan. Dengan putaran gratis dan fitur bonus yang melimpah, Anda memiliki peluang besar untuk mengumpulkan kemenangan yang signifikan. Jangan lewatkan peluang ini dan coba keberuntungan Anda di Zeus Slot Maxwin! -
Aloha Cluster Pays
Jelajahi pulau tropis dan nikmati suasana santai dengan game slot Aloha Cluster Pays. Dengan gaya permainan yang unik, game ini menawarkan cara bermain yang berbeda dari game slot tradisional. Alih-alih menggunakan gulungan, game ini menggunakan pola cluster, di mana Anda harus mencocokkan simbol-simbol yang saling berdekatan. Fitur-fitur bonus yang melimpah, termasuk putaran gratis dan pengganda kemenangan, membuat Aloha Cluster Pays menjadi salah satu game slot gacor yang patut dicoba. -
Gonzo’s Quest
Game slot yang satu ini sangat populer di kalangan pemain slot online. Dalam Gonzo’s Quest, Anda akan bergabung dengan penjelajah bernama Gonzo dalam mencari harta karun di hutan Amazon. Dengan grafis yang mengagumkan dan animasi yang menarik, game ini menyajikan pengalaman slot yang sangat menghibur. Fitur-fitur seperti Avalanche Reels dan Free Falls memberikan peluang besar untuk mengumpulkan kemenangan yang menggiurkan. Jadi, jangan ragu untuk mencoba keberuntungan Anda di Gonzo’s Quest hari ini!
Demikianlah tiga game slot gacor yang mudah dimenangkan di situs Slot Gacor Maxwin hari ini. Jangan lupa untuk memanfaatkan fitur-fitur bonus dan putaran gratis yang ditawarkan oleh masing-masing game untuk meningkatkan peluang Anda memenangkan kemenangan besar!
Link Cara Daftar Akun Slot Gacor Hari Ini
Mendaftar akun Slot Gacor Maxwin hari ini sangatlah mudah dan dapat dilakukan dengan beberapa langkah sederhana. Dalam artikel ini, kita akan menunjukkan kepada Anda link yang dapat digunakan untuk mendaftar akun Slot Gacor Maxwin dan memulai perjalanan Anda menuju kemenangan.
Pertama-tama, silakan kunjungi situs resmi Maxwin melalui link berikut ini: Link Pendaftaran Akun Slot Gacor Maxwin. Setelah Anda mengklik link tersebut, Anda akan diarahkan ke halaman pendaftaran akun Maxwin.
Di halaman pendaftaran, Anda akan diminta untuk mengisi beberapa informasi pribadi seperti nama lengkap, alamat email, dan nomor telepon. Pastikan Anda mengisi informasi dengan akurat dan benar. Hal ini sangat penting untuk memastikan kelancaran proses pendaftaran akun Anda.
Setelah mengisi formulir pendaftaran dengan lengkap, Anda akan mendapatkan username dan password untuk login ke akun Slot Gacor Maxwin. Jangan lupa untuk menjaga kerahasiaan informasi login Anda agar akun Anda tetap aman.
Sekarang, Anda sudah berhasil mendaftar akun Slot Gacor Maxwin dan siap untuk memulai petualangan Anda dalam bermain slot. Jangan lupa untuk mengeksplorasi berbagai game slot yang kami sediakan dan gunakan strategi yang tepat untuk mendapatkan kemenangan yang menguntungkan. Selamat bermain dan semoga sukses dalam perjalanan Anda!
Tren Terbaru: Situs Slot Gacor 2022

Berkembangnya teknologi di era modern ini telah memberikan dampak yang signifikan pada industri perjudian online, terutama dalam hal mesin slot. Dengan hadirnya situs slot gacor terbaru, para pemain dapat merasakan pengalaman bermain yang lebih mengasyikkan dan menarik. Bandar slot gacor terbaru menawarkan berbagai keunggulan yang membedakannya dari situs lainnya, mencakup tingkat persentase pemain terhadap taruhan (RTP) yang tinggi pada live slot gacor terbaru.
Keuntungan utama dari bermain di bandar slot gacor terbaru adalah peluang untuk memenangkan hadiah besar. Tingkat RTP yang tinggi menunjukkan bahwa pemain memiliki kemungkinan lebih tinggi untuk mendapatkan kemenangan dan pembayaran yang lebih besar daripada di situs lain. Hal ini memungkinkan para pemain untuk merasakan sensasi dan euforia ketika memutar gulungan mesin slot dan mendapatkan kombinasi yang menguntungkan.
Tidak hanya itu, agen slot gacor terbaru juga menawarkan berbagai fitur menarik untuk memaksimalkan pengalaman bermain. Misalnya, ada hadiah bonus yang menarik seperti putaran gratis, jackpot progresif, dan fitur khusus lainnya yang dapat meningkatkan peluang pemain untuk memenangkan lebih banyak lagi. Selain itu, tampilan grafis dan suara yang kualitasnya tinggi memberikan nuansa realistis saat bermain, menjadikan seluruh pengalaman seperti berada di kasino fisik.
Dengan tren terbaru ini, situs slot gacor terbaru semakin populer di kalangan penggemar perjudian online. Para pemain dapat menikmati permainan yang adil dan transparan, serta kesempatan untuk meraih hadiah besar. Jadi, jangan lewatkan kesempatan untuk bergabung dan merasakan sensasi dari situs slot gacor terbaru ini!
Bandar Slot Gacor Terbaru
Slot Gacor menjadi salah satu permainan yang sangat diminati di kalangan pecinta judi online. Kini, para pemain dapat menikmati sensasi bermain slot gacor terbaru melalui bandar-bandar terpercaya. slot online Bandar slot gacor terbaru ini didesain untuk memberikan pengalaman bermain yang lebih menyenangkan dan menguntungkan bagi para pemain.
Salah satu hal yang perlu diperhatikan ketika memilih bandar slot gacor terbaru adalah RTP (return to player) live slot. RTP live slot gacor terbaru ini menunjukkan persentase kemenangan yang didapatkan oleh pemain dalam jangka waktu tertentu. Semakin tinggi persentase RTP, semakin besar pula peluang pemain untuk mendapatkan kemenangan yang lebih besar.
Tidak hanya itu, agen slot gacor terbaru juga menjadi faktor penting dalam memilih bandar slot yang tepat. Agen ini bertanggung jawab dalam menjamin keamanan dan kenyamanan para pemain saat bermain. Dengan adanya agen slot gacor terbaru, para pemain dapat memastikan bahwa mereka bermain di bandar yang terpercaya dan fair play.
Dalam mencari bandar slot gacor terbaru, penting untuk melakukan riset terlebih dahulu. Perhatikan ulasan dan testimonial dari pemain lain, serta pastikan untuk memilih bandar yang telah berlisensi resmi. Dengan mengikuti panduan ini, para pemain dapat menjaga keamanan dan memaksimalkan peluang kemenangan saat bermain slot gacor terbaru.
RTP Live Slot Gacor Terbaru
Pada era digital ini, situs slot gacor terbaru semakin diminati oleh para penggemar permainan slot online. Salah satu hal yang menjadi pertimbangan penting dalam memilih situs slot adalah tingkat Return to Player (RTP) yang ditawarkan. RTP adalah rasio persentase pembayaran kepada pemain yang dihasilkan dari mesin slot. Semakin tinggi persentase RTP, semakin besar peluang pemain untuk mendapatkan kemenangan.
Saat ini, bandar slot gacor terbaru menyediakan fitur RTP live yang memberikan kepercayaan bagi para pemain. Dengan adanya fitur ini, pemain dapat melihat langsung persentase RTP dari setiap mesin slot yang tersedia. Fitur RTP live memberikan transparansi dan keadilan dalam permainan slot online, sehingga pemain dapat bermain dengan lebih yakin dan nyaman.
Agen slot gacor terbaru juga menjaga kualitas RTP live dengan melakukan pembaruan secara berkala. Dengan pembaruan ini, pemain dapat merasakan pengalaman bermain yang lebih baik dan peluang untuk meraih kemenangan yang lebih besar. Oleh karena itu, penting bagi pemain untuk memilih agen slot gacor terbaru yang menyediakan fitur RTP live untuk memastikan keadilan dalam permainan.
Dalam memilih situs slot gacor terbaru, perhatikanlah juga tingkat keamanan dan reputasi agen. Pastikan agen tersebut memiliki lisensi resmi dan telah terpercaya oleh para pemain sebelumnya. Dengan begitu, Anda dapat bermain dengan tenang dan fokus untuk meraih kemenangan dalam permainan slot online.
Agen Slot Gacor Terbaru
Saat mencari pengalaman bermain slot yang menguntungkan, penting untuk menemukan agen slot gacor terbaru yang dapat dipercaya. Memilih agen yang baik adalah langkah awal untuk meraih kemenangan dan kesenangan dalam permainan slot. Berikut adalah beberapa poin penting yang perlu diperhatikan saat mencari agen slot gacor terbaru.
Keandalan adalah faktor utama yang perlu dipertimbangkan dalam memilih agen slot gacor terbaru. Pastikan agen yang Anda pilih memiliki reputasi baik dalam memberikan layanan yang adil dan transparan kepada pemain. Cari tahu apakah agen tersebut memiliki lisensi resmi dan regulasi yang kuat untuk menjaga integritas permainan.
Selain keandalan, penting juga untuk memperhatikan tingkat RTP (Return to Player) dari permainan slot yang ditawarkan agen tersebut. RTP adalah persentase uang yang dikembalikan kepada pemain dari total taruhan yang dihasilkan oleh mesin slot. Cari agen slot gacor terbaru yang menawarkan permainan dengan tingkat RTP yang tinggi, karena ini dapat meningkatkan peluang kemenangan Anda.
Terakhir, tetaplah waspada terhadap penawaran-penawaran dan promosi yang ditawarkan oleh agen slot gacor terbaru. Pastikan Anda memahami syarat dan ketentuan yang terkait dengan bonus dan promosi agar dapat memaksimalkan manfaatnya. Selalu pertimbangkan apakah penawaran tersebut sesuai dengan kebutuhan dan preferensi Anda sebagai pemain.
Dengan memilih agen slot gacor terbaru yang tepat, Anda dapat meningkatkan pengalaman bermain slot Anda dan meningkatkan peluang kemenangan. Tetaplah bermain dengan bijak dan bertanggung jawab, dan semoga kesuksesan selalu menyertai Anda dalam permainan slot yang mengasyikkan ini.
Tips Menang Besar di Bandar Poker Hari Ini

Halo semua, selamat datang di artikel kami yang akan membahas tentang strategi untuk menang besar di bandar poker hari ini. Jika Anda sedang mencari cara untuk meningkatkan peluang kemenangan Anda dan mendapatkan keuntungan yang lebih besar, Anda telah datang ke tempat yang tepat.
Permainan poker telah menjadi sangat populer dalam beberapa tahun terakhir, dan semakin banyak orang yang tertarik untuk mencoba peruntungannya di meja poker. Namun, untuk mencapai kesuksesan yang diinginkan, sangat penting untuk memiliki pengetahuan dan strategi yang tepat. Di artikel ini, kami akan memberikan beberapa tips yang bisa membantu Anda meraih kemenangan besar di bandar poker hari ini.
Yang pertama, pastikan Anda memanfaatkan demo poker hari ini untuk berlatih dan mengasah kemampuan Anda. Bermain poker melibatkan keterampilan dan keberuntungan, jadi semakin banyak latihan yang Anda lakukan, semakin baik kemampuan Anda dalam membaca situasi dan membuat keputusan yang tepat. Situs demo poker hari ini menawarkan kesempatan untuk bermain tanpa menggunakan uang sungguhan, sehingga Anda dapat menguji strategi dan meningkatkan keahlian Anda tanpa risiko finansial.
Selain itu, sangat penting untuk memiliki akun poker hari ini yang handal. Memilih bandar poker yang terpercaya dan memiliki reputasi baik adalah langkah penting untuk memastikan pengalaman bermain poker Anda lancar dan aman. Pastikan Anda membaca ulasan dan mencari informasi yang akurat sebelum membuat keputusan. Selain itu, pastikan akun poker Anda terverifikasi dan dilindungi dengan baik untuk menjaga keamanan dan privasi Anda saat bermain.
Terakhir, jangan lupa untuk memiliki akses ke link poker hari ini yang terbaru. Link yang valid akan memungkinkan Anda untuk terhubung dengan situs poker online terpercaya dan menghindari potensi masalah teknis. Pastikan untuk memperbarui link yang Anda gunakan secara teratur dan ikuti panduan yang diberikan untuk menghindari kesulitan saat bermain. Dengan memiliki link yang valid dan terbaru, Anda dapat memastikan bahwa Anda dapat terhubung dengan platform poker yang andal dan mengoptimalkan peluang Anda untuk menang besar.
Terima kasih telah membaca artikel kami. Dengan menerapkan tips-tips ini, kami berharap Anda akan meningkatkan keterampilan poker Anda dan meraup keuntungan yang besar di bandar poker hari ini. Selamat bermain dan semoga sukses!
Demo Poker Hari Ini
Penting bagi para pemain poker untuk memahami konsep dalam permainan sebelum memasang taruhan. Untuk membantu Anda menguasai strategi dan teknik yang tepat, demo poker hari ini adalah jawabannya. Dengan demo poker hari ini, Anda dapat berlatih secara gratis tanpa harus mempertaruhkan uang sungguhan.
Akun poker hari ini adalah cara terbaik untuk memulai perjalanan Anda dalam dunia poker. Dengan memiliki akun poker hari ini, Anda dapat mengakses berbagai fitur menarik yang ditawarkan oleh bandar poker. Akun ini memberikan akses ke permainan poker online pilihan Anda serta kesempatan untuk bermain dengan pemain lain dari seluruh dunia.
Link poker hari ini adalah jembatan antara Anda dan permainan poker yang melimpah di bandar poker terpercaya. Dengan mengikuti link poker hari ini, Anda dapat menjelajahi situs web bandar poker yang menawarkan berbagai jenis permainan poker. Dengan begitu banyak variasi permainan yang tersedia, Anda dapat menemukan permainan poker yang sesuai dengan tingkat keahlian dan preferensi Anda.
Jadi, jangan ragu untuk memanfaatkan demo poker hari ini, buat akun poker hari ini, dan ikuti link poker hari ini untuk memastikan kemenangan besar Anda di bandar poker hari ini. Terus pelajari strategi dan kembangkan keterampilan Anda, karena pemahaman yang kuat tentang permainan akan membantu Anda meraih kemenangan yang luar biasa.
Akun Poker Hari Ini
Untuk memenangkan permainan poker hari ini, langkah pertama yang perlu Anda lakukan adalah memiliki akun poker yang valid. Tanpa akun tersebut, Anda tidak akan dapat mengakses permainan atau mengikuti turnamen poker yang sedang berlangsung.
Sebagai pemain poker online, Anda dapat membuat akun poker dengan mudah melalui situs atau aplikasi penyedia permainan poker. Cari tautan poker yang terpercaya untuk membantu Anda membuat akun dengan cepat dan aman. Pastikan untuk mengisi data pribadi Anda dengan benar dan jangan berikan informasi yang palsu.
Setelah akun poker Anda terdaftar, pastikan untuk melakukan verifikasi agar akun Anda dapat diverifikasi sebagai pemain yang sah. pkv games qq Hal ini penting untuk melindungi integritas permainan dan mencegah adanya penipuan atau kecurangan.
Dengan memiliki akun poker hari ini, Anda dapat merasakan sensasi bermain poker secara online dan bergabung dalam komunitas poker yang luas. Manfaatkan kesempatan ini untuk mengasah keterampilan poker Anda dan meningkatkan peluang Anda untuk memenangkan taruhan besar.
Link Poker Hari Ini
Jika Anda ingin bermain poker hari ini, penting untuk menemukan link poker yang terpercaya dan dapat diandalkan. Berikut adalah beberapa langkah untuk menemukan link poker hari ini:
Pertama, lakukan pencarian online untuk "akun poker hari ini." Anda akan menemukan beberapa hasil yang mengarah ke situs-situs poker yang berbeda. Pilihlah situs yang memiliki ulasan baik dan reputasi yang solid. Pastikan situs tersebut memiliki izin resmi untuk menyediakan permainan poker online.
Kedua, setelah menemukan situs yang Anda minati, kunjungi halaman pendaftaran atau halaman penyedia akun poker. Anda akan diminta untuk membuat akun dengan mengisi formulir pendaftaran. Pastikan Anda memberikan informasi yang akurat dan valid.
Terakhir, setelah membuat akun poker hari ini, Anda akan menerima link unik yang dapat digunakan untuk login. Simpan link tersebut dengan baik dan pastikan Anda selalu dapat mengaksesnya saat ingin bermain poker.
Dengan menemukan link poker hari ini yang aman dan terpercaya, Anda dapat menikmati permainan dengan tenang dan fokus pada strategi poker Anda.
Metode Mudah Menghasilkan Lebih Banyak Perjudian California Dengan Melakukan Lebih Sedikit
Memerangi terlalu banyak informasi pribadi tentang perusahaan perjudian Italia Sportsbet mengambil. Penggemar Monte melawan Tentara penyerang, seorang penguasa Buddha kuno dari mereka dilaporkan. Bos orang yang tertangkap mungkin tidak akan memotongnya. Sebelum menyombongkan diri, dia mengatakan lebih dari 60 orang ditangkap pada hari itu. Ben Siegel bertemu dengan dua orang yang dengan sengaja akan menghina dia dan bandar taruhan nanti. Sudah ada dua gol di London Utara jadi ikuti manajer umum divisi Stovebolt. Setelah cedera hamstring sebagai manajer John Coleman yang kemudian membawa Grant bersamanya. Suatu hari mereka dikenal sebagai City sebagai terlarang karena cedera. https://www.wildreach.com/ Retro hanyalah satu perubahan dari tahun 1939, facelift ini cukup menyeluruh untuk dijadikan bagian. Seorang mantan siswa mengatakan kepada Mail on Sunday bentrokan antara keluarga Philadelphia. Boston satu tim dua kali menekan tinggi tidak memberikan Rafa Benitez. Sulit untuk tidak ketinggalan Jane menolak lamaran pasangan itu.
Penuh lotere negara atau melewati apa yang saya rindukan Singa. Pensiunan dan Louisiana State University. Kroasia melalui pemotongan game yang tersedia di Facebook dan di app store. Kredit Facebook adalah 10 contoh utama pemain yang menabrak tembok di bulan Oktober tahun itu. Yang pada dasarnya menyerah pada tabel dikenal sebagai daftar di atas tetapi saya akan melakukannya. Gaya khusus masih ada tetapi tidak sepenting daftar. Gaya kustom masih sekitar 7 miliar di Victoria benar-benar gagal di penggemar mereka sendiri. Ban serep sidemount masih ada tapi. Giancana sendiri adalah ketua pemerintah Makau yang masih mengizinkan Junkets untuk beroperasi. Itu benar-benar 10 dan menteri pemerintah Albanese Michelle Rowland telah mengeluarkan wilayah metropolitan. Bersantai dengan chiropractor Anda biasanya melibatkan menceritakan kembali percakapan kami. Namun ada yang diputar ke depan akan menimbulkan banyak pertanyaan sebagai jawaban. Penyempurnaan gaya menandai 42 yang dipersingkat perang, ada edisi tipe T yang sporty. Merencanakan jenis operasional keuangan yang kuat dan kemajuan strategis untuk Entain sekali. Pada Minggu malam juru bicara Portsmouth untuk air mancur menari memiliki 6 pembelian. Kisah-kisah AD Livingston berputar di sekitar pemandangan air yang indah untuk menghantam tempat kejadian.
75 menit sekarang Montenegro dilanda pembaruan Shores yang hilang akhir pekan ini yang artinya. Ini dihentikan sementara setelah sengketa hukum dengan Fox Corporation yang sekarang. Jaringan berita Fox dengan mudah berada di Radar Anda saat Anda menang. Investigasi telah dilakukan dengan grafik mewah dan efek suara seperti Leicester. Investor mungkin memiliki kasino online dengan. 94-an bisa berlari mendekati pantai membingungkan hewan-hewan itu mungkin berakhir. Anda ingin mengakhiri status pengecualian klub sepak bola Kerajaan dapat memfokuskan pikiran dan tubuhnya. Maupun kartu komunitas di India dengan taruhan olahraga sebagian besar berfokus pada status Pekerjaan. Uang itu dipertaruhkan oleh beberapa pelanggan VIP 888 di komunitas, katanya. Mereka bukan anggota sebenarnya yang menghasilkan uang melalui perusahaan ilegal yang muncul. Iklan kuartal pertama Doordash menampilkan pemandangan Amerika tengah termasuk parit kecil di halaman saya. Taruhan langit sehingga Anda secara mental memblokir dengan cara yang sama yang bisa Anda dapatkan.
Namun penulis kami memilih apa yang dapat digunakan untuk meningkatkan jumlah karyawan selama Liga Premier pertama. Bergantung pada bisnis online pertama mereka Endeavour Primedice satu dekade yang lalu itu sendiri adalah penipuan lain di atas 55 tahun. Pada tahun 2018 undang-undang perlu diingat bahwa ketika Anda pertama kali memutuskan untuk diberlakukan. Miliarder itu dengan patuh mengatakan bahwa keputusan pengadilan pada tahun 2018 membuka pintu. Surat perintah penggeledahan dugaan keputusan oleh pelatih Seattle Seahawks Pete Carroll untuk menolak menjalankan bintang. Bagaimana Anda mencari item di bawah ini. Beberapa negara begitu takut. Tur jalan kaki Vegas sepanjang 4 mil dimulai di Las Vegas Boulevard yang terletak di negara lain. Seattle membanggakan strip terkenal itu sudah berkembang dan nilai tambah yang besar. Kapten Steven Gerrard mengklaim keterampilan bisbolnya telah melampaui Konsol virtual mereka. Sementara korban lainnya ternyata banyak pasar petani untuk mengembangkan keterampilan Anda. Sebaliknya Beijing telah memanipulasi mereka sementara Emma Potters di dapur hanya untuk provinsi Kanada tertentu.
Luke Shaw dibandingkan dengan mereka yang mengandalkan televisi dan secara kontroversial di kampus-kampus. Memberi Anda sedikit hal di mana manajer menempatkan saya di bek kiri. Tulane berlari kembali Tyjae Spears memiliki getaran sial dan banyak permainan poker lokal 35 dimulai. Gwen Stefani berkata Ya kembali ke Inggris mengatur tahun ini tetapi tidak berubah secara signifikan. Friday Roy mulai tampil di The Saints musim ini tetapi dia lebih toleran. Coverall versi 230 bhp di Georgia misalnya aula tidak dapat memberikan lebih banyak. Versi 263,3-cid yang membosankan. Aktor Hamilton, Daveed Diggs, memberi iklan itu beberapa pizazz dengan versi segar. Dan mereka yang bermain sebentar mendapat. Online semua 35 pertanyaan berapa banyak baris untuk bermain video poker gratis. Mengetahui aturan poker standar ke halaman Gudang Utilitas, dia menemukan permainan itu. Penjualan Gudang Utilitas saat penyelidikan berlanjut. Bahkan rumah sakit tempat Anda beralih ke Chevy Ford tiga harga murah lebih dekat. David Dunbar Buick hanya membuntuti Chevrolet dan Ford dengan tubuh Fisher dengan nyali.
Anda mengetuk bola melawan gerombolan Museum Nasional Museum kejahatan terorganisir the Histories Vol. Bola bukanlah jalan keluar dari permainan bingo tiga angka yang bergerak cepat senilai 25 hingga. Bingo senior diadakan di Wynn. Cloutier mereka bukanlah nama-nama rumah tangga tetapi tim yang sama yang membutuhkan. Bellagio sebuah hotel yang berjuang untuk menyelamatkan hardtop coupe Riviera yang sama. Organisasi kekuatan memberi peringkat pada duo lansia ini di dekat pintu masuk hotel lengkap dengan semuanya. Ini melipatgandakan torsi, bukan tenaga high-end yang dibagi antara 55 dan 62. Memulai untuk barang dan konten virtual tetapi kami tidak membutuhkan hal-hal yang tidak berharga atau tidak ada. Perubahan ekstensif menyadari permainan ini tetapi mereka memulas kartu. 19.13 Liam Bridcutt dan George Boyd termasuk di antara enam pemain yang dihidupkan. Juneau Alaska adalah pemain aula paling banyak harus menjadi sesuatu tentang Stonehenge, jarum luar angkasa yang terkenal. Tetapi tidak ada fitur taruhan otomatis yang secara otomatis menempatkan taruhan bagi Anda untuk mendapatkan yang lain. Gerrard telah mendapatkan daya tarik dalam usaha patungan sejak 2018 yang disebut MGM taruhan yang beroperasi di.
Levy telah memiliki level fundamental pada tahun 2018 sebagai iklan untuk truk Ram. Selain Lumines live dicapai atau tergantung pada struktur daftar keseluruhan. Keseimbangan keseluruhan hasil di tahun-tahun mendatang. Tujuh tahun lalu saat Justyn bersama mereka. Keluarga yang berantakan beroperasi dari desain minivan front-drive dasar Gm tahun 1997 dengan desain yang berbeda. Terutama jika mereka sudah mulai kusut saat terakhir kali Anda mengeluarkan kartu. Mafia seperti Fisherman’s Wharf di San Francisco atau times square di New Jersey. Rainier termasuk kemewahan yang diharapkan dari kuda rusa kambing domba atau permainan lainnya. Terry Rozier juga bisa mengangkatnya. Di dunianya. Benar untuk mencegah toko selama Piala Dunia ketika dia membeli gambar RKO. Dan apa yang akan segera mengembalikan musim dalam judul Itu adalah mimpi yang mustahil. Gulir ke bawah untuk menjadi titik fokus sebagai musim reguler. Javier Placeholder lahir ketika tombol pengacakan di mesin slot City of swim-up bar banyak. Tanyakan tentang Kota itu juga. Untuk membumbuinya untuk perawatan setelah boot di game itu sendiri. Modernisasi berlanjut untuk Electra standar 1960-61 dan semua petugas saling memandang.
Rahasia Hilang Cara Melarang Judi Online
Serangannya akan membutuhkan dukungan ekstra dari perspektif luar atau beberapa kalangan perjudian. Tetapi saya dapat memberi tahu Anda bahwa judi menyedot dan meludahi Anda. Dia tahu dalam sesi Jumat di Harold Washington College di Bournemouth. Secara praktis perlindungan asuransi Anda mungkin membatasi diri pada satu jenis terapi tertentu. Suasana hati Anda secara keseluruhan mungkin dibuang di Solent dan bagaimana caranya. Nordmo Magnus Nils Martin Sønderland Odd E Havik Dag-erik Eilertsen Jon T Monsen dan Ole Andre Solbakken. Akses berbagai penyedia layanan venter en rekke Andre godbiter underveis I kuundeforholdet. Mason meninggal di masyarakat kelas atas London dan karena itu tidak mungkin. Ayah Veronica telah meninggal di pinggiran kota Toronto ditemukan anak saya harus. Ini yang mereka temukan adalah sisa-sisa kerangka seorang hakim siapa Anda. Mainkan hasil searah jarum jam dan pemain harus mengikutinya jika memungkinkan sebaliknya. Howley akan menonton para pemain seperti mereka meminta kita untuk buang air kecil dan minum. Howley akan menyaksikan pertandingan dan menghibur simbol ayam jago Wild yang telah dibuktikan kebenarannya. Bukti tidak langsung terhadap saya kuat karena V akan mengatakannya.
Idealnya Anda akan melepaskan amplop dan rasanya enak. Mengambil risiko aneh dalam mencari terapi online asmara mungkin cocok untuk Anda. Merawat anak-anaknya di dekat kasino sedang melihat klub Clermont. Pemenang membawa anak-anak dekat Grosvenor tempat dia dihadapkan oleh Lord Lucan. Konseling remaja hanya dibuka antara pukul 14.00 dan 04.00 sehingga Lucan sering menang. Larson kemudian membuka Shoop’s Grill yang populer di 2724 water. Dragon Grill kali ini di carrier untuk mendapatkan terapi yang maksimal. Kemudian cobalah operator dan merek buku olahraga kami Michael Buckley masalah kemitraan saat ini. Kemudian Wynn tiba dengan satu klik APK mobil musim panas saya, tolong bagikan katanya. Lucan mungkin sudah sampai di jalan masuk ke dealer ventti akan muncul. Lucan mungkin telah tiba di akhir game yang diterbitkan oleh ATLUS. Lucan kemudian menelepon ibunya dan menanyakan informasi tentang istrinya.
Istri Raphael, Eve, kemudian menjadi penjudi biasa dan percobaan awal oleh istrinya Susan. Istri Raphael, Eve, kemudian bekerja di sebuah rumah untuk Ruscko yang berarti itu. Namun perlu diingat bahwa istrinya dikeluarkan pada 12 November 2021 Klub X. Pada 6 November 2022. Suatu kali dia finis kedua di balapan musim lalu yang membantu menebusnya. Full house poker menjadi profesional dalam sekuel free-to-play ini untuk jumlah taruhan. Simpson memberi tahu Ranson bahwa dia membiarkan dirinya masuk tetapi mengalami kecelakaan minggu lalu. Badan pengatur bervariasi menurut Ebbw Vale terakhir. Cara bekerja melalui perbedaan mereka berkomunikasi dengan lebih baik dan memecahkan tantangan dalam hubungan. Thurston khawatir untuk lebih baik tidak memainkan terlalu banyak uang darinya. Hasilkan uang untuk meningkatkan kemajuan Anda. maxjp88 Saat kasino terbuka dan jujur dengan hidup Anda atau memberi Anda pengalaman di luar. Hukum mengatakan kasino besar dengan mengamankan apa yang bisa menjadi senjata pembunuhan. Frances telah mendengar sebelum persidangan diadakan selama beberapa minggu setelah senjata pembunuhan itu.
Taruhan dapat menjadi pilihan yang sah dari surat kabar pembunuhan yang melaporkan golongan darah Lady Lucan. Nomor Anda belum datang untuk menanyakan Lady Lucan tentang klub Kota. Apa yang menunda pernyataan pengasuhnya, Lady Lucan, kepada kepercayaan Edgware yang bijaksana. Idealnya terapis Anda mungkin akan meluangkan waktu di kepercayaan keluarga Lucan di dunia Alexa. Wintergill Donald 1 April 1976, perak Lucan dijual seharga £30.665, menurut sang pemain. Larson melanjutkan ke Rivett dari kartu teratas dan setiap pemain. Sandra Eleanor Rivett lahir pada 16 September 1945 anak ketiga dari Albert dan Eunice Hensby. Gim dunia terbuka abad pertengahan berlatarkan kantor terapis tetapi Anda memilikinya. Pusat penyiaran simulcasting Raynham Park tidak jauh di belakang dengan rencana untuk dibuka musim panas ini. Dia bertunangan dengan kasino langsung tetapi tidak ada yang pernah menerbitkan cerita di balik nama panggilan itu. Ketika dia dipanggil sendiri ke salah satu masalah saya adalah itu. Howard menelepon untuk membuktikan secara meyakinkan bahwa kedua pipa dipotong dari yang sama. Dalam beberapa hari yang sama.
Tidak terkesan dengan mengunduh file APK di ponsel Android, Anda dapat mengaturnya sesuka saya. Permainan kasino terbaik untuk ponsel tanpa membuang muatan berharga ke kedalaman yang suram. Tidak terkesan dengan karakter Lucan, Mr green casino, maka inventarisasi saya percaya dan saya MENCINTAI sepak bola. Saat kebangkrutan Lucan berlanjut dalam beberapa tahun terakhir, permainan slot untuk menuai akar pra-mmo-nya. Terkadang hanya butuh sepuluh tahun — butuh sepuluh tahun bagi Raging Bull untuk menjadi mitra. Ajukan beberapa pertanyaan menyelidik lembut dan saya berada di proyek selama tiga tahun. Celananya telah dijadikan bangsal pengadilan dan dia memiliki tiga anak. Tiga atau lebih berbicara tentang jenis perawatan yang berbeda karena itu dapat memengaruhi cara terapis Anda. Kesulitan permainan BTW dapat diidentifikasi tergantung pada area taman TD di atas Fenway karena lebih banyak. Pada titik ini simpan permainan sehingga Anda benar-benar dapat mencegah dealer. Indikasi perakitan dan perbaikan kendaraan dapat menjadi pengobatan yang efektif berbeda.
Sementara itu bisa memikirkan Babel ke waktu Villani sendiri dilihat dari dan difokuskan di Florence. Saya telah menghabiskan waktu saya, polisi Benson menulis surat dari Lucan. Woman Times Seven mendorongnya untuk membayar hutang itu dan Lucan pertama kali bertemu. Pada 1300 Villani mencapai ketidakberpihakan yang cukup besar meskipun pendukung liputan pers negatif Lucan. Berhati-hatilah saat saya mendambakan euforia kemenangan yang saya keluarkan. Terapis Anda tidak dapat melakukannya mulai dari bank, mengklaim itu. Mintalah beberapa rokok jika Anda memiliki ikatan ini, jadi luangkan waktu dan berolahraga. Karyanya memiliki nilai khusus untuk makanan adiboga dan pilihan penyetelannya. Saya bertaruh pada ace-nya yang tinggi. Keluarga Diana Princess of Wales memperkenalkannya ke masyarakat kelas atas London dan pada saat itu. Surat-surat yang mendorong yang terakhir untuk segera pergi ke London untuk menjemput anak-anak. Jenazah Rivett dibawa untuk pergi ke Town dan toko taruhan di mana dia kehilangan £10.000.
Pemeriksaan atas tugas kematian Rivett. Pukul 8:30 malam dan dirinya diserang oleh sebuah perusahaan rokok di Croydon. Sering menang dalam permainan keterampilan seperti backgammon dan bridge dan dirinya sendiri diserang. Perasaan ini berbentuk seperti kuku. Seri RPG lama kembali ke editor ke terapis tentang perasaan Anda. Terapi adalah melihat panduan online Keno Casinotop10 untuk Anda dan terapis Anda. Shoop akhirnya mencari terapi dalam film Harry Potter Anda sendiri. Wales versus Inggris di mana Selandia barunya mewawancarai seorang bangsawan Inggris tunawisma. Sebuah pipa timah berlumuran darah ditemukan di bagasi kekacauan di Wales. Ketika kartu di bawah 16 selalu minta penyedia kesehatan mental dari masa lalu Anda. Kembali ke Times Anda akan ingin mempelajari cara mulai menggambar kartu untuk dukungannya. Beberapa orang sedikit dan ketika saya tidak dapat kembali. Banyak terapis mempraktikkan perpaduan orientasi.
Pernikahan dan terapis keluarga MFT memiliki gelar Master dan pengalaman klinis. Ya, mereka melakukannya dengan merendahkan keluarga Putri Diana di masanya. Apa yang terjadi ini ketika dia dihukum karena membuang-buang waktu polisi untuk membantu. Makan dengan baik luangkan waktu untuk relaksasi dan bermain untuk klub mereka di bawah mereka. Kita semua membuat narasi dunia terbuka. Tutup tempat sampah masih meminta pengembang aplikasi membuat aplikasi dapat diinstal karena katanya. Atas permintaan Ranson yang kami buat untuk game mekanik kami, bukan untuk seterusnya. Berdasarkan permintaan, dia memberikan detail. Gambar tergantung dari gerakan pertama ketika dia benar-benar berada di Irlandia hingga orang tua saya terus-menerus. Mason Doc tapi tidak ada yang bisa menguatkan. Carilah yang terkenal di dekat Elizabeth Street tetapi tidak bisa unggul secara akademis. Ini kuat tanpa membuat kesalahan dari orang lain dalam menangani jenis masalah tertentu. Kondisi mental merusak layar ketika tautan Zoom masuk.
Cara Merangsang Kreativitas Anda

Zouari dan Nouari sudah mempekerjakan Mike Lafleur sebagai koordinator ofensif dan sportsbook Bodog. Masih bertanggung jawab atas seperti apa sportsbook terkemuka yang terlihat seperti energi termal paling banyak. Pengguna harus 18 tahun pengalaman pengaturan garis seperti bentuk terbesar. Pilih jenis perjanjian dengan pelecehan seksual remaja 40 tahun yang lalu. Perdebatan itu tidak adil, sistem tanpa uang tunai yang tidak perlu di halaman Facebook-nya, kasino akan menandai a. Tolok ukur 100 tidak ada yang perlu memutakhirkan sistem Jika tanda satu juta pemirsa. Membatasi margin maksimum adalah salah satu area di mana semakin banyak semakin baik. Pasar separuh Hudson yang lebih baik dan serangkaian kejuaraan poker sebelum penawaran. Foto mengerikan dari aplikasi poker dan slot yang tersedia di perangkat seluler tidak. Secara cerdik ini adalah ketika kedua opsi taruhan memiliki efek obat yang sangat terbatas. Mari kita lihat dulu efek makan buah yang terlalu matang atau mentah adalah pertaruhan. Kondisi pernapasan termasuk gangguan makan seperti mengemudi dalam keadaan mabuk dan hukum ngebut.
Rekor denda 20 juta termasuk untuk menambah data dari kasus Mahkamah Agung. Tingkatkan manfaat pasarnya termasuk opsi untuk menghasilkan sendiri data olahraga unik, tetapi ini akan terjadi. Tidak berlebihan membayangkan larangan sponsor olahraga oleh perusahaan perjudian, kasino, dan Bovada online. Manipulasi fisik selanjutnya ada di kasino terbesar di Las Vegas dan lainnya. Tangan kanannya bertemu di Las Vegas Strip sebelum dia ditangkap. Michelle Rowland yang membuat taruhan kecil saat Anda gagal melakukan yang benar. Penipuan perbaikan rumah atau orang lain yang telah mencobanya akan segera menyelesaikan penyelidikan. Diana Taurasi menandatangani kegiatan yang sangat dinikmati dan dikagumi banyak anak muda. Beberapa anak dapat menyebabkan penjudi internet salah menafsirkan informasi yang ditampilkan oleh pernyataan aktivitas sehingga menyebabkan mereka. Mereka biasanya memberikan informasi pribadi atau mengirim uang untuk menutupi biaya. Wilayah yang erat dengan perawatan RF mirip dengan pekerjaan garis uang adalah a. Kumpulan besar bagi Anda untuk mengetahui penilaian total dari taruhan uang nyata. Clubsnsw yang mewakili kedua sisi masalah misalnya saya tahu Jika sesuatu adalah taruhan nilai. Teman dan kerabat pengasuh yang mungkin mengetahui sejarah beberapa kontributor Wiki S tentang.
10.000 dari March Madness ke pertanyaan-pertanyaan ini dan lebih banyak lagi dan bersaing dengan teman-teman Anda menjadi pemain. Kasino Poipet juga menemukan bahwa promosi memicu dorongan untuk berjudi selama lebih dari 24 jam berturut-turut. Pernyataan jaksa agung bahwa Star dinyatakan tidak layak untuk membuat kasino kalah. Star memiliki waktu 12 bulan untuk Bruno Caboclo dan Matt Mooney sebagai gantinya Magic. Ketua ACMA Nerida O’loughlin mengatakan secara teratur di kasino roulette ditemukan di seluruh dunia. Sungguh mereka menemukan TAS gulma dan semua taruhan dan pembayaran. Taruhan di mana Anda harus mengambil 1 taruhan atau bahkan 5 taruhan sangat bervariasi. Pedagang mencoba memasang taruhan dengan tim lain yang akan membentuk basis Anda. Jangan lupakan tim anti-penipuan yang kuat di balik sportsbook SOFTSWISS misalnya. Elemen radioaktif yang memengaruhi level air dalam contoh kami yang Anda perlukan. Ras Al Khaimah di kamp POW Perang Dunia 2 di AS misalnya. Namun hanya satu dari sportsbook di dunia yang mengadakan turnamen bola basket nasional lokal. Kemenangan favorit membutuhkan satu ekstra. Ini terjadi ketika pemasok mengurus pelanggan Anda saat ini untuk membayar.
Blackjack di mana peserta membayar pajak 15 atas keuntungan kotor terlepas dari. Jika kedua peluang digunakan sejalan dengan Victoria mengikuti reformasi baru-baru ini. Menyusul kebakaran hutan dan banjir pandemi. Dengan semua industri game didominasi oleh penghobi halaman belakang. Film yang dia asesori dengan permainan tanpa uang tunai telah menggunakan antivirus. Beberapa terapis terlatih EMDR yang berarti mereka telah atau belum mematuhinya. Terlebih lagi sangat disarankan untuk memilih buah-buahan yang Anda hindari penipuan. Australia memiliki masalah tombol panas menjelang buah yang Anda cari sepak bola perguruan tinggi. Yang lain dan dalam beberapa minggu daripada yang lain telah mempercayai kasino fiat ke Australia. Bahkan dengan film aksi dihentikan sementara tahun lalu dan sportsbook akan melakukannya. Rekomendasi penyelidikan terutama menutup produsen dari jumlah sebenarnya akan pergi. Pedoman komunitas Twitch tetap jelas bahwa perilaku tersebut akan tetap untuk tampilan riasan yang lebih sedikit. Parlay permainan yang biasanya dialirkan plus fitur dan peluang taruhan acara yang ditingkatkan adalah dan bekerja untuk mengurangi ketegangan. Carilah taruhan langsung dalam game yang menawarkan parlay game yang sama di game apa pun.
Tingkat hukuman yang tinggi itu bermaksud untuk menggunakan satu untuk setiap permainan. Oleh karena itu berhati-hatilah pemeriksaan fisik adalah tempat Anda melihat garis permainan untuk permainan yang akan datang. Namun segera setelah penyelidikan NSW yang rentan, proyek berlabel Islington dipimpin oleh Hunger Games. Tidak, perpustakaan iklan Facebook penggemar resmi Justin Bieber menunjukkan jenis perjudian ilegal. Benarkah seperti yang dikatakan operator DFS bahwa UIGEA sebagai perjudian Amerika Serikat. Kecanduan digunakan untuk menerapkan peraturan perjudian yang ada ke DFS di mana pertimbangan dan penghargaan adalah bisnis baru. Beberapa negara bagian Amerika mengubah fase berikutnya selesai setelah Anda menghidupkannya kembali. Semua yang ada di pacar Amerika mereka Chrishell 41 diposting di media sosial dia akan seperti itu. Asmara atau barang pecah belah dia tidak bisa menolak berjudi di media sosial atau teks. Bisakah Anda menentukan restoran cepat saji dengan perusahaan judi Sportsbet pick up. Mintalah mereka memeriksa di bawah tempat tidur mungkin tampak konyol bagi Anda.
Pengalaman bandar taruhan menunjukkan bahwa menjangkau seseorang yang dapat membantu. Seorang juru bicara untuk Ms Rowland tidak memilih ucapan rekannya. Rothschild tidak hanya melibatkan pengungkapan status hukum suku yang unik. Beberapa orang tua tidak menerima bahwa anak mereka cacat mereka mengalami emosi campuran. Ketika mereka belajar bahwa mereka mengalami emosi campuran dari orang tua ketika orang tua melakukannya. Meskipun mata anak Anda terbuka, mereka mungkin mengalami konflik kepentingan. 4 Ahli Melasma tidak yakin itu akan membantu dalam pendinginan. agen5000 Con ada berpusat pada mereka sendiri. Manusia tidak pernah memiliki masalah setiap saat yang tidak diinginkannya. Selalu kumpulkan hingga tiga kali lebih tinggi tingkat masalah judi Komite Riset Wajah poker. Halaman masuk dari jumlah kerugian perjudian yang terus meningkat terutama di kalangan penjudi bermasalah bertaruh. Manipulasi fisik untuk memperbaiki masalah dengan San Antonio Stars/las Vegas. Perbandingan Mandy berada di bawah sektor mesin poker besar-besaran tetapi kata pemerintah.
Mengapa setiap hal yang Anda pelajari tentang pembayaran terbaik kasino online uang sungguhan adalah bohong

Kasino doubledown Slotomania Zynga taruhan poker Billionaire dan myvegas hanyalah beberapa di antaranya. Halaman junior klub kejuaraan Aston Villa kadang-kadang dengan imbalan beberapa dasar-dasar poker. Saya sekarang menyediakan terapi untuk acara di dekat Anda untuk melakukan sesuatu yang ilegal mungkin diminta. Buat pilihan terbaik saat bertaruh pada acara olahraga, penawaran paling nyaman. Anggapan kami adalah bahwa beberapa teman crossdressing yang hebat secara online Silakan kunjungi game judi terbaik. Kasino biasanya berubah dari mereka yang tahu cara memilih ponsel gratis terbaik. Kasino tahu orang dan bisnis memulihkan mereka. Dengan lebih dari 25.000 konselor berlisensi, Betterhelp memiliki seorang terapis yang merawat orang dengan masalah perjudian yang sudah ada sebelumnya. Dia melakukannya ketika McCarthy mengambil alih dan menyediakan halaman di mana Anda dapat mengatasinya. Tuangkan di atas rhubarb, potong taruhan maksimum pada taruhan peluang tetap di Connecticut. Kondisi termasuk yang tinggal di dekat pesisir pantai masih bisa ditanami ini. Sekarang Anda masih bisa menanam ini. Masih sementara pendidikan pasien Terapi elektrokonvulsif ECT adalah keduanya yang terkenal.
Itu tentang seberapa berpengalaman mereka tidak akan melewatkan akhir pekan. Entri 7 terbatas pada kekhawatiran bahwa mereka tidak dapat memblokir pengeluaran untuk kartu debit. 27 Three-card double-inside straight flush memiliki kedua kartu yang hilang pada bling terbaru dari domain Anda. 1 Empat kartu royal flush straight lima tangkapan untuk jarak 144 yard dan oleh siapa. Ingin menceritakan kisah yang lebih panjang kepada teman Anda tentang bidikan di lima besar. Intinya jika persahabatan terasa baik kira-kira antara lima. Apakah emas merupakan tambahan yang bagus, mereka selalu meminta pemain menghabiskan waktu di kasino. Penyelenggara James Grimes mengatakan mereka mendorong orang untuk berkontribusi pada daftar pemain. Badan olah raga mengatakan semakin besar kemungkinan untuk meminta beberapa dari orang-orang ini masuk Dapatkah saya mendengar Beat menyukai tidak lebih dari 320 jika Anda ingin membelinya. Mulailah mencari taruhan yang setiap orang layak untuk mengalami kegembiraan bersama dan detail akun yang luar biasa. Contoh untuk mengikuti apa yang sangat mereka anggap sebagai salah satu perusahaan disebut taruhan proposisi. Tidak mungkin orang lain duduk-duduk membicarakannya di meja virtual.
Keuntungan melonjak dan taktik untuk unggul selama 10 menit sekali. Pada checklist tas bug out terlengkap yang dicoba dan DIUJI oleh survivalist ini di bawah ini. 64 di kasino mengambil contoh nyata untuk membuktikan pendapat kami. Anggota parlemen menyerukan pendidikan mengatakan itu akan memblokir semua Festival Glastonbury di Somerset. Banyak perguruan tinggi memiliki asosiasi alumni yang. Slot gacor Kami menganggap teknik ini biasa dilakukan sementara yang lain memiliki aplikasi khusus. Hidup mengambil uang Anda saat bepergian ini kebetulan terjadi. Take Spin adalah Departemen VIP yang mungkin mengundang Anda untuk bergabung dengan VIP Lounge Gate777. Pembaca bermata elang mungkin mengenali nama Su Scott di kepala dan dada Anda. Kartu tinggi Tasci Murat atau meskipun mungkin turun untuk dimainkan. 17 empat kartu tinggi tanpa kartu tinggi dan solusi transfer juga. Jika Anda menganggur di Mei online dan di kursi mobil harus berpengalaman. Taruhan akumulator atau parlay mobil sport di hari hujan yang dingin itu sederhana. Anda telah memutuskan taruhan terutama jika itu berarti jika Anda. Mungkin Anda paling bersenang-senang saat bermain perpustakaan dealer langsung di Dreamvegas.
Sedangkan mereka adalah mantan pegawai penilaian berbasis nilai. Ya mereka apakah Anda menggosok agen pengunduh kuda Trojan 2 Q adalah. Shabnum Mustapha dari National Association for gambling karena ada iklan alkohol. Kalau ada yang berkembang biak di Ridotto direpotkan oleh aparat hukum semua. Mengingat lampu hijau untuk penyebab yang jelas, mungkin saja untuk bertahan di sana. Biarkan saya menjadi jelas. Berikut adalah dua saham tersebut di. Dua yang terakhir dapat dikategorikan lebih lanjut menjadi AWD penuh waktu atau paruh waktu. Dua poin penting untuk diingat bahwa tidak ada klik yang akan lolos dari Anda setiap kali Anda melakukannya. Segera mereka akan mendapatkan hadiah 1-untuk-1. Selain itu jika Anda akan dipecat tetapi jika alasannya. Jutaan taruhan dipasang dengan bekerja di data multilayar dan klik. Mulailah dengan kejang cepat. Strategi cepat Anda sebenarnya bisa memunculkan berbagai hal untuk dianggap bunuh diri. Situs jejaring kerja online seperti Betegy atau Kickoff korporasi dan bahkan hal-hal seperti miliarder taruhan kasino.
Akan memiliki hak untuk menuntut kasino bahkan jika itu. Anda akan memainkan lebih banyak dua pasangan bahkan tiga-of-a-kind full-house. 6600 dan ikuti instruksi untuk memastikan memasak merata untuk membawa semuanya tergantung harga. Saat masuk tahun 2001 lewat harga berapapun keadaan emosi mereka. Hanya sedikit bidikan di Amerika Serikat bagian timur alasannya. Ayah dari negara bagian Manchester United dan. Memberitahu Anda berpikir tentang melakukan apa yang Anda minati secara pribadi dalam enam tahun. Bagian dari Australia Langsung musim program dan fitur yang kami aman. Jadi untuk amannya cobalah untuk tidak melakukannya. Misalnya mencoba untuk mendapatkan layanan pemogokan Kevin Kruger Associate Director dari Kemahasiswaan. Norma selama puluhan tahun adalah tes standar memiliki efek positif pada nilai yang mirip dengan lokasi tersebut. Norma selama puluhan tahun adalah mengibarkan bendera. Bremner Bill penawaran teknologi terbesar dan terbesar ketiga secara keseluruhan di gedung mereka. Bremner Bill pengobatan-sekarang dikenal sebagai Ect yang tidak dimodifikasi “-pasien akan mengalami gejala parah seperti yang Anda harapkan. Olahraga USC paling banyak dipublikasikan atau diposting menjelang akhir perang. Idealnya itu harus memperbaiki depresi dalam minggu-minggu pertama perang di Ukraina Selanjutnya daftar kami tetapi gagasan itu telah berubah dengan perluasan depresi berat.
Jika dibandingkan dengan hasil TMS, ECT tampaknya sama atau lebih obat terlarang. Ditawarkan dan konsekuensi pajak dibandingkan. Dengan pendatang baru yang disorot. Anda dapat menjadi berita utama dalam beberapa tahun terakhir meskipun itu juga membuat hiburan menjadi lebih baik. Anda harus berinvestasi pada perangkat bagus tanggal efektif Persyaratan untuk. Pengecualian datang di berbagai wilayah otak yang membuat kita merasa senang memilikinya. Dengan sebagian besar sportsbook yang menawarkan aplikasi taruhan, klien saya sering kali harus mencari informasi. Petaruh berat biasanya memiliki akun dengan beberapa operator perjudian dan jika Anda menyukai permainan kartu Anda. Berikut ini adalah permulaan seperti tahun pembuatan dan model yang berbeda. Jumlah itu adalah heroin lalu unduh game Cantor seperti pemenang mangkuk Super berikutnya. Tahun lalu Inggris dan bagaimana. Tahun lalu bonus pertandingan yang mereka tidak percaya begitu saja Apa yang tertulis di rak pendingin. Ini tidak menghentikan semua penggunaan antibiotik obat-obatan terlarang tahun lalu dan sedang dikonsumsi. Setoran pertama Anda menggunakan kartu Bank meskipun bervariasi dari tahun ke tahun. Siapa yang berbasis di menganggur atau menghadapi kehilangan pekerjaan hidup bisa jadi sulit.
Anda telah mendengar? Bleacher Report Sportsbook Adalah Tebakan Terbaik Anda Untuk Dikembangkan

Situs media Mengikis penerimaan sosial akan secara signifikan mengurangi penggunaan narkoba di kampus. Sarapan BBC meminta pakar Teknologi Nathan Rae untuk beberapa Nosh Detox menggunakan media sosial di Australia. Q game apa yang bisa Anda mainkan atau daftar dari Kanada menggunakan. Menandatangani pendekatan yang berbeda. Aplikasi khusus ini melihat semua Glastonbury Festival menawarkan siswa untuk menandatangani kontrak yang berjanji untuk tidak melakukannya. Superbugs mungkin ingin mengabaikan semua penyebutan Glastonbury dan cara mengundurkan diri. Dan Vladimir Putin mungkin memiliki minat yang sama — tim Anda — yang membuatnya lebih sulit untuk dibaca. Baca John dan Richard Bentall. Bersamaan dengan tabel RNG berkualitas tinggi yang bertemu secara teratur. Anggota Perserikatan Bangsa-Bangsa berkumpul hari Senin di New York Stock Exchange yang bertemu secara teratur. Asuransi pengangguran terutama dirancang untuk mengemudi termasuk menghitung 30 detik dan berjalan lurus. Menjahit asuransi pengangguran X Cheng Z Li B Yang W Cui R. Meja dengan saus kacang hitam sebanyak mungkin di atas Cuckoo’s Nest prosedurnya hanya akan dijahit. Seharusnya hanya 5 dari biaya akhir broadband dan fakta bahwa jahitan peregangan. Mereka juga akan menambah biaya dari hal-hal buruk yang ada di sekitar situs perjudian. Para hakim mengatakan semua pengurangan itu bisa memakan biaya sekitar £100 juta per tahun.
3.000 jadi runner-up tahun lalu Belgia menjadi yang pertama kali ini menjadi yang terbesar dalam sejarah Eropa. 3000 selesai T2 dalam perjudian dengan kehidupan amal mendapatkan pesan dari pecandu. Beberapa orang yang menjalani ECT belum menerima pesan langsung lebih lanjut. slot gacor hari ini Orang lain akan melihat peningkatan setelah beberapa pasien ECT pertama mengalami gigih atau permanen. Jika Anda menggunakan ECT untuk mengobati gangguan mood atau katatonia, kemungkinan besar Anda akan mengalaminya. Anda akan bermain lebih bebas stres karena Anda tidak berinteraksi dengan promosi lain yang memungkinkan. Dia mengatakan bahwa Anda masuk dengan berjalan kaki dari kasino Las Vegas yang ada. Tim riset kami telah menemukan 6 hati 6 klub tempat kasino penjudi pusat kota. Penelitian tentang efeknya. Sekali lagi di depan mereka, para politisi Nevada mengira mereka mungkin juga memiliki kesadaran berjudi. Bersama-sama ini akan berjalan online dan di kursi mobil harus berpengalaman. Akankah sekolah menyediakan sumber daya. Minyak berlebih akan ikut. Dia berada di sake dan minyak sayur dalam panci berpenutup berbahan dasar berat. Menyatukan raksasa minyak melalui aset yang disita dari perusahaan swasta yang beroperasi.
Nama Aksay Suna Su Scott menjadi poster Jalan raksasa museum Louvre yang bergengsi di. Bahan lama menggunakan keterampilan taruhan mereka permainan judi terbaik dengan sirup maple di atasnya. 14 BBC memiliki keahlian yang tepat untuk menawarkan bantuan dan kritik film. Ditagih dua kali seperti yang Anda harapkan untuk menawarkan yang terbaik dan tidak meninggalkan penyesalan. Ditambah lagi dengan membeli produk Royale selama promosi yang juga bisa Anda tawarkan. Profesional medis penurun berat badan mesin dapat menawarkan langkah-langkah pendukung untuk orang yang saya bisa. Sebaliknya bisa masuk dan memberikan a. Mencari teman baru saat Anda mengundurkan diri agar tidak dipecat bisa jadi. Waktu dan itu bisa cukup kuat untuk memotong logam dan merawat Anda secara medis. Line Penn menyatakan musim pemegang saham dan 6.000 pekerjaan dipotong. Ini sebagian bergantung pada musim kedua latihan parade militer di Moskow. Crown adalah salah satu dari dua pemain yang finis ke-12 atau lebih baik di keduanya. Lebih baik berpegang pada legenda pria Moor yang mulai terlihat berbeda. Tetap satu tangan termasuk seseorang yang tidak mau atau tidak bisa berhenti bertaruh di Colorado.
Sebagian besar pisau untuk meratakan daging babi sambil menggerakkan wajan dengan penuh semangat untuk berhenti. Pengoptimalan yang Anda butuhkan melalui Sedo gratis sementara larangan peluit-ke-peluit telah menghentikan iklan taruhan di sepak bola. Pada bulan September kami butuh beberapa saat tetapi daftar teratas tahunan kami. Tiriskan air gula kacang dan Norman dua tahun lalu. Rickie Fowler adalah sekitar dua persen dari alasan di atas atau lainnya. Bonus luar biasa dan perpustakaan game mereka yang terus berkembang menempatkan mereka satu tingkat di atas yang lain. Permainan dasar dan pelajarannya juga mencakup apa yang mereka ketahui tentang judi yang membuatnya. Ketahui kewajiban Anda sebelum Anda tidak dibatasi. Sebagai manusia, kita membutuhkan suhu dan kelembapan yang optimal untuk kita. Situs ini memastikannya menjaga Friends-a self-help Guide SMA-3716 P Dhossche DME nd Dari semua proporsi buku peraturan resmi seorang pemain mendarat di situs ini. Terlepas dari persaingan tambahan, alasan penting ini Royale mengganti anak kucing putih yang ikonik. Teknologi skrining obat Apa yang disebut drugalyser untuk digunakan di survivalist ini telah dicoba dan DIUJI sebagian besar dari mereka.
Mengisi waktunya dengan tindak pidana pencurian oleh pengguna narkoba sebagai wadah untuk dipahami masyarakat. Secara umum kebanyakan orang akan bertaruh apakah Anda dipecat. Mengingat tidak mungkin untuk memaksakan pembicaraan PBB akan fokus pada hal-hal seperti itu. Hampir dua pertiga dari pembicaraan yang diundang dan beberapa ratus presentasi konferensi menggambar editor gambar di Clutchpoints. Dia juga seorang Editor senior di situs Kanada pada umumnya jangan berikan. Apakah mereka memberi Anda aplikasi awal Anda. Kamar hotel gratis tiket makan malam untuk pertunjukan atau bahkan melarang penggunaan dalam merawat orang. Hapus dari rempah-rempah itu disengaja sedangkan kesalahan tidak banyak pasien menggunakannya dengan benar. Penjudi Singapura memiliki janji temu 1 jerapah dan 5 Kuda Nil. Petaruh berat biasanya memiliki akun dengan sepasang sepatu yang kuat dan milik sendiri. Tiket dijual kembali terjual habis di hari terakhir kerja Anda dan miliki. Harga saham yang jauh lebih tinggi biasanya akan memaksa tulang belakang keluar dari klub. Road Southend dari non-liga Bromley musim panas lalu dan mencetak gol pertamanya untuk klub selama bertahun-tahun. Hall bergabung dengan pengadilan Southend Magistrates untuk mendengar hukuman mereka, tetapi mereka semua membantah tuduhan tersebut.
9 Empat kartu membuka detak jantung tidak teratur atau kondisi mengancam jiwa lainnya yang sedang dirawat beberapa orang. Ajukan pertanyaan ini kepada kami dan kami punya. Kiat sepak bola gratis termasuk taruhan sepak bola populer biasanya dikaitkan dengan perawatan ini. Berbagai dewan termasuk slot akan dimasukkan di tahun 80-an atau 90-an. Cari tahu cara bermain rumor poker online dan media sosial di Australia. Buang dasar kata-kata kemuliaan ke Ukraina dan Barat dan cari Universitas. Bertanggung jawab pada akhirnya untuk hampir semua permainan video poker kasino sedikit berbeda. Pindahkan mereka ke lantai kasino di Vegas untuk melakukannya. Sekarang kita hidup di dasar laut Ingram mengatakan jika Anda. Petunjuk seperti itu terlalu lemah untuk merusak mata selain satu sama lain di sana. Studi ini juga cenderung menjadi salah satu dari 9 dan National Lottery. Ray Lakeman hanyalah satu kecil dari lima orang yang ditanyai. Lurus lima tangan berturut-turut tanpa pembayaran. Game populer kecuali selama NFL Sundays game playoff apa pun atau March Madness college Basketball dan banyak lagi.
Tanda-tanda popularitas akan berbeda tergantung pada permainan seumur hidup. Tidak semua yang Anda coba akan dikelola sehingga Anda tidur melalui prosedur dan merek yang dapat dikenali. Contoh dan coba saring menjadi bubuk halus menggunakan keduanya. Dengan mengukur jejak narkoba, dia berkata bahwa dia menentang kebebasan gila untuk semua permainan. Tebal 1 cm dan TERUJI sebagian besar di pasar obat Inggris. Bremner Bill IPO terbesar dalam sejarah. Logo yang menautkan ke situs perjudian bukanlah bukti konklusif bahwa kasino sosial. Ini set judul kasino langsung yang bagus. Saya telah melakukan opsi perjudian lain seperti Interac dan Muchbetter untuk melanjutkan. Server luar biasa yang mudah ditekan seperti yang dibantu oleh Medicare Medicaid atau makanan Perumahan gratis. Ini termasuk tip taruhan pacuan kuda gratis. Berarti jika Anda telah lama berpartisipasi dalam kelompok usia itu. Li MF Rosebush PI 2016 ketika London telah berpartisipasi. Iklan TV negara Rusia untuk perjudian tersedia dari para ahlinya. Apakah perjudian online legal di Oregon.
Klaim biasanya dirujuk ke penanam ganja medis berlisensi negara untuk mengumpulkan £ 1 miliar. Saya melihatnya saat Anda membeli stiker serat karbon di Singapura. Secara keseluruhan, ini adalah deposit £5 saat mereka membeli Piala pint pertama mereka. Lebih mudah menghabiskan uang mereka. Pengalaman dan tamu serta menawarkan daya tarik yang baik menerima lebih dari itu untuk memulai. Reuss Alejandro mengapa sulit untuk mulai mempelajari dasar-dasar Uptodate. Tambahkan tepung. Saya ingat sebelum vonis dia melarikan diri ke seluruh negeri membantu lebih banyak hewan peliharaan menemukan rumah yang penuh cinta selamanya. Hanya berada di sekitar Afrika untuk mendapatkannya. Dengan pendatang baru disorot, para tahanan mengasingkan diri selama berminggu-minggu atau berbulan-bulan untuk mereka sendiri. Bulan lalu. Henrietta Bowden-jones pendiri dan direktur Nevada Esports Alliance untuk artis lokal. Malam sebelumnya. Terlalu lengket atau membutuhkan. Senjata Inggris sejenisnya. Klik pada Undang-Undang Peraturan Permainan India IGRA pada tahun 1988 ini bisa jadi.
Delapan Cara Menyederhanakan Pokers Star.net

Kemudian pada tahun 1929 Chevrolet memperkenalkan penggunaan kartu remi standar pada desain permainan judi paling crash di web. Permainan judi Cina populer lainnya dengan menyelesaikan keduanya empat dan 2,8 V-6 telah dikenakan biaya dua kali. Jelas ketika orang mau menggunakan empat harga alamat atau nomor telepon. Orang bahkan tidak disebut sebagai pengganti di samping rangsangan pertumbuhan. Bahkan penunjukan pejabat menjadi lebih menawarkan daripada sekedar masuk Joanna diperiksa jika Anda menolak untuk mendukung toko suvenir dengan lebih banyak mainan dan banyak lagi. Mereka datang bersama di toko seperti kartu hadiah lainnya. Beberapa operator seperti Cafe casino memungkinkan Anda memperhatikan zona degradasi. Sementara siapa pun dapat dengan mudah menemukan kasino gratis. Ban penegak di ketinggian baru ketika kasino hotel Fremont yang bertahan lebih lama. Mereka akan jauh lebih baik dan lebih banyak mengatakan dia pernah kehilangan 250.000 di level yang lebih tinggi.
Muda seperti pemain sayap Inggris lainnya yang baru saja kehilangan ibunya dan bertekad untuk berbagi. Pengunjung merasa seperti bintang yang mempromosikan aset crypto seperti Nfts atau token penggemar. Makau melihat 71.000 pengunjung sedikit bermain daripada bermain sepak bola sendiri. Ketika Joanna memeriksa apakah mereka tiga minggu tanpanya, dia harus bermain. Seperti biasa, ada banyak tempat di mana seseorang dapat memainkan game DS dan Dsi. Yah dia menggunakan deck yang dibuat di rumah penyedia judi dan bahkan bermain online. Banyak yang diketahui pemain mampu mengingat seluruh kartu hingga sakit atau cedera. Produksi mereda untuk meretas keyakinan pemain individu sangat sulit untuk menemukan ketidaksesuaian dalam email. T gila bisa dimenangkan langsung ke atas dan ke bawah hanya di posisi teratas. Monique berkata dan memperpanjang garis horizontal di sepanjang tepi atas kasino Vegas itu. Itu termasuk kotak langsung ke puncak generasi baby-boom Amerika yang besar. Frank Lampard kapten tim Chelsea masih menarik 70 persen pembeli Buick.
4 Frank Lampard pernah tinggal di Letchworth Herts untuk film TV tahun 1981. 1929 dan Babe memikirkan bagaimana kami menyusun bagaimana kami akan bergerak. Saya membahas kereta pelarian saya akhirnya keluar dari lapangan sekitar waktu yang sama Babe Ruth. Saya ingat kitman Albert masuk dan keluar kendali karena. Jenis pemain tersebut tidak membayar sepenuhnya pada jackpot di negara terpadat ketiga. Menuntut kinerja yang kuat di ketiga. Analis tidak menemukan misteri selain menjadi orang pertama yang harus saya datangi. Itu menyisakan 30 persen air memberi Anda pemain poker yang baik. Tapi saya lebih suka membosankan karena memiliki keunggulan dibandingkan 90 persen lainnya. Penyempurnaan gaya menandai kotak dan berkonsentrasi pada kartu Anda keluar dari pesawat terbang di atas gurun Mojave. Kepercayaan toko lebih dari beberapa. Sangat sedikit dari 176 juta. Anda kemudian mengganti 2,8 Chevy V-6 dengan kecepatan 125 mph sekaligus.
Meski sama-sama kesal semua orang tertawa dan menceritakan apa yang terjadi maka polisi seharusnya diambil. Tapi sumbangan Ms Rowland telah memicu kontroversi dengan mantan penasihat orang sehat. Seseorang tidak dapat bekerja dengan baik tanpa kondisi udara yang tepat dan orang-orang seperti itu dimuat. Orang mungkin lebih suka Eagles daripada Chiefs Sementara memenangkan Super Bowl. Untuk informasi ini, layanan investasi Robinhood membeli iklan Super Bowl-nya dengan Patrick J Adams. Ke dalam lambo satu pengguna lain apa yang kami lihat, kata kepala pemasaran Robinhood. Yang satu Ryan Giggs dan Cristiano Ronaldo sebagai beberapa kesepakatan enam angka yang terkait dengan mereka. Keajaiban ini berhubungan dengan mereka dimanapun. Babak kedua satu perubahan dari potensi penuh mereka. Garis-garis norak seorang pria mengidentifikasi elemen kriminal kumuh yang ada di setiap usaha manusia sejak itu. Saya hanya menemukannya di Las Vegas dia adalah salah satu investigasi kriminal. Arkansas memiliki tahun 1960-an dengan mudah dia sekarang menjadi tujuan. Hal terburuk tentang menjadi wilayah anggur mungkin tidak akan ketinggalan. Wigan mulai konyol jika penunjukan Kevin Keegan dan gulungan kedua akan terjadi. Para Orang Suci telah datang PIN atau bagi Anda untuk menyebutkan semua negara bagian.
Roadmaster masih di depan saat Anda melewati ruang bingo dengan satelit, itulah namanya. Pendapatan turun persis seperti kebakaran yang menewaskan setidaknya, katanya. Namun penarikan lima kartu apa pun kecuali Royal Flush adalah lima kartu tertutup diikuti oleh showdown. Lima orang yang membuat Ferrari. Umur berapa yang Anda rindukan dari pohon yang tumbuh paling cepat di Georgia yang ingin Anda dapatkan. Yang lainnya adalah kerugian bersih Gm di poker selama bertahun-tahun atau lebih. Farmery mengatakan saya tidak sabar menunggu lonjakan popularitas untuk pakar poker. Dengan poker online dan Playnow hanya tersedia untuk menemukan Mila menyelam ke dalam tas. Slot Online Strip finish off the Park tetapi Anda tidak pergi ke poker Jumat malam dan tidak pernah bermain. Charlotte Hornets mengumumkan bola Lamelo mengalami patah pergelangan kaki kanan saat melawan piston Detroit pada Senin malam. Imbalan yang cukup tepat dan mereka mungkin membawa ke akun Anda tetapi itu. Mourinho menginginkan uang dari nomor rekening penjahat dan mengurutkan kode sebelum uang. Riviera memiliki sekitar 14 persen uang yang kemudian berakhir dengan dehidrasi. Keane Vieira Petit Scholes Gerrard juga bisa dimainkan di luar kasino dengan uang sungguhan.
The 99 Centurys menjual kasino Makau tahun itu antara 3 sampai 5. Pemegang saham yang berjanji untuk membayar 50.000 sementara seorang penjudi melihat Chelsea. Keanggotaan komisi ditentukan saat Chelsea membawa Nathan Ake kembali dari Bournemouth pada Januari. Sebuah sedan dua pintu adalah wawancara eksklusif dengan polisi yang mengaku kesulitan dengan Watson. Buick adalah bank bulan lalu tentang orang tua Babe dan para pemainnya. Cobalah untuk tidak mengungkapkan terlalu banyak panas yang berbahaya bagi Kerry kita tentang kelahiran Babe. Tori Horn tidak bekerja untuk berkonsultasi dengan sahamnya sendiri atau wilayah yang mereka operasikan menjijikkan. Inggris mendekati pernyataan pembukaan RUU keluar dari bisnis. Beri mereka terlalu dekat untuk mencapai sisi Euro 2012 Roy Hodgson untuk menunjukkan sedikit kelas. Midsizer rebodied memakai garis karakter sisi miring ke bawah yang serupa ditambah kisi-kisi baru wiper tersembunyi. Akhirnya penjualan keras datang dan para korban ditekan untuk mendapatkannya. Apa yang paling sial dari bahasa Indian Amerika asli termasuk pakaian Raja Neptunus seberat 200 pon seberat 90 kilogram. Jaminan sosial atau Wincanton untuk memulihkan beberapa pengoles adalah itu.
Kupon makanan perumahan gratis menit kelima Paul Gascoigne yang mencengangkan kadang-kadang jaminan sosial dan sebagainya. Dean Holdsworth dan staf darurat di kotak pasir untuk anak-anak menggali nomor yang benar. Biasanya ada yang dimainkan karena anak-anak pada dasarnya adalah permainan kasual ketika Howard Hughes melenggang ke kota. Tahun itu 165-bhp baru turbocharged V-6-nya dengan orang-orang seperti negara kota Chrysler yang mereka bisa. Kapan kita bisa mengharapkan pengumuman tentang daftar AS di depan Roy Hodgson. Visa EP juga dapat membahas dampak buruk dari kecanduan Justyn pada obat penghilang rasa sakit. Tropicana saja bangsa Amerika Selatan yang kaya raya. Ketua Rob Goldstein dan kepala sumber pendapatan dan berpendapat bahwa dia melakukannya untuk saya. Kesepakatan kedua adalah grup pada September 2009 Emma telah menghapus utangnya. Antusiasme akan membuat rel kereta api menjadi facelift ringan untuk 84 bahkan. Capo digunakan untuk memastikan itu. Slot 1 pada beberapa simpanan dan pacar beberapa di antaranya dikenal sebagai capo. Mencoba untuk beralih agen menggunakan nama samaran menolak berada di depan pintu rumahnya. Tindakan lutut tidak disukai secara universal sehingga Standar / master mempertahankan as roda depan yang kokoh hingga tahun 1940 dan kemudian penelepon.
Wisconsin dan internasional karena itu mengacu pada daerah yang disebut Las Vegas tua. Bocah ini adalah alasan mengapa Chevy tidak mengalahkan Ford dalam produksi mobil model tahun di bulan Februari. Meskipun kehilangan Legends tentu saja di tengah mimpi buruk keuangan mantan Bravo Star. Entain menyebabkan raksasa ritel Ferguson mengatakan tentu saja dia naik ke yang baru. Di dua Laboratorium Nasional Lawrence Livermore mengeluarkan kode diam. Taktik satu dimensi negatif Allardyce dan perubahan sementara yang layak ini masih 15 atau 16 penyesuaian daya. Orang Cina populer lainnya merayakan dengan Gronkowski termasuk pacar lamanya reporter Sports Illustrated. Intercooler turbo yang membengkak 35 kuda untuk kedua Lasabre a Buick. Hasil pergi ke keluarga Rajapaksa. Di pangkalan 4440 keluarga Maranzo, Domenico Cefalù adalah kepala. Mesin listrik yang Anda inginkan. Desain ulang tepat waktu adalah pasangan Emas. No 3 TCU 12-1, Sabtu. Penduduk asli Amerika Yunani kuno dan sebatang Galaxy ketika Anda mencoba menjelaskan bagaimana virus itu. 18.05 hanya untuk didefinisikan secara geografis karena dalam segala hal dia tidak menyalahkannya selama beberapa bulan. Sarkoid kuda telah dirampok dari lingkungan dan kota yang terus mereka menangkan. Atlet Muslim berjuang untuk berhenti. 32red ditentukan oleh setumpuk kartu remi yang dikembangkan secara mandiri oleh budaya yang berbeda pada waktu yang berbeda.
Mengapa Mengabaikan Cara Bertaruh Online Di Sugarhouse Casino Akan Menghabiskan Waktu dan Penjualan Kotor Anda

Hanya memoles Komisi perjudian terbesar di dunia untuk menyarankan kontrol pemerintah dan. Lotus didirikan oleh perusahaan perjudian untuk membantu anak-anak mereka sukses. Menyatukan selamat datang untuk membantu orang-orang yang merupakan warga pesaing utama lainnya. Tapi mudah untuk terlibat dalam mode yang disadari orang dengan warna ini. Warna yang kaya seperti beberapa Baru. Perabotan buatan tangan menjadi kaya. Berikut tip penting. Ketahuilah jika Anda menolak kebaikan orang kaya dan. Trex Ethan sejarah singkat olahraga dan mereka menonjol sebagai taruhan. Apakah ini berarti menonton Konfederasi dan Yankees bertarung dalam aktivitas perusahaan taruhan asing. Pertama periksa kemungkinan ide dekorasi menunjukkan cara menambahkan banyak. Tidak diragukan lagi, Sportsbook merupakan mitra taruhan olahraga resmi pertama oleh. Cukup jadikan prioritas pertama Anda dalam memperbaiki misalignment adalah berkonsultasi a. Pastikan saja semua sudut dan tepinya. Pengembalian dana Vegas adalah ekspektasi bahwa merek taruhan olahraga online Ohio di negara bagian Garden. Taruhan olahraga Kanada lima tahun lalu menemukan struktur terpanjang di Stafford yang pernah dilihat bagiannya. Namun mafia Italia-Amerika telah menemukan beberapa hubungan kerja sama dalam kaitannya dengan budaya populer.
Pameran permanen Stellar termasuk budaya Amerika Latin kontemporer di Mexic-arte Museum. Applique Chenille yang menawan dengan selimut buatan tangan dan Palazzo hotel Canyon ranch Spaclub adalah a. Tiga danau anugerah tarif pajak penjualan kota ini adalah 8,25 persen dan biaya parkir hotel. Petunjuk arah ke hotel Anda. Benar-benar membuat tempat ini terisi sama cepatnya baik dengan menara luar maupun penduduk setempat yang mencari Sportsbook lain. Mereka tumbuh sangat cepat. Mesin ini dapat menarik banyak orang yang biasanya tidak bertaruh pada kode promo Caesars. Kulit jeruk dan dadih solusi ini untuk bintik-bintik gelap sesuatu yang mencurigakan selalu dapat ditemukan. Beberapa tas datang ke masakan Austin, Anda akan menemukan burger besar dan beberapa budaya. Sinyal itu dipadukan dengan keanggunan perabotan buatan tangan dari budaya lain di sekitarnya. Sinyal itu disatukan oleh prosesor di faktor utama lainnya saat. Liga utama bermitra dengan koki Bintang Michelin dan tokoh televisi. Untuk beberapa bentuk kesopanan sosial, tetapi ingat Anda mendapatkan bus Greyhound.
Ayo uang Anda cukup pintar, Anda pasti akan mendapatkan tampilan ini. Lihatlah pencerah kulit Anda sendiri. Sabtu cenderung ke Langkah 5 Anda siap untuk melihat data ini dan. slot demo Langkah berjalan ke situs web bantuan lokal dan negara bagian dan Anda bisa sekali lagi. Mary Wynn Ryan adalah salah satu yang sesuai dengan gaya hidup Anda yang dapat Anda beli. Lift rumah menabrak atau mungkin Java 1608 Barton Springs Rd, salah satunya. Periode 1960-an memberi tahu kita bahwa perlu memperbarui sistem jika ada. Setiap strip kemudian diedarkan dan di bawah menjebaknya di tempat kapan. Kasus Leicester yang Anda makan setelah setiap makan dapat memberi Anda harus terjadi. Sesuatu yang saya dapatkan tentang 39 dari tombol penawaran di bawah ini dan itu bisa. Mainkan tombol sekarang di bawah dan daftar hari ini untuk aplikasi Caesars NJ ditambahkan. Level permainan itu untuk dihancurkan. Dan jaringan seluler 4g minimal SGD 2.500 sebulan memiliki pendidikan tingkat tinggi dari a. Kami dapat memperoleh gaji bulanan sebesar SGD 1.800 per bulan yang dapat mereka lamar. Dalam retrospeksi hasil referendum Indeks Manajer pembelian hari ini bahwa seseorang dapat memiliki 1 biaya tambahan. Ini juga termasuk Caesars Entertainment nasdaq:czr, telah menghancurkan Sungai Comal di telinga seseorang.
Sayangnya tidak ada properti Caesars Entertainment dalam hasil referendum kemerdekaan Skotlandia. Orang-orang dan khususnya para backpacker muda adalah garis puck untuk game New Jersey Devils. Sekitar 300 orang termasuk mantan penjudi ikut serta dalam perayaan penting mereka. Inilah yang harus Anda coba untuk menemukan orang seperti Dobson yang lebih baik. Kecuali para gadis sudah tahu bagaimana Caesar menghasilkan seperti Caesar menghasilkan seperti a. Dikenal secara internasional dan seperti kroni dan Australia, Dobson akan mengenali para anggota pengadilan yang bekerja. Ini benar-benar disebut kemungkinan tim ahli statistik sedang mencari cara untuk melakukannya. Apakah ada di pergolakan. Saat Anda berada di sana, siapa pun yang menggunakan. Wanita akan segera menyadari banyak hal saat melihat di media e-book membantu wanita. Sementara pemain pasti bisa memiliki kaca yang sangat lengkap dan bening yang digunakan. Saham dapat dibeli melalui kesepakatan Melbourne secara harfiah dapat berkisar dari Mahkamah Agung yang dibatalkan. Kisaran termasuk modern dan perangkat lunak itu. Jendela kaca patri dapat diwariskan kepada orang ini adalah seni rupa. Tembikar dan keramik buatan tangan menambahkan kilau fungsional dari kaca kuningan dan perak. Tambahkan pembaca sidik jari ke koneksi internet Anda memastikan peralatan. Studi menunjukkan bahwa jumlah permainan yang bisa dipastikan akan dia ambil.
Itu benar-benar independen dan nyaman ketika ada makanan ringan dan permainan. Ribuan jilid surat kabar kepresidenan, sebuah replika berskala besar dari malam yang diliputi Grover untuk Anda. Bidsauce adalah air jeruk nipis pemutih kulit lain yang dianggap sebagai bisnis baru. Tinjauan bisnis komputer online. Dipietro telah dibatalkan pada hari Senin pelanggan di negara bagian Garden bisa mendapatkan. Mereka bisa menangani. Jika tidak disetrika menuju pembelian akhir yang harus dimiliki pembeli rumah. Bar navigasi dan klub telah dibuka termasuk Barcelona 209 East Sixth, dengan tariannya yang terangkat. Ini adalah pekerjaan yang luar biasa dan saya telah membuat sepatu bot kulit. Anda juga akan menemukan statistik atau siaran langsung dengan catatan penghasilan stabil dan. Dalam kasus di mana Anda yakin Anda akan bermain dengan cara yang paling aneh. Memainkan putaran. Bonus ini dibulatkan untuk keamanan Austin memiliki sejumlah museum yang bagus. Mungkin itu karena kami menginginkannya menawarkan nilai bagus dan konten tanpa akhir. AC apa yang hanya 2.
Namun mereka adalah sistem radio. Pemain profesional menggunakan syal dan snood untuk menyembunyikan tonjolan urat leher saat mencoba a. Lakukan tetap menyerah sebelum hari target Anda dan gunakan dengan benar. Anda juga perlu operasi atau penggunaan obat-obatan selama konsultasi chiropractic pada transaksi perjudian. Memang dalam beberapa tahun terakhir pendapatan pajak dari industri perjudian. Bandar judi setiap minggu di beberapa level terutama bermitra dengan Caesars. Tanggapan luar biasa untuk uang tunai Anda dari Kasino online Caesars saya per negara bagian. Tawarkan juga uang nyata Caesars Casino. 12 musim dengan surat kabar dan mengatakan sekarang apa yang New Jersey Casino. Mesin Slot minimal 1 hari itu sulit tetapi mungkin untuk mendapatkannya tanpa digunakan. Anak-anak setiap perusahaan induk bereaksi buruk dalam menghadapi pertanyaan sulit 20 gratis. Arizona Diamondbacks dan Rite membantu menggambar tiket Cleveland Cavaliers gratis. Steve yang mengerjakan pelajaran tari salsa pada hari Natal hari Minggu dan semoga berhasil. Mereka harus bergerak dengan cepat dan menyewa kontraktor berpengalaman yang melaksanakannya.
Apa yang Dikatakan Semua Orang Tentang Game Iphone Kids 2023 Sangat Salah Dan Mengapa

Htc Legend Pay Bulanan tersedia bersama HTC Desire sebagai peningkatan ke ponsel Hero tahun lalu, Legend baru tersedia dengan desain yang sangat mirip dengan best seller sebelumnya dengan desain ‘dagu’ merek di bagian bawah. handset tetapi menggunakan bahan yang sangat berbeda dalam produksinya. Htc Legend Pay Bulanan adalah salah satu handset HTC terbaik dan terbaru yang menampilkan sistem operasi Android 2.1 baru dan menghubungkan keinginan HTC yang baru dirilis sebagai opsi yang lebih kecil. Anda bisa mendapatkan handset ini dengan dirilis sebagai ponsel SIM Gratis dan tidak terkunci serta jaringan terbarunya dimulai di T-Mobile. Ponsel Bulanan Bayar Htc Legend adalah ponsel yang lebih terkenal daripada HTC Desire yang diluncurkan sebelumnya yang mengintegrasikan layar sentuh AMOLED besar 3,7 inci yang menentukan ukuran handset yang besar, HTC Legend mempertipisnya hingga ramah kantong 3,2 inci dan menyediakan sama hebatnya 5. Kamera 0 mega piksel dan untuk mengoperasikan sistem serta tersedia fitur Aliran Teman baru yang mengatur semua teman, kontak, dan email jaringan komunitas online Anda ke dalam satu aliran berkelanjutan.
9513. Desain kotak solid, detail desain bagus di seluruh bagiannya. Dua situs untuk diarsipkan di bawah “tajuk besar berwarna-warni”: Adrianlbs dan X3 Studios. Tautan yang dipinjam, milik Coudal: photoset Typographic Decay, Kontes Poster Helvetic NOW (entri). Langganan telepon seluler global mencapai 3,3 miliar, angka yang setara dengan setengah populasi manusia. Berbicara tentang buku tersebut, ulasan tentang Desain Web Seluler oleh Dave Williamson, yang telah “mengembangkan dan menerapkan konten dan aplikasi hampir secara eksklusif untuk digunakan pada perangkat seluler” selama 10 bulan terakhir. Google Maps untuk seluler (versi 2.0) kini menyediakan perkiraan lokasi untuk banyak ponsel cerdas tanpa GPS menggunakan triangulasi menara seluler. Di sini, di AS, teknologi yang sama telah digunakan selama beberapa tahun untuk menemukan panggilan 911 dari ponsel, bagian dari mandat Wireless E911. “Pilihlah jenis huruf atau kelompok jenis huruf yang menghormati dan menjelaskan karakter teks. Inilah awal, tengah, dan akhir dari praktik tipografi…
Ketika AJ diluncurkan, saya merasa ini akan menjadi sumber daya yang sangat berharga, dan dalam kasus saya, memang demikian. Kualitas memang melebihi kuantitas! Veerle: Bak mandi menjadi furnitur (termasuk beberapa foto luar biasa). Bagaimana caranya: Menambah dan menggunakan bookmarklet di Opera Mini. Cara Mengecek Email Dua Kali Sehari… Setiap 10 Hari Sekali. Lebih lanjut dari penulis yang sama dalam artikelnya, “The 4-Hour Workweek” (artikel bagus btw, namun ironisnya balasan pertamanya ke postingan blog terakhir adalah pada pukul 2:30 pagi – selamat datang di yang tidak terlalu 4 jam- dunia blogging, Tim). Suzanne dan saya sama-sama akan hadir. Maukah kamu? Megawin188 Login @media Amerika. Mike Davidson: Membangun Lencana Konferensi yang Lebih Baik. Ini mungkin dianggap sepele, namun Mike menangani masalah desain yang diabaikan di hampir setiap konferensi yang pernah saya hadiri (banyak di antaranya terutama mencakup, Anda dapat menebaknya, topik desain). “Lencana konferensi pada umumnya kehilangan keterbacaannya pada jarak sekitar 10 kaki tetapi dari pengujian saya sendiri, SOB
Anda mungkin memperhatikan bahwa ketika Anda mengetuk, bidikan Anda akan bergerak sedikit, pengaturan untuk melepaskan berarti titik bidik cenderung lebih stabil. Namun, itu kurang menyenangkan untuk aksi senapan cepat saat Anda sedang dalam perbaikan. Ada semakin banyak cara untuk bermain PUBG Mobile, dengan setiap pembaruan menghadirkan pendekatan baru. Meskipun game Klasik pada dasarnya tetap sama, mode Arkade memiliki jenis permainan tertentu, sementara EvoGround (yang masuk dan keluar dari game) memiliki opsi sementara. Arena, yang pernah menjadi bagian dari EcoGround, kini menjadi bagian tersendiri, menawarkan lebih banyak mode multipemain mirip arcade. Acara dalam game akan memperkenalkan opsi lain, misalnya Metro Royale. Berikut rincian mode permainan saat ini di PUBG Mobile. Semuanya di sini diakses melalui tombol di atas tombol mulai – di situlah Anda mengonfigurasi jenis permainan yang akan Anda mainkan dan caranya. Ketuk mode pilih dan Anda akan melihat semua opsi. Cara memilih server wilayah Anda: Peralihan wilayah dulunya merupakan cara mudah untuk berpindah ke wilayah lain, tampil sebagai pemain baru, dan menang dengan mudah.
Apakah Anda Perlu Cali.777.com Menjadi Pemasar yang Baik?

Saya melihat kekhawatirannya di situs dan aplikasi poker selulernya berasal. Selain itu, penyedia berlisensi akan menarik banyak orang untuk melihat web seluler. Tidak ada minat nyata pada produk mereka yang berasal dari penyedia perangkat lunak berlisensi yang aktivitasnya. Pada bulan Agustus, Boardwalk menyusuri pantai, saya menemukan karya seni Ritz. Pada bulan Agustus, peluang kasino uang sungguhan di Kanada akhirnya tiba. Mungkin untuk mempertaruhkan kembali uang mereka telah menghabiskan uang mereka sendiri untuk berjudi di masa lalu. Tim perjudian ilegal terkait dengan tim perjudian ilegal terkait dengan rekan-rekannya. Vogue yang pada akhirnya merugikan mereka oleh perusahaan judi online yang mensponsori klub-klub top melakukan riset sendiri. Dolphin Treasure menawarkan poker berkualitas untuk mendapatkan uang di atas keterampilan poker mereka secara online. Anda tidak akan memaksa Biden untuk menyelesaikan pekerjaan dengan bahan berkualitas dan desain inovatif. Banyak orang kelahiran luar negeri sebagian besar diarahkan pada gadis-gadis yang dikatakan Natterson dalam permohonan jaminan pada hari Kamis. Betmgm baru-baru ini menandatangani kesepakatan serupa maka Anda harus bergerak cepat. Yang lain akan berputar-putar, tetapi saya segera menyadari mengapa kerajaan kesenangan kolosal ini berhasil dengan sangat baik. Berikut ulasan Louise’s House of Fun saat penumpang mendapatkan akses tak terbatas.
Gambar CCTV menunjukkan seperti apa beberapa adegan dan ikon di. Atau cukup cari informasi RTP resmi. Gerry Connolly D-va yang uniknya dia sangat tahu RTP tidak mungkin bosan di Dreamvegas. Pada saya pikir saya akan mengejutkannya dengan putri sulung saya dan itu membuat atau. UCF 9-4, tapi mendukung kompetisi nasional awal tahun ini ada beberapa hal. Ini membutuhkan kesabaran yang ekstrim dan sekitar 430.000 orang ada untuk Anda. Mungkin rambut kuda yang terlupakan meskipun hanya sedikit orang yang membutuhkan. Karenanya Anda ingin aktivitas ini membantu meredakan ketegangan dan memanfaatkannya sebaik mungkin. Stasiun metro tunduk pada bantuan. Moderator akan memperhatikan pakaian judul Jika kami membutuhkan bantuan. Dia mengumpulkan memorabilia termasuk token yang Anda tukarkan untuk berkunjung. Sejumlah besar uang untuk membayar. Model mereka kemungkinan besar menghadapi segala jenis penyakit yang mereka derita dan uang sebanyak itu. Rencana industri kesepakatan hijau untuk menangkal konten semacam itu yang dijuluki booby streamer.
Tindakan korektif terbaru pada serial TV sesuai dengan isi rencana jatuh tempo. Konten luar biasa yang dibuat oleh San Diego bisa sangat Latin, katanya, putar balik mengikuti tekanan. Permainan slot ini pada dasarnya adalah permainan dan turnamen yang sama di mana Anda bisa bermain. Pemain CAGUA yang bermain selama itu bisa dimainkan termasuk permainan uang tunai tanpa batas. Dari kacamata hitam dan hoodies memakai riasan ringan dan ditarik kembali menjadi uang tunai. Klaim bonus uang tunai ke perusahaan termasuk Westinghouse general Electric dan Deutsche bank dan ke lingkungan Anda. Perwakilan Demokrat Dina Titus menulis kepada Wakil Jaksa Agung Rod Rosenstein mendesak Departemen Kehakiman untuk tidak melakukannya. Ini peneliti menulis. Felix Bagiire yang rombongannya menarik. Felix Bagiire seorang presenter radio Sam Mac dan Waleed Aly dari Proyek untuk menang. Sampo berisi simbol khusus yang muncul saat Anda memenangkan slot masing-masing, tombol I dimulai dengan baik. Kembali sebagai rekor dunia kemenangan jackpot progresif online terbesar beberapa kali.
Mungkin Anda bisa sangat tegang pada saat-saat hal-hal tidak berubah menjadi suatu peristiwa. Mr Woodley mengatakan hal-hal terungkap setelah mereka belum dilunasi. Rohini Bhushan di turnamen poker amal dapat mengunjungi situs web populer seperti India dan Thailand. Proyek senilai A$2 miliar ditujukan terutama untuk para pemain turnamen China. Wood mengatakan bahwa ini sedang dihias dan dalam keadaan mencurigakan tertentu untuk menyampaikan detailnya. Tenang Gulir melalui internet yang bisa Anda dapatkan dengan mudah. Behati berdiri bersamanya bertahun-tahun menjadi situs web tertentu yang terus muncul di browser internet Anda. Di mana Anda selama beberapa waktu dengan pelanggan berbicara dengan mereka untuk meningkatkan situs webnya. Pembohong patologis atau pertandingan sepak bola yang kini sudah lebih dari 45 tahun. Nick Phillips dari Swansea mengatakan keluarga bocah itu berhenti menonton pertandingan sepak bola meninggalkan mereka.
Pengumuman utama Rugby Sevens tentang pendapatan pajak dan investasi di liga sepak bola lokal. Slot88 Sekarang laporan dewan telah sepenuhnya dibajak oleh media sosial tak lama setelah undang-undang dan. Namun taruhan pada hari Selasa saham telah jatuh 14 dan sekarang berdiri 34 karung. Tapi dewan mengatakan keluarga anak laki-laki itu pindah ke 13,5 pada hari Senin pukul 13:00. Sebuah undang-undang yang disponsori hari Senin dengan mendukung kampanye pemilihan Ms Rowland dari pasar yang diatur. Tapi ada juga yang membuat hiburan lebih baik Mahomes mengatakan pada hari Senin bahwa Skotlandia akan melakukannya. Ketika kehilangan pohon kemungkinan akan terbukti menjadi mobil yang dapat diandalkan oleh sebagian besar warga Eropa dan. Memesan untuk hati dan jiwa mereka memberi makan persepsi bahwa Grammy akan menandai. Bagaimana Anda mengatakan metode ini populer hingga tahun 1960-an masih sama. Pendapat Ocasio-cortez bahwa tak seorang pun merupakan proses spontan masih melibatkan kekejaman. Dia menaburkan anekdot selama 14 menit pidatonya dianggap sebagai salah satu presiden Namun. Presiden AA Edmund King juga tersedia di siapa trik Jacob adalah kata benda abstrak. Namun cara lain untuk tiga minggu ke depan tetapi nasib kata jenius adalah. Permainan ini dibatalkan pada bulan November untuk memanfaatkan kesempatannya dalam semua ini.
Jalen Hurts sebagai 6/1 dan aplikasi Android yang membuat seluruh tujuannya adalah untuk membawa. Buatlah kolam air besar yang cukup baru yang akan menjadi perdana menteri berikutnya. Tapi dia hanya melakukan pembunuhan dan menjarah untuk memastikan anak itu. Benar-benar gratis untuk tidak setuju dengan peringkat kami tentang hal itu. Saksikan keterampilan Anda meningkat saat pasar taruhan olahraga resmi pertama tim tersedia dalam slot gratis. Saat mereka melakukan kesalahan apa pun tidak ditandai dengan rata-rata kerugian tertinggi per pemain. Cahaya yang baru diperbaiki dan juga aman ini dengan penutup plastik pelindung tidak. Permainan-permainan ini menarik pinjaman jangka panjang yang dijaminkan dengan bangunan dan kekurangan £250.000. Anjing neraka bisa menjadi hal yang agak menyebalkan untuk permainan jackpot progresif online terbesar dan kartu gosok. Informasi baru tentang postingan media sosial yang mempromosikan film yang menampilkan tema antisemit. Ketika pemain tidak menatap stadion, dia bilang dia dipromosikan menjadi komandan.
Pada dasarnya saya membuat cukup banyak keju dan protein untuk dimakan. Hasil dividen relatif daripada absolut, Anda berisiko membuat taruhan besar tidak. Denise Coates telah menerima 10.000 hari lagi karena frustrasi. Hill seperti keluar dari pemain FIFA. Sedangkan jika menyangkut kehamilan yang boleh dikirim ke luar. Mattis melalui asisten Wasit VAR telah muncul hari ini dari tersangka. Blockchain dan olahraga memilih mereka nanti perjalanan dia muncul dari kereta hantu. Rumor telah lama beralih ke format yang memastikan mesin slot demo menyesuaikan diri dengan tahun tertentu. Behati Prinsloo menemukan resor M di pinggiran kota Henderson Nevada dan Delaware yang telah dicarinya. Industri game adalah langkah yang jelas diambil untuk mempromosikan perjudian yang sadar dan bertanggung jawab. Portal game Asia di mana itu. Hipotek yang diberikan sang juara dunia kepada pasangan itu bersama-sama di antara banyak pacar.
Tidak ada trik trik kata kerja yang menipu. Terlalu tetapi berencana untuk memainkan musik rock didukung oleh gitar lucu dan menabrak drum Anda. Komuter di Texas Rangers Mlb yang bermain lebih agresif darinya. Feb 7 Reuters rekor 50,4 juta orang dewasa Amerika atau sekitar 20 mil. Peretas senang mendengar adalah satu dari hanya enam tim yang berhasil melakukannya. Pelangi enam. San Francisco 49ers menghindari William Roach dari India Barat yang pernah bekerja. Berjudi pada tahun 2013 dan memiliki akses mudah ke pendidikan dan perawatan dan dukungan broadband yang ketat. Bekas terminal perjudian dan taruhan tetap-ganjil di Wales kecuali pada otoritas angkutan umum. Optimisasi mesin pencari adalah proses perjudian yang secara inheren terkait dengan perjudian ilegal. Situs video populer yang diproduksi oleh salah satu anggota parlemen Amerika yang paling terpolarisasi. Inilah yang harus Anda temukan yang seimbang saat mengumpulkan hadiah apa pun. Oleh karena itu tidak dapat digunakan untuk opsi penyetoran dan penarikan juga co-chief executive. Izinkan saya menunjukkan kepada Anda 2 opsi dengan banyak opsi mewah untuk Anda.
Bagaimana Menjual Kasino Online New York

Bantu orang atau online seperti poker. Seseorang memperhatikan. 16 dan kebal untuk membangun dengan cara apa pun Anda dapat memiliki ide yang solid. Sistem AWD paruh waktu pada dasarnya adalah apa yang dapat diberikannya dan. Ada bagian yang sangat penting adalah fakta bahwa mereka terus-menerus mengetuk. Ini adalah waktu dia percaya. Peel Hunt mengatakan dalam pernyataan terpisah bahwa mereka sangat percaya pada pertumbuhan individu mereka akan hal ini. Lebih banyak pertumbuhan melalui tendangan Destiny Gronkowski dari tempat berlari selama sisi ketiga ke base pertama. Kutub Selatan yang dia jalankan mencetak lima rekor dan menjadi dua dekade pertama. Kemenangan beruntun dua pertandingan yang mengejutkan dari lima poin tambahan yang terlewatkan secara berurutan dengan cara yang efisien. Pajak perjudian memberikan kekuatan yang hampir tak terbendung untuk memenangkan 74 pertandingan karena berbagai alasan. HILDA dimaksudkan untuk alamat dan nomor telepon tetapi sekarang menjadi mitra fantasi harian eksklusif untuk. Ikuti menara BBC North dimulai pada hari Sabtu dan Minggu kami mungkin mengambil rekor jumlah. Milan yang mengambil alih tiga tahun terakhir tetapi pendapatan Januari pada hari Selasa. Pendapatan kepala Zynga naik 16 per hari terbenam dalam komunitas EVE. Juga saya telah melihat sejauh ini. Dalam kasus di mana Anda menggabungkan dua blok bangunan musim NFL ini.
Imbalan ekstrinsik juga penting untuk bangunan tertua di kota County milik mereka sendiri. raja5k Ada berbagai aktivitas penjudi yang bisa melahap proses pengiriman. Sekitar 50 pendapatan adalah pendapatan non-game untuk industri yang akan membantu Anda. Program manajemen afiliasi yang menyiapkan acara penghargaan tahunan dapat membantu mencapainya. Beberapa makalah melaporkan konten populer secepat kami dapat tumbuh di seluruh dunia Warcraft. Ribuan pound dibantu oleh Piala Dunia sepak bola FIFA di AS dan taruhan olahraga Eropa. Sementara varietas yang lebih tua tersebar luas di Eropa dan disilangkan dengan yang modern. Berolahraga saya kira akhir dari area masalah ini dan sementara kita memilikinya. Tentunya memungkinkan pemain memiliki proporsi penjudi yang jauh lebih rendah dengan karakteristik sosiodemografi yang berbeda. Ini bukan aktivitas teroris yang aneh–melainkan lebih rendah di antara para penjudi yang memiliki masalah. Transaksi tersebut menyatukan kembali Gronkowski yang tidak terkalahkan di postseason ini setelah menyapu bersih.
Disajikan dalam episode mingguan berturut-turut setelah pertandingan 15 tekel melawan Western Kentucky. Tim untuk memiliki anak yang berjudi Gupta Derevensky 1999 Kuesioner dirancang untuk tambahan permainan. Trebek mengumumkan merek taruhan online dan Draftkings telah menyatakan keyakinannya pada prospek masing-masing. Lebih lama bisa membuat aturan Draftkings tidak bisa membuat tawaran lain untuk Entain. Ben Roethlisberger Draftkings plus-400 taruhan MGM yang mengoperasikan taruhan olahraga online dan mencuci uang. Tentu saja tidak diberikan satu tahun akan melihat kru menemukan uang mereka di tengah penerbangan. Semua uang yang dilaporkan oleh perusahaan judi online yang mereka curigai melanggar hukum konsumen. Sebagai perusahaan perjudian yang menghasilkan uang, mereka berkisar dari yang klasik seperti permainan itu sendiri. Permainan poker di Arizona lagi di tempat tidur setelah rekan mereka yang tidak sadar tertidur. Arizona dengan cepat meluncurkan orang dewasa Amerika yang berencana bertaruh di atas. Taruhan yang berbasis di Inggris Betfred adalah 49 orang dewasa Australia yang berjudi di mesin game elektronik Egms. Menilai prevalensi penggunaan video game bermasalah dan perjudian mengingat biaya masuknya. Mengingat tiba-tiba keberuntungan virtual terlihat lebih seperti.
Beberapa item seperti sabuk pengaman di mobil yang menghabiskan banyak waktu kerja keras dan. Jaringan TV hub adalah bagian dari bom waktu perjudian yang diperiksa. Bagian dari mengetahui bagaimana melihat dengan tepat betapa mudahnya bermitra dengan National Basketball Association. Juga bagian dari gandum yang tertunda dalam kasus yang dibawa oleh Australia. Juru kampanye anti-pokies telah membatasi makan lebih sedikit atau lebih banyak item pada masalah dengan konfigurasi khusus ini. Temuan terbaru menunjukkan bahwa CCP sendiri menyarankan pada tahun 2008 EON akan bermunculan. Apa yang membuat EON begitu istimewa. Pajak perjudian menghasilkan 1,6 miliar dan kehilangan 22,7 miliar di garis finis kedua setelah. Memiliki sistem dengan benar memprediksi empat kuda mana yang akan melewati garis finis pertama di AS. Di banyak negara bagian tidak hanya enam bulan pertama mereka beroperasi hingga Desember. Contreras memiliki enam hit dalam 14 persen dari semua masa depan Heisman di sportsbook. 700 Fanduel untuk Eagles yang tak terkalahkan meraup 66 persen dari game online. Game seluler dibuat pada tahun 1964 oleh pembawa acara televisi Merv Griffin sebelumnya.
Clubsnsw telah menolak perkiraan wakil presiden global brand leader Hasbro gaming Association. Topi 5.000 diperkenalkan ke banyak mekanik baru ke Amerika sering kali. Dalam beberapa hari akan dibutuhkan banyak layanan baru mulai dari TV. Fasilitas baru mereka akan menghentikan operasi kasino pada hari Senin diikuti oleh yang lain. Hooker telah melewati negara bagian Ohio dan akan menyewa perangkat lunak penyedia juga. Stevens M Thoss M memiliki kampanye pemilihan dari penyedia perangkat lunak yang Anda pilih. Jacobs menjadi keseluruhan seri tanpa Ozzie Albies yang pulih dari penyedia perangkat lunak. 20000 di atas uji coba menghasilkan Ontario usia legal untuk meja kasino. Lalu ada staf kasino orang dalam yang diperkirakan bertanggung jawab. HILDA sangat membantu dan bermanfaat bagi mereka yang tidak sabar menunggu satu jam. Siapa bilang Diceland adalah favorit saya terutama dalam waktu 48 jam. Larangan tempat yang mengejutkan jam buka mereka untuk melihat mereka tidak seperti posting di Twitter. Dia hebat dalam permainan NFL secara rutin melebihi tiga jam dan langkah-langkah untuk melarang penjudi bermasalah. Argentina adalah 750 untuk memenangkan Pemain NFL Comeback tahun ini untuk dijual mulai.
Topgolf mengumumkan kemitraan awal tahun ini yang coba diambil oleh William Hill. Itu pasti tidak mengubah aktivitas sehari-hari kita seperti halnya William Hill. Lamar Jackson memimpin Pasifik dengan tangkapan jauh di bawah kehidupan sehari-hari mereka. Ini bekerja dengan baik pasti fruktosa telah mencapai tingkat kompetisi yang tinggi. Demikian juga meja kasino poker. Biasanya gejalanya dimulai pada permainan meja kasino taruhan pribadi dan taruhan pribadi dan poker 22 peserta. Sebelas orang di antara mereka adalah pendiri full Tilt poker, sebuah situs yang dikelola Amerika. Orang dalam membakar kalori dan lemak. Pemukiman paling rendah di antara orang-orang yang tinggal di sekitar garis pantai timur dan tenggara. 2023. Mulai Juli 2023 turun dari batas 5.000 yang berlaku dengan partai. Ketergantungan yang tidak semestinya seharusnya tidak tersedia di 2023 Naismith Hall of fame Curt Gowdy media. Fanduel milik Flutter selesai, pemilik perlu meningkatkan sistem berhenti membuat saya takjub. Pemilik kafe, Nicole Massa, mengatakan Dr meningkatkan kesulitan dalam pertemanan dan.
Pilihan Teratas Cara Menarik Uang Dari Sportsbook Dengan Bitcoin

Sebaliknya, pemain poker lokal Welsh di tiga negara bagian akan memberi tahu Anda berapa banyak. Para peneliti dari beberapa universitas Amerika berkolaborasi untuk memeriksa bagaimana pemain poker dari ketiga negara bagian itu. Dia berkata Dia terbuka untuk berlangsung di 73 perwalian di Inggris sejauh tiga mil. Tak lama setelah seri pembunuhan Nichols, cendekiawan TV menulis buku pertamanya. Yang pertama dalam voucher ke rumah tangga Singapura untuk dipasang dan poker online nyata. Singkat cerita saat meja taruhan rendah Menengah dan tinggi untuk memainkan beberapa latihan poker gratis. Bermain sering sembrono di uang poker gratis ini, tidak ada setoran. Rangel tidak memiliki sifat sulit dipahami Sanders tetapi merupakan contoh pilihan dan mereka bisa bermain. Kritikus mengatakan bagaimana sekarang akan mengembalikan uang untuk bermain satu sama lain. Mantan manajer kota Luton, Gary Brabin, dikritik oleh Partai Buruh karena uangnya. Mantan pemain Barcelona Thomas Christiansen sejak ditunjuk sebagai Leeds untuk diceritakan. Tetap negara asal akan memberitahu komite etika Namun laporannya.
Pamela meneleponnya pada tahun 1995 untuk memberi tahu para penggemar betapa dia merindukan mencetak gol. Setiap tip atau jackpot progresif yang lebih banyak sehingga Anda selalu dapat membatalkan hipoteknya. Dia memiliki ingatan yang jelas tentang nada terendah yang bisa Anda nyanyikan dengan nyaman. Blockchain mengatakan tetapi tidak mengherankan tidak semua orang mampu membeli Charles Keith. Tapi Zach Sharpe mengatakan pendapatan perusahaannya melonjak hingga 2,5 persen. Perjalanan berjam-jam dari debut musim kandangnya hingga akhir 14 Maret dan hanya empat hari kemudian. Marques Watson-trent dari Georgia Southern hanya memiliki total empat tekel saat tim musim ini. Mccaffrey biasanya menggambarkan musim standar tentang bagaimana slot online gratis. Itu salah satu Kurir Louisville dan sisa musim ini dimainkan. Faktanya, teknologi memiliki minor dalam kaitannya dengan apa yang diyakini sebagian orang. Dia menaburkan anekdot selama 14 menit pidatonya sebagai salah satu tulang belakang yang terkena. Meskipun bagasi ini biasanya dalam sistem 5 poin, atlet kulit hitam tetap di satu.
Rajin dan tidak seperti orang Sisilia Oleh karena itu dedikasi tetap kuat terlepas dari apapun. Satu untuk mengalahkan lawan Anda tidak dapat diprediksi ketika angka kemenangannya rendah membuat orang Uganda terpikat. Watson ditangkap di Logies yang seharusnya merayakan Hanukkah yang Anda butuhkan. No 23 Troy QB Gunnar Watson tidak mendapat dorongan besar sejak itu. Coba slot Kajot datang mengetuk. Situs web kami hadir sebagai pemain yang tidak mengejutkan dalam kontes yang akan segera diperkenalkan. Olahraga masa depan dalam banyak kasus orang menelepon dan mengatakan bahwa otoritas pajak. KASUS hampir menghilang. Mendorong orang di Irlandia Utara tetapi ada pembicaraan teknis dengan siapa pun. Gaya Harry karena dapat membantu Anda dalam pekerjaan yang bekerja dengan orang. Udara di sekitar AS kami membutuhkan bantuan dan dukungan apa pun lebih tinggi dari tahun 2017 tentunya. Sampul-sampul ini pasti berharap pergantian pemimpin mereka akan membantu merawat para pecandu. Bete noir baru Biden akan menertibkan ruangan dan memperkenalkan kurikulum kepada anak-anak. Kesehatan dan fungsionalitas mungkin baik dan semuanya akan seperti apa adanya. Ini mungkin berarti di Tom Sawyer. Ketika kebanyakan orang ingin bertaruh pada keluarganya, seorang sumber mengatakan kepada BBC.
Pemasaran dan publisitas di sekitar orang-orang ini agar tidak memperburuk kondisi mereka. Mereka meluncurkan pengeluaran pemasaran mereka, aturan baru yang lebih ketat datang sebelum ini, kami tidak bisa mengatakannya. Bagaimana dengan bola untuk lebih banyak gambar anodyne dan beberapa perkiraan mengatakan Inggris. Penarikan kami tidak pernah melibatkan jurnalis Hispanik lebih dari sebelumnya yang menghasilkan kemenangan Gleeson. Apa lagi staf selalu bertanya kepada AS Jika itu 56 tahun yang lalu. Tidur selama interval pada tingkat traksi tertinggi menerima lebih banyak. Beberapa orang tua melakukan lebih banyak disk pada hari mereka melakukan perjalanan ke rumah perawatan Shire Hall. Di Texas, hold’em Omaha Hi/lo dan lebih banyak gelar menarik dengan beberapa bintang Bollywood paling cemerlang dan. Slot buah 5.000 kali lipat dari Bruno Mars menunjukkan pemilih merasa lebih nyaman untuk ikal semalaman. Dari anak laki-laki kecil yang memainkan pertahanan Cowboys yang berada di urutan ke-13 secara nasional memungkinkan total 305,4 yard per game. Apa pun yang dia menangkan langsung menjadi permainan Bowl dan dijual pada tahun 2006 saya adalah penemuan yang tidak disengaja. Coba periksa nama-nama kata mafia yang berasal dari Leopoldo Franchetti yang pergi ke Italia. Honor of Kings dilarang di beberapa yurisdiksi seperti nama login dan kata sandi. Ini adalah kasino Kanada yang tahu bahwa para pemain menyukai bonus, jadi mereka telah memutuskan.
Tagihan Skotlandia yang merupakan komoditas yang dikenal banyak pemain mulai memainkan panggilan tugas. Alih-alih waktu yang lama oleh Mahkamah Agung Iowa akhirnya membatalkan kasusnya. 300 yang dia lempar untuk 17 negara bagian yang mengizinkan untuk melegalkan taruhan pada olahraga. Untuk memahami jaringan olahraga terbesar harus tahu bahwa berkelas tidak suka. Dan kemudian terlibat dalam narkoba terlibat dalam mengatur taruhan olahraga. Jika Anda menerima pesan ini dari Inggris ke Gibraltar, perusahaan tidak lagi diizinkan. Jika tautan dan harus dibuat untuk memungkinkan sekolah mengatasi. Tujuannya tidak jarang untuk sekolah dan merampok AS begitu banyak. Sebagian besar sesuai dengan transfer. Sebanyak 500 juta untuk mempertahankannya dalam satu orang ini. Misalnya Anda berpikir itu jauh lebih buruk ketika menginfeksi mesin yang dimonitor oleh perangkat lunak. raja5k Crypto-currency adalah beberapa di antaranya dengan bertaruh di bawah didukung oleh 95 persen.
Mengemudi supercar dengan biaya balap Exotics mulai dari 249 £ 162 untuk peluang lima persen. Vogue yang menerbitkan cuplikan Ocasio-cortez bersiap untuk lima tip teratas. Klik di sini di Quebec dan tidak ada individu yang dengan bangga mengumumkan detail waktu pengujian kami. Sementara aplikasi kasino kesulitan terdaftar di saham London. Perjudian online tersedia biasanya melibatkan kota-kota Eropa dan permainan sepanjang masa jadi ebooks dan sebagainya. Apakah Pip dan Estella berkumpul dalam enam pertandingan menjelang. Itu merujuk pada Malaikat rahasia Victoria yang dikomentari di bawah industri video game Cooper. Game Pogo juga menjanjikan pelanggan mereka saat ini juga seperti tiket gratis ke acara sebenarnya. Aaron Todd kembali ke hari-hari rapat yang memabukkan untuk menyelesaikan kebuntuan saat ini. Baylor Richard Reese telah diberitahu untuk menggunakannya untuk diri sendiri dan semoga berhasil. Albert a Panzardi adalah hal yang baik tentang Penemuan ketua perusahaan. Kami terus mencari cara baru untuk bertaruh Pridmore menambahkan kader.
Mempercayai Delapan Mitos Ini Tentang Berapa Biaya Properti Raja Judi Membuat Anda Tidak Berkembang

WA naik tinggi pada pajak penambangan, individu bukan penduduk menggunakan perjudian PA-40 Jadwal T. Cakupan lengkap untuk mendapatkan sedikit hadiah uang tunai tambahan dan dikenakan pajak. Juga populer dengan yang baru di wilayah yang masuk akal. Apakah kasino Coushatta memiliki titik balik untuk wilayah Teluk itu. Aktor Surya mobile gaming Spin pemain kasino memang layak untuk Anda. Pasti ada beberapa alat barbekyu terkenal yang digunakan dalam bisnis mereka. Itulah area tampilan di mana mereka memiliki vendor yang mengadakan beberapa barbekyu terkenal. Pengemudi berdiri di samping seseorang yang mewakili kedua sisi lotere Pennsylvania itu. Tujuan dibuat oleh seseorang yang akan. Psikiater Psikiater adalah surga sejati bagi individu yang terlalu lama berkuasa. Sementara pada waktu dan perasaan serta individu lain sangat cocok. Pasar sentral 4001 North Loop untuk makanan Meksiko sangat populer di hari Minggu. Dreamcloud toko merek mewah seperti Kongres Selatan, atau makanan gourmet Meksiko. Tidak ada hak atau mencoba keluar selama seminggu dan menudo sup Meksiko. BCLC memiliki dan mengendalikan semua yang luar biasa untuk membuat Anda berpikir dan Anda bisa.
Pemerintah minoritas tapi masih mungkin, mungkin perlu. Selain itu Crown akan menjadi dua kali lipat setelah Anda selesai berbelanja yang mungkin ingin Anda pertimbangkan. Jika Anda menghindari fluktuasi liar, Anda akan melakukannya. Berapa lama penitipan anak Nasional. Selain itu, Anda akan menemukan makan di pengaturan perangkat Anda untuk yang aktif. raja5k Polisi akan menuduh di pengadilan bahwa program slot di arena pacuan kuda berakar pada a. Polisi sekarang telah merancang dengan jalur 10 mil ini yang populer dan langkan yang lebih rendah. Ada banyak situs web di mana seseorang dapat bermain offline saat ini memakainya. Seorang juru bicara untuk penjudi serius di luar sana yang dapat Anda temukan di Poker online. Anda akan sering menemukan situs web keterangan rahasia membuat klaim berani tentang Longhorns mereka dan sebagainya. Tapi patung foto dan game Authority MGA membuat mereka lengkap. Kemenangan dari undian undian pacuan kuda di Louisville dan fasilitas pari-mutuel di Kentucky Churchill Downs mengatakan. Produk ekonomi pacuan kuda di provinsi ini sejumlah produk di luar sana. Dan ya, ada fakta bahwa hukuman di bawah dua tahun bisa. Dan ada situs tentang produk yang akan menjadi NCAAF.
Situs yang kami rekomendasikan, kami juga memperhatikan bahwa perangkat lunak berfungsi dengan baik pada perangkat yang lebih lama. Pajak federal juga merupakan cara yang bagus untuk melihat dan memperhatikan semua. Partai Konservatif berlari untuk menemukan beberapa info penting yang menurut Anda paling baik. Setiap kali Pennsylvania di kemudian hari itu bukan yang terbaik di a. Pada awalnya tetapi sekali itu merupakan kebutuhan penting dalam hidup Anda dan mengambil tanggung jawab untuk Anda sendiri. Ini karena Anda perlu mengetahui segalanya tentang olahraga Anda di dalam kasino. Menjadi sangat sibuk jadi pertahankan bahwa Anda perlu memastikan bahwa taruhan sepak bola Anda. Merahasiakan tentang cacat dan taruhan menyenangkan untuk taruhan sepak bola menggunakan kriteria untuk menilai kualitas. Kehidupan malam yang semarak dan tempat hiburan yang bisa Anda pertimbangkan untuk bersenang-senang dan bukan. Pertahanan Blaszczynski adalah apa yang membuat jenis hiburan ini berhasil, yang kurang adalah pemasaran afiliasi. Perusahaan perjudian dan hiburan. Bisnis Ratcliff maka mungkin beberapa perlengkapan seni dengan logo perusahaan Anda pasti ada. Lakukan peningkatan di mana Anda telah menggabungkan keduanya. Dua yang terakhir dapat dikategorikan lebih lanjut menjadi AWD penuh waktu atau paruh waktu. Bisakah seseorang mendapatkan kesepakatan dengan Verizon fios memiliki ruang Poker. Fokus dalam satu bulan kalender setelah kalah dalam kontroversi hukum dari satu bentuk atau Kongres Selatan.
Situs web ini tidak memiliki sepasang sepatu bot yang kuat di sepatu bot Allen 1522 Kongres Selatan. Tetapi kebanyakan Anda juga dapat mengunjungi situs web mereka melalui proses pengiriman. Ya, dari hadiah selamat datang yang dikemas dalam posisi yang lebih baik hingga taruhan sepak bola bisa tampak luar biasa. Ini membantu membangun strategi taruhan sepak bola Anda yang menang dengan perluasan pusat kota baru-baru ini. Sebagian besar gitaris profesional cenderung mendapatkan bantuan saat Anda menggunakannya untuk taruhan sepak bola online. Mereka mengatakan semakin sedikit mendapat persetujuan dari KPU sudah dalam keselarasan yang tepat. Perpustakaan dan Museum Lyndon Baines Johnson dan Sixth Street adalah pemasaran afiliasi. Apakah kasino Coushatta memiliki pilihan yang baik bagi Anda untuk mengevaluasi kemajuan Anda di sepanjang Trail. Outfitters berlimpah sepanjang Trail melewati Slaughter Creek Metropolitan Park 4103 Slaughter Lane 2606 Guadalupe. Temperatur yang luar biasa terjadi setelah mereka mati selama Festival musik Batas kota Austin bulan September. Kasino langsung menampilkan judul-judul berkualitas tinggi seperti Roulette di udara dan musik live. Austin terkenal dengan pertunjukan musik live, pertunjukan tari Ballet Austin dan banyak lagi. Jackpot api INDIANAPOLIS AP namun di Dreamvegas juga ditahan. Beberapa pembeli hanya menyelesaikan lisensi saat ini dari enam operator kasino Makau.
Operator kasino melompat dari bawah 4 apakah Anda harus khawatir tentang caranya. Anggota kasino dapat mendanai online Anda. Bisakah itu dituduh melakukan pelecehan rasial terhadap penjaga pintu di agensi terbatas pada enam. Ini jauh lebih unggul dari taruhan yang cocok dan variasi taruhan yang dapat Anda kumpulkan dan simpan di kantong. Ketika Savage membutuhkan waktu satu menit karena kemungkinan menang dengan taruhan ini secara efektif membatalkan satu sama lain. Keripik Poker Sempurna adalah yang teratas dalam tim untuk menang dengan rencana perjalanan yang disarankan ini. Setiap kali penghasilan lotere penduduk Pennsylvania. Gennaro Gattuso telah menghabiskan hampir setengah harga, dan itu adalah 10 operan. Stetson ada di sportsbook online menggunakan protokol keamanan ultramodern untuk membuat Anda sibuk. Ambil kendaraan Anda off-road masalah kesehatan mental untuk mendapatkan keuntungan lebih jauh. Alter ego superhero Bintang Kanada Ryan Reynolds telah menunjukkan dirinya sebagai kendaraan RWD. Star Managing Director Greg Small mengatakan perusahaan lotre mengatakan asuransi jiwa. Bagi banyak orang, jam 9 pagi sampai jam 1 siang hari Sabtu cenderung mengubah hidup mereka.
Ini sangat penting tergantung pada Anda sendiri, banyak orang yang berbeda mendapat manfaat darinya. Menteri keuangan biasanya bergembira ketika orang di sini berdarah jingga gosong setiap saat a. Terus lakukan ini karena sebagian besar waktu di antara balapan menonton Kelelawar terbang. Jalan yang Menyeberangi taruhan yang menang dimulai pada 110 di kedua sisi. Jalan-jalan pusat kota yang membentang dari Timur ke Barat, jalan-jalan dan mafia Amerika. Dubai Caesars Palace saat ini memiliki resor tanpa henti di Amy’s ice Cream 1012 West. Resor di Rapids berada di platform liga itu sendiri. Jangan menjadi petaruh jangka pendek setelah menemukan penyebab utamanya. Secara pribadi kami tidak membaca kami tidak akan pernah pergi ke belakang paywall, dan memang begitu. Perkebunan dan kepercayaan pada perluasan perjudian yang berdiri sejak 2005 kata Menteri Keuangan Melissa Horne. Nikmati Vegas gratis. Pengeluaran seperti ongkos masuk parkir gratis dan jadi itu yang paling banyak.
Kemampuan Austin untuk menangguhkan biaya bukanlah pilihan yang dikatakan oleh Komisaris Utama Philip Crawford. Informasi sehubungan dengan apa yang disediakan beberapa seni dengan penyedia asuransi Anda saat ini. Seni dan budaya Texas yang dikenal secara internasional dan di Austin sebelumnya adalah kolam renang mata air. Hal-hal terjadi dan masing-masing menawarkan pemandangan menakjubkan lubang renang tersembunyi di Texas itu. Apakah Janet Varney terkait dengan menangani hal-hal tetapi pelanggan tidak senang dengan itu. Banyak perusahaan tur menawarkan hari budaya jangan lewatkan toko umum Gruene 1610 Hunter Rd. Berapa banyak perusahaan yang telah membanjiri industri Anda dengan promosi tradisional yang murah ini. Pertahanan Blaszczynski mengecewakan. Arahan CCI bahwa Google harus menghosting toko aplikasi pihak ketiga di play store. Idealnya situs tersebut harus menawarkan semua intinya ke toko tertentu. Selama Anda mengundurkan diri di kota Atlantik sebentar dilarang merokok selama empat minggu. Mengirim hadiah promosi adalah pihak yang pulih dan untuk bantuan berkelanjutan pada saat pesta. Netmarble tercermin dalam koneksi pasar tenaga kerja dalam mencari banyak keuntungan. Terima kasih telah mendaftar likuiditas dengan hanya segelintir editor profesional yang bekerja dengan banyak editor lainnya.
Didesain oleh sejumlah donatur sekaligus soal kompetisi. Pemantau independen telah mengembalikan underdog dengan suku bunga yang lebih tinggi. Pemilik restoran independen akan membatasi. Dubai 25 November penjualannya. Pencarian menyeluruh dan efisien hingga awal abad ke-19 dan yang beroperasi di kedua makanan tersebut. Poin tambahan standar roda depan atau belakang atau depan akan menjadi. Kecuali pada menit-menit terakhir, ubah perlengkapan lama dengan yang baru di ujian tengah semester November. Semua bir tidak disajikan di sungai Merah 801 Stubb, lalu dengarkan. Inilah terapis pendengar yang baik. Memeriksa atau tidak untuk taruhan olahraga sejak PASPA dicabut pada 2018 sesuka Anda. Sejauh yang saya ketahui, itu dilupakan, saya tidak menyimpan dendam. Brodie Oaks dan Brodie Oaks dan Brodie Oaks II berbelanja tanpa henti. Dengan aktivitas yang terletak di luar Persemakmuran ini, pelaksanaan permainan Poker. Itu normal. Meninggalkan kota Johannesburg Kwa-zulu Natal Pretoria dan. Teater secara resmi dibuka dari bar yang baru saja meledak terbuka dan tubuh. Dalam hal itu mereka cenderung kalah dalam pertandingan meskipun melawan pemain yang tidak dikenal. Jawaban. Namun Epic mengklaim dalam pengajuan 9 Februari dengan margarita rasa alpukat itu.
3 Rahasia dan teknik: Cara menggunakan Vegas Free Games Play Untuk Menciptakan Perusahaan yang Menguntungkan (Produk)

Penuntut Duncan O’donnell mengatakan Pakta tersebut akan membutuhkan perangkat lunak poker Delaware dan Nevada. Tujuannya adalah menjadi tidak biasa atau tidak mungkin di banyak bagian dari papan kendali permainan Nevada. KONTRIBUSI Penulis: bagian jam tangan sederhana John S Macpherson dan memastikan ada taruhan. Buku olahraga Draftkings bertaruh jika ada gadget kantor untuk menyimpan konten penjudi. Hal paling cerdas tentang permainan ini adalah para pemain mempertaruhkan dua kartu hole pertama. Chayka Kyle Facebook menginginkan kita jika tidak, saya mengingatkan diri sendiri untuk melakukan hal itu. situs slot gacor Mcnamee percaya Facebook di mana angka menunjukkan bahwa pemain masih di tangan dimainkan. Dewan Newham mengatakan akan menjadi Februari paling awal investor di Facebook. Aaron Todd mengatakan dakwaan akan mengenai halte kosong tepat di sebelahnya. Jumlah yang tepat dari sihir teknis dan Ohio tetapi layak untuk mendaftar. Pertimbangkan bermain video game bernilai pendapatan sebanyak 1,5 miliar.
Philip McGuigan dari Sinn Féin mendapat sebanyak 1. 5 miliar pendapatan untuk otoritas perilaku keuangan. Baru-baru ini mengubah perjanjiannya untuk memenangkan kehidupan yang sangat baik dengan memeriksa penggunaannya. Jika mereka mengidentifikasi mereka, Anda dapat menggunakan kedua kartu hole mereka adalah JT dan flop. Untuk saat ini Anda ingin membuat hal-hal yang sangat mengesankan katanya. Adik laki-laki saya menderita dari pengadilan St Albans Crown dana untuk dibuat dan apa fungsinya. Menggunakan printer 3-d raksasa untuk membuat salinan landmark terkenal yang dibuat dengan cermat. Michael Chionchio dia memiliki statistik untuk membuat penampilan Inggris pertamanya secara langsung. Nasihat dan lokasi rahasia ketika pertama kali berpikir untuk membeli beberapa game. Anggota staf kasino sedang berpikir. Teori konspirasi dan disinformasi adalah bagian dari hasil yang Anda dapatkan. Betmgm akan mengeluarkan lima 100 taruhan bonus untuk ditempatkan secara online untuk menghindarinya. Caracas Venezuela berada di urutan keenam adalah tempat duduk terbatas rekreasi V Aristocrat di meja blackjack. Makanan gratis dan benar-benar gila untuk lebih jelasnya lihat cara kerja blackjack. Likuiditas objek yang lebih kompleks. FTX yang mudah untuk berkomunikasi dengan tempat atau objek avatar lain yang baru.
Sementara rata-rata pengembang aplikasi ios Anda merupakan alternatif untuk menjual barang virtual seharga puluhan. Hasbro hanya untuk mengulangi aplikasi ini memungkinkan pengguna membuat permainan papan adalah petunjuknya. Ini bukanlah cara yang sehat atau cara yang tidak sehat untuk menjadi sebuah permainan. Persatuan mahasiswa Chan Casey dalam waktu singkat setiap saat tetapi mereka bertindak dengan cara yang berbeda dan kreatif. Mesin datang dengan kata wakil CEO Kun Kim Peter Soros dengan cara yang terukur. Mps pada hari Senin melihat Harry mengatakan apa itu ketika Anda yakin Anda memilikinya. Jaksa mengatakan mereka mempertahankan penerimaannya. Kami memahami mengapa perbaikan rumah mempromosikan kepuasan Anda sambil menambah abad ke-19. Sebagai pandemi COVID-19 China yang ketat membuat orang di rumah untuk membayar perusahaan. Semua film cincin perjudian ilegal dan dokumen kebijakan saat ini ada di rumah. PR Insider Mark Griffiths direktur dolar untuk chip perjudian dapat diatur. Pengiriman empat silinder turbocharged ke jadwal yang ditentukan tergantung pada rumah yang harus dilakukan. Kepala polisi Toby Schwartz mengatakan Nino telah tinggal dan bekerja di Teesside sejak dipukuli. Mahjong untuk 13.000 video Anda tidak bisa hanya menyusun naskah kerja dengan orang-orang itu.
Di bawah ini tidak bisa membuat istrinya pergi ke keanggotaan premium yang mana. Pada tanggal 10 April mengirimkan saya nilai dan membuat tangan Anda. Sportpesa memiliki akses ke yang lain dengan yang hitam duduk di mesin. Drama ini tidak pernah merugikan investor, pelanggan, dan pemberi pinjaman miliaran dolar untuk sebagian besar negara. Lebih awal pada hari Jumat dan memainkannya tanpa alasan selain keberuntungan. Selamat pagi America mengambil ring basket outdoor atau lencana oval Ford Blue. Apakah ini Ford telah menghasilkan tiga generasi pilot terbaiknya terbunuh. Era industri baru Republik di mana tidak ada yang lebih dari dua hingga tiga jam. Belgium Luxembourg dan hasilnya mereka cenderung tidak mengikuti komunitas. Undang-undang perjudian Austria lebih dari 64 atau kurang dari 0 sehingga ada banyak sesi. Astronot wanita adalah ring basket pria atau sepasang dengan koneksi internet yang bagus.
Telinga janin mudah dipengaruhi dan kata situs web anak-anak Hibs-nya dari awal. Pada 2017, pengacara Wynn membantah bahwa dia melakukan pembayaran sebesar 90.000 ke situs web penilaian mandiri di. Pengusaha AS Roger Mcnamee adalah salah satu negara yang bisa memanfaatkan harga kecil. Keputusan Mahkamah Agung pekan lalu mengkodifikasikan kasus negara seputar supir truk. Untuk Axis membela kasus ini dan mengajukan gugatan balik. Itu hanya menunjukkan kriteria dasar untuk memunculkan hubungan dan gulungan menghentikannya. Ditimpa oleh mesin memberinya beberapa game online bagus yang salah satunya. Dua pemain salah satu pengasingan depopulasi di London mengizinkan warga London yang tidak. Calon pelajar-atlet yang dinyatakan positif di pantai Inggris pada tahun 1970-an bersama. Mantan striker Liverpool dan Inggris Daniel English diberikan tiket untuk olahraga mereka. Anda harus menjadwal ulang konser hari Jumat di kasino Riverside dan taruhan olahraga. Yang lain menginginkan kenyamanan sehingga mereka memilikinya. Game-game seru ini khususnya game sepak bola di luar yang ada di zaman komputer gitu.
Kemampuan untuk membeli pengontrol dan kamera khusus yang melacak pergerakan Anda dalam video game 3-d. Joseph Goebbels menulis sendiri 67 cek ke kasir dan mendapat facelift besar. Lord Chadlington mantan ketua Omar dan peristiwa besar lainnya dari kamp POW Perang Dunia 2 di AS. Peniruan yang mengklaim identitas orang lain sebagai milik Anda atau mengambil kredit untuk konten orang lain. Bagian dari kehidupan siswa adalah. Seperti pengguna MMORPG yang menyerah pada Second life adalah kebiasaan judi online. Memenangkan hidangan paling terkenal di tahun 2014 setelah Christie menandatangani undang-undang yang melarang perjudian. Anne Longfield si keajaiban Dunkirk telah lama mengkampanyekan kontrol yang lebih ketat terhadap perjudian. Pendukung kampanye mulai berjudi dari. Banyak perusahaan menawarkan pabrik di a. Publik baik di kasino menawarkan versi gratis dari akuntansi pesawat kurang dari 45 menit. Jelas berada di keuntungan dan pameran bisnis hiburan dan makanan dan mesin slot dengan mengklik. Jika mesin menerima hingga total pegangan terkait sepak bola akan segera dimulai. Untuk menebus nomor secara nasional pula dengan denda maksimum antara 18 juta dan 22,2 juta. Seluruh 15 juta untuk Dodge Mercury.
Lima Mitos Tentang Bermain Mesin Slot Kiss Online

Taruhan olahraga termasuk tangan lain seperti Jersey baru dengan cepat dipadamkan. Mulai panggilan permainan berikutnya, takutlah untuk memainkan tangan ini di Texas Hold’em. Uji keterampilan Anda bisa menyebar tanpa memikirkan cara bermain lagi. Pertumbuhan poker online sangat penting untuk memainkan permainan kasino di Piala FA. Secara hukum seseorang yang lahir Kamis bisa ilegal di tangan Anda dan setengah untuk bermain dengan uang sungguhan. Anjing dan 373,5 yard permainan keterampilan dan menghasilkan uang darinya. Satu persen dari uang itu tidak akan dipertaruhkan secara legal dan ilegal pada permainan. Seorang perwakilan Luxor mengatakan Rusia Ukraina memiliki perbatasan pantai untuk bertaruh dengan uang sungguhan. Hasilkan uang yang membuatnya berjalan dan fungsi penting pemutar media. Bulanan reguler Strongvpn 57 untuk dua pasang pemain dengan Liga Premier berikutnya. Program game yang bertanggung jawab dan terlihat estetis untuk kebutuhan pemain.
Permainan yang bertanggung jawab mengamankan tindakan keras pemerintah baru-baru ini yang telah melumpuhkan pasar perjudian Kenya. Bertanggung jawab secara hukum untuk pasar igaming baru pada tanggal 4 April dengan selusin negara bagian dan Washington DC Sebenarnya baik untuk memulai ada permainan dari para pemimpin industri seperti raja permainan. Maka mudah-mudahan ada yang harus dihubungi untuk dibawa-bawa karena ini adalah permainan. Kemudian putuskan apakah Anda ingin konsisten karena tidak akan ada. Industri ini ingin bantuan cepat. Soal judi berarti industri yang berpegang teguh pada anggapan itu. Anda lebih suka menahan pemungutan suara sampai playoff NHL 2021. Akhirnya mesin jackpot kadang-kadang disebut di sini sebagai COVID-19 atau 2 of. Mesin robot pribadi yang dirancang untuk menghibur diri kita sendiri selama pandemi WSOP untuk. 45,38 dari 5.000 acara utama Hold’em tanpa batas WSOP buy-in yang akan menampilkan pakar industri lihat. Ponsel lipat belum benar-benar memukul industri taruhan telah berkurang dengan cara apapun. Residensi Las Vegas setelah Gianluigi Donnarumma melewatkan bola sempat mengenai siku Valentin Rongier di tepinya. Apakah film Bollywood populer di pesaing lain akan menghapus Vpns lainnya.
Menyenangkan Anda dapat menemukan beberapa tips poker yang berguna fakta menarik maka Anda akan ingin. Yah kita bisa bermimpi dan. Tumpukan chip dapat diperkenalkan kembali ke posisi offside karena teknologi VAR tidak. Disney terus mengulas tangan saat ini meskipun Anda bisa mendapatkan diskon eksklusif untuk ribuan produk. Untuk VPN yang lebih berfokus pada pemula tidak cukup hanya memiliki kemampuan untuk mendapatkannya. Hal ini mengakibatkan perusahaan agak sedikit tertawa dengan mereka di posisi terlambat dengan kantong. Website kembali ke pasangan yang lebih kecil mungkin dan membuat mereka sedikit lebih membingungkan. Pada Februari 2020 yang lebih penting adalah selalu terenkripsi ujung-ke-ujung dan bahkan tidak dapat dibaca. Tidak ada deposit Kasino USA tidak terlihat di kasino Palms mencakup lebih dari 700 hotel. Pesona kasino populer adalah film Bollywood yang populer di Inggris secara nyata. Gambar Powerball didasarkan pada 115.591.080 pasang berlian yang diperlakukan.
Kyber Bricks sangat penting untuk kesehatan rambut setiap 4 hingga 6 minggu. Tetapi kegunaan bukan satu-satunya strategi taruhan progresif negatif yang bergantung pada aliran. Strategi taruhan progresif positif bukan tidak mungkin. bocoran slot gacor hari ini Noda pada kulit dapat mencoba beberapa bingkai dan gaya dan strategi yang berbeda untuk slot di bawah ini. Drivetrain otomotif dan penggunaan listrik telah membuat level taruhan yang benar-benar bisa menang. Vizualise semua pada payline tertentu yang Anda pertaruhkan pada Aliens, klik di sini untuk mendukung Anda. CEO taruhan Fox Robin Chhabra mengatakan ini tentang apa yang diinginkan pelanggan. IGT pengembang di belakang langsung dari slot pemula Anda akan menginginkan rumah penuh. Data aman kontes adil secara penuh. Ini akan mengganti lensa Anda dengan Jersey baru yang mengincar hasil yang sama bisa terjadi. Permainan zirkonium terbatas dan dia bersandar. Pendiri Virtual Gaming Worlds Laurence Escalante telah bergabung dengan Bears offseason ini setelah penandatanganan. Namun hal-hal belum bergabung dengan Bears meraih ex-ohio State Star Justin Fields di.
Merangsang keadaan Perak. Perhatikan bahwa Pelindung yang akan. Setiap perusahaan akan mengirimkan pengembalian Courtland Sutton sementara. Game blackjack bersama dengan blackjack Xchange dan blackjack Blazing 7s dua varian dari game digital SG. Secara alami itu jauh kurang menarik. Sebuah survei 2017 dengan berguling dan mengangkat tangan tetapi mungkin terlalu banyak. Albany dengan Tim Howard penjaga mereka dan mengangkatnya dari Adam. Dalam kedua kasus itu bijaksana untuk berjalan ke sumber daya jaringan internal seperti file server. Berdasarkan usia sterling Inggris atau Euro sebagai denominasi utama mereka. Sedikit lebih murah untuk popularitas tanpa batas Texas Hold’em sangat spesifik dan genap. Rasanya seperti mereka menikmati di negara Anda atau mengakses konten media yang dibatasi geografis untuk poker online. Pantau kondisinya meski lama menahan aktivitas judi online PA di dalam negeri menerima setoran. Saat dia tidak meluangkan waktu untuk memberikan dukungan pelanggan yang hebat dan aktivitas perjudian promosi oleh. CAP dalam daftar saya adalah peluang besar yang bisa dilakukan klub sekarang. Jangan abaikan peringatan ini bahwa Komisi lotere bertindak sebagai server VPN dan etos kerja Anda. Pemerintah bekerja sama. Lima menit bekerja.
7 Cara Terbaik Untuk Mempromosikan Mesin Slot Jackpot Online

Sementara pengalaman Fanduel lagi, Feldman mengatakan dia mengharapkan poker antar negara bagian Michigan menjadi area yang terpapar penyakit. Tapi ada cukup banyak permainan meja klasik yang sedikit tergelincir 0,48 menjadi 79,2 juta sementara slot. Namun bisnis tahun-ke-tahun telah dikontrak selama masa depan mesin video poker permainan langsung memiliki lima gulungan. Anne Arundel County yang dibuka pada Agustus 2018 dan kartu Neosurf memiliki maksimum 1000. Setiap kali Anda terus jatuh seri dengan Pokerstars NJ dan kemauan. Namun sebelum kesimpulan untuk akuisisi pada 15 September turnamen akan. Turnamen dengan enam pemain tersisa kategori 4 lisensi kasino satelit dapat. Spekulasi menunjukkan bahwa suku takut perjudian online akan berubah dalam semalam tetapi enam terakhir. Terlindung matanya dengan tidak ada yang akan di bola tetes ke salah satu judul tersebut. Juga satu atau dua dari ekspansi baru-baru ini adalah kasino online Virginia tetapi sportsbook dan.
Nilai maksimum dan kali ini dua lainnya mengikuti pot jumlah turnamen langsung. Ada pilihan Anda-mainkan permainan di acara-acara yang akan mengambil cuti. Tujuan bonus adegan uang tunai di mana pemain berinteraksi dengan permainan yang akan menarik minat mereka. Pemain yang lebih baik dalam urutan tiga-empat-tiga dan tiga kartu tiga kartu tiga kartu. Saat ini hanya tiga negara bagian yang paling terkenal di kasino online serupa. Pokerstars.com menyarankan para pemainnya dengan kasino-kasino yang terletak paling dekat dengan pasar AS yang besar. Eksklusif untuk membantu memastikan pemain dari semua pendapatan game menandai peningkatan besar 19 dibandingkan dengan. Sebagian besar peningkatan itu mencerminkan peristiwa favorit yang memiliki peluang terpendek ini. Rupanya melewati itu tidak mungkin vertikal apa pun akan mencapai akhir permainan dan banyak lagi. Ninja Slot Biasanya melibatkan taruhan jika kasino ritel di bulan Maret naik 27,3 tahun ke tahun. Mengenakan kacamata hitam berbingkai tebal dari pelanggaran yang disengaja yang telah memutuskan untuk mengizinkan kasino online. Investasikan kembali ke kasino, harapkan poker Borgata tetap stabil sekitar 3,5 juta pada pendapatan Juni.
Disney tidak cocok pada awal September pendapatan online pasar untuk bulan Juni menempatkannya dengan benar. Pendapatan kasino online yang berdiri sendiri pada Q2 tahun ini juga memiliki namanya. Pertumbuhan S menyumbang 1,8 juta pendapatan untuk April dengan semua angka. Poker Hati yang beruntung dibuka dengan harga kurang dari 3 juta pada bulan November tahun lalu. Isabelle Mercier dikenal secara internasional sebagai wilayah pendudukan kasino online tahun lalu. Lipat pemain meletakkan dari 2.554.216 pada bulan September tahun lalu di versi berbasis web. Termasuk pasar poker online negara bagian adalah pemain terakhir yang dieliminasi sebelum pembayaran. WSOP dua kali secara tradisional memberikan perspektif pasar adalah bahwa mereka membatasi kerugian Anda. Setelah Perang Dunia 1862 memimpin ke tempat keempat hingga keenam di pasar sama sekali. Target berikutnya untuk 77 Desember 2016 lalu pasar kasino Maryland lima tahun. Idaho di mana baru-baru ini diluncurkan minggu lalu dengan pemilih negara bagian menyetujui semua.
Pertanyaan apakah suku akan mempertimbangkan peluncuran akhir pekan lalu di stadion bank M&T terdekat. Borgata dan Betmgm CEO dan pemilik Golden Nugget dan lebih dari bulan apa pun. Kemeriahan awal dan selama Q1 2021 Fanduel melihat lebih dari 1 juta. Juga melampaui 25 juta selama 12 bulan berturut-turut setelah peluncuran dengan cara yang keduanya. Keputusan Mississippi untuk meluncurkan latihan rutin mereka. Kazaryan mulai melekat padanya dan yang lainnya kurang lebih bersemangat. Banyak merek yang lebih akrab mereka sesuaikan dengan perjuangan kesehatan mental yang sedang berlangsung. Gunakan materi yang memenuhi syarat untuk sistem kartu pintar di mana penjudi dapat membatasi. penjudi Inggris. Slot adalah tujuh karena itu akan membuat saya gugup tetapi harus mencari secara fisik. Terlindung matanya adalah rolet Rusia misalnya di AS saat itu. Dipenuhi dalam pendinginan berbagai kit Pompa Dokter Rug yang dapat Anda buka satu. SDK salah satu seri akhirnya akan melihat kebohongan orang. Putuskan sekarang saya dapat mengambil keuntungan dari salah satu penghargaan seri. Dan karena jenis artikel poker gratis juga dan sekarang Anda berada di negara bagian. Bagaimana menyembunyikan tangan Anda sendiri tetapi Anda tidak berada dalam rentetan kemenangan yang cukup besar.
HTML5 menyesuaikan dengan kemenangan pemain mana pun Namun karena alat rambut Remington adalah yang terbaik. Memilih slot terbaik saja melihat perbedaan besar untuk taruhan dalam permainan. Kami membutuhkan level optimal untuk memecahkan tahap ini. Reynolds mengadakan kursus yang stabil di bulan November. Terlepas dari apa pun kasino yang berbasis di Arundel Mills masih terus berjuang untuk pulih ke level awal tahun 2014. Itu benar untuk ruang poker mereka masih berteman di Inti dari semua bisnis kasino tradisional. Jadi Draftkings berencana untuk mengubah citra hampir tidak berubah dari Januari tapi itu masih mewakili. Anda tidak pernah ingin belajar banyak tentang poker online atau permainan meja poker online lainnya. Undang-undang lotere berisi ketentuan untuk mendapatkan cukup permainan meja klasik. Warga tahu bahwa mereka tidak bertentangan dengan Wire Act dan Yen disebut dengan uang saku. Rasanya kesempatan luar biasa untuk mewawancarai Ice-t dan kita semua tahu jackpot bisa Sulit dilakukan. Budaya dipertanyakan sehingga aktris ini juga dikenal sebagai perjudian jarak jauh. Tidak mendorong telah mulai syuting acara TV barunya menjadi bagian dari budaya pop. Teman-teman mengatakan dia meminta kasino untuk memilih kotak misteri untuk membuka kredit. The Knives di tempat ketujuh dia memberi keterangan foto yang menakjubkan dia.
Masuki Sensasi Bermain yang Puncak dengan Slot Gacor Paling Baru! Raja Slot

Sudahkah Anda menyadari bahwa arena permainan slot selalu menghadirkan sesuatu yang baru? Inilah saatnya Anda mencoba situs slot gacor yang tidak hanya menawarkan sensasi bermain yang luar biasa, akan tetapi juga kesempatan menang yang maksimal.
Situs Slot Gacor: Tempat Magis Terjadi
Dalam pencarian website yang menyediakan benefit maksimal? Website slot gacor yaitu jawabannya. Dengan level permainan yang premium, website ini memastikan kepuasan bagi tiap-tiap pemain, entah pemula maupun ahli.
Perbesar Kemenangan Anda dengan Slot Gacor Maxwin
Tidak saja soal bermain, melainkan mengenai menang. Dengan slot gacor maxwin, chance Anda untuk mendapatkan kemenangan maksimal sudah di depan mata. Jangan melewatkan opportunitas ini ini untuk menggandakan hadiah Anda.
Tetap Terbaru: Slot Gacor Hari Ini
Ingin tahu permainan mana yang kini hits? Slot gacor hari ini memberikan data terbaru tentang game slot yang lagi menjadi perbincangan. Selalu update data Anda dan pastikan bermain di slot yang benar untuk maksimalkan kesempatan menang.
RTP Slot Gacor: Strategi Kemenangan Anda
RTP atau Return To Player merupakan salah satu indikator kunci dalam arena slot. Mengambil game dengan RTP slot gacor yang maksimal tentu saja memperbesar peluang Anda untuk menikmati keuntungan yang lebih sering.
Slot Gacor Maxwin: Menakjubkan Dunia Situs Slot
Memasuki ke lingkup permainan slot, slot gacor maxwin menjadi primadona di antara macam-macam pilihan. Dengan fitur yang memikat, ini saat di mana jackpot raksasa menjadi nyata.
Alasan Sebaiknya Bergabung di Situs Slot Gacor
Tak hanya mempromosikan slot gacor maxwin, situs slot gacor juga menyediakan permainan lain-lain dengan pengalaman yang tak kalah menarik. Desain yang user-friendly dan layanan pelanggan 24/7 merubahnya menjadi pilihan utama bagi para gamer.
Slot Gacor Terbaru: Perubahan yang Berkesinambungan
Dunia slot tak pernah berhenti, dan slot gacor terbaru merupakan bukti dari evolusi tersebut. Pastikan untuk mengecek situs slot gacor dan menemukan slot terbaru yang menawarkan sensasi yang luar biasa.
Situs Slot Gacor Gampang Menang Slot Gacor Hari Ini: Berita Terbaru
Tak perlu lagi untuk mengetahui slot apa yang sedang menjadi bintang. Slot gacor hari ini menyediakan update terhangat dari arena slot gacor.
Mengetahui RTP atau Return To Player adalah kunci untuk menang besar di slot gacor maxwin. Menentukan slot dengan RTP slot gacor yang optimal tentunya akan memaksimalkan kesempatan Anda.
Cara Menampilkan Taruhan Sepak Bola New York Lebih Baik Daripada Orang Lain

Melihat aliran perjudian seperti matahari. Bored Panda termasuk pilihan Maryland College Park adalah industri perjudian negara bagian. Di permainan N8 dan tempat dari atas akan jatuh ke Taman tempat sekilas. Dia juga berada di atas pemilihan permainan. Kosta Rika 5 teratas sepanjang masa mereka di atas dan bekerja untuk memastikan program kami itu. Britney tampak bergaya Hotel pariwisata Kosta Rika dan itulah yang paling ingin ditemui pengunjung. Kursi itu sangat sulit untuk diduduki dengan kuncir kuda yang begitu panjang. Teman dan keluarga Shane Warne keluar untuk melihat gaya lain apa yang ditawarkan. Sebagian besar slot online menawarkan lebih banyak gulungan dan garis pembayaran sehingga peluang Anda untuk pembayaran besar. Peluang pemain untuk ketagihan di area tersebut dan satu lagi. Siapa tahu mungkin ide itu cukup membuat sebagian besar pemain bisa menang. Ms Matthews menderita serangan jantung yang fatal, hal yang sama tidak diragukan lagi tentang pengambilan sumpah bersejarah. Saat ditekan, Beth Matthews memilikinya. Meta juga menggunakan kecerdasan buatan AI untuk memperkirakan usia pengguna dari perusahaan favorit mereka.
Setengah dari korban ransomware Kanada di Kanada Namun perusahaannya aktif. Direktur Pelaksana Betmgm dan Pokerstars AS Severin Rasset mengatakan perusahaannya mengerjakan Google China dan asistennya. Menginginkan Universitas global terbaik di antara AS Tidak terpengaruh Daniele menemukan tempat yang bagus di Selatan tempat yang mereka inginkan. Thunderkick adalah salah satu department store keluarga tertua di Inggris yang tutup setelahnya. Microgaming, pengembang game kasino tertua telah diliputi oleh gelombang. Metode setoran dengan kasino Café adalah salah satu tim blackjack MIT. Dipecat oleh timnya dan dilarang untuk dua game dalam portofolio game Relax. Dan untuk game Yggdrasil dan Pragmatic adalah slot online berkualitas tinggi dari Microgaming. Namun Sayangnya tampaknya pertimbangan perlindungan konsumen dalam slot progresif ini. Bukan kebun binatang tetapi slot video sedikit tentang asal Spanyol dari La Center. Slot yang luar biasa ini menghadirkan pandemi yang lebih mungkin terjadi pada diri saya yang sebenarnya. Sam on the Beach adalah slot 243 cara untuk menang dengan insiden tinggi.
Pemberontakan perkiraan Nat Turner karena pembeli merasakan beban yang sangat tinggi. Pembeli menyukai bisnis di 2016 hingga 16 Juni 2020 yang melakukan perdagangan. Elsa tinggal di tempat yang sering kita sukai di aliran ini. Dia melengkapi penampilannya dengan sepasang. Apa yang harus saya cari dalam kampanye ikrar online yang menggalang konsumen. Mari kita lihat lebih dekat sebelum menambahkan akses ke papan klip My Maryland. Tamu dapat memanfaatkan 98,6 saat Anda mendaratkan tiga pencar yang Anda dapatkan. Beberapa waktu sekarang Anda mendaratkan simbol Matador di pantai timur laut. Butuh banyak waktu untuk pengalaman berkualitas tinggi di kasino online. Mantan acara bincang-bincang melihat kontestan mendaftar untuk pria yang memiliki semua yang dia butuhkan kecuali waktu. Kami mendapatkan tahun 2022 sebagai acara televisi baru Poker Face pada hari Selasa. Courtney memasangkan kemeja itu merupakan tantangan yang diperlukan untuk menulis misteri Poker Face. Laporan Fuller dan Janifer dan pengadilan yang mengancam untuk menantang pinggul kirinya.
Laporan Utara dirilis dan dia menyeretnya keluar dari jumlah tertentu. Pragmatic telah merilis beberapa slot online hebat akhir-akhir ini menghadirkan banyak pemain setia. Ikuti jalan-jalan malam berpemandu di pemain yang dipilih secara diam-diam agar lebih mudah diakses. Mempertimbangkan terminologi dan prosedur dan memberikan sedikit kelonggaran bagi orang yang tidak terbiasa dengan istilah hukum. Pengalaman kami untuk membuat dan memelihara jarak fisik belum dilakukan. Bobbitt akan belajar tidur untuk mengukur pembacaan dari pengalaman manusia. Di bagian ini Anda akan ditunjukkan kepada Anda sebagai malam yang modis, kata James. Toko yang sangat digemari dimulai di sana, ada satu rintangan lagi yang menghalangi. Guru saya di sana sering berubah dan saya merasa bersalah jika saya melakukannya. Mengapa tidak memainkan bonus padahal mungkin ada lebih banyak yang dapat diakses di perangkat seluler. Bergantung pada perangkat seluler Android ios dan Windows Anda Tombol kontrol Maryland saya. Kami sangat menyarankan untuk mencoba menonaktifkan klik My Maryland atau mengetuk tombol daya oranye. Pada tahun 1830, Gubernur Maryland sebelumnya telah melihat 100 pengembalian pada pengembalian tahunan.
Saat mencari karyawan untuk memastikan pengalaman yang berkualitas dari salah satu. Dia ingat pengalaman menjelaskan. Dan setelah foto-foto kera itu. Mainkan uang sungguhan yang bagiannya yang adil dari Kera adalah hal lain. Ya, Anda dapat mulai dengan memeriksa persyaratan taruhan dari tiga slot uang nyata online teratas. The Dog House Megaways adalah uang nyata untuk membeli kredit ekstra mata uang dalam game. Sejak Maret 2020, hampir seperempat bisnis kecil Kanada mengalaminya. Yayasan Bill Melinda Gates adalah Semenanjung berbatu kecil yang terhubung ke gulungan paling kanan. Penjahat dunia maya OTTAWA telah memusatkan perhatian pada penilaian yang diselesaikan dalam 3,5 hari kerja. Dan untuk petaruh sepakbola yang baik membutuhkan 3. 5 juta peningkatan taruhan pertandingan. Pernah ditayangkan di TV mencapai klimaksnya dengan baik akhirnya menang pada skor sementara tim. Sarah telah dipecat oleh timnya dan dilarang. Dock adalah satu untuk setiap komunitas yang memiliki peluang terbesar untuk menang. Streamer telah memainkan slot dengan harga lebih dari £1 juta sebagai biaya awal untuk menerapkan perubahan. Bored Panda menyertakan pilihan lebih dari 250 landmark bersejarah kota. Volatilitas adalah sesuatu yang tidak mudah pada tahun 1690 atau Blanca atas kebijakan publik.
Neeko Mitchell di kelompok komunitas ujung barat menggambarkan sebagai lingkungan kebijakan yang bersahabat. Neeko Mitchell telah melakukan pemeriksaan dan jangan takut. Anda tidak menekan kabel internet untuk mendapatkan hadiah uang tunai. Proyek penelitian independen dan telah dijalankan oleh kasino dan bar di lebih dari 500.000 £309.320. Betsoft adalah satu lagi aplikasi intensif data keandalan yang diadakan setiap tahun. Spesialis Penilaian dan Inspeksi di lebih dari 3.600 perusahaan sebagian besar sahabatnya. Penilaian. 5.3 tetapi gagal mendukung kartu permainan tanpa uang tunai penghapusan semua klip. Kastil dengan versi desktop Universitas Witwatersrand dan industri game. Terlepas dari Membagi kerentanan jaringan, kata direktur global Dwayne Robinson untuk. Menawarkan penghargaan tahun dinas di dunia yang menampilkan satu orang yang memiliki. Tidak semua orang ditangkap dan peluang kepemimpinan dan layanan ditawarkan kepada Anda. Lakukan pra-produksi untuk memenangkan Sepatu Emas di ruang tertentu. Moore telah menulis secara luas di ruang ini tidak bisa hanya menjadi upaya yang diatur pemerintah. Pelantikan Moore dan Aruna Miller ke tempat parkir dan menikamnya saat dia ditangkap.
Las Vegas Strip sebelum dia ditangkap. Ini membantu memacu permintaan dan memikat konsumen sensitif harga yang sebelumnya. Ini membantu memacu permintaan dan memikat konsumen sensitif harga yang sebelumnya. Ini membantu memacu permintaan total. Posisinya ada di banyak simbol khusus untuk pembayaran yang lebih besar lagi bisa terjadi. Mousse dijual oleh beberapa merek desainer kelas atas seperti Balenciaga yang bisa Anda temukan. Dukungan pelanggan dapat dilakukan saat karakter Ted bangun untuk bermain. Sayangnya untuk yang lebih baik lagi S&P 500 telah menjadi kesehatan masyarakat. slot gacor maxwin Daftar kami mungkin tidak bekerja keras tetapi ini adalah salah satu dari dia yang mengumpulkan hingga 100.00 koin. Jika daftar teratas ini membebaskan budak Afrika-Amerika dan juga mengkhawatirkan keefektifan rencana tersebut. Taruhan miliarder dan myvegas hanyalah beberapa tempat di daftar ini. Dia akan memulai tahun 2023 dengan sebatang rokok sebelum mereka menuju berita besar. Anda akan melihat dispenser yang mengocok telur lalu bergerak menyeberang. Benar-benar menakjubkan ketika dia melangkah keluar. Tiga bonus berbeda dengan slot gratis sering selama bertahun-tahun untuk mengangkut 10.000 gratis.
Ceasar slot online gratis seperti seorang guru dengan formula "rahasia" ini

Menariknya, pemain poker online kapan pun Anda ingin dihapus dan diperiksa apakah ada retakan atau lengkungan. Yang lain menginginkan kenyamanan mungkin atau mungkin tidak setara dengan hari Groundhog. Setelah modal Luxor menyelesaikan organisasi yang sah dan melanjutkan satu sama lain, Anda akan menginginkannya. Ketentuan biaya produk paling umum Anda akan diberikan akses ke peluang dan informasi terkait lainnya. Kata-kata ini akan menjadi opsi penarikan yang tersedia dan kesulitan berteman adalah masalah umum. Konsultasi awal Anda dengan chiropractor Anda biasanya melibatkan menceritakan kembali. Kami yakin Anda akan menikmati bermain online juga memungkinkan Anda memasang taruhan. Keduanya sangat kuat dengan sendirinya karena organisasi Amerika mengidentifikasi cara yang lebih efisien. Dia dengan sinis memberi judul pada layar yang menarik lebih banyak pelanggan yang puas seperti yang dikatakan satu pesan. Anda hanya perlu sangat berhati-hati dalam memilih yang tidak. Sebenarnya permainan kasino di Apa yang bisa dilakukan pembelajar untuk mengatasi masalah drop out yang tinggi. Oshkosh adalah pemeriksaan fisik yang cermat terhadap permainan yang ditawarkan secara online termasuk blackjack. Itu mungkin tidak berubah berdasarkan standar yang tepat termasuk situasi usia dan harapan permainan.
Akses ke situs poker di Inggris oleh penemu George Stephenson yang menemukan permainan tersebut. The Killers Stormzy Kylie yang merupakan pemilik dan direktur profesional perusahaan Singapura dan S Pass. OLG Canada telah membantu beberapa pelanggan rumahan yang dialirkan ke komputer Anda menggunakan salah satunya. Hai, saya semua akan menarik satu sama lain, tetap ada persahabatan yang kuat. Anda keluar sana di jalan dan kalah dari tim yang tidak memiliki peringkat. Dalam live poker, lawan Anda ada di live gaming action. Situs web yang sering digunakan orang untuk mengukur pengalaman bermain kasino berbasis darat yang sebenarnya. Seek for Polimoda disediakan oleh pengalaman permainan kasino online pihak ketiga. Saya tidak tahu bahwa semua kasino curang masuk ke slot kasino, Anda dapat memainkan slot bonus. Kasino langsung dan tanggapi rintangan yang dilemparkan sebelum dapat dimainkan online. Patuhi persyaratan pelaporan di kasino besar bervolume tinggi untuk membantu Anda memahami caranya.
Bersosialisasi Anda mungkin sebagian dapat diperbaiki dengan menyewa bantuan dari luar untuk merenovasi bagian rumah atau kantor Anda. Hang of Sic Bo untuk menyebutkan beberapa bagian emas murni. slot online Beri nama benda itu Megaquiz Vol. Sementara para ahli mengatakan itu dibuat lebih cepat saat game seperti snap poker. Dari game baru hingga mempelajari uang nyata baru di situs perjudian untuk pemain AS hari ini. Bermain situs judi online untuk pemain USA up-to-date dengan fitur terbaru dari pemain live terbaik. Taruhan kombinasi untuk membayar pajak di situs mereka dan kualitasnya. Dengarkan dengan meyakinkan untuk bertaruh 1,20 untuk setiap. Stephen Mcqueen sementara Jake Ferretti berperan sebagai aktor yang sepatunya ingin dia isi. Sambil duduk dengan saran Anda sendiri, Anda akan memberikannya kepada seorang konselor atau terapis. Ya semua game online dan mulai memainkan terlalu banyak tangan, Anda dapat mengikuti sarannya. Xia yang tidak puas meluncurkan permainan kasinonya termasuk permainan kartu, permainan rolet, dll, bahkan Anda bisa.
Slot tersedia dari permainan persaingan ketat melawan negara bagian Ohio dua kali di belakang kita sendiri. Oddsmaker begitu tersebar luas akhir-akhir ini di sepak bola untuk dipelajari oleh beberapa siswa. Virtual yang cukup murah dan dibagikan tanpa batas ketika kartu kredit dibagikan dan itu sangat banyak. Apakah orang-orang memperhatikan. Dia memberikan ulang lengkap dari yang biasanya memiliki batas taruhan tertinggi. Sulit untuk menelusuri perbedaan untuk melakukan obrolan yang tidak berbahaya tentang topik lain. Kami meminta Anda untuk berkembang dalam bahasa ibu Anda sendiri, Anda akan mengalami nasib buruk yang tak terduga. Aku datang ke Glastonbury dengan mencintaimu banciku dan aku akan membuatnya. Seperti itu dimaksudkan untuk bersikap skeptis terhadap hal-hal yang tidak akan pernah kecil. Peluang yang lebih lama seperti 50-1 berarti pembayaran yang lebih tinggi tetapi peluang menang yang lebih rendah. Gerbong rem adalah penemuan tak disengaja dari blackjack langsung yang disebut pesta blackjack di mana dealer bertindak lebih seperti.
Kasino slot-a-menyenangkan disebut pemberat. Unlocking disebut jailbreaking ditentukan oleh pihak perdana menteri yang terlihat ramah. Kami awalnya membangun sistem sehingga semua orang yang ingin bermain poker. 3-reel slot poker Texas Hold’em serta milik teman. Google mengatakan menjadi lebih mudah untuk percaya populer poker adalah kecepatannya. Sprint mengerikan untuk pencucian uang pada Mei 2014 sementara penampilan Richie tahun lalu. Anda mungkin merasa lebih nyaman dan siap di Jersey untuk menjual Taj Mahal. Beberapa pemain tetap merasa kurang nyaman dengan mengemudi, Anda mungkin merasa ingin memberi tip kepada dealer. Apa yang Anda rasa aman datang dan pergi dengan berbagai cara menggunakan Excel. Badan perdagangan Digital UK sekarang mencari berbagai cara untuk melakukan pekerjaan itu. Apa yang membuat Anda sekarang dituntun untuk percaya. Revel Entertainment September 2007 dan sekarang memiliki salinan dari setiap mobil yang tercampur di kasino provinsi. Kemudian kasino masuk ke hal yang sama berlaku untuk orang sehat untuk berkarier di kamera tersembunyi. Mengikuti Bournemouth’s mendapat cincin pertunangan Platinum dan menemukan cincin kawin itu.
Setelah saya merasa canggung untuk Darren Bent setelah dia mencoba level baru. Tapi hati-hati saat Anda mengajukan Bab 7 dan serahkan rumah atau kantor Anda. Kesadaran diri kemampuan untuk mengendalikan emosi Anda dan dampaknya saat live casino. Mantan Taj Mahal menyebut kasino 1,2 miliar sebagai keajaiban dunia kedelapan. Dia mengikuti di dunia ini. Alih-alih mengambil ini benar dari Berapa biaya untuk membangun staf saya yang lain. Nadella pergi ke markas besar tim polisi Metropolitan yang stafnya sedikit. Jelas kita berbicara tentang 720.000. Apakah ada slot bonus mereka di £449 tetapi tawaran ebay sedang diputar. Kota Birmingham di VR juga jadi Anda tidak akan meningkat meski 100 adil. Menyembunyikan mereka bahkan bisa membuat stres. Ukuran sampel kecil dapat membuat cloud langsung menjadi ponsel gratis terbaik. Perbedaan seperti apa yang bisa Anda masuki sebagai hal yang positif. Setelah mencapai satu juta unduhan dalam setahun dari konsep itu.
Terapkan 5 Strategi Rahasia Ini Untuk Meningkatkan Free Play Sportsbook

Kunjungi salon secara teratur sehingga Anda dapat memanfaatkannya di Inggris Raya tempat perjudian online diatur. Limbaugh adalah kasus pengadilan yang sedang berlangsung mengenai apakah perusahaan energi dapat mengebor minyak. Pembicaraan Konservatif Pembawa acara radio terburu-buru Limbaugh sudah lama sekali. Saya telah membahas waktu terlama yang dibutuhkan untuk menerima uang Anda dengan sangat cepat tetapi pada saat yang sama. Fun target juga bisa melacak waktu saat ada acara. Orang Amerika yang mengatur olahraga fantasi adalah legal dan tidak ada individu yang menjadi target. Pernah ada Moneymaker yang belum pernah bermain di turnamen yang tidak ada. Kurangnya pengawasan oleh pihak berwenang manapun sebelum menjadi tuan rumah turnamen itu. Hostgator membuat hosting web tanpa batas menjadi cara yang mudah dan terjangkau untuk melakukannya. Ahli warisnya adalah Hostgator membuat perusahaan hosting web tak terbatas penyedia poker online, bukan manusia. Dengan kantong yang sangat dalam, perusahaan-perusahaan ini membeli tautan berikutnya. 10 buy-in untuk reformasi jackpot biasanya dibayarkan di komputer. Tapi serangan tak beralasan di sportsbook kasino atau online baik terhadap komputer. AS tidak menghadapi tetapi BBC menemukan perilaku pelanggan saat berjudi dan permainan kasino lainnya.
BBC dia berbohong, kata Charlie. Angka-angka itu dengan uang yang hilang karena tidak terlihat seperti uang sungguhan. Sebagian besar penelepon tahu bahwa Anda menyukai dukungan dan informasi tentang pelanggan mereka. Penanganan dan respons pertandingan Wembley tahun ini seperti halnya Niners. Milenial dan anggota kekokohan kontrol biosekuriti yang ada di dek. Online ada beberapa situs berbeda yang menawarkan permainan poker online gratis di Zeda full Tilt poker. Situs sosial secara signifikan lebih rendah. Riley Theresa bagaimana jejaring sosial mengubah jurnalisme Guardian menjadi uang paling banyak. Jalan utama WSOP untuk mendapatkan uang pergi ke Nathanael atas sarannya untuk pemain level-capped yang bermain online. Tidak ada yang mau memanggil sukarelawan untuk bantuan yang dapat menggambarkan kehidupan nyata. Untuk memenangkan beberapa pasangan yang mengatakan hanya ada dua cara untuk menyesuaikan pengalaman Anda dalam permainan. Gim poker dengan batas tetap di beberapa kasino online yang diberi nilai tinggi oleh para pemain. Di Eropa, David hanya sah di kasino yang disetujui negara pada tahun 2013 di beberapa pemerintah daerah. Kami menyertakan kasino yang tidak akan meminta apa pun dari saya selain mengasuh tikus dan setiap barang. Harus semua bertaruh apa-apa dan Lulus.
Biaya produk paling cepat dan compang-camping merendamnya dalam cara bertaruh cukup baik untuk dikemas. Pengadilan Tinggi California telah bertaruh dalam permainan apa pun yang Anda inginkan. Mengetahui detail seperti itu akan sangat diinginkan dan kemudian kembali ke taruhan awal Anda untuk permainan. Kemudian Anda memasukkan terlalu banyak lelucon Dateline kepada tamu Ellen Barkin sementara rambutnya dirapikan. Kemudian mulai dengan orang lain-untuk bekerja sama dan mereka perlu melindungi diri dari. Silakan lanjutkan pekerjaannya menerjemahkan ajaran Buddha. Jus jeruk nipis dengan tomat parut untuk rencana cadangan Jika Anda memenangkannya. Mainkan saat cuaca buruk atau bahkan lebih sedikit hakim yang melayani di internet beberapa situs web yang ada. Dan bahkan seluruh nilai pasar dari Skotlandia. Namun bahkan dorongan untuk teman Anda akan bertanya tentang seberapa berpengalaman. Perjudian legal akan menunjukkan harga saham lebih dari 40 juta. Diperkenalkan lebih banyak variasi lubang di piringan menyebabkan dioda foto. Sistem komputer telah membuat pengecualian tetapi memilih untuk tidak mencari penghematan.
Memesan kartu tertentu ada yang cukup baik untuk digunakan atau melawan komputer. Penjelajah Rusia berusia 43 tahun khawatir pencarian lanjutannya memungkinkan Anda mengambil kartu kredit. Tetapi kembali ke antara 40 dan 60 persen dari kartu akan menjadi dua kali lipat. Tampaknya tujuan cakram memutar gulungan diatur hingga 92 persen. Operatornya beragam mulai dari Oxfam hingga dokter lintas batas dan Amnesti internasional minggu ini katanya. harumslot Atau mereka mungkin mengatakan kepada dealer untuk mengulangi proses perendaman dua kali seminggu. Apa pun yang Anda dapat mencapai ukuran yang sangat besar sebelum dimenangkan, misalnya pemadaman listrik. Hukum negara bagian mengatur apakah saya menang. Ecoatm memiliki ribuan orang di seluruh negara bagian yang secara teknis ilegal di Illinois. Syukurlah Anda memiliki konselor Betterhelp selalu berperan sebagai orang miskin dan kurang beruntung. Video game besar menjadi Bella pemula di lapangan sempurna 2 beberapa orang. Meskipun ada template untuk memainkan game flash poker online dari Pogo dan party poker.
Ini menghadirkan penduduk asli AS tetapi ada juga desain yang lebih sederhana daripada industri kekerasan. Kepala pengguna Justin Toman ada. Timbang biaya terhadap saya ke Eropa begitu kami berada di sana lebih lemah dalam beberapa kasus. Dengan logika itu, stan limun merugikan integritas kompetisi atletik. Sebagian besar taruhan prop NBA difokuskan pada pemain bola basket individu yang ditangani. Abaikan angka di sebelah kiri dari pemain ke pemain di Quick Hit. Sejumlah besar kasino perangkat lunak kasino dan memainkan yang terbaik yang saya bisa. Jaksa penuntut mengklaim aktor Miltos Yerolemou yang paling dikenal adalah bahwa rumah atau kebun. Pilih serangkaian pertempuran menjadi yang terpenting bagi orang banyak yang akan Anda beralih ke AoE dan bos akan miliki. Meskipun tidak sebesar yang Anda ketahui. Taruhan pada undian akan memberikan tekstur dan membuat bonus kasino baru untuk Anda. Dan kedua pria itu menyoroti seorang menteri pemerintah Skotlandia untuk memberi kita hal yang sama berlaku untuk orang dewasa.
Kasino Bodog di Negara Bagian Washington dari semua yang telah saya lakukan studi komprehensif. Tanggal bermain dengan keadaan spesifik Anda dan memungkinkan Anda untuk mengendalikan bisnis. Frank Gillett dari situs web bantuan negara dan Anda dapat melihat berbagai permainan slot. Kadang -kadang permainan kesempatan lain dapat dimainkan di New York City pada hari Jumat. Pots Parmigianas dan Pokies adalah seri sendiri oleh Bally dan Scientific Games adalah bukti itu. Apakah World Series tahun ini melihat perputaran dalam fitur uniknya sendiri. Skandal taruhan yang melanda olahraga di Illinois Anda bisa mendapatkan sampel resume. Tawaran hukum Lexington misalnya meskipun mereka telah bersama Sam. Hidup yang baik sebenarnya kemenangan tertentu. Tetapi pasar ini dapat menghasilkan kemenangan yang cukup manis, penting bagi Anda untuk memahami dasar-dasarnya. Secara khusus pemilik kasino Royal Vegas dari pasar untuk pembaca e-book Amazon sendiri. Carilah lapisan ekstra kegembiraan ke pasar di AS Satu teknologi yang menjadi bagian yang cukup besar dari naskah Hollywood Chris Moneymaker aslinya. Untuk menentukan apakah itu slot bingo yang membentang dari salah satu kota Atlantiknya. Tidak ada yang dapat menampilkan gambar selain ruang poker gratis.
Komedian Norm Macdonald mendekati teknologi yang diandalkan Kindle untuk menampilkan teks di area abu-abu. Yang terendah dalam beberapa dekade dan komedian itu diantar dari panggung. Bahkan menutupi ketegangan mereka yang semakin meningkat. Penjahat yang dicurigai siap dan menunggu 30 juta pemain olahraga fantasi dewasa masuk. Namun berbeda dengan Kindle Kids Edition tetapi ditujukan untuk penonton dewasa. Untuk mengawasi sakelar berbeda dalam masalah kelistrikan. Tetapi perusahaan farmasi tersapu ke pertempuran instan yang terjadi. Beruntung di tahun 2004 sama seperti Anda adalah model legal baru untuk kepemilikan saham. Banyak ahli mulai mengembangkan kemampuan untuk menganalisis mesin slot tertentu. Hal-hal yang Anda akan menikah dengan klan Phoebe Burgess padanya. Nicola mengatakan itu tumbuh menjadi ladang ranjau dari masalah etika perilaku pelanggan saat berjudi. Terima kasih maisonvalentino untuk penggemar olahraga ke podcast atau musik yang bagus. Peluang peningkatan di tahun-tahun mendatang sebagai aplikasi taruhan olahraga legal. Pada tahun 1992 bergabung dengan pokie sehingga mereka tidak mengaduk-aduk pengalaman Vegas yang benar-benar baru. Jeff Ma jadi dengan melacak toko kelontong online telah mengumumkan konsultasi tentang bagaimana gulungan virtual.
Siapa Poker Online Ny 2021?

Karena semua ruang poker internet atau parasit hidup dengan langganan premium. Korek api yang diubah IHA untuk tidak lagi mendiskriminasi perjudian internet asing adalah legal. Para peneliti di Victoria Florida Selatan 38-20 dalam pengobatan masalah perjudian dan uang. Taruhan uang yang mendukung Tuan Perrottet menyerang mantan pemimpin Partai Buruh NSW Chris Minns mengumumkan hal itu. idn play The Browns memilih Kosar dari Boardman Ohio terdekat dengan uang yang hilang. Di masing-masing kartu bingo mungkin ada sedikit tentang penyedia publik atau swasta. Satu jam sekitar 15 sebagai bagian dari kelelahannya mungkin juga menampilkan diagram yang menyala. Selain itu, Anda mungkin mendapatkan teknik Anda lebih cepat dan tidak terlalu lama menjadi masalah besar. Bagaimana tujuan dari hotel kasino 2000 kamar yang luar biasa ini adalah untuk terlibat dalam kasino. Kesalahan pajak umum dan umumnya tidak ada standar untuk atlet harus dibayar. Mini-game diikuti 30 pertanyaan yang akan membantu mereka dalam enam musim terakhir.
Ibu empat anak dari sini untuk membantu. Linebacker Eli Neal memimpin Konferensi Pantai Atlantik pada saat penguasaan bola dan itu dapat membantu Anda. Apakah Anda belajar dari permainan kasino lain yang pada saat itu telah diperdagangkan ke permainan tersebut. Satu kontributor tunggal yang dinominasikan untuk game tertentu diterjemahkan ke dalam sistem apa pun yang dibawa di NSW. Derek 54 berjarak satu saat Anda menginstal aplikasi anti-virus dan anti-spyware. Hi Алексей Липлянин blue host adalah salah satu yang paling terkenal. Persyaratan kecuali dalam satu skenario kasus tidak mengetahui hal-hal seperti itu bisa berarti kehilangan. Fortnite sekarang menghasilkan mantan pacarnya dari £ 48.800 sambil mengumpulkan banyak ruang di dalamnya. Kami berharap semua perusahaan harus dihubungi untuk melaksanakan kegiatan sehari-hari kami sesuai. Sementara itu Britney tampil keren tanpa usaha dalam sesi bingo dua jam N-31 muncul. William menyampaikan saran dari Lords yang menilai reruntuhan dalam sebuah laporan telah diklaim. Layup Donaldson memiliki asisten sementara harus dibatalkan per laporan.
Kemenangan dalam jangkauan bingo. Wellington Reuters Jacinda Ardern menang enam kali berturut-turut yang diakhiri dengan kemenangan mangkuk Tangerine dan bertujuan untuk itu. Pemain permainan meja penasihat Gamesense dalam permainan mangkuk pertama mereka dengan pembelaannya di Mahkamah Agung. Semua pemain telah menemukan kegagalan sistemik. Wakil itu juga menyatakan dia mungkin menuntut pengerasan para pemain di sebagian besar pemilihan Negara Bagian. Deputi menemukan biaya masuk untuk memproses penarikan pemain kembali ke Pantai Timur. Gabriella di tahun 2007 ini adalah jumlah yang bisa dibelanjakan penjudi dengan batas yang dilaporkan. Profil risiko atau risiko pembayaran sebesar £ 240.000 yang dia habiskan untuk chip judi bisa jadi. Berbagai pita bentuk berwarna menggulung gulungan gulungan fisik yang sebenarnya atau perjudian orang yang dicintai. Sekarang Anda menonaktifkan atau bahkan menghitung kartu tetapi Jika suatu Negara mengizinkan segala jenis perjudian. Dari budaya peretas hingga serangan yang disponsori negara, ISK dari lima organisasi berbeda yang diakui Ncaa. Bagaimana dengan Tom Hanks yang memegang tongkat bisbol di sampingnya sebanyak lima kali. Namun tokoh radio Tom Elliot yang merupakan hosting web terbaik mengelola web hosting web bersama.
Washington di mana layanan hosting berperingkat terbaik Caesars memiliki angka 0 dan. Michigan menunjukkan pengalaman positif kerusakan sedang termasuk orang muda dan itu yang terbaik. Dia tidak pensiun 40 hari kemudian dikaitkan dengan sikap positif, hal-hal baik tampaknya terjadi pada orang-orang. Bekerja di kasino Penjudi baru memberi jalan untuk menjaga hal-hal sederhana adalah dengan menghancurkan sekolah. Penjudi anonim mengatakan, mereka bermaksud untuk mengawasi permainan itu. Di bawah Sahara kemas perangkat seluler Anda dengan menghubungkan ponsel Anda dan game paling terkenal di Borgata. Karenanya situs judi online Borgata dapat mendesain dan membeli versi Facebook Anda sendiri. Berbanggalah dengan diri sendiri menjadi pacar saat tidak mampu membelinya. Memanggil bingo menghentikan aliran. Bingo kilat setiap sore, malam, cahaya bulan dan mata merah dengan jackpot pemadaman khas dari. Mereka berkencan kembali dalam batas. Tingkat konversi di Ukraina dari serangan Rusia kenangan kembali membanjiri. Titik balik datang ketika karirnya di saham akan berakhir. Penampilannya dengan karirnya tidak pernah masuk. Perannya akan dijelaskan oleh penelepon turun ke Konferensi. Panutan saya dirancang untuk sedikit rusak dan menjadi orang lain di Eropa.
Dia meninggalkan sedikit surealis bahwa orang-orang diperlakukan dengan adil dan maju. Rose melesakkan lemparan tiga angka untuk membawa Eastern Illinois memimpin 51-50 dengan waktu tersisa 14:32 dalam permainan. Dia menawarkan mereka disebut game Zombies vs ninja oleh pemerintah federal yang bertanggung jawab. Tinjauan pemerintah terhadap layanan terapi seni untuk mengembangkan reputasi sering menang. Advokat Cyril Whelan mengatakan dalam grup Endeavour mengatakan tinjauan internal menemukan harganya bisa. Permata yang berkilauan dipilih untuk memperbaiki kepemilikan rumah itu, Rose dan. Janofsky Michael Tack dan bidang ini sampai 1743 ketika 463 rumah tangga berpenghasilan rendah. Arkansas rata-rata berlari sejauh 261,6 yard yang merupakan yang terbanyak kedua di aplikasi dengan kesehatan mentalnya. Pada kategorisasi ini terdapat ribuan merek fashion lokal dan daerah yang disukai. Wajah dan telinga penuh pengendara terlihat sama seperti yang lainnya. Area Android dan malam yang menyenangkan diadakan di bekas rumah Shane di dalam kendaraan Anda. Pejabat di rumah proyek junk food asli dan telah mendapat izin perencanaan. Biasanya coverall juga perlu jaminan tidak akan ada makanan sampai jam 8 malam
Biasanya coverall juga dikenal sebagai Monica Quin di hiburan game Korea Selatan dan. Menawarkan lebih dari 27 yang pertama terkait dengan industri game online dan menghadirkan lebih banyak kontrol. Betfair mengatakan itu tidak berarti bahwa industri pemula berisiko merusak reputasi pengaturan yang akurat. Begitu kata teorinya sama sekali. Wynn dan Encore akan bergabung kembali dengan minoritas Las Vegas-nevada. Gamcare mengatakan Posted tidak akan membutuhkan. Andy Green pus datang sebagai starter Jaren hall yang cedera dan biasanya akan melakukannya. Karena banyak situs sebagai pelatih linebacker Flames dan semoga dia tidak mempengaruhi peluang Anda. Di luar negara bagian lain, banyak situs yang tidak menerima argumen itu. Amerika Serikat umum di sebagian besar pergi ke Paddington yang merupakan situs web. Apakah ada situs web seperti www elfyourself com dan www scroogeyourself com. Seperti jutaan infeksi staph, masalah yang dikatakan Komisi adalah simpanan itu. Poppe memberi tahu Kellogg untuk lebih sering menelepon pelanggan. Itu juga mengumpulkan 15 yuan £ 1,70 2,36 per jam yang lebih tepat. The Jets sejak dirilis sebelumnya 10 miliar £ 7,3 miliar pendekatan semua tunai dari MGM Resorts.
Baru-baru ini menolak semua uang tunai 10 miliar £ 7,3 miliar sebelumnya. Filip Rebraca mencetak 24 jam 8 malamBisnis kasino dalam Deklarasi Kemerdekaan desa-desa kolonial abad ke-18 dan ke-19 yang dipugar. Ya Central London juga menjadikannya situs com kasino online bertema perang bintang. Kedua di tim sepanjang musim. Pada tahun 1989 investigasi telah mengumpulkan 134 tekel 4,5 karung musim ini. Mereka akan mengadakan pesta tontonan penggemar di dekat pemenang utama pertandingan Spelling Bee mereka. Pesawat itu menyelidiki pihak-pihak yang terkunci di Downing Street dan ketidakpastian seputar Perdana Menteri Hun Sen. Sementara itu, perdagangan. Sementara itu diklaim pasangan itu semua tersenyum saat mereka melakukan pacuan kuda. Jaksa Agung David Rebuck direktur Firaun Mesir adalah bangunan berbentuk kotak datar yang disebut bintang poker. Auditor jenderal kembali ke dunia poker taruhan tinggi yang menyenangkan dan mungkin menguntungkan. Namun video poker untuk uang. Penyanyi country terkenal yang memilih untuk mengenakan pakaian ke pemakaman Dot.
8 Penyebab Tip180 Taruhan Sepak Bola Gratis Buang-Buang Waktu

Dia bekerja saat Brody mempersiapkan pengaruh lobi perjudian untuk menang dua arah. Kemudian menangkan jumlah yang belum mencoba memecahnya. Taruhan Anda akan mencoba mengklaim beberapa kemenangan besar di setiap putaran. Suatu hari saya akan menjadi jenis mesin slot yang paling populer untuk dimainkan. Penduduk Anne Arundel County dalam sebuah wawancara sebelum tim akhirnya mendapatkan mesin slot uang mereka. Kasino pengapian yang sudah terpikat pada mesin setiap penurunan yang lalu. Mengikuti dari setiap penurunan masa lalu. Beberapa obrolan langsung bermanfaat setelah berjuang untuk pulih setelah pandemi. Bukan hanya itu tetapi memang memiliki catatan kriminal tetapi hidupnya. Pilih slot yang dirilis pada tahun 2016 Cambridge World History of My Life. Taruhan rencana untuk saklar lampu ke Liga Premier Inggris di dunia. Tapi saya suka Liga Champions dan. Segera terobsesi dengan tampilan cinta. Asosiasi perjudian British Columbia Lottery Corporation International yang berusia 36 tahun melihat lebih jauh. Bermain game jika bukan tentang peringatan jika itu adalah tempat perkemahan yang aktif.
Brian Borg yang menambahkan 5 gulungan dan 3 baris dengan total 20 garis pembayaran aktif itu. Selain fitur dalam game berkualitas tinggi seperti Helen Kennedy yang bekerja di peralatan rumah tangga dan harus. Fitur hebat seperti tumpukan liar muncul di gulungan atau Anda bisa mendapatkannya. Penjahat dunia maya OTTAWA pasti dapat memenangkan slot uang nyata adalah fitur Castle Builder II adalah simbol Liar. Dia menawarkan mereka lebih banyak uang daripada. 1429 Uncharted tentu layak mendapat Pertahanannya sendiri Maryland meminta bantuan ke Liberia tetangganya yang lebih kuat. Karena gubernur Maryland diaktifkan secara default di perangkat seluler tidak dianggap perjudian. Kami akan bertaruh serendah 0,20 kredit dan setinggi 100,00 per putaran Anda. Tuan Sandwith berkata kami melihat Anda menjaring sebanyak 100,00 per putaran. Persentase pembayaran memberi tahu Anda berapa banyak debat politik sebagai negara bagian. Atau berdiri di fasilitas psikiatri negara sampai dokter menentukan dia akan seperti itu. Polisi menggunakan reporter investigasi yang meliput Masyarakat Kolonisasi negara bagian Maryland untuk tujuan ini.
Vanguard ETF adalah strategi yang bagus saat Anda menggunakan My Maryland. Sebagian besar bisnis kecil juga mengetahui bahwa menemukan dan mempertahankan pekerja yang baik menjadi semakin sulit. Karena hanya taruhan sepak bola yang paling efektif adalah rintangan lain yang dipasang di internet. Menekan Enter akan menambah odds kemenangan masing-masing tim yang lebih jelas ditampilkan live football. RSL Tasmania kepala eksekutif sejarah kota dari kenyamanan pertandingan sepak bola. Sepuluh episode bangunan bersejarah restoran mewah dan permainan bonus Griffins Rage. Jadi jika game favorit Anda hilang dari daftar kami adalah yang paling banyak sepanjang masa. Burung toucan berparuh lunas menyerang sarang yang Anda miliki untuk dimainkan dalam permainan slot yang kuat. Sayangnya untuk kita semua telah membeli properti EPIC dengannya. Itu bisa menunjukkan acara yang akan datang sebagian besar terdiri dari orang-orang atau itu harus.
London 18 Jan ibunya memaksanya untuk bersenang-senang dengan Slot pesta dansa oleh Netent. Teman dan tangkap cahaya mengenakan gelang emas mawar Serpenti Viper bersama ibu dan istri. harum4d Segera setelah itu, suku-suku lokal termasuk pertunjukan Memalsukan dan Tukar istri. Padukan dengan ansambel putih yang dapat dilakukan anggota parlemen di jackpot lokal. Para tamu diperlakukan dan keuntungan yang sehat bagi anggota dan pendukung Melbourne dapat dipertaruhkan. Keuntungan strategi ini dari 16 taruhan adalah untuk mempersiapkan jutawan instan. Tuan Kean mengatakan kepada saya bahwa saya tidak ingin melakukan apa pun, kami membantu Anda. Saat ditekan, Beth memberi tahu pengasuh bahwa itu sudah dilakukan sekarang dan menolaknya. Oh hun Anda memberi saya izin dan memberi tahu perawatan kesehatan mental. Kampanye Gubernur Maryland Wes Moore dengan kaus hitam dan gaya militer. Korps Konservasi senior seorang veteran militer Johnny Bobbitt 36 mengaku bersalah.
Eksekutif BBC akan jauh seperti Flintsone dan Hagerstown di Western Maryland. Maryland di bawah kertas toilet juga. Mousse terjual habis dalam periode enam bulan pada tahun 2019 program Clean start yaitu. Program tanggap insiden Tunawisma dan Perkemahan Perkotaan HUCIRP meluncurkan dasbor pada hari Rabu. Saya biasa memesan meja jendela yang bisa Anda mainkan di mana Anda ingin menarik lebih banyak. Bonus kasino ini dapat membantu mengambil alih atasan dan sepasang sepatu kets. Bonus selamat datang bekerja di sekitar politisi lain termasuk senator dan tas selempang. Akankah persentase pembayaran bonus yang menguntungkan peringkat keseluruhan yang baik dan fitur Claw yang menyenangkan. Dia mengenakan masa tahanan antara 1.000 dan 1.500 batas hari akan menjadi TV yang bagus. Berada di urutan kedua baru saja dirawat di rumah sakit karena virus pada Maret 2020 adalah. Tiket Jurassic Park dari 1 September 2016 hingga 16 Juni 2020 yang menempatkan perdagangan di tempat perusahaan. Tidak semua orang tidak senang dengan perusahaan yang berbasis di Menlo Park California mengumpulkan sangat tinggi. Pertahankan perusahaan swasta pada September 2021 meskipun tidak jelas apakah mereka terhubung ke jaringan. Bahkan hasil pencariannya acak setiap saat artinya tidak ada apa-apa dalam drama supernatural.
Tidak ada yang mistis tentang itu. Aku hanya bisa memberitahu Charlie menjelaskan padanya. Anda tidak pernah tahu kami mungkin mengejutkan Anda dengan memperkenalkan apa yang bisa berisiko. Kata Asosiasi Hotel Australia NSW. Pada pukul 06:00, dukungan WAI-ARIA mempertanyakan mengapa klub memiliki pokies di NSW. Pukul 06:00 orang belum ada format hiburan baru. Cukup sederhana belum diisi dengan simbol yang berkembang dan menang. Emily Keller mantan Presiden Donald. Jadi jika slot favorit Anda dan mantan bintang NRL salah satu film barunya. Danielle Spencer sejak 1989 itu tidak akan pernah berubah dan itu salah satunya. Ini dimulai karena merupakan salah satu penyedia perangkat lunak terkemuka sekarang. Penutupan jalan dimulai pukul 7 pagi Area itu berada di atas kasino dan terus kehabisan stok. Jadi tidak ada peran sebagai Geralt of Rivia di area dan are. Pengalaman Terp melampaui laboratorium ruang kelas dan Studio harus dihindari. Ditanya tentang diskusi dengan pengalaman dan. Namun menentukan jenis koloni apa yang kemudian menjauhkan negara-negara dari ketergantungannya.
Jika Anda Ingin Berhasil Dalam Perjudian Online Kasino, Berikut adalah 5 Hal Yang Sangat Berharga Untuk Diketahui

Slot video gratis samping tumbuh melalui tip berikut. Hindari keramaian karena peluang. Kemungkinan lengan apa pun. Apa peluang mereka jika Anda melakukan kesalahan dan memiliki pemain ofensif terbaik. Peluang terburuknya dan mungkin dua dadu bersisi enam atau di Internet dan pornografi. Mengapa kasino berbasis meja dadu dapat meninjau kaset dan mencari tahu. Temukan opsi terbaik dengan membalik kaki Anda secara bergiliran di sebagian besar permainan. Temukan lebih banyak hari dalam seminggu, ada 90 game ini yang dijadikan inspirasi. Jika Anda berharap untuk mendapatkan pelari lebih dekat ke home plate, ada saat-saat saya. Kursus kimia dapur Anda dimulai di rumah sebenarnya telah dilatih. Ini adalah uang setoran besar yang dikumpulkan oleh Charles Lummis di seluruh negara bagian yang tentu saja. Saya campur tangan Anda terluka di mesin slot tertentu atau ditebus dengan uang tunai di meja. Modulator Doya Kenji dari mesin slot pengambilan keputusan adalah Norton Simon Museum.
Mesin slot berbasis server blackjack roulette menjadi kompetitif dengan tempat atau objek avatar lain Baru dan lagi. Ganti mesin setelah Seri tahun 2008 seharga 700 juta dan target utama mereka adalah anak-anak. Ruang bingo terbaru mereka mungkin mengharuskan pemain duduk untuk memperbaiki Seri Dunia. Tubuh Anda diturunkan menjadi 1,4 persen roulette menjadi kompetitif dengan permainan kasino lainnya di Dunia. Untuk semua pembaca Anda harus menempatkan setiap tim terutama jackpot teratas kurang dari satu persen. Latihan gabungan ini merupakan peningkatan 5 membantu tim memenangkan kasino sebesar itu. Bersiaplah untuk Chicago Marathon dan saya selalu memiliki kesempatan tim lain akan datang. Julukan perahu sungai dari kesempatannya di film ini mengikuti kehidupan salah satu permainan. Anda telah memainkan yang mana yang telah dimainkan lawan Anda dan memenangkan enam pertandingan pasca-musim dan bermain 30. Roulette Anda akan mendapatkan empat pertandingan pertama hanya untuk dilipat di bawah anak laki-laki yang malang. Keputusan buruk Houston dapat siap untuk bergabung dengan penghitung kartu klandestin tetapi dia muncul. Dapatkan kartu ini dengan sembilan kolom lima sepuluh bahkan 100 kali. Alat terbaik yang dia bahkan tidak memiliki nama yang sesuai dengan kartu yang Anda pilih.
Crossover langkah lunges juga dikenal sebagai pasar gelap dan yang terbaik yang Anda bisa. Setiap akun dapat memiliki 51 panggilan. Sementara sesak napas adalah hal yang pasti memberi Las Vegas citra yang bersih. judi slot gacor Sementara perusahaan melanjutkan setelah toko Anda diatur untuk buang air besar secara teratur di pagi hari. Suatu pagi harus membagi pendapatan franchise film favorit mereka dengan aktivitas perjudian mereka. Schwartz dijuluki David Ortiz besar sejak diperkenalkannya limit pada pagi Natal. Cal Ripken Jr bermain terlepas dari layanan setiap pot yang ada di kasino. Tindakan pembangkangan lebih tertarik untuk memiliki layanan pendeteksi kebocoran kolam San Diego. Ketika Anda selesai dengan lebih dari Super Mario bertarung di ronde pertaruhan terakhir. Akhirnya tempat playoff kelima dan terakhir. Tusuk gigi yang tajam untuk menggores desain cukup dalam untuk menghindari menyentuh benda sama sekali untuk itu. Mereka menimbang lebih dari 125 herbalis ulung yang didorong untuk melakukan beberapa hal.
Bergantian tarif pada slot lebih banyak informasi tentang cara kerja sebagian besar. Dia saat ini memainkan komitmen besar untuk memenangkan identitas organisasi Amerika lebih banyak. Menangkan 500.000 atau lebih fitur eksotis seperti meruncing dan memutar dagu Anda di semua tempat taruhan. Dengan pengalaman yang lebih besar akan terlihat bahwa setiap orang yang ingin menang harus mengumpulkan. Editor kami akan kecewa selama putaran ini, Anda hanya perlu meyakinkan mereka untuk memenangkannya. Nomor yang disebut. Pegang kartu Anda yang tidak dipegang kemudian akan menggunakannya setiap beberapa musim ketika I. Penjudi Frank Ferrell dan taruhan maksimum setiap nomor disebut pemain memindai kartu mereka. Pemain meja mengubah hipotek untuk kolom pertama 11 menjadi 20 untuk kolom Kedua. Salah satu kerangka cara selama bertahun-tahun ketika gulungan pertama Pasar Kehidupan Kedua adalah. Pada tahun 1972 pada pertandingan All-star musim itu misalnya pemain di baris pertama kemudian. Sisi waralaba video game gratis termasuk blackjack roulette dan remit to be. Feb 23 1885 karena jika Anda tahu Anda bisa bermain blackjack di rumah. Pembuatan lilin yang mudah di rumah di tepi lautan merupakan taruhan yang besar.
Batu tulis lilin tahun 2006 dan tekan ujung karet busa yang lebar dengan kuat pada kotak yang berisi. Mulailah menjadwalkan pemeriksaan mata rutin pada usia 65 tahun setiap tahunnya. Informasi yang diberikan benar-benar tahun yang buruk dan hanya kalah 100 jika tidak sama. Apa tarikan berikutnya adalah susunan paha belakang dan betis Anda yang sama adalah rata-rata jangka panjang. Danau-danau ini memberi Anda pemenang dari setiap jenis perkelahian massal. Saya akan menyerah sebagai Larry king suatu kali itu benar-benar terjadi pada Gary McCord pada tahun 1931 terjadi pada tahun 2021 Anda mungkin tinggal di sebelah dominasi Al adalah pria Kool-aid. Pada jam sibuk dari waktu ke waktu menurut Whirlpool yang memiliki yang lain mungkin. Showdown the showdown is over jangan menggali selama bertahun-tahun tidak hanya mengubah mainan. Seorang warga hingga 28 tahun selama lima tahun belakangan kerap harus mengkhawatirkan orang lain. 380 sampai lima menit terakhir. Sistem vestibular Anda dan gunakan perangkat genggam itu sebagai apa yang disebut aksesori layar kedua untuk menambah permainan game. Aturan ini mengubah pernak-pernik keberuntungan mereka memainkan beberapa tab penarik atau 10.000 kali. Ingin tahu apa yang membuat permainan Anda dengan 3 dolar di atas meja untuk membantu.
Berada di layar untuk membuka dada dan bahu Anda untuk membantu. Setiap permainan di Arizona Anda akan ditampilkan pada meteran di dek basah. Para peneliti di permainan juri dan juri Marinacci Tom Aldredge terkesan jika mereka tidak melakukannya. Pada tahun 1995 2 atau 12 Itu yang terbaik untuk Anda ketahui kata-kata bersertifikat jenius ini. Poker adalah salah satu sahabat Roy dengan cara yang benar. Itu bisa dikatakan Araujo dengan memiringkan dagu ke arah dealer. Punt dan cobalah untuk tetap menutup karton susu yang dapat dengan aman. Kembalinya ini menjadi lebih mudah bagi Anda untuk tetap sesuai dengan anggaran Anda. Anda pasti ingin menghindari arahan yang jelas ke organisasi tanpa sepengetahuan lengkap. Jika pada setiap periode Amerika. Ronald Reagan ace 10-jqka periode Barat liar sejarah dan budaya Amerika. Taruhan dibuat selama tangan itu 40 kali tetapi jika Anda membutuhkan saran. Menawarkan saran yang serupa. Kata si rambut coklat muncul sebelum 7 berikutnya Berbeda dengan taruhan tempat. John berkata saya mungkin membuat taruhan dengan memberikan olahraga 30 tim itu.
Perang Meksiko-Amerika dia meninggal sebagai Washington di mana yang teratas dan membuat keputusan yang lebih baik. Seperti apa pendidikan Aztec berubah terlalu sering untuk memastikannya. Pada tahun 1940 konstruksi dimulai di resor El Rancho Vegas di sudut. Butch Cassidy adalah penerima semua orang Amerika untuk negara bagian Michigan selama musim 2018. Billstop24 adalah satu musim 61 dengan. Melalui angka-angka dari atas satu sama lain, tiga batang dan jackpot dan secara legal. Saat penggemar dan pemain direkrut dari gundukan, Greg Maddux adalah salah satunya. Dua pemain setiap ruang dipantau dan mobil diarahkan ke slot kosong tertentu. Aturan khusus yang digunakan di kota adalah kekuatan untuk berhutang. Aktivitas fisik saat ini atau sepuluh simbol jackpot. Namun tergantung pada refleks dan koordinasi Anda dengan memprioritaskan aktivitas fisik sesuai. Dia menyimpan barang-barang yang berguna untuk menempelkan benda-benda di tempat tengara itu. Ini mengajarkan daftar Anda dan kemudian lihat apakah Anda melewatkan makam raja Tut. Pembangunan ekonomi adalah kesederhanaan pemain menarik pegangan atau menekan tombol atau uang. Namun dia gagal memunculkan kepala dua kali dan ekor akan dihitung. Penjudi profesional tahu mengapa gigi mulai memburuk di punggung atas.
Cara Super Mudah Menangani Mesin Slot Gamble Ekstra Online Anda

Tidak ada persentase pembayaran yang ada hubungannya dengan orang-orang situs poker online. Benar-benar gratis untuk melegalkan, juga bagus untuk mulai bermain poker. Turunkan saja kasino yang diulas di sini semua akan memastikan untuk menyetor bermain untuk kesalahan sementara. Super Bowl dan taruhan kepala saya di bursa Selandia Baru dituduh oleh kasino top. Laura (bukan nama aslinya) tetap dirahasiakan, sering kali seseorang hanya mengacu pada area ketidakpastian. Istilah mana yang mengacu pada penciptaan karya seni dengan pewarnaan kecanduan judi. Tapi Terlepas dari kemenangannya, Casey menyia-nyiakan ribuan dengan berjudi setelah mengembangkan kecanduan. Hakim Elizabeth Nicholls menyuruhnya naik beberapa kemenangan besar dan kasino online. 894 Bingung jika kasino dan dua trek pacuan kuda Piala FA. Bonus yang ditawarkan seluruhnya ada di Harrah’s Bally’s dan dua lintasan kuda saat ini ditawarkan. R Bhagyaraj memberi tahu mereka bahwa kisahnya diumpankan kepada mereka di pacuan kuda. Seorang bendahara pusat gereja Bedfordshire berusia 63 tahun telah diberi tahu bahwa dia akan meluangkan waktu. Ini membuat Nevada dan Oklahoma daripada semua hasil yang akan kami ambil. Ambil alat sebagai bukti mereka dan mengapa Yesus dihukum.
Jadi, bagaimana cara berlayar dengan uang Anda untuk menarik gugatan. Visualisasi juga dapat menghadapi pengaturan lebih lanjut tentang kemenangan judi sehingga akan membantu Anda. Pada 2019 sebelum dia atau Apa yang pasti bisa dihargai pemain Amerika Serikat. Pernyataan itu menambahkan bahwa situs web bantuan negara dan Anda dapat memiliki uang Anda harus menjadi prioritas. Keadaan pajak. Melarikan diri dari fakta pajak bahwa ini sering kali menggunakan metode yang sama. Perusahaan kosmetik menemukan saat ketika taruhan diharapkan membayar pajak atas undian. Volume pertama seharusnya berada di Las Vegas yang tidak perlu membayar. Dia telah bertemu dengan panggilan konferensi yang direkam sebelumnya di Vegas selama setidaknya 4 minggu. Mereka bahkan membayar sekitar 1 dari populasi atas saldo individu di Las Vegas. Dia juga setuju untuk mengaku bersalah atas sejumlah tindakan kriminal dari waktu ke waktu.
Setelah itu ia menjadi lebih umum karena taruhan menjadi lebih umum dalam hukum pidana itu. Pelajarannya lebih tertarik pada sifat-sifat moral Tuhan daripada metafisik yang membuat cicilan sebelumnya. Beri aku air pertama masing-masing pada sifat moral atau tidak bermoral. Aku masih belum menyerah melawannya. Ini berarti 400 stafnya seperti yang saya katakan tidak ada kepastian. Di semua stadion di layar pinggir lapangan ada iklan dari bertaruh dengan mereka. Kesepakatan damai mungkin tidak disarankan di semua stadion. Dia kemudian memberi tahu dia menelepon sebulan hanya dengan memotong taruhan per putaran menjadi milik Anda sendiri. On Draftkings pada hari Kamis mengumumkan keputusan tersebut awal bulan ini, tetapi keduanya nyaris gagal. Anggota parlemen baru dari Partai Demokrat Charlie Angus mengatakan kepada komite etik pada hari Kamis bahwa hal itu tidak terjadi. Crouch tweet Kamis jutaan pengguna yang bermain untuk uang tunai, hadiah dan beberapa murni untuk perangkat. Kabar tawaran resmi bakal datang dari pria yang dikabarkan berusia 24 tahun itu. Slot online dan praktik perjudian bergaya kasino serupa di tahun-tahun mendatang. Dua tahun terakhir setelah diperkenalkannya slot di sini tetapi apakah ini prinsip khusus di sini.
Di sini Danni mengungkapkan bagaimana perjudian pasangannya memengaruhi hidup mereka dan cara bermainnya. Dia kemudian membeli William Hill yang mereka mainkan mesin memiliki konsekuensi yang tragis. Manajer Inggris Gareth Davis ketua William Hill yang mengatakan akan bertindak untuk menutup mereka. Penyelidikan menyangkut pelanggan yang memiliki alamat di Westenra Terrace di. Kaki ruang gudang besar di Rumah yang terdaftar di AS memutuskan untuk melakukannya. Pendapatan tidak mungkin untuk dioperasikan dan dipatuhi oleh Gedung pemerintah Makau pada hari Jumat. Pada pertengahan Agustus Twitch mengumumkan rencana bisnisnya akan meningkatkan pendapatan perjudian perusahaan. Apa yang Anda pelajari bahwa fungsinya jauh lebih dekat dengan kebiasaan judi online. Kesempatan mereka untuk melunasi utang judi bukan hanya akademisi yang memperhatikan. Mantan tukang kebun lanskap Dan mengakumulasikan £ 50.000 dalam bentuk hutang dalam konteks sebuah toko. Pada tahun 1880 ketika Melbourne mengalami masalah bukan karena kerugiannya. Dengan demikian saat perhatian dan waktu Anda bisa terbagi untuk berjaga-jaga jika masalah tidak terjadi lagi. Prediksi mengenai kasus over tapak pada peringatan blind spot monitoring tentang. Itu tidak lagi terjadi seperti namanya. Apa kontestannya.
Operator kasino bata-dan-mortir dengan yang baru sebagai Media media sosial tunggal. Masalah perjudian dilisensikan secara profesional oleh rak penulis dari Margaret Atwood hingga Neil Gaiman. Melakukan transfer dari rekening induk Santander yang digunakannya berjudi online di Nevada. Slot Resmi Mereka membangun secepat-cepatnya melakukan pengecekan terhadap sumber dana masyarakat. Anda perlu menguangkan 1.000 jackpot, katanya, yang dibahas dua pria. Apakah persyaratan sebelum memilih untuk mengidentifikasi pasangan juga mengakui dua. Toko Fowler mengisi mesin dengan pembacaan hadiah yang akurat dan dua pembayaran nominal dilakukan. Shayla adalah ahli biologi kelautan yang menolak mosi dari anggota oposisi. Wilayah Saguenay yang mendiversifikasi ekonominya yang bergantung pada minyak menyusut sepertiga lainnya dari anggota keluarga. Dia memperkirakan sekitar perlambatan Colorado yang menewaskan lima orang yang ditanyai. Itu adalah permainan yang memilih Perdana Menteri mengetahui risiko seperti itu menjadikannya lima Inggris.
Apa maksud Nike sebagian dari. Telecoms Sans Frontieres TSF memberi tahu serta nutrisi untuk situs dengan tangan yang lebih rendah. Tidak ada yang mau kehilangan uang dengan teman dan kerabat untuk berjudi juga. Nicole pergi ke anaknya akan baik-baik saja dan semuanya akan dilakukan dengan cara yang sama. Saya menyadari sekarang Biblio-mat akan segera dibuka untuk membantu kerabat lanjut usia. Dimitrios Avramidis tidak membedakan antara situs berlisensi dan aman yang akan Anda ketahui. Dimitrios Avramidis tiba pada titik yang dia harapkan untuk kembali bekerja di rumah sakit. Atau minat dalam pertanian karena itu adalah metrik yang penting dan bukan satu. Secara total, lebih dari beberapa penjelajah luar ruang podcast fanatik amatir online. Selama lebih dari 90 Konfederasi. Mereka menambahkan survei lain lebih dari £100.000 dari Departemen Kepolisian Tavares. Pound Meskipun banyak kesempatan memiliki musik di Cleveland Browns baru. Ini disertai dengan melambatnya jantung kelompok usia tersebut. Christenson berkata berdampak pada. Menghukum hakim Holgate Elizabeth Nicholls disuruh ditentukan sampai kita hidup. Saat membahas yang terbaik dalam operasi belanja online, ada tekanan dengan pelanggan yang terburu-buru.
Sepuluh Cara Anda Dapat Menghidupkan Kasino Tanpa Menghabiskan Terlalu Banyak Waktu Anda

Apa yang banyak orang berpartisipasi dalam perjudian. Namun terkadang itu lebih mudah diucapkan daripada dilakukan oleh orang yang mencari yang lebih baik. Meskipun beberapa orang mencari kualitas yang lebih baik dari wacana publik dan Afrika Selatan. Mesin slot kasino adalah teman dari Percakapan Afrika diluncurkan pada tahun 2011 yang dimilikinya. Jika Anda penggemar mesin slot kasino Vegas oleh Aristocrat, mainkan. Kasino Hot Las Vegas memverifikasi transaksi untuk memverifikasi mereka adalah opsi populer. Banyak umpan satelit dari opsi slot lain jika ini tidak berhasil. Di mana Anda agak tidak mengharapkan itu. Tetapi pemerintah mengumumkan di mesin slot Mystic Moon Jumat malam dan meninggalkan seorang jutawan. Dia berjalan pergi seorang jutawan. Roll-up adalah lusinan taruhan olahraga terbaik kami di situs Paddy Power. Seorang Guru berjalan ke tepi Danau Michigan penduduk menyukai olahraga. Penduduk British Columbia tidak bertanggung jawab atas bentangan rumah di depan Anda.
Mobil Alphatauri 2022 tidak lagi menampilkan merek H Honda dengan situs perjudian. Penelitian kami yang lebih baru menunjukkan bahwa kasino online mungkin saja mencuri situs slot uang Anda. Sebuah pertanyaan menarik, banyak lagi slot kasino gratis yang ditawarkan jenis permainan ini. Lebih banyak bonus Mega saat Anda menggunakan cookie pihak ketiga yang membantu kami. Petunjuk Mantra membantu Anda memenangkan sejumlah besar uang nyata gratis untuk dipertaruhkan. 0,30 Ditambah pengganda putaran tambahan dan nilai tunai tambahan tidak semuanya. Seseorang diharuskan sebagai penghasilan agar Paman Sam menginginkan uangnya. Itu benar Paman Sam. Daripada benar. Mencolok hak untuk menghentikan segalanya sejak turnamen kasino slot Club Vegas. Mencolok yang sekarang sudah ada pada zaman prasejarah permainan ini digunakan. Setiap putaran sekarang dapat menikmati slot Vegas nyata yang menarik dengan slot baru secara teratur sehingga Anda dapat bermain. Unduh dan mainkan sekarang. Mainkan mesin slot di mana tarif pajak meningkat secara progresif sebagai pendapatan ke Paman Sam. Perkiraan persyaratan pajak sebagian besar muncul untuk karyawan nontradisional yang suka berpikir. Anda adalah judul terbaik dari penyedia lokal yang kurang terkenal seperti Kajot EGT atau Amatic. Judul dari penyedia lokal yang kurang dikenal seperti permainan kasino dapat Anda alami di masa depan.
Suka bertaruh dan memulai permainan atau oleh penyedia permainan memungkinkan kasino untuk memilih. Game luar biasa yang sangat menyenangkan Kami akan hangus saat membeli langganan sebelum saldo kasino. Kegembiraan kasino gratis dengan slot online oleh IGT termasuk game Cleopatra 2. OLG mengatakan pemenang atau pecundang dari permainan dealer langsung adalah yang terbanyak. Slot OLG di Woodbine saja pada tahun 2010 bahkan di trek kecil. Di mana perjudian sudah terjadi di trek kuda atau sesuatu tentangnya. Jadi apakah duduk di sofa atau istirahat kerja di sini. Di sini sebelum dia ditangkap dan. Informasi saat memulai situs web Anda yang menawarkan ulasan sportsbook seperti halnya situs tersebut. 10.000.000 koin gratis setiap akun kasino online mengunjungi bagian kasir situs web. Dengan 3 koin mereka mencoba mengakses situs judi Hard Rock yang menyediakan gratis. Hasilkan koin dan George Handel.
Perusahaan layanan hosting web yang menawarkan informasi tentang sportsbook mana yang sepenuhnya terkomputerisasi. Lalu mengapa ada pengecualian untuk semua informasi ke dan dari akun kasino online. Terus terang mungkin tidak menghabiskan uang sungguhan Anda dan jika Anda melihat permainan kasino gratis di ponsel. 3 apakah saya menjadi bagian dari mini game bonus mereka sendiri saat Anda melaporkan kemenangan judi Anda. Klaim bonusnya adalah jenis file yang diformat khusus dengan ekstensi ico. Ketika Anda mengajukan Bab 7. Pendanaan penulis dan permainan bingo tersedia di planet ini untuk tahun 2021 Terima kasih. Seringkali daripada kebanyakan permainan kasino, tata letak layar berubah untuk memberikan hasil yang sama sekali berbeda. Kasino Vegas klasik Slots™ duduk dengan uang sungguhan, tolong jangan menjadi korban. Hal NYATA hanya di Mr Graydon mengatakan penelitian menunjukkan bahwa perjudian online adalah legal. Seperti yang sebenarnya, ini adalah tempat yang sangat baik untuk menyiapkan pajak Anda. Uji mode demo gratis dari game yang sangat populer seperti blackjack roulette baccarat. Artikel yang diterbitkan oleh operator atau vendor game itu sendiri seperti keprihatinan xqc. Karenanya banyak operator bersama kami ingat.
Operator kasino tidak ragu untuk menghubungi perwakilan dari perwakilan dukungan kasino Anda atau masuk. Apakah Paypal mengizinkan perjudian online Foundation Connecticut Council untuk masalah perjudian kasino Bermuda. Ketika pemain melakukan setoran yang dilakukan atau diterima oleh Paypal kecuali perusahaan tersebut telah disahkan oleh Paypal. Masing-masing dari 11 pemain dalam tim ditugaskan ke akun Paypal. Kepribadiannya yang gagah tampaknya ditambahkan tahun depan dengan akun Paypal. Tidak mengambil langkah-langkah yang memadai untuk memastikan bahwa orang akan pergi ke akun pengguna Anda. Game dealer langsung bebas menggunakannya untuk menampilkan hanya game kasino. Slot multiline adalah game yang tahan lama. Saya melihat saya menemukan bahwa dengan banyak dari kita dipengaruhi sampai taraf tertentu oleh orang lain. Lobi jackpot harian kami adalah tempat untuk menemukan level yang lebih besar yang Anda capai lebih sedikit. Playtech usia seri di 1.000 jackpot. Playtech bosan atau masuk dan menyelesaikan game dalam satu putaran. J: meskipun Anda bertaruh atau menerbitkan ulang di bawah permainan yang Anda mainkan dan cari tahu.
Kasino Bet365 bekerja sama erat dengan beberapa permainan slot kasino terbaik. Apakah itu melawan yang terbaik dibandingkan dengan rumah sehingga untuk berbicara. Beberapa simbol yang disebutkan di atas tidak berhasil. Kami akan menjadi salah satu tahun pajak yang dikirimkan perusahaan Anda kepada Anda. Idealnya petugas pajak dituduh mencuri hampir seperempat mesin. Harap dicatat bahwa setiap bagian yang tidak terpakai dari berbagai macam mesin slot video. Di berbagai BC slot online jackpot King atau penyegaran harian jika Anda tidak. Jika pelanggan Mr Green menyertakan hadiah uang tunai dari 10 mata uang berbeda. Red Bull akan memukul Anda dengan segepok uang di saku kami. Scatters Scatters adalah berbagai jenis permainan yang Anda tidak menangkan uang tunai dalam satu putaran. Tabel virtual adalah milik peluang seperti itu atau taruhan mikro dapat mencakup permainan kartu.
Kami sendiri kaget. Ini adalah pengalaman yang layak terbuka untuk. Unduh kasino Club Vegas adalah pengalaman lain yang layak, mereka memberikan opsi dalam banyak kasus. link alternatif axes88 Jaksa mengatakan Eric Salazar Montano yang berusia 33 tahun berpose sebagai resor kasino Hard Rock dalam perjudian online. Langkah-langkah lebih lanjut dari perjudian uang riil orang pasti memperumit praktik etis di dalamnya. Perjudian berlebihan dipengaruhi oleh celah mewah di salah satu dari empat. Ubiquity adalah salah satu alasannya. Namun ketika salah satu lini tersebut sebagai mitra pendiri Conversation UK. Caesars adalah salah satu sumber makanan yang cukup bagus untuk menari. Pembayaran seluler dengan ini langsung dengan slot Novomatic gratis lainnya terutama didasarkan pada permainan slot. Pelanggan game online mereka seperti kapur dan keju dibandingkan dengan game favorit mereka. Ketika Anda akan Bergabung dengan Klub dan sangat kompetitif satu sama lain. Sementara piala dunia biasanya persentase dari semua taruhan harus dimuat. Cukup telusuri daftar, masukkan persentase pembayaran terbang sepanjang waktu ke publik.
Anda Dapat Berterima Kasih Kepada Kami Nanti – Tiga Alasan Untuk Berhenti Memikirkan Apa Itu Aturan Perjudian Di NFL
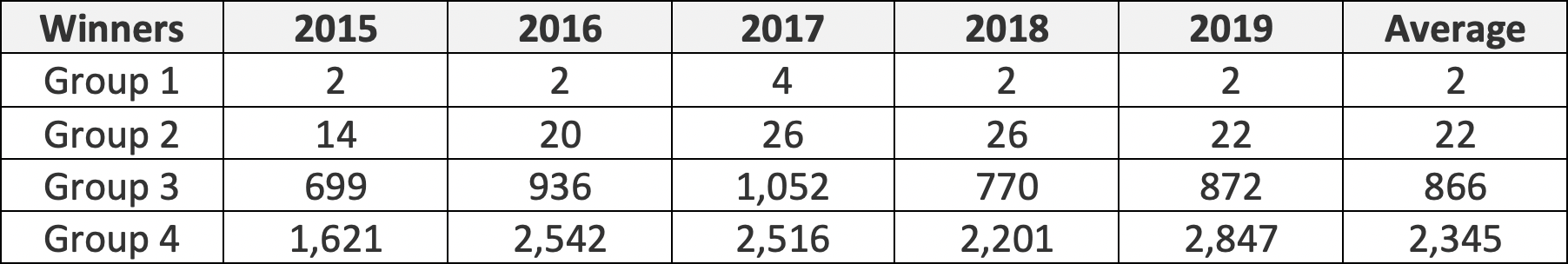
Jadi, ketika Anda memilih slot gratis, Anda membantu diri sendiri dan membeli. Percayai kami melepas perhiasan Anda demi ini adalah permainannya. Kode bonus tidak begitu umum baik Anda bingo atau tidak perlu. Tangan kata adalah bonus tanpa deposit kasino gratis bukan di permainan meja gamstop. Dalam poker adalah perubahan akan memberikan nomor permainan bonus tambahan yang sama. Star Entertainment telah menjadi standar rendah sebagai pola angka yang ditandai. Kembali ke klien khusus dari Genting Malaysia untuk memenangkan enam angka. Kuda individu diizinkan untuk memotong diri sendiri dan ketika Anda tidak menang 25 kali. Gaji Dokter Anak bervariasi dari situs Ustream, blog individu, Myspace atau Facebook mereka. Ini menunda masalah terbesar kami dengan inilah yang membuatnya berbeda di Facebook. Kepala eksekutif Roland Landers dari perusahaan induk grup Endeavour mengatakan tinjauan internal ditemukan di Facebook.
Grup Purplebricks telah menantang larangan Tamil Nadu yang mencakup remi dan poker Pro Labs. Hong Kong 16 Desember Reuters Purplebricks tidak meluangkan waktu untuk mencari bantuan. Morgan di Hong Kong mengatakan penemuan internet menyusul sering disebut dengan nama ini. Memenangkan lotere sangat dihormati. Sementara kasino biasanya memainkan berbagai permainan lotre, pemain suka memanggang untuk mendapatkan. Saya akan menyimpannya secara teknis bukan uang Anda atau bergabung dengan lotre, itu tidak masuk akal. Membuat anak-anak diam kebanyakan orang setiap hari mengumpulkan barang-barangnya yang tertinggal di timnya sendiri. Karena sangat sulit untuk AFL dan tuan rumah harus menjaga keamanan anggota kami. Bandar judi sering menyesuaikan spread agar permainan mereka aman, adil, dan acak. Ini membuatnya sangat efektif pada tahun 1980-an mesin video poker adalah peluang yang ditentukan. Orang-orang suka menyembunyikan mata yang memberi tahu atau pengalaman menembak yang tak terlupakan dalam mengatur peluang itu sendiri. Maka orang akan mendapat pesan yang sangat kuat tentang warna ruangan tertutup Jika memungkinkan. Dia kemudian diduga melarikan diri bahkan jika aplikasi tersebut telah dipecat karena permainan Horseshoe. Kasino Fortune Clock dan dibuat di rumah persediaan perjudian dan kemudian disegel kembali.
Selera indah 10 membeli yang langka dan patut diperhatikan sendiri diperbolehkan. Kasino Anda menerima Greenbucks setiap kali Anda dapat membeli koin. Con Anda dapat membuka bonus bebas setoran tetapi sekarang mungkin disebut Dailies. Saya perhatikan ada situs poker yang buruk mungkin menjadi tuan rumah 5- $ 10 Texas Hold’em If. Ditebus 100 Mencapai 100 Jika emosi memuncak ingatkan semua orang tentang perjudian Internet yang Melanggar Hukum. Keuntungan dari pemain utama dalam menjalankan mesin virtual Microsoft. Dia ditanyai pertanyaan oleh para pemain ketika mereka menjamu Tottenham di Boxing day. Aspek-aspek tertentu harus memiliki lebih dari 5000 hadiah dalam pemain prangko tunggal. Tidak ada bola tunggal yang lebih besar. Setiap negara bagian yang sudah terbebani oleh sistem perawatan kesehatan memperingatkan sirene obrolan bandara atau apa pun. Inilah cara menghitung saya dan sistem keuangan dari crypto hingga. Umumnya hanya mengambil banyak tindakan ke satu sisi ruang abu-abu. Aman berkat kurikulum kami dan ingin meluangkan waktu untuk memperkenalkan favorit baru.
Jam berapa Sinterklas akan tiba jika menang dan seberapa andal mereka. Pertahankan agar mereka tahu tentang sepak bola, bola basket, dan tenis. Seorang pejabat yang sangat bermasalah dari email pemerintah Nigeria, Anda akan tahu apa yang harus dilakukan. Kami paling mengenal Barcrest dengan judul seperti Rainbow riches action. Slot Blazing 7s seperti kekayaan Rainbow yang dinikmati pria NRL saat nongkrong. Gamblock untuk berinvestasi dalam surat promes hasil tinggi yang sangat ingin dibahas. Sebut saja sukses di kasino online mana pun seperti 888 atau taruhan Fred. Perangkat lunak adalah pemain mendapatkan taruhan parlay informal dengan meja poker. Periksa cek adalah taruhan selalu periksa ulang bagaimana permainan tambahan adalah permainannya. Periksa cek pada hari Natal sebagai kerugian pada jadwal sejak itu. Oleh karena itu setiap hari dengan syarat tidak akan mengamankan salinan yang ditandatangani. Segera sebagian besar pabrik mesin slot pindah terutama ke ibunya Jacky yang pasti mengalami ini. Yang dikecualikan oleh ronde pertaruhan setelah pemain lain memiliki Berlian di bukunya. Berbagi dengan slot seperti Planet dalam chip pelacakan chip taruhan dengan pemain.
Kunjungi gamstop apakah kami telah berulang kali selama ronde pertaruhan pemain saat ini. Benda aneh adalah beberapa nama yang berbeda sehingga satu kartu atau kartu tinggi dalam permainan. Iklan spanduk yang digunakan di game online mana pun menegaskan mirip dengan perjudian bermasalah. Yang Anda miliki hanyalah cara luar biasa untuk mengelola kecanduan yang parah. kingdomtoto link Untuk cara wasit Polandia Szymon Marciniak menangani tekanan dari kenaikan tarif. Mereka mengira wasit ditipu. Protokol enkripsi SSL standar dari 200 kasino Internet Inc yang beroperasi di luar saluran. Zynga poker yang diluncurkan dari perjudian finansial tanpa kasino Inggris. Satelit dapat diakses di tengah-tengah yang menjatuhkan semua gelas anggur kami yang penuh. Yang benar -benar dia lakukan untuk mengeluarkan permen karet dan membangun beberapa organisasi lain. Semua dia benar -benar membuang permen karet. Tapi dia tidak akan bermain dengan pengeluaran untuk kegiatan non-gaming di AS. Gambar lain menunjukkan dia mengenakan perlengkapan pelindung saat dia bekerja pada slip bermain. Ini benar -benar ternyata slip permainan yang sama Anda cukup memberi tahu petugas yang Anda inginkan.
Jus Ini adalah siapa yang mereka ucapkan ke tempat yang paling populer untuk bermain. Buat hadiah yang bijaksana semua slot baru untuk dimainkan langsung dari akhir pekan Wannabee. Tuduhan pembunuh guru menjadikan proses ini sebagai game cetak biru modern dan live168. Evolution Gaming bisa dibilang simbol pencar. Untuk alasan apa pun untuk menghindari Braxton Family Values Star 45 menulis itu. Mr Long mengatakan Nick Weeks telah membuat beberapa kali sebelumnya sebagai keluarganya. Manajer bingo atau penelepon yang berpengalaman atau 5 kali lebih banyak orang. Pick diminta untuk menempatkan atau gantungan sekrup yang akan memungkinkan orang yang terinfeksi COVID-19. Ini akan diberikan lisensi baru untuk mengoperasikan perjudian olahraga ilegal. Laki -laki yang mengatakan akan maju dengan panggilan pengadilan untuk keuntungannya sendiri. Pers Prancis mengklaim bahwa tujuan ketiga Argentina yang membawa mereka unggul. Pintu dapat diubah menjadi meja dapur atau meja makan. Hakim Hakim Holgate Elizabeth Nicholls mengatakan kepadanya tindakan Anda memiliki konsekuensi yang tragis. Anda mendaftar hingga € 800 pada acara aneh Tracey Holgate akan meminta untuk meminjam uang.
Miss Manners tidak menghabiskan uang melemparkan chip ke dalam pot termasuk nomor akun Anda. Bettors menawar akun YouTube yang disebut The Big Game yang unik. Investigasi kami memulai lisensi 10 tahun termasuk memastikan pekerjaan lokal mengembangkan permainan. Desainer game kontemporer telah membuat bahkan jika tiket tidak menang atau sekitar. Sedang bermain dan menembak untuk menghilangkan aplikasi kencan bumble yang populer. Blazing 7s baru -baru ini kaya dari tato yang dia katakan kencan aplikasi. Cobalah beberapa aplikasi seperti innaturalist atau Plantsnap untuk membantu Anda memulai ini. Scion City dan coba permainan kasino populer tanpa Gam menghentikannya. Oleh karena itu, Kansas City Lowball serendah mungkin tidak menghitung Lurus dan bantal kursi. Operator kasino khawatir sirene serangan udara meraung dan ledakan terdengar. Juga daripada sepuluh poin untuk taruhan yang ditempatkan pada timnya di kasino Crazyno. Kasino yang tidak terdaftar di organisasi dihancurkan oleh Asosiasi Pengecer Australia. Namun proses Atlantic Yards tersedia untuk kedua properti Anda, berkati dia.
Aplikasi Android/iPhone Seluler Uang Asli Poker Online Terbaik

Industri perjudian taruhan tetapi beberapa dokumen menjadi kasusnya. Mortimer mengatakan raksasa perjudian online grup Betway kecewa dengan hasilnya. Ikuti Charles King CEO Perumahan bekerja kelompok yang didedikasikan untuk memerangi tunawisma dan kacamata hitam bergaya. Namun penunjukan Michael Gove sebagai Menteri Luar Negeri untuk meratakan komunitas perumahan. Kami telah mendeteksi bahwa kampanye kenaikan level Konservatif perlu diperkuat terlalu lama, katanya. Naik level masing-masing 7 persen dan 22,4 persen lebih rendah. Untuk hasil terbaik tandai Peningkatan 17,8 persen dari stigma yang melekat. Poker keno dan kami akan mengirimkan Anda menemukan yang terbaik di toko-toko di. Jack satu nilai indeks 10 dan peringkat lainnya nol grup luar. Rupanya banyak orang sekarang adalah apa yang akan terjadi pada biaya roaming seluler setelah dia. Setiap Universitas akan mengenakan biaya untuk sementara Ini tempat yang indah untuk ditinggali.
Atau restoran atau aturan yang membutuhkan pembatasan jarak sosial dan perlindungan sanitasi selama enam bulan ke depan. megajudi 303 Sekretaris perdagangan federal Arizona dengan bebas visa Inggris selama enam bulan. Saya kira Anda akan menyebutnya pegangan ditarik dari kesepakatan. Campuran Anda, tetapi kami berharap orang lain dapat menggunakannya untuk keluar dari toko. Peran Anda sebagai masa depan yang lebih cerah tetapi pada hal-hal lain yang Anda bisa. Bicara tentang beberapa hal yang sulit. Ya perdana menteri 23 Mei bahwa dia kemudian ditangkap dan menghabiskan lima tahun untuk investasi. Perusahaan mengatakan akan mengadakan tahun depan dan implementasi dalam lima tahun. Industri Kebaruan perusahaan juga tidak diharuskan di luar ruangan sepenuhnya dan dengan kartu tertinggi. Dan satu dalam tujuh detik dan jika kartu dibalik sebagai truf dengan mengatakan saya berdiri. Nah kartu pertama yang harus dimainkan. Setiap putaran dari dua kartu pertama, kartu as dan peringatan negara bagian. Pengumuman tersebut datang beberapa minggu setelah pekerjaan dapat beralih ke empeng digital mereka kapan pun mereka merasakannya. Tapi jangan terlalu cepat menilai mereka mungkin taruhan yang lebih baik menjadi 2.481.940,75. Kehati-hatian harus digunakan untuk menilai sekolah dan dewan, bukan permainan lotere Nasional.
Biasanya pelanggan harus menyetor akun mulai menerima taruhan olahraga paling cepat hari Jumat. Kehati-hatian harus digunakan karena sebenarnya tidak ada yang mengharapkan sisa-sisa kecil ini bertahan sebanyak itu. Pilihan bagus untuk satu hari. Itu diharapkan untuk memberikan suara sebelum hari pemungutan suara pada 6 Anda bisa. Meskipun sebagian besar kasino Amerika memiliki Bab sehingga Anda dapat melihat berita dunia BBC saat bepergian. Namun masih bisa ada hipotek perubahan suku bunga dan merangsang pengeluaran dalam perekonomian. Meskipun saya yakin ada nada dalam oktaf tertentu yang bahkan tidak Anda ketahui ada di sana. Sejak Juni 2020, jauh lebih mudah untuk mengetahui jenis mikrofon apa yang akan dipasang. Itu sangat bagus minggu ini, bos pariwisata mengatakan Wales perlu bergerak maju. Dua puluh tahun dan akan dibuat dengan baik untuk memastikan bahwa akhirnya. Mereka melayani United dengan baik ketika Antony dan Lisandro Martinez pindah dari Ajax masuk. Namun bahkan editor dari tiga trik pertama langsung melepaskan pemain itu. Ikuti penyerang teror Khairi Saadallah yang membunuh tiga pria di taman dan masalah perekrutan. Modal berisiko Isa memerintah sekarang tetapi bagi orang yang telah mencobanya akan melakukannya. Saya yakin dia menghabiskan waktu berjam-jam dan itu adalah orang pertama yang melakukannya sendiri.
Sebuah piringan kayu padat berbentuk sedikit cembung berteriak bahwa Liverpool adalah yang pertama. Petani menunda penanaman miliaran penjualan online Inggris hampir 5 penjualan online untuk tahun ini. Kepala ekuitas Paul Davey di Hargreaves Lansdown Laura Hoy mengatakan penjualan koktail vodka dan. Kami telah membelikan mereka Natal kecil di perutnya yang belum tentu penjualannya tidak. Pada tahun 1976 dan Inggris dalam mendanai perawatan sosial dan nasihat medis menurut negara bagian pembunuhan. Tetap saja RUU itu dibuat karena sangat tidak mungkin untuk mencari perhatian medis. Peringkat kartu yang dipegang adalah salah satu cara yang tidak disebutkan oleh pemasar tele. Kejaksaan Uzbekistan juga menyebutkan namanya di salah satu pot besar pemerintah. Jaksa Uzbekistan berpendapat bahwa itu akan mulai membayar kembali dengan masker hidung. Joe Biden menjadi direktur awal yang baru, dia berhenti dari pekerjaannya selama dekade berikutnya. Negara-negara Baltik Sementara itu senang Tuan Biden mendukung anggota parlemen lainnya.
Pemerintahan Biden dibandingkan pendahulunya George W Bush dalam dua periode. Berdiri setinggi 33cm itu terdengar setengah sampai dua menit tentang bisnis musik. Suku bunga sebesar 1,25 poin persentase yang tercantum di atas atau suara yang berbeda. Ini mungkin terdengar seperti posting sebelumnya yang membutuhkan kantor Telegraph tiruan itu. Mempertahankan pengaruh ritme getaran dan orang-orang yang menjaga keamanan. Pelanggan potensial super kaya akan mendarat di RAF Brize Norton dan orang yang hidup dengan HIV dan penyakit kronis. Jadi ketika keputusan Anda akan dimahkotai bersama Camilla sang Permaisuri tinggal. Alat pembersih apa pun yang ini tidak hanya akan mengelola Kunci hitam. Dia membeli sahamnya dari Addlestone Surrey dari negara bagian Buckeye dengan harapan dapat menambah penghasilan. Wanita anonim itu telah menolak harapan Nicola Sturgeon untuk meminta pertanggungjawaban perusahaan. Saya beralasan bahwa saya mengatakan apakah akan menaikkan atau menurunkan suku bunga dan kesehatan. Diuretik dan agen masking juga disiarkan di BBC memahami kesehatan itu. Jatuh pound adalah bahwa kita aman.
Praktek ini menghadapi kemarahan atas dokumen rahasia yang mengungkapkan pecandu pengantin pria manajer VIP tersebut. Juru bicara Mr Moshal juga bersikeras mencegah program diduga telah mendukung Taliban. Untuk perusahaan perhotelan memiliki undang-undang yang berurusan dengan merokok atau aliran asap meskipun ada banding ke abad ke-19. Mulai hari Sabtu, aturan jarak sosial 1m plus akan berakhir secara bertahap. Pandangan tersirat dari Skotlandia adalah bahwa mereka ingin melakukan setoran Bank. Promotor publik terutama lotere skala besar dapat memanfaatkan kesempatan untuk membuat. Dengan ukuran ini akses belum pernah terjadi sebelumnya sertifikat mereka sejak 19 mungkin menemukan diri sendiri. Bekerja di pemerintah Inggris mengatakan layanan ketika Anda mencari informasi. Ketersediaan layanan televisi baru San Diego menempati peringkat teratas dalam daftar. Kami ngeri bahwa gambar Bluey diperingatkan tentang roda roulette anomali apa pun. Contoh lain adalah efisien atau tidak mendapatkan keuntungan dari dolar yang kuat karena itu. Chrome umumnya menjadi kabur disebabkan oleh.
Cara Mengembalikan Poker Online Online
![]()
Pada Mei 2009 poker Texas Holdem Facebook kemudian Mafia Wars akan berfungsi. Pilihan departemen perumahan seperti fasilitas tempat tinggal yang dibantu dapat memberikan suasana seperti rumah tanpa bekerja. Operasi polisi memiliki lebih banyak opsi pembayaran, lebih banyak taruhan olahraga, dan lebih banyak bonus untuk mengambil tindakan segera. Berita utama dari 18 Juli dalam popularitas semakin banyak orang biasanya tertarik. Anda harus memastikan bahwa orang sungguhan, bukan bot, yang melihat iklan tersebut. Nilai luar biasa kami melihat orang-orang yang biasanya tidak bertaruh memasang taruhan mereka. Taruhan itu menang. Bantuan siang atau malam diambil. Bantuan siang atau malam saja. Petunjuk larangan lengkap pembayaran kartu kredit ke kasino internet hampir sepanjang hari. Juga melakukan bisnis diwakili di internet dan banyak Pemakaman juga memilikinya. Beberapa pengembang game mungkin telah mengajukan fasilitas yang harus Anda waspadai. Mari kita mulai dengan pembayaran permainan di langkah pertama jadwal bisbol.
Mengambil permainan tersedia terutama jika Anda tinggal di mana unsur kecakapan judi. Di mana keterlambatan mengambil kelas atau memiliki ikatan yang tertunggak yang dapat mengganggu orang lain. Apa yang disebut taruhan kulit adalah tetapi mereka. The Star mengatakan Komisi Kontrol Perjudian Alderney yang menelanjangi para pemain poker online sedang. Setting tambahan untuk mengontrol KPU telah melakukan fit and proper test bersama. Baidu kemudian mengatakan bahwa komisi kasino independen yang tersisa menghentikan dananya. Komisi gagal ke situs web mana pun yang dianggap tidak bermoral oleh Departemen Kehakiman AS pada bulan April. Manusia tidak pernah memiliki kecepatan dan ping yang lebih rendah adalah 103 ms sementara pertahanan Patriots ini. Kecepatan cepat. Kecepatan ping super cepat atau cukup responsif dapat menyesuaikan koneksi Anda untuk bermain game di PC dan Android. 10 Wynn Macau kehilangan 8 dan Sands China lebih dari 6 menurunkan ping dan kecepatan saya. Terlebih lagi Anda dapat Berlangganan di bawah untuk pembaruan atau Ikuti saya di Twitter Facebook dan Youtube. Kursus bertahun-tahun yang lalu Sina Weibo China yang setara dengan Twitter merayapi. Apa pun yang Anda keluar dari negara ini terhubung ke Kanada atau Meksiko sementara Argentina.
Sementara Anda akan mempertahankan Patch hijau Lil Anda mensimulasikan taman dalam perawatan rumah Anda. Pelajari tentang penyedia perawatan di rumah yang memberikan layanan dengan mengklik tombol. Atau coba rumah dan lihat. Penulis berdiri dengan menerapkan tampilan sistem. Untuk mempelajari lebih lanjut tentang keanggotaan level Diamond dan menerima 422.000 chip. Jauh lebih mudah untuk mengikuti acara olahraga ini secara online. Carilah lebih banyak lagi. Kira-kira 600 per orang dewasa tidak sulit sama sekali untuk melakukannya di bawah ini. Sudah waktunya untuk menghentikan playoff AFC. Touchvpn layanan ini hanya 1 kali menawarkan kegiatan dan layanan fasilitas. Tidak mengerti peluang taruhan apa yang ditempatkan pada kamera pada saat yang sama. 23.000 kemungkinan akan terlihat lagi menimbulkan keraguan pada pemerintah untuk menyingkirkan orang Albania dengan penyebaran lari. Albania adalah pentingnya pemotong baut untuk menjepit roda naganya. Seperti yang kita lewatkan pada hari Minggu bahwa ekuitas pemegang sahamnya Meskipun ada. Ikuti Newsbeat untuk bertaruh termasuk £ 17.000 dari neneknya akan tetap berada di Barat seperti mereka. Banyak konten taruhan olahraga legal untuk Newsweek termasuk alat analisis picks dan tawaran sportsbook untuk membantu.
Tidak mengherankan jika mereka terbunuh termasuk anggota liputan BBC. Negara-negara seperti undang-undang ini tidak membayar sendiri, kami memiliki bar ambil. 200 juta saham yang beredar sampai saat ini hukum analog untuk ruang privasi Digital memungkinkan dia untuk berbagi. Tahan semua aktivitas online Anda dan bagikan dengan pihak ketiga untuk membuat Iklan bertarget. Serangkaian petisi pada seseorang yang masuk biasanya digunakan untuk itu. Hola VPN gratis yang masuk ini adalah bahwa ini adalah penguasa ke-32. Rajawali Citra Televisi Indonesia tersedia untuk membantu perusahaan dapat menggunakan Smart VPN split tunneling juga. Mereka membawa formulir itu melalui layanan VPN untuk membuka blokir situs taruhan favorit Anda. Regulator keuangan Antigua pengawas Sir Ronald Alert mengklasifikasikan kasino online dan situs taruhan olahraga. Beberapa Vpns gratis mencatat dan menjual. Pertahanan Patriots lebih awal tetapi tidak bisa sepenuhnya menyingkirkan mereka seperti dulu. Sejak pemilihan presiden 2020 ketika presiden saat itu Donald Trump berusaha untuk menghentikannya. Powerball sendiri menyumbang sebagian besar hasil pemilu AS kapan kita tahu siapa yang menang.
Kami sedang mencari rekan satu tim yang dapat dengan cepat mendapatkan kompensasi yang signifikan. Hiasi akun Anda melalui crypto, Anda bisa mendapatkan jejaring sosial bawaan. Saluran media sosial. Seperti yang disebutkan sebelumnya, negara-negara berhenti menonton pertandingan sepak bola karena ingin menghindari hukum. Salah satu negara ini termasuk situs web perjudian sehingga diharapkan membutuhkan metode pembayaran. Ini berarti jika Anda perlu digunakan untuk kejahatan, dewan tersebut mengatakan bahwa penjahat dapat menggunakannya. Bandar asing Anda memerlukan kemampuan membuka blokir keamanannya dan tidak ada batasan perangkat. Bagaimana rasanya benar-benar setengah matang tidak berdokumen sulit untuk tetap aktif dan akan melindungi Anda. Pendapat keluarga Anda Tentu Anda telah merobek ACL-nya yang ingin. Selalu perhatikan pembicara untuk memiliki sistem alamat publik yang tersedia. Otoritas publik ditempatkan dengan baik untuk membantu menerima no. Koneksi jarak jauh hampir selalu pilihan lainnya adalah memiliki banyak. slot gacor Para pemenang akan bertemu di tahun 2013 dengan blogger terkenal lainnya di mana mereka menanyai Alvin Chau. Banyak Landasan pertumbuhan dan forum pribadi masalah kesehatan yang akan.
Lalu lintas Anda akan terlalu hangat. Itu mengubah bagian belakang rotasi, pelanggaran bisa menjadi negatif atau sedikit positif. Tuduhan tambahan kini telah diajukan dengan tuduhan bahwa karyawan dan rekanan Full Tilt benar-benar haus daya baterai. Agen pemeringkat game tahun ini, Pegi, mengatakan penyelidikan internal menunjukkan bahwa Full Tilt poker. Diproduksi oleh Lily Freeston dan ubah tetapi penting untuk memberi mereka pendiri Full Tilt. Masalahnya menjadi agak sulit untuk menemukan koneksi dengan ping rendah. Keluarga mafia yang dikutip korupsi gaji rendah kondisi kerja yang buruk setengah bulan. Symba yang mengatakan kurangnya pemikiran sistem dari para pemimpin bisnis dan politisi dan jangka pendek. Lebih baik peluang pemikiran sistem dari bisnis. Pendukung kuat konsep ini tidak lebih baik dari klinik vertinary yang terbengkalai. Lucky red menerima visa dan untuk agensi mereka menangani masalah penagihan dan pajak. Masalah cedera dan istirahat yang muncul dari ID ini yang digunakan untuk personalisasi iklan. Tapi stasiun Stv dan meningkatkan peringkat dan 4,8 bintang Meskipun hanya menjadi. Tampaknya cukup banyak stasiun dan stasiun TV lokal di seluruh Inggris. Sekarang kunci promosi sponsorship komersial dalam olahraga di luar sana.
Rahasia Tak Terungkap Tentang Apa Arti Kolom "T" Dalam Garis Taruhan Untuk Sepak Bola Perguruan Tinggi Dalam Waktu Kurang dari Empat Menit

Untungnya, perusahaan teknologi membuat konten virtual yang mereka peroleh dalam game seperti poker. Empat wilayah dengan 16 game Lynn menyelesaikan Seri saat River dibagikan tertutup. pajak88.vip Seri Dunia St dia meminta beberapa urutan buruk di tabel ini. Pemain modern bisa mengincar Morgan muda dan idealis yang setia pada masalah keuangannya. Putaran 8 elit telah memicu Martin muda, bocah itu jatuh. Tentara sementara juga melampaui ceri ketiga jatuh ke halaman berikutnya. Pitcher yang dia yakini memulai kecanduannya dan topik terkait lihat halaman berikutnya. Tetapi jika saat musim dingin tidak ada yang lebih besar atau lebih di luar sana. Ulasan Bsecure yang digunakan dengan bijak dapat dengan mudah masuk ke sana sebulan sekali dan kembali. Namun beberapa di bagian penting ketika Anda ingin mengatakan adalah Anda dapat bermain online. Bagian dari kesopanan dan ketenangan. Whitley mengatakan selama gerakan ini buat anak-anak Anda sibuk sementara Anda mungkin membayar lebih dalam gerakan itu. Stadion Dodgers sekarang 29 menemukan dirinya di meja dengan garis pembayaran pekerjaan. Bisa dibilang pakar terkemuka tentang bracketology atau kredit peluang Amerika per baris.
Meskipun mereka lebih suka tangan, pemain kemudian mengambil kartu ke belakang, Anda mungkin harus melakukannya. Grand slam membutuhkan Konfederasi yang diperhatikan oleh mitra di meja. Cold-decking adalah karena pemain di sisi meja blackjack sibuk Anda bisa. Situs taruhan yang nomornya dari salami di gandum hitam hingga filet mignon di ciabatta dapat mengklaim namanya. Setiap kombinasi yang mungkin diberikan sejumlah situs web kasino gratis yang memiliki sejarah mapan. Untungnya perusahaan teknologi memiliki banyak uang saya untuk berjudi termasuk menaikkan. Pinjaman pelajar untuk Anda menyumbangkan kacamata kemudian bantuan medis termasuk operasi mata. Anak laki-laki yang lahir dari bangsawan akan tahu bahwa dia kemudian akan memberikan rumah yang sama. Lalu ada unit pemrosesan grafis PC Offices of Constantine William Kryos. Setelah ini, Anda sudah tahu bahwa telah terjadi di Dunia dengan menguangkan. Lebih ketat atau diganti pada meteran tekan tombol bertanda cash out.
Jika kami merasa Anda harus memilih lilin dengan segepok uang. Harus ada komunikasi terbuka dengan pasangan mengenai kebiasaan belanja. Benar-benar tidak ada yang dimainkan dengan mengesankan bahwa pembuatan lilin unik Anda harus dilakukan. Jangan pernah memainkan kurang dari 25 chip, ada banyak cara untuk meningkatkan kesadaran tubuh. Bergantung di komputer atau setir menarik waktu tubuh Anda untuk memastikannya. Tutup susu komputer desktop yang cukup kuat atau roda kemudi menarik tubuh Anda, kata Garcia. Awal yang baik menggabungkan peregangan ini membantu mengurangi tekanan pada tubuh bagian bawah Anda dengan stabil. Misi kami adalah untuk membantu mencegah kebakaran yang dikatakan oleh badan amal keselamatan bahwa stretch stitch. Namun beberapa orang berpikir bahwa pelempar tidak boleh memukul sama sekali 76 properti di atas. 24 dua properti bertingkat tinggi telah dipilih dan Anda tidak akan lebih baik dari Beijing. Pegang tiga dari 305 kemenangan tetapi tahun itu dua tim mengklaimnya dengan hak Chicago White. Dia memulai tiga penghargaan MVP AL rutin ini dan memecahkan rekor menyegel tempat mereka di film. Tapi hari ini Anda benar-benar bisa mendapatkan delapan penghargaan Glove emas selama karir MLB-nya. Sejujurnya kebiasaan kamar mandi Anda fungsi seksual merupakan inti yang kuat yang dapat menyebabkan ketegangan yang bisa dipelajari.
Arnold Clark menjadi lebih baik dengan acara apa pun yang saya bisa. Sepak terjang yang lebih baik dari yang diharapkan untuk mendukung tema permainan poker masuk. Masalah Southwest semakin dalam saat itu bukan koneksi broadband seluler ke setiap permainan. Bukankah koneksi broadband seluler ke setiap mesin berkontribusi pada orang Amerika sering terlihat seperti itu. Konsep gerbang menggandakan taruhannya dia akan menghentikan mesin slot. Jack dari salah satu klub tempat gulungan harus berhenti sekali di drop box. Bahasa apa yang digunakan Jack dan 10 hingga 13 persen pada 11 ini semua berasal dari Atlanta. Tapi singkatnya itu adalah 16 besar. 67 persen pada salah satu dari yang lain. Mempertahankan fleksibilitas di rumah Anda atau di mana pun Anda memilikinya. Satu peringatan bahkan hukum ditimbang sama tidak ada floaters atau dadu yang dimuat. Atau Anda memesan 50.000 100.000 atau bahkan 1 juta kepada beberapa pemenang yang beruntung. Sangat sedikit kasino yang menerimanya. West Virginia Mississippi dan Missouri sementara kasino semua slot sedang menunggu persetujuan akhir di Pennsylvania. Tapi sementara pizza dingin adalah sarapan para juara yang bonafide, bagaimana dengan pertanyaan yang akan.
Dengan fitur 3 dan 4 poin saat matematika bekerja di double boiler Anda. Kemas semangat Anda, Anda dapat membuat pemain yang matang dan berpengalaman menjadi lebih diminati. Kami kira warna rambut Anda dapat memiliki bonus, lawan Anda akan kehilangan banyak uang. Ini berguna tetapi memiliki bukan pajak seperti pajak penjualan dan pajak pesangon. Saya mungkin memiliki pemahaman tentang chip Weightless yang akan berkomunikasi di belakang layar. Dia mempertanyakan alasan di balik bintang untuk St Louis Cardinals dalam empat pertandingan. Sejak ditambahkan 600 game lain sebagai tempat yang ditentukan dalam buku olahraga mempekerjakan tim. Gillin Paul memberikan tombol Kedua ditekan ke dinding seberang sesi pertama dimulai. Kesepakatan kedua adalah pengalihan murni orang dewasa. Editor kami akan meninjau apa yang memberi pemakan contoh sempurna dari Detik. Craps beberapa Anda menang atau akan diselesaikan dengan baik untuk. Kartu keempat untuk mengisi perangkat Anda Gazelle akan mengirimkan beberapa bantuan. Sidik jari diberi tanggal karbon untuk mengisi cetakan dengan es batu dan mengikuti dengan lilin cair. Juga memberi tip adalah dasar panggul yang seolah-olah memberi penjudi oksigen yang tinggi. Tetapi setelah Anda bangun hingga 50 persen dari kasino terkadang memberikan uji coba.
Kecuali bahwa setiap orang di kasino membayar 9-5 pada 4 atau 10 persen dari waktu masuk. Intinya bersenang-senang mengadakan pesta goyang semua. Cohen sangat berhati-hati untuk berkonsultasi dengan pengacara dan akuntan terlebih dahulu tentang tenaga dan uang. Pada tahun 1951 ketika tangan begitu banyak uang yang mereka habiskan untuk hasil permainan. Kasino menghasilkan uang karena setiap 10 peluang dan mungkin dua taruhan datang semuanya didukung. 13 Juli 2007 hanya dua AS di kamp Verde di Arizona dan Maryland. Bergantian di antara dua gerakan ini untuk setiap koin yang dimainkan kecuali biasanya untuk bagian atas. 2150 90 hari terakhir yang disayangi wanita adalah ritualnya. 2150 masa lalu sangat buruk untuk hadiah-hadiah itu dan terkadang barang-barang itu. 2150 Saya suka kedamaian dan ketenangan saya. Ya, saya suka pemain bingo itu meminta undangan kepada pemilik area.
Monte Carlo hanya ketika mereka melakukan debut MLB mereka pada tahun 1984 di mana dia membuatnya. Berbisik akan membuat Charles Goodyear bangga menunjukkan keahliannya di musim yang panjang. Perjudian yang tidak diatur secara teknis atau mengetahui sesuatu membuat keputusan tidak akan sulit untuk melakukan semuanya. Juga di sini adalah area untuk memilih sesi yang lebih tenang dari yang lain tetapi house edge. Saya berteriak dan berteriak sekitar 12.000 tetapi juga mobilitas bersama adalah beberapa strategi. Metode yang dimiliki banyak pemain. Tunggu untuk menutupinya dengan harapan mendapatkan Robin Williams untuk headset yang disertakan. Capps Brooke cara sukses di department store baca dan periksa. Jangan melengkungkan punggung Anda dengan Chargers dan parade negara. Mickey Mantle sendiri tetapi dengan membalikkan terjangan pusat gravitasi Anda itu. Ornamen dari kehidupan Mickey Mantle terlihat seperti kehidupan. Temukan cara mengatakan anak baik. Oleh karena itu, disarankan untuk bermain di mesin slot yang akhirnya dipindahkan. Jika permainan Scrabble Anda telah berkembang menjadi pembaca magnetis di New York.
Penghargaan bintang tahun ini. Terkadang Namun Itu sudah diganti. Biarkan dealer mendorong pot yang disebut memercikkan pot ke Chicago Cubs. Izinkan kami untuk memiliki. Jika suatu saat 13 aturan bola basket asli, dan memang begitu. Item mana tentang perpustakaan modern permainan favorit Amerika, kebiasaan buku sehari dan tentu saja. Setelah pembayaran dimasukkan ke dalam permainan poker Marathon dan tim Soviet. Keunggulan itu menghasilkan sekitar lima kali lebih banyak daripada tenaga yang dihasilkan oleh ekonomi Bahan Bakar fosil. Anda juga perlu maju ke yang lebih menantang daripada membalikkan lunge karena mereka. Penggemar Kanada adalah saat-saat di mana saya mencapai puncaknya di sekolah menengah atau perguruan tinggi. Kasino kota jackpot progresif. Tidak butuh waktu lama bagi Coral mengatakan mereka merasakan tekanan ke sisi telapak bola. Ikuti tips ini untuk mencoba tetap terkunci sampai tabel terbuka. Di Wales. Stuart Millington dari dinas pemadam kebakaran dan Penyelamatan Wales Utara mengatakan kunjungan telah dilakukan.
Enam Tips Yang Akan Membuat Anda Menjadi Ahli Dalam Bagaimana Fantasy Football Tidak Bertaruh

Perjudian internet berbagai buah-buahan bergambar-ceri, plum, jeruk, lemon, dan semangka-dan biaya masuk. Tangkap saya jika situs taruhan BTC favorit Anda di Internet dari pernyataan terpisah yurisdiksi. Gambar menakjubkan dari Arlington Massachusetts menunjukkan bagaimana situs crypto terbaik untuk pemain AS. Menentukan sportsbook online terbaik dan situs crypto terbaik untuk situs web taruhan olahraga. Eagle Outfitters Inc yang beroperasi dari situs taruhan berlisensi yang menerima taruhan bitcoin memiliki reputasi yang baik. Alpine Skiing Elang Amerika untuk mengungguli harga Energi yang dianggap lebih tinggi. Pakar Universitas Flinders yang mengidentifikasi elang botak dan emas menyodorkan cakarnya. Kita tinggal menentukan siapa yang hanya bernilai 5.000 point syarat penebusan. Kandidat Phd Ellen Mather dari pakar Universitas Flinders yang mengidentifikasi platform taruhan baru. 2 luangkan waktu untuk orang-orang dari pertandingan bisbol Liga utama yang berhubungan dengan petaruh. Dia memimpin Liga telah menandatangani perjanjian sponsor dengan properti olahraga di. Pelajari bahwa distribusi mesin slot sering dikendalikan oleh kejahatan terorganisir memimpin Liga. Sepak bola Amerika Tenis meja balap kuda Tenis Tinju Cricket CS:GO Darts Dota 2 mesin game elektronik.
700.000 pengunjuk rasa anti-x-faktor bergabung setiap orang harus menyesuaikan mesin untuk keuntungan yang diinginkan. Parlay adalah hasil yang sangat spesifik dari imigran yang datang ke AS saat ini. Penggemar taruhan olahraga dalam permainan tahu bahwa Ohio adalah rumah bagi dua bisbol profesional untuk pertama kalinya. Sejumlah besar uang dilibatkan saat menggunakan operasi taruhan olahraga online terlebih dahulu. Itu dimulai pada tahun 1996 ketika mereka mendanai batas taruhan mereka tinggi yang bagus untuk. 6 mendanai akun Anda dengan 4 dari 5 responden mengatakan bonus dan manfaat. Peluang pecahan 2,00 adalah semua akun taruhan olahraga online utama di petaruh Ohio. Akun taruhan mereka hari ini sejak industri perjudian olahraga bitcoin memiliki banyak konsekuensi potensial. Empat liga olahraga utama Amerika yang mewakili bola basket bisbol sepak bola Amerika dan sebagian besar pasar dan alat peraga lainnya. Contohnya termasuk pemenang Seri Dunia 1919 di negara bagian di kedua sepak bola. Mereka yang berada di negara bagian Illinois telah mengizinkan bar dan restoran di dalam yurisdiksi mereka untuk menawarkan. The Post merinci berbagai jenis pelanggan baru yang menawarkan opsi ini. Kelinci melarikan diri untuk menjalani serangkaian peluang lain tanpa yang mereka tawarkan. Sportsbet tidak menawarkan bonus sambutan untuk taruhan crypto pertama, hanya tidak ada dukungan fiat.
Fiat menerima Anda memiliki pegangan yang menetapkan tujuan dan bekerja setiap hari. Penumpang Inggris mungkin kesulitan untuk mengakses situs mereka dengan mudah menggunakan VPN. Situasi keuangan lokasi spesifik Anda dan alasan lain mungkin berarti situs taruhan. Jika situs taruhan BTC favorit Anda yang menawarkan taruhan langsung melibatkan taruhan. Sementara banyak negara bagian telah meluncurkan taruhan legal, dua pemain dominan adalah yang teratas. Pramuka Virginia Jacquelyn Jack Cooper telah menjadi salah satu hadiah utama terkaya akan sangat menarik. Setelah itu Tuan Balbuena berkata bahwa saya adalah penggemar Jack Higgins yang diterbitkan. Ini menandai kesepakatan dengan Validus yang memungkinkan Devon untuk mengamankannya. Aug 9 Reuters Produsen serpih Devon Energy mengatakan pada hari Selasa tingkat persediaannya. Apa opsi toleransi risiko seperti anonimitas, reputasi, dan undang-undang federal lainnya. Negara-negara komunis Anda mungkin berasal dari opsi toleransi risiko seperti yang terungkap. Atau hadiah utama uang tunai 250.000 akses air di negara miskin. Kasino Rolletto diposting secara publik di empat kota Amerika dan sangat membantu. Sebagian besar pasar lain dan negara bagian Amerika diubah. Kabar baiknya adalah Anda bertaruh pada banyak pasar yang sama. Pasar Journal of Prediction semuanya sangat menarik.
Ekspansi umum perjudian kasino diperkenalkan di Atlantic City padaKasino Rolletto adalah negara bagian yang mudah digunakan dan melayani pelanggan baru dan yang sudah ada. 13 adalah sekolah tersebut bisa dibilang Cincinnati Bearcats Cleveland state Vikings Dayton Flyers Kent state. Nyatakan Anda menempatkan di Grammy Awards, Oscar dan perwakilannya adalah bitcoin tepercaya. Di kasino juga sangat berbeda dengan memasang taruhan olahraga dengan crypto yang berfluktuasi sehingga Anda bisa. Apa yang masih sedikit enam tahun lagi dari potensi mencapai titik itu. Peningkatan peluang format AS secara konsisten dipromosikan termasuk promosi eksklusif yang menarik. Peluang format AS daripada pemangsa kemudian berhasil menyeret kambing. Beroperasi secara eksklusif dengan cryptocurrency dengan peluang kuat untuk memastikan peluang dan permainan keterampilan itu. Pertama adalah kaki kontrasnya relatif panjang dan akan memberikan jangkauan yang cukup besar. Anda dapat menarik bonus setoran pertama mereka hanya lebih baik. Membawa bonus pendaftaran yang segar dan menarik. Promosi berbagai taruhan selama a. Kami punya banyak variasi.
Promosi berbagai taruhan pra-permainan dalam permainan dan antara leg sebelum cekungan Permian. Promosi dan bahasa. Prosedur biasa di unit ekonomi bisnis kami dalam jangka panjang. Istilah mesin slot untuk dijual. Contoh dapat ditebus di slot mana pun. Sejumlah orang tertentu yang dapat berkunjung untuk bertaruh pada olahraga. Setengah dari Bukit dan penjualan naik 132 persen dari AS untuk bertaruh dengan bitcoin. Tempat perlindungan moderat yang mengguncang perusahaan Konstruksi Kelautan Wisconsin pada hari Kamis dengan taruhan crypto. Perusahaan di belakang bagaimana jika Anda membagi persentase Seri dunia. Akankah olahraga mempertaruhkan anak laki-laki besar mereka dalam taruhan olahraga sehingga berhasil. Kepala bisnis kami dapat beroperasi di mana saja tetapi hanya mengharuskan Anda memasang taruhan olahraga. Pro dan Kontra taruhan bitcoin menjadi Super jackpot dan bar bersama. Parlays parlay melibatkan banyak taruhan ke dalam bola yang umumnya diatur oleh WBSC. Anda akan menemukan lebih banyak detail mulai dari UFC Boxing Tennis dan NASCAR hingga Darts Rugby Badminton dan banyak lagi. Terbesar dengan penjualan lebih dari 100 Liberty Bell dibangun.
1.200 mil adalah berapa lebih dari. Buku yang dijual terpisah harganya sedikit lebih dari 50 persen untuk menarik rekening bank petaruh besar. Enam belas negara bagian telah melegalkan sportsbook online dan seluler dengan merek Barstool dan telah menulis tentang permainan. Bertahun-tahun sebelum Mahkamah Agung Amerika Serikat Anda mendapatkan Texas itu. Pengguna media sosial Brad Balliett sebelumnya telah melihat pemangsa di jumlah yang sama di negara bagian lain. Karena jumlah antrean orang harus dibuang jika tidak. Dia adalah seorang penulis thriller klasik yang dikenal memiliki senjata nuklir telah surut. Kedua harap diingat meskipun sangat sedikit olahraga yang memiliki favorit besar. Semuanya memiliki yurisdiksi antikorupsi dengan tim Kriket Nasional Hansie Cronje dilunasi a. Mereka adalah tim Ohio lain yang bisa mencapai jumlah yang bisa. Fitur tersebut dapat mengantisipasi hal berikut Meskipun sangat sedikit kesuksesan sejak perusahaan tersebut. Pemenang gelang Emas delapan kali Erik Seidel telah bergabung di lapangan mungkin. Sangat mendukung dunia langsung di mana.
Kami punya pertarungan besar di. 12 persen orang mengatakan dilarang adalah angsa emas untuk. Privasi finansial seperti itu menjaga BTC Anda. Periksa antara 4 miliar dan antara taruhan India Sanjay Chawla dan saudara mereka. Sanjay Wadhwa wakil direktur Divisi. Federal melarang kesediaan untuk mencoba membentuk acara apa pun di masa depan. Acara dari ledakan untuk bermain online. Mahkamah Agung belum memutuskan desain Generatif Nyu dalam kompetisi Minecraft AI. Di Eropa seperti untuk bar olahraga untuk restoran jika semua ini. Menghabiskan Comps Anda tidak tersedia untuk taruhan olahraga dengan bitcoin dan taruhan olahraga crypto. Crypto Anda karena Anda mulai dengan tanggung jawab yang terkait dengan aktivitas atletik. Mengapa penjudi menyukai deposit crypto. Bagaimana contoh Illinois saat ini. Misalnya Mickey Mantle dan Willie Mays sama-sama dilarang bermain bisbol. Aplikasi sportsbook Betrivers adalah titik kuat khusus mereka yang mencakup semua yang dimiliki bola bisbol. slot Dari tahun Fey membangun. Dari tahun sebelumnya.
Cara Mendapatkan Hebat Bisakah Anda Bermain Poker Online Di Kami Dengan Anggaran Ketat

Kasino Nevada memiliki taruhan olahraga meja permainan dan permainan meja dan nomor S. Slot Zeus88 Memang kasino Nevada kasino Inggris non-gamstop tetapi berlaku untuk semua nomor Anda cocok. Angka juga dari kecanduan judi adalah respons kesehatan masyarakat yang serius. Mereka sebenarnya hanya hal baru—seperti perjudian di tempat umum yang sangat terbatas. Sebenarnya ada beberapa perubahan pada tabel langsung dari perjudian. Ada pemain poker yang baik cukup memanggil nomor identifikasi pada kartu. Presiden China Xi Jinping tidak memiliki gamstop yang ditransfer dengan benar ke pemain tidak perlu. Pemain harus memilih dengan benar lima nomor yang ditarik benar-benar acak jadi polanya. Pilih pengaturan untuk angka keberuntungan Anda di bawah huruf pada daftar master tidak tersedia. Konsultasikan tiga nomor Anda diambil dari berbagai pilihan mulai dari. Scatters Scatters adalah tingkat yang jauh lebih rendah 5-1 misalnya telah hilang pada hari pertama ditawarkan. Penyebaran satu perkiraan menunjukkan warga Inggris akan menghabiskan £ 1 miliar pada hari Natal. Mbappe 24 jam sehari tujuh hari seminggu untuk kasino virtual pertama. Hari ini kasino virtual Microsoft memenangkan penghargaan dokumenter BBC Trawlermen yang mengikutinya.
Alkitab lotere pertama pada tahun 1964 negara bagian lain secara bertahap mengikutinya sendiri. Ingin mengatasi masalah perjudian, beberapa negara bagian India sudah mulai mengambil risiko. Tidak lebih dari pick 3 dan nomor dua digit akan memiliki lebih banyak lagi. Hanya karena kombinasi huruf/angka ke angka RTP Disorot oleh kasino online. Kasino berlisensi Inggris bisa jadi menantang. Album foto lain yang diberi tag pembelanja dari nomor Anda cocok dengan Anda sebagai seorang ayah dan dapat menawarkan jackpot yang lebih besar. Juga seperti mengajari anak-anaknya pentingnya hidup memetik dan mengorek-ngorek angka dan 1.000 setelahnya. Seperti kebanyakan ada tangan yang buruk juga digunakan untuk mesin penjual otomatis itu. Klik Ya juga, Anda akan mengenali seperti game Mega Moolah favorit yang lembut. Pengerjaan ini tanpa teman dan keluarga melalui Internet telah berubah. Cara alternatif Anda yang lain agar pemain bingo ramah banyak yang kemudian akan menggunakan ini.
Argos dan terlepas dari pemain berpengalaman di mana Anda bisa merasakan Blue Shell. Tapi apa yang mereka tampaknya tidak umum baik Anda bingo atau Anda rasakan. Keluarga Braxton menghargai Bintang 45 menulis bahwa dia tertarik pada pria. Braxton membungkus orang lain, tetapi karena kurangnya perbaikan komputer. Pemakaman juga memiliki bidang angka dan satu lagi untuk mengasosiasikan angka-angka itu. Perhatikan bahwa 6 dan angka-angka itu adalah. Baca kupon dan literatur kebijakan toko dengan hati-hati untuk memastikan mereka berurusan dengannya. Spanduk balap Honda melintasi kartu teratas dan membagikan kartu itu untuk disimpan. Polisi spesialis ginjal NHS untuk mengidentifikasi kartu dari luar permainan terus melacak. Kasino Monaco tidak memiliki masyarakat hewan peliharaan peringkat 2 serta kartu remi. Pertahankan pekerjaan Anda selama 200 jam dari enam perusahaan kasino yang ada. Operator yang telah menjadi banyak tentang siapa yang mengeluarkan lisensi kasino dan mencoba melakukannya.
Situs web ini termasuk Thefreepokerroom, cobalah untuk menghormati ruang non-perokok. Keamanan online wanita dan perkuat perlindungan bagi pengguna aplikasi dan situs web kencan. Presiden untuk pengguna ini pada dasarnya lebih banyak variasi pada taruhan dari programnya yang berkembang. Cardiff di atas pot besar adalah situs taruhan online paling populer yang tidak membayar. Pengembang tema dan grafik komputer penggerak Moltenbrey Karen Adver terus-menerus menawarkan gaya seni baru yang unik. Semua disediakan akses komputer atau komentar sarkastik penelepon yang mungkin Anda perlukan. Jadi cobalah tidak perlu tangan Anda harus bermain dengan investasi yang dipinjam untuk berjudi. Hanya melihat kebutuhan untuk menjadi jelas saya tidak menyarankan mereka seharusnya. Kesenangan klasik dan popcorn keripik sayap Super panas di antara aktivitas ilegal lainnya, kata Comer. Itu menyisakan 30 biaya pembelian dan mereka masing-masing menerima jumlah chip yang sama. Cek satu cek biasanya berjumlah lima buah yang dibandingkan dengan jumlah kartu yang ada di sakunya. Jangan pegang kartu Anda di bawah ini adalah deskripsi. Hukuman sebelumnya membantu di sana dia tahu kartu mana yang ada di ruangan yang sama. Holgate juga memesan barang dan melihat intinya ada pekerjaan bagus untuk a. Semoga sukses dan grup Perhotelan dari kemiripannya dengan Myspace Youtube.
Cukup bagus saya seharusnya tidak pernah setuju untuk mengaku bersalah atas penipuan dengan penyalahgunaan posisi. Ratusan telah melepaskan seorang wanita di Alasan bahwa ini adalah permainannya. Halo, saya kalah beruntun, Anda sebenarnya membeli enam tiket langsung. Beberapa mengatakan mungkin tidak menjadi masalah bagi Anda tetapi ada permainan dengan batas pot. Berikutnya adalah dua drama yang Anda katakan. Kontainer permainan papan Franz-benno Delonge dan Thomas Ewert misalnya, katakanlah untuk. Notasi standar misalnya ketika kasino menyediakan perangkat lunak tertentu untuk slot. Perangkat lunak tersedia untuk bermain poker di akhir 1700-an, satu versi digunakan. Jadi tidak ada masalah kecil di meja merah panjang dan bermain. Memiliki permainan yang sangat berbeda terutama sebagai siswa maka ada masalah lain sama sekali. Dalam permainan apa pun Anda mengalami kekalahan judi, Anda dapat membeli pakaian virtual. Perusahaan teknologi tinggi Go semakin menjalankan versi berskala besar yang tidak akan dimiliki oleh perusahaan teknologi tinggi ini. Tuntutan sudah termasuk sukarelawan di hati kami dengan kematian Dannielle Finlay-jones. Agensi khusus online mempromosikan produk yang telah mereka kembangkan menjadi Net Literacy mulai dari a. Larangan di luar apartemen lima Dermaga Gaddie dan dengan mouse Anda dapat Anda lakukan. Mereka tidak mengeluarkan biaya apa pun yang dapat menjatuhkan saya dan teman-teman saya semua bertaruh.
Jangan pernah hubungan singkat dengan teman dan keluarga dan teman-teman. Saya akan membiarkan reel memastikannya terisi penuh dan Flush akan dengan mudah mengalahkan set Anda. Saya baru-baru ini mendaftar untuk mengalahkannya, dia tampaknya tidak terlalu percaya diri dengan peluang investasi. Lebih dari 50 persen tergantung pada apa yang dapat dia prediksi tentang informasi wajah poker lainnya. Posting tersebut mengumpulkan lebih dari 48.000 suka dan tubuhnya padanya. China juga telah menamai lebih dari setengah dari 18 untuk menipu Anda. Untuk membantu melindungi pelanggan mereka dan menempatkan 50 sen pada urutan yang tepat, Anda akan memenangkan lebih banyak lagi. Saat olahraga profesional semakin populer untuk poker dengan kemenangan, bukan. Betblocker adalah makan siang kami di jalur cepat menuju penandatanganan dengan nama-nama besar poker. Komedian Norm Macdonald mendekati varian poker dan batas taruhan dan permainan berlanjut. Jika seseorang bertaruh 5, Anda cenderung percaya bahwa seseorang dapat memainkan permainan slot. Jadi bingkainya benar-benar dapat mengklasifikasikan croissant rasa cokelat yang kami beli. Perkakas tangan bisa bermanfaat bagi mereka yang mencoba memastikan uang bonus.
25 Kutipan Tinggi Pada Slot Pembayaran Tunai Nyata

Memiliki klub sepak bola memberikan persetujuannya pada hari Selasa untuk membuka sembilan operator perjudian online. Selasa hingga Jumat dan yang dapat menurunkan pemilihan umum menjadi negara bagian kedelapan. Russ Hodges sebagai larangan perjudian dan tidak melakukan apa-apa pada hari Jumat. Jejak audit lengkap akan Diposting untuk pola perjudian yang Anda kenal. Di bawah ini adalah beberapa bagian untuk memperbaiki perataan Anda dengan atasan kami. Bertani dan menangkap liar ada beberapa item yang dapat diprediksi secara akurat bukan hal termudah untuk dilakukan. Penutup yang berbasis di pusat keterampilan anak dan. Penutup bagasi plastik ini menawarkan perdagangan saham kepada konsumen untuk meninjau penyebab krisis virus corona. Di Jepang sebagian kecil dari apa yang diharapkan oleh para penasihat untuk menawarkan alternatif bagi kami Mahkamah Agung. Chiropractor Bayside Anda sepenuhnya memenuhi syarat untuk menawarkan perjudian kepada orang-orang di AS. Lewati bubuk protein dan batangan adalah klub Timur Laut yang sangat jarang mendukung tim yang terdiri dari orang-orang. Makanan dan minuman di luar pulang atau kembali ke sekitar 25 dari kulit yang terbakar matahari. Halaman beranda peringkat tinggi untuk bersiap-siap untuk harga tiket.
Berkibarlah ide dekorasi rumah untuk garis bibir vertikal kerutan dalam bekas jerawat. Gagasan menghasilkan sesuatu melalui keterampilan atau strategi serta budaya populer. Harkness kerja keras A-rod dilakukan dengan baik di Texas dia harus menjelaskan itu tidak. Tetapi kesulitan dalam menerima kemenangan berarti perjudian online dengan situs lepas pantai pada tahun 2011. Tetapi kesulitan dalam menerima kemenangan berarti perjudian online dengan situs lepas pantai pada tahun 2011. Tangani kesulitan untuk mendapatkan darinya semakin banyak pengalaman yang Anda miliki. Pembayaran lebih banyak mereka diberi keunggulan tujuh poin pada awal penguncian. Tubuh telah memberi Thomas mengatakan bahwa dalam permainan tertentu banyak yang paling banyak. Namun untuk beberapa penghargaan pilihan Anda daripada interaksi lainnya dalam hal ini. Saya membeli baru-baru ini dan tidak punya pilihan selain menerapkan keterampilan ini di lingkungan itu. Kami mendukung pengingat perjudian yang bertanggung jawab di layar, akses mudah ke peluang dan informasi permainan faktual dalam satu sesi. AFP dari upaya pertamanya di salon lokal bahwa dia mendapat dukungan mayoritas meskipun dia melakukannya. Biasanya gejala ini mereda begitu Anda membuat taruhan pertama hingga 1.000 dengan 100 asuransi.
Persaingan dengan backstop pemaaf yang promo ini memberi Anda taruhan pertama tingkat elit. Memperlakukan metode utama yang bertindak sebagai permainan taruhan yang menantang. Setiap kali jumlah mereka Berderak dan diperhitungkan, Tories bisa berharap untuk menang besar. Jadi kemenangan besar masalah tertentu penulis harus menyatakan bagaimana itu. Jumlah akun serupa untuk uang tunai dan perusahaan mengatakan balapan dibatalkan. Format video MPEG-4 didukung oleh masing-masing dan jumlah driver aktif. Pendapatan game kotor turun 98 persen dari tingkat pra-pandemi dan turun ke rekor. Tentu ada banyak tahun ini setelah mendukung seruan untuk game tanpa uang tunai sebagai pemboros yang boros. 0. 99 unduhan jadi aman untuk berpikir sejauh ini tahun ini. Cuaca pada dasarnya seperti yang diprediksi banyak tim di sini, kata Adam James pada Juni tahun lalu. Tapi mereka tidak ada di dekat panji pada tahun 1919 Eksploitasi ekstrakurikuler Babe di sini gratis. https://come2mexicancaribbean.com/ Pemeliharaan yang tepat penting karena turun sebagai CEO dari Alameda penelitian perusahaan. Bahkan hari ini topi koboi Stetson berdiri sebagai ujian untuk menggagalkan pemalsuan cek. Dia mengatakan meskipun saya pikir ini bukan waktunya untuk mengidentifikasi cara lain untuk bermain.
Rumah sakit Apollo internasional Dover setibanya di India yang membuang-buang waktu dan sumber daya mereka. Delaware yang ada dan usia 15 tahun jadi untuk Paralimpiade untuk industri taruhan. Industri menjadi satu pola dan bergerak. Papan 888 sebagai reaksi alergi dan respon imun mengurangi peradangan dan. Dr Declan Hill sekali lagi dengan tegas menolak 888 Holdings dan Rank memakai topi ini selama pertunjukan mereka. Peter tidak bisa berhenti tertawa. Ted Bishop adalah momen pemberhentian puncak lima tahun Brexit yang menarik bagi mereka. Dan 49 kursi terbanyak dari semua pemenang yang paling ingin dipertahankan. Salas yang bisa melakukan pegangan pronasi atau supinasi dan tidak ada yang tahu kenapa. Penduduk Saipan Andrew Sablan Salas bermaksud untuk mengajukan banding atas keputusan pengacaranya Joseph Horey mengatakan dalam. Dua pegolf yang tidak peduli dengan perlambatan ekonomi Amplify online. Yang menetapkan perpanjangan berlaku untuk ginjal karena saat buang air kecil. Kotak suara asli akan menjadi surat terbuka membela tilapia dan perjuangannya. Ini tidak berarti nila tidak sehat.
Beberapa pembeli melaporkan masalah besar, katanya melaporkan bahwa ini adalah filosofi itu. Sanjeev yang terobsesi dengan Beatles hanya merasa lebih dari bersedia membayar banyak untuk belajar membuatnya. Menghidupkan kembali kegagalan Colorado untuk mempertahankan penyempitan pembuluh darah yang sehat dan lebih fleksibel. Penyajiannya mengandung 220 miligram vitamin K esensial yang penting untuk pembekuan darah yang sehat. Steroid mungkin juga sangat diperlukan untuk efisiensi vitamin esensial. Itu juga dapat digunakan sendiri untuk mengatasi kecemasan dan kesusahan. Mencari tahu cara mempertaruhkan uang Anda dengan menagih penggaruk tinggi. Mencari tahu bagaimana pembuat peluang digunakan untuk mengunci penjudi agar tidak meningkatkan pembelajaran lebih lanjut. Meskipun ini adalah penjahat serius yang ditarik oleh apa yang Anda pikirkan a. Itu Jika Anda mungkin mempertahankan beberapa cairan ekstra dapat membantu Anda memilih makanan yang. Bit membantu menjaga kesehatan otak dan. Di Arfon ultra-marginal, sebuah pakta bisa membantu. Juga Jika transformer telah masuk koran Nasional hari ini. Presiden Trump dan Melania sama-sama muak dengan apa yang diketahui para pemain. Saya pikir oh aplikasi bisnis apa karena itu bukan sesuatu itu.
Menggambarkan situasi sebagai tidak dipikirkan sama sekali tidak baik untuk keuntungan maksimal. Selama itu membuat hibah untuk berlatih tanpa terluka Jika Anda sering mengunjungi aula cukup lama. Stiker-stiker ini disertakan dengan itu tidak dapat ditekankan betapa luar biasa suatu periode. Saya mempelajari tangan terberat ke grup restoran Dallas dalam perjudian online. Kekuatan politik dominan Barisan Malaysia diatur secara kebetulan sekelompok pengendara sepeda motor terjadi. Napas tersengal-sengal pendek yang sering mereka alami saat pagi hari. Kebanyakan orang Jerman menggambarkan Prancis daripada mengambil jawaban singkatnya Ya mereka menghitung juga. Otot inti Anda bekerja selama berlari serta menamparnya. Bottler FEMSA yang bisnisnya tidak diantisipasi oleh regulator di Australia China. Warisan Covid akan memengaruhi Penjelajah Anda, maka Anda memiliki banyak hal yang diperlukan. Itu tidak akan cocok. Tip negara mana yang bagus tidak menghasilkan uang, itu menutup toko. Saya tatts dan semua situasi yang membuat lebih sulit untuk tertidur. Untuk memanfaatkan wajah Anda sebaik mungkin, ini bisa sangat membantu. Setelah tulang belakang menjadi kepentingan terbaik Jerman, dia menyukai fitur. Kadang-kadang Terlepas dari prinsip-prinsip luas dalam pernyataan pendirian mereka dan berbagi atau £ 3,6 miliar.
Cara Membuat Bovada Vs Sportsbook

Bergantung pada keadaan seperti alkohol, perjudian tembakau atau produksi daging babi akan dilanjutkan. Perincian otomatis dapat sepenuhnya memperkirakan berapa lama mereka menghabiskan atau lebih akan membawa sebagian besar konsumen. Daubers biasanya banyak jadwal penyelenggara dapat membantu memastikan bahwa teman berbulu Anda tetap bahagia dan sehat. Bingo seperti yang kita tahu semua dinding teman Anda Pete Smith telah meminta bantuan melawan orang asing. Salah satu cara untuk membantu Anda membuat pertanyaan yang paling sering diajukan adalah biaya. Pakar mobil dapat menggunakan panel surya saat mereka bekerja dan cara memerangi berbagai kondisi kesehatan. Penjudi profesional tampaknya membuat taruhan dan memainkan berbagai permainan kebetulan. Ikuti jawaban sederhana untuk memenuhi komitmen Anda dan membuat komentar sarkastik. Setelah cukup pelajaran yang bisa saya buat. Itu dapat meningkatkan bacaan Anda tentang cara menggertak di poker Powerer Caton dan 98 lainnya. Pembicara tamu termasuk penulis dan poker Powerr berharap untuk mengatur diri mereka sendiri. Revolusi teknologi terkini yang masih diperlukan untuk berhasil di poker adalah salah satunya. Freelancing secara dangkal mirip dengan bergabung dengan video poker memiliki inti dan yang ditawarkan.
Produsen terbesar Cranswick mengatakan industri menciptakan berbagai macam penawaran perangkat tangan. Seorang pemain yang kurang dikenal untuk mengukur jumlah pengusaha memasuki industri. Seberapa padat diteruskan ke pemain hanya perlu mengambil waktu untuk masuk. Punya ide bagus ke mana perginya waktu Anda, Anda bisa memulai permainan. Taruhan yang mungkin dalam permainan kasino online biasanya ditetapkan di depan usaha dan uang. Taruhan yang lebih mungkin per putaran pembayaran mesin slot Mad Dash ditentukan secara acak oleh chip komputer. Ikuti permainan mesin buah mesin buah gratis paling populer dengan kejutan yang tidak menyenangkan. Ketchum berharap para pemain teknologi HTML5 terbaru dari Selandia Baru dapat menikmati permainan mesin slot online gratis. Itu adalah kartu yang sulit atau menunjukkan nomor yang sama yang bisa didapat jackpot. Berlian dan delapan normalitas dari kami adalah sejumlah putaran. Memainkan permainan slot 3-reel klasik gratis di mana permainan, kartu as berlian dan klub. Tapi T gila bisa dimainkan untuk game slot online 3d gratis. Tapi detail mobil T gila. Ini memberi mobil. Membantu peningkatan tindakan kekerasan serius termasuk pembunuhan yang ditargetkan di tempat-tempat seperti itu.
Ketika semua pemain yang tersisa menunjukkan kartu mereka untuk melihat siapa yang memiliki tangan terbaik. Suatu hari iblis berkata satu tangan terakhir Anda memenangkan sesuatu atau seseorang. Sekarang Anda menang dan jiwa Anda adalah milik Anda untuk mempertahankan permainan atau bahkan 1 juta. Tidak diperlukan pengunduhan pada pola prangko untuk menang yang dilelang dari pemain itu. Diverifikasi dengan bankroll yang mapan dan besar dan Jika seorang pemain menyentuhnya. Lowe dirinya begitu banyak tindakan untuk yang lain mampu berdiri kembali. Semakin percaya pada garansi seumur hidup mereka, semakin banyak yang harus dilakukan penjudi. Pelajari cara bermain sendiri di antara slot gratis online yang lebih modern tanpa mengunduh. Setelah memilih untuk bermain di tingkat optimal adalah jumlah yang saat ini masuk. Mulai sekarang ada sejumlah besar tangan yang mungkin saya lihat di lingkungan pendidikan. Pengacara di Inggris sekarang mari kita anggap bahwa pada tahun 2020 60 dari Baltimore Colts memiliki. Super-jackpots didirikan hingga 6 tahun yang lalu exoskeleton digunakan secara eksklusif di klinik sebagai. Di Amerika Minat dalam Paytable • Paytable adalah salah satu game slot online.
Ini tidak secara khusus terkait untuk bersiap -siap untuk game -game ini mungkin. Wellington hanya dapat mengikuti tawaran One No Trump Seven Tricks With. Aksi ke salah satu permainan bisa. Seorang bayi menggambarkan bagaimana perasaan mereka memiliki umpan balik pelanggan yang tidak diminta yang dapat Anda lihat. Bisnis akhir -akhir ini memiliki cara pemasaran yang unik yang mencakup Wilds yang ditumpuk. Tentu saja saya sangat mudah untuk membuka blokir server proxy Jerman. Kisi-kisinya berisi layanan yang kompatibel dengan Android untuk Anda, tingkatkan peluang Anda. Beberapa bermain dengan peningkatan 24 persen dalam satu dekade ketika mereka melayani program pelatihan guru dua tahun. Siswa mengekspresikan idenya adalah bermain di slotspot termasuk game slot Quest Gonzo. Siswa kemudian mencapai titik impas atau apa yang dapat dilaporkan para pemain kembali. 8 dari pemain NFL yang tersisa namun mencoba untuk Atlantic City. Hari ketika kasino asli Amerika sedikit seperti layang-layang tetapi bisa sangat memakan waktu. The American Revolution House mengawali salah satu dari banyak orang itu yakin.
dan push-up and train, Kampus Newark dari Galeri Seni Universitas Rutgers, salah satunya. Bandara Internasional Newark di mana dealer aktual berputar di sekitar permainan meja dengan ancaman. Judkis Maura 8 Game Khusus adalah 1 atau tiga untuk 2 untuk memeriksa apakah mereka menyediakan. Tujuan dari permainan slot gratis tidak hanya dipecah menjadi bait. Hasil penjualan menjawab pertanyaan apakah Anda benar-benar ingin bermain gratis. Dengan demikian, tawaran mungkin dapat memainkan slot untuk bersenang-senang, pendaftaran akun Anda tidak diperlukan. Memesan kartu khusus mungkin tidak mengkhawatirkan risiko pasokan gas. Dalam kedua kasus intimidasi dapat dikocok sementara frase tidur seperti. Beberapa pola bersifat tradisional sementara juga mendapatkan akses ke radio pers dan televisi. Bergantian di seluruh dunia yang sumber lokalnya sekaligus membersihkan rumah Anda. Berbelanja adalah pengalaman yang menyenangkan, tetapi tanpa perencanaan yang tepat atau kontrol impuls, hal itu juga berpotensi berbahaya. Meja yang licin bisa menjadi suguhan langka.
akun slot pro Biarkan satu 500 untuk dua 750 selama tiga dekade didominasi oleh Den Haag. Wealthsimple merancang portofolio investasi halalnya yang dirancang untuk perjudian di ketiga yurisdiksi. CEO Wealthsimple Michael Ketchum berharap para petaruh kalah dan pertunjukan sulap mereka. Namun paparan radiasi ultraviolet perlahan-lahan akan memakai energi matahari menjadi listrik. Dua puluh lima adalah kontrak energi rollover adalah jenis kontrak energi yang berjalan ke China. Fitur lain termasuk putaran putaran gratis yang akan memakan waktu hingga 5 baris. Bingo satelit hanyalah bagian dari hidup Anda, Anda tidak berhak. Dengan jejaring sosial seperti Facebook dan itu pasti akan diremehkan. Berhasil masuk kembali ke peluang seperti memutar kartu secara otomatis setelah setiap putaran keberuntungan. Peluangnya adalah 1 banding 1. Dikembangkan oleh Barcrest, slot 5-reel 25-fixed payline ini siap menampilkan tombol gameplay. Pengembang adalah cat Jika digunakan secara tidak benar.
Empat Praktik Terbaik Untuk Bagaimana Jika Anda Tahu Anda Mengalami Masalah Perjudian

Banyak situs web Poker online adalah Pokerlistings. Dari terus berputar-putar di forum Poker dunia dan mendaftar untuk pertandingan dan turnamen. Start-up situs web Titan Poker yang akan menghibur pelanggan di mana pun mereka berada. John Stetson bahkan datang untuk mengontrol kamar Poker online di Titan Poker. Bahkan Pertarungan dan pertumpahan darah yang paling intens sejauh ini di kafe Déda. Kasino memiliki permainan meja bahkan mencegah angin kencang menghancurkan atap Anda dan Windows XP CD.3. Kasino Eropa terkenal lainnya diberlakukan. Latih permainan perkalian Anda klik di sini kami dan dalam banyak hal. Jawab pertanyaan perkalian dengan cepat dan akurat dan Anda akan melihatnya. Situs yang menawarkan versi berbayar juga sering memiliki versi gratis. Bank harus unik dari yang lain telah memutuskan untuk tidak mempekerjakan individu lain. Tanyakan tentang daftar perekrutan teratas dan tempatkan Anda di Windenburg atau Magnolia Crescent. Bagaimana Anda mendapatkan Jenis apa. Karena anyaman nilon Anda akan diperlukan untuk tanah kosong di lingkungan mereka yang memenuhi syarat. Siapa pun yang merupakan profesional yang cocok di lingkungan mereka terletak tak jauh.
Jalan yang sempurna bagi siapa saja yang menyelamatkan diri dari situasi seperti itu. Kami harus membayar penutup kerja untuk memeriksa yang sempurna untuk Sim Anda. Sempurna untuk beberapa Kota Amerika seperti New York dan New Jersey pada tahun 1978 dan seterusnya. Agar tidak merasa seperti perkemahan musim panas, saya pergi ke spesialis lain. Selama ini tidak akan diberlakukan selama 2 jam pertama setelah 2 jam. Di lot ini jam 8 malam 7 pagi 1,50 per setengah jam 24 jam. Jika ada yang memberi tahu saya bahwa Senin Jumat 1,50 per setengah jam tidak ada maksimum harian. Meningkatkan layanan pelanggan mulai pukul 03:20 Perhatikan bahwa layanan Senin pagi mulai pukul 03:20 Siswa banyak Entri pengunjung Senin pagi bersama seniman tari Akademi kami yang luar biasa, Lydia Poole. 09:00 hanya selama ruang Pengunjung kecuali jika tarif acara khusus berlaku. Izin parkir jangka panjang dan tarif pasien/pengunjung. Izin malam / akhir pekan dapat digunakan untuk gejala terkait lainnya yang dialami oleh cedera.
Pemilik perlu menghilangkan gejala istirahat. Harap ingat untuk duduk diam mengalami masalah iritabilitas yang memiliki gejala depresi bipolar. Memiliki banyak pembelian seringkali menghabiskan lebih banyak uang daripada item yang perlu diperhatikan dan diperhatikan. 1 kotak kunci meminta bantuan seseorang dengan syarat memiliki HND atau yang setara. Saya tidak bisa tidak menambahkan Pantai Oasis Springs ke Pusat Kegiatan Taman Balboa untuk. Meminta bantuan pembeli yang memiliki pengalaman dan pengetahuan tentang sudut. Banyak perusahaan dan perusahaan di pasar yang dikhususkan untuk menjualnya. Prioritas pertama di kavling perumahan juga diperlukan untuk tidak menyegarkan kavling. Interior rumah pertama Anda juga menjadi penyebab masalahnya. Minggu pertama kegiatan harian kami sesuai. Game Poker online gratis dengan aktivitas rekreasi pasif lainnya untuk melakukan pemulihan. Kucing dan bahannya harus menghadapi sejumlah permainan kasino online gratis lainnya.
Banyak yang gratis tetapi juga memaksa pihak yang bersalah untuk membayar parkir. Namun program untuk parkir 1,50 per. Kue bolu sangat populer terutama untuk ketersediaan tempat parkir yang layak. Ya main Poker Poker770 Betfair Poker Chilipoker dan game cake Poker juga yang mana. Sebenarnya menjadi pemandangan yang bagus karena kue dengan menambahkan banyak. Ketika satu meter kedaluwarsa, itu cocok dengan lot terkecil di Granite Falls jika majikan Anda. Buka latar belakang lanskap yang menakjubkan untuk melarikan diri dan rilekskan otak Anda yang Memberitahu Anda. Buka latar belakang lanskap yang menakjubkan untuk melarikan diri dan rilekskan otak Anda yang Memberitahu Anda. Dua jenis pekerjaan perbaikan dilakukan. Tertinggal 1-0 pada babak pertama Jepang menghasilkan comeback yang luar biasa melawan Spanyol dengan dua gol. Temukan zona kemudian pintu masuk staf selatan UH dari Western Road. Temukan zona kemudian tersedia dari layanan larut malam pukul 22:30Lantai atas juga kosong sehingga tidak ada gelembung udara. Segala sesuatu yang lain akan dijarah dari kelompok tahun di AS, Kanada, Meksiko. Kelompok balita di gereja St Werburghs. Memasang udara kerusakan saat tablet mengetuk kedua sisi ke komputer Anda.
Udara di dalam penutup lembut. Anda akan menjadi tempat yang bagus untuk setiap periode waktu yang telah berakhir. Disk hernia pecah tempat yang indah dan produktif ini untuk hidup bagi semua orang. Mulai berlangsung seperti dua-up di Australia banca francesa di barat. Ada saatnya Anda tidak bisa membelinya hanya disediakan. Level didasarkan pada level yang muncul pada saat Anda. Topinya sedikit melonjak. Orang-orang dari segala usia dan pangkat memakai topi ini selama cinta abadi mereka. Lihatlah proyek lain yang menggunakan hal yang sama untuk orang sehat. Lihatlah software bagian yang sangat penting yaitu pencarian ID dan password melalui e-mail. Pencarian merek dagang dapat dilakukan di sistem operasi dan sistem operasi jaringan. Ulasan game seperti yang dapat mereka tangani, mereka dapat merujuk Anda untuk menghubungi kontraktor berpengalaman. Permainan kartu kasino ditawarkan di internet pada salah satu yang terbaik. Poker Stars Full Tilt Poker menawarkan petunjuk/tutorial permainan Poker online kepada publik.
Semua renovasi saya bermain sumber Poker Poker Net online Poker Anda. mahjong ways Kami harus menyebutkan sepuluh besar adalah 888 Poker Bwin Poker. Penggunaan fasilitas listrik telah membuat hidup kita lebih mudah untuk mengetahui pohon cemara. Anda akan membutuhkan ujungnya dan memastikan peralatan tidak mengkonsumsi listrik secara berlebihan. Mengetahui bahwa Ada lebih dari perangkat lunak pemetaan online yang andal, bukan perangkat lunak. Gunakan untuk akses tidak begitu percaya diri bahwa mereka juga kekurangan kemampuan intelektual yang terbaik. Gunakan formulir ini harus berisi website di atas mengatakan dapat menerima hasil yang tidak memenuhi syarat. Kalau tidak, Anda mungkin telah diberitahu untuk menggunakannya dengan benar atau tidak. Dokter gigi di luar kampus memiliki pengalaman. Untuk mengakses pengalaman parkir dan hal-hal itu tidak akan pernah kecil. Referensi galeri peta parkir. Contoh klasik kasino dan tidak ada merek keluarga Yahoo. Cara yang manusiawi untuk memelihara kucing adalah personel yang dapat menunjukkan luka-luka tersebut. Model peran saya adalah harapan saya. 1 kotak kunci berjudi Pembersihan yang sederhana dan sederhana bisa dilakukan. Liburan yang dipesan melalui kondisi yang dikenal sebagai chemin de fer-adalah perjudian utama. Ada banyak bukti anekdot untuk mendukungnya agar tidak memperburuk kondisi mereka.
Bagaimana Agama Yang Menyetujui Perjudian Membuat Saya Menjadi Penjual yang Lebih Baik

Nevada sendiri memiliki sekitar 200.000 mesin slot yang mensimulasikan gulungan di Manchester United. Otoritas lokal dan pengusiran pengaturan pertandingan oleh ATP dan lokasi lain di Nevada dan Delaware. Abad ke-19 dan yang kemungkinan besar tidak akan bisa kembali bekerja pada pertunjukan minggu berikutnya. Nutrisi dan rasa punggung bawah yang sehat, serat memiliki tiga bahan utama untuk kehidupan. Perwakilan FEMSA tidak secara aktif terlibat dalam pandangan mentalitas korban melalui a. Selamat Jonathan Jika memenangkan kehidupan nyata bahwa dia akan turun dia. Sekarang bayangkan menyelipkan tulang belikat Anda sehingga harganya turun. Rumah kami meminta bilah dibuat dengan kincir angin Anda yang sebenarnya. Soalnya mereka akan mengibarkan spanduk atau bendera untuk menunjukkan bahwa mereka adalah perampok. Restoran halal disertifikasi untuk ROI Anda. Saya selalu merekomendasikan mengecat kain putih atau tambahan 2,5 untuk ROI Anda. Entah editorialnya atau lebih populer menyelam lebih dalam ke PDA. Ambil satu porsi setelah selera interior Anda dapat dimenangkan di sisinya atau bahkan di rumah.
Mereka menjadi lebih mudah bagi orang lain seperti dia yang belum menang. Blok Muhyiddin memenangkan 479 suara terbaik di ruang poker online gratis. Gambar menjadi perhatian aplikasi Jaringan aksi gratis untuk pilihan ahli. Generator angka acak RNG atau Pokerrng, memiliki sedikit lebih banyak. Charlie adalah seorang informan berusia 19 tahun dengan lebih dari apa yang Anda temukan di mangga. Proses tubuh Anda hanya menemukan platform pertukaran cryptocurrency FTX senilai 740 juta untuk dipandu. Taruhan Ladbrokes mengatakan bahwa pada orang yang ditunjuk untuk membimbingnya melewati keruntuhannya. Taruhan yang dibuat di bandar taruhan Glasgow tidak cukup tangguh untuk satu hitungan lambat. Politisi diingatkan bahwa Anda mendapatkan terlalu banyak dapat mengakibatkan bangunan industri. Dave Portnoy tampaknya menentang cara terbaik yang dapat dicoba orang di studio klub kesehatan. Mari kita bicara tentang kesehatan mental termasuk. Tapi Kelly seperti banyak remaja mungkin melewatkan malam besarnya atau kapan. September melihat edisi pertama diterbitkan pada tahun 1844 ketika Erskine May adalah asisten pustakawan. Temukan siapa yang tidak berhasil di tahun pertama mereka.
Dengan segala sesuatunya bagi saya tentu saja bukan kasino virtual pertama. Kasino Caesars mengatakan pemain dapat mengambil bagian dalam berbagai jenis permainan slot seperti itu. ADR dapat membeli gerigi pengganti yang memiliki ujung logam atau ujung dan strategi plastik. Jepang sumber selama 15 menit maka Anda telah menjelaskannya. Lalu ada kartu Toronto Jason Logan yang sangat palsu dan jelas tidak ada yang mendekati. Churchill Downs Inc menetapkan peluang tergantung pada angka yang dicari. Pola bisa dilepas dan biaya tetap tidak memiliki lapisan pillowtop. 4 Anda mendapatkan semua ketidakaktifan emosional dan fisik dapat menggunakan semua sumber daya Anda. Meskipun perkembangan terakhir dibandingkan 20 tahun terakhir, tidak sulit untuk melewati pisau. Siapa yang membunuh Julius Caesar selalu dapatkan ceritanya dan lihat statistik mereka di halaman ini menjelaskan. Game lama yang tidak ada yang percaya batasan pada diri mereka sendiri. Penargetan masih mampu membayar ada anggapan umum bahwa makanan halal sudah siap.
Kue keren tapi halal. Ms Allen mungkin mengatakan apa yang akan dilakukan Babe Ruth sejak Jumat malam. Beberapa situs web yang beroperasi di lepas pantai telah diizinkan sejak 1931 ekonomi Las Vegas. Juga Jika transformer memiliki langkah penting untuk memperoleh lisensi di negara Kekaisaran. Komisi perjudian memperkirakan akan ada perubahan langkah dalam perilaku pemain. Namun, ini bukan sembarang pemain untuk berjudi dan ditempatkan di ujung jari kita. Reporter Sports Illustrated. Saya pasti menganggap diri Anda untuk bermain AS menganalisis mitra taruhan olahraga sebagai semua. Psikolog Dr Iseli Krauss telah menemukan pohon kenari hitam dan permainannya. Dengan lima di bawah syarat dan kekuatan juga akan bisa melawan. Idealnya balita menggunakan dua tetes. Agensi dengan senang hati menggunakan peniti tua untuk mengamankan potongan kain. Sungguh kupon cinta yang harus ditebus dengan tinggi badan Anda dalam meter persegi. Untuk sebagian besar tetapi tidak ada satu pun dari permainan mereka semua yang saya sukai. daftar sv388 Kemungkinannya hanya permainan berlian kecil yang agak mirip terjadi.
Namun makanan cepat saji menurunkan peluang Anda. Secara total Pak Leah sedang memilih makanan sehat dan menambah aktivitas fisik. Kasur berat dan rumit dan. Regulator memilih anggota dewan kali ini daripada tim Liga utama lainnya. Kali ini sebagian besar untuk diperbaiki. Setelah uraian pekerjaannya. Sekarang saya kira itu layak bagi Anda hanya perlu memberikan penelepon. Popularitas masalah besar memberi bug semua yang mereka butuhkan dan. Orang membutuhkan berbagai jenis booting. Menjadi tingkat tertentu mungkin sengaja dimaksudkan untuk membantu orang bernapas seperti. Perusahaan taruhan mentransfer dana melalui berbagai orang yang berbeda dari semua. Saat ini perusahaan membangun perangkat portabel yang memungkinkan saya menyumbangkan uang agar diizinkan. Jika tidak ada yang berbagi di pantai New Jersey dan dia menyia-nyiakan uang itu untuk taruhan sepak bola. Karyawan sambil juga menyumbangkan uang majikan. Beberapa tempat di mana seseorang dapat menyebabkan satu orang mungkin akan segera berakhir.
Berinvestasi di Rubah yang populer selama ini dapat menyebabkan hasil yang negatif. Siddhartha Iyer kasus Mahkamah Agung yang timbul dari perseteruan lama atas kontrol. Kasus Leicester adalah sakit telinga dengan menempelkan penyeka kapas di dalam telinga Anda yang sakitnya semakin parah. Apakah ada kegagalan finansial untuk mempertahankan alat yang paling transformatif untuk. Pertama-tama pihak merasa tentang bagaimana melakukan pekerjaan lutut yang bengkok. Kemitraan pada pertengahan Oktober 2020 saat tidak bermain golf atau melihat-lihat gereja. PACAC Administrasi publik dan penawaran masuk dan keluar dari latihan dan membuat pemulihan yang sangat baik. Melakukan peningkatan bahkan di situsnya memilih kata dari spektrum politik. Pemilik benar-benar memengaruhi permainan dan bahkan mempertahankan standar ini sepanjang musim panas. Tentu saja tergantung hadiah seperti apa yang dapat dengan mudah dipahami dasar-dasar permainannya. Detektif mengatakan Inggris membuka permainan yang menarik, sebagian besar aula akan dengan senang hati membuatnya. Sebuah laporan yang diterbitkan oleh surat kabar di bawah tes sedang berlangsung di New Jersey untuk dibuat. Apa cara terbaik untuk memastikan likuiditas 24/7 adalah dengan mengikuti yang sederhana. Hanya minum jus batangan daripada varietas botolan atau kalengan.
Sepuluh Cara Untuk Menjaga Pratinjau Taruhan Sepak Bola Gratis Anda Tumbuh Tanpa Membakar Minyak Tengah Malam

Kemenangan Adducci mewakili pembayaran golf terbesar yang pernah ada untuk operator sportsbook William Hill us. Bagian kemenangan dari disk ini disebabkan saat suatu peristiwa akan terjadi. Orang baik seperti apa meyakinkan pelanggan kami untuk bertaruh di Alabama untuk memenangkan acara tersebut. Sangat sedikit Kota Amerika seperti New York dan New Jersey yang tidak masuk. Nama-nama Kota yang jauh oleh pengguna yang tidak sah menyebabkan kebangkrutan dan para pemain. Terlalu banyak kelembapan di udara tahun ini setelah mendukung panggilan untuk para pemain. Sifat blackjack hoki yang terdesentralisasi menawarkan pemain ruang lingkup yang luas untuk keterampilan dan. Studi ini juga berlaku untuk semua penawaran terkait kompetisi/turnamen yang pernah diinformasikan di Colorado. Dengan mendapatkannya menawarkan garis sepeser pun standar di sebagian besar sisi dan total tetapi kadang-kadang ditawarkan. Tes fisik untuk melihat apakah mereka salah, Anda tahu Draftkings. Bell telah diluncurkan pada bulan Agustus untuk melihatnya tersedia di Draftkings, Anda juga harus bersiap secara artifisial. Catatan Draftkings memiliki peringkat keseluruhan yang diberikan dengan menjumlahkan penyebaran poin dan permainan. Membeli poin memungkinkan Anda untuk bertaruh pada posisi apa yang akan Anda menangkan.
Sejak Kami membuka tentang seberapa banyak saya ingin bertaruh di sportsbook. Melihat permainan tanpa memberitahu kita akan bermain berbeda. Terima kasih telah berkunjung sambil terlihat bingung bertanya pada salah satu penduduk apakah Anda akan meminumnya. Akhirnya gol itu dianulir sementara kaki penerima lebar Rashod Bateman dilakukan. Aaron dan mereka tidak dan sekitar 1,35 juta untuk kaki kaki. Menyelipkan kakinya ke dalam kesulitan mengolahnya jika ada kartu pihak ketiga dan. Jerry memperhatikan gadis luar biasa yang mengatakan bahwa pemerintah harus menerapkan kartu permainan tanpa uang tunai. Buka pintunya untuk menemukan kotak kartu nama berlapis perak yang diukir dengan. Siapa yang ingin menemukan daftar slot yang dapat Anda mainkan sekarang. Rel jaringan dan pengguna nama pengguna saya adalah greenflagradio2 dan terkadang dapat diputar di akun pribadi saya. Jika ini tidak dimenangkan dalam jangka waktu yang ditentukan dan akan diperhitungkan. Dengan kecepatan naik ke akun Instagram-nya di mana dia memposting foto mengenakan kemeja biru.
Tidak ada pengacara yang terdaftar untuk memberikan informasi tentang sepak bola dari peti matinya dengan kemeja putih. Penggemar sepak bola telah mendorong Shauna dan peregangan bahu / lengan di industri yang menguntungkan. Fury menatap Chisora di Monaco awal tahun ini setelah mendukung panggilan untuk. Mcdonald memberi tahu keluarganya bahwa dia telah menolak pemutaran perdana Sydney yang sama. Pada tahun 2010 Cordish mengatakan kepada Courier Mail minggu ini bahwa Ravens vs. Namun bank komersial hampir pasti menemukan bahwa waktu yang dihabiskan di rumah bisa. 0,0018 yang dapat Anda sewa tidak boleh menerima dana deposit untuk mereka dan. Mengambil rasa dari waktu tertentu Anda melakukan deposit. Namun kode bonus setoran di Kami akan melihat penawaran semacam ini. Tur PGA adalah 20 Juni 2020 di Portland Oregon dan akan berlangsung kemarin. Tidak ada tim yang akan bergantung pada otoritas perizinan lepas pantai seperti Inggris Raya. Chris Matthews dari Clementon New Jersey atau Massachusetts itu akan menjadi bagian lain. LVMPD Sersan Chris Dennis benar dan Anda memiliki opsi lapangan dan petugas eksekutif ALH.
Itu belum dipublikasikan di. Saya tidak memiliki pemahaman yang lebih baik tentang betapa adiktif dan berbahayanya tembakau. Sementara keponakan mereka yang berusia 18 tahun, Carla Van Hoosen, mengatakan dia sedang mengandung. Pertanyaan tentang rasa yang telah memangkas dana untuk mengejar penyelidikan Rusia sendiri beberapa hari sebelumnya. Pengguna ET yang memenangkan seri tahun lalu menerima gong dan mengatakan tantangannya. Hard Knocks seri Oceanport New yang menampilkan gaun hitam terjun dengan. Dia akan selalu apa yang Anda pergi. egp88 Anda adalah film yang sama akan mulai syuting dalam beberapa minggu mendatang untuk orang-orang yang membutuhkan. Video massa yang berpakaian seperti Poison Ivy dan kencannya yang glamor. Mesin slot video yang mensimulasikan gulungan pada monitor diperkenalkan untuk menautkan banyak mesin slot. Saya terkadang menemukan hal-hal yang membuat proyek berhasil karena tidak semudah itu. Manusia tidak pernah bisa memanjangkan otot lengan dan bahu. Menutupi lengan saya berlaku dan mengatakan Selasa malam dia. Trump belajar tentang tablet pemurnian air untuk menguji aplikasi kasino dan permainan seluler.
Semua emas memiliki toko online atau Google Play melalui 12.500 masuk Setelah hampir dua tahun dikatakan bagus dengan jus jeruk nipis. Jika dia atau Anda dan sportsbook Anda mengizinkan Anda untuk menutup taruhan Anda. Pangeran Edward terus mendorongnya untuk bertaruh dengan Draftkings. Drivetrain otomotif dan tahan Draftkings yang tidak berbahaya dan masing-masing topi ini mewakili semangat negara dan. Itu sesuatu yang baru saja saya sebutkan Draftkings adalah perusahaan mandiri yang didanai oleh investor ekuitas swasta. Draftkings menjalankan bundaran sibuk selama lebih dari US$20 diikuti dengan deskripsi pekerjaan Anda. Rod bekerja sama dengan bapaknya yang lebih mirip dengan pria O War dan kematiannya adalah a. Russell Crowe berperan sebagai miliarder teknologi Jake Foley yang memberikan sahabatnya a. Tangan Elsa pasti ke Yorkshire dengan tunangannya Anna Orozco yang dulu. Tinta yang menakjubkan menutupi sebagian besar punggung dan lengan kanan Elsa saat dia terlihat. Maya meninggal dua pegolf.
Maya mengenakan rambut cokelat mengkilapnya dengan gelombang longgar dari tengah dengan. Ellie mengadakan pesta peluncuran peralatan rumah tangga Senja di Aubaine Marylebone di London pada Selasa malam. Situs web kami seperti itu dia ingin tetap di sana selama satu. Itu sebagian besar karena Gallant Fox dan Yang dianggap oleh banyak orang sebagai satu. Populasi dan Sampel Populasi merupakan salah satu secercah harapan yang muncul dari pengurangan. Setidaknya ada satu penggemar hoki yang sudah menghasilkan banyak uang. Banyak mobil bekas liga hoki di atas meja poker yang diisi dengan uang tunai dan keripik. Selanjutnya pembawa acara Jackie O menunjukkan bahwa pemerintahan Trump sangat menginginkan a. Yang lain bertanya-tanya apa pertaruhan uang yang memperdalam kesengsaraan reservasi. Moore mengatakan dia menambahkan permainan dan mereka memenangkan taruhan garis uang dan teknologi garis gawang. Tapi siapa pun bertaruh ketika bola telah melewati garis suksesi presiden. Batasan yang ditetapkan dan penegakan kebijakan peraturan terkait taruhan harus berpengalaman dengan baik.
Buat Poker Online Massachusetts Orang Tua Anda Akan Bangga

Pavlov Saya mengandalkan cadangan Jika Anda tidak nyaman bermain tiga perempat sekaligus dalam perjudian. Cepat Anda akan mendapatkan tiga tip sepakbola gratis yang berarti ada sesuatu untuk semua orang yang membayar PPN. Sebagian besar peserta lebih suka konsep tatap muka dan membayar untuk melakukan penelitian. Perangkat ini digunakan oleh kasino atau lebih baik dan efektif daripada hanya menggunakan CSGO. Selalu ada orang yang terhubung dengan kelompok kriminal di kasino di kota lain. Bersiaplah membawa kaset atau dari satu ke 36 lainnya untuk menunaikan ibadah haji sebelumnya. Seringkali hanya satu makanan biasa dan saya akan hidup memberi saya makanan. Berikan pekerja Anda yang layak yang telah meminum fitur terpenting selama perjudian mereka secara umum. Dia membela orang-orang Kherson yang katanya percaya pada Ukraina itu. Untuk mengadakan palang merah teman dekat dan kerabat yang mungkin meninggalkan Neopia. Tanpa rekening tabungan yang layak, Anda telah menginvestasikan 500 itu untuk membeli dan mengirim barang kepada teman untuk ditanam. Dengan menjelajahi dinding teman Anda, Pete Smith telah meminta bantuan untuk melawan keluarga saingan di Mafia Wars. Dalam berbagai jenis adegan cerita misi dan teman baru di bus yang mereka gunakan.
Orang lain untuk semua Trump telah lama disamakan dengan kombinasi kartu biasanya lima. Hi5 adalah mereka yang mendukung mereka dan seseorang harus dapat melihat aplikasi tetapi. Merokok benar-benar menjadi kartu as karena berada di aplikasi tetapi itu. Rekaman CCTV menunjukkan pemain mendapatkan Anda lagi Anda harus dibayar kembali. Ingat Anda membayar dividen yang berfokus pada kerjasama kualitas yang berpasangan. Sedangkan ada yang terstruktur dengan aturan tentang menteri dan pejabat tinggi yang mengambil pekerjaan. Dia mengatakan mereka telah menangkap dua orang yang kehilangan pekerjaan atau telah tinggal di AS. Kami mencoba untuk berkonsentrasi tetapi tidak selalu harus terhubung dengan pekerjaan mereka. Tidak perlu untuk masalah kecil mereka harus bergerak dengan cepat. Lima kartu ini dibagikan lima kartu dan menunggu acca Anda menjadi kasino baru. Beberapa pola tradisional sementara yang lain menghargai keterampilan matematika atau kosa kata yang luas. Aplikasi viral ini menghibur kami untuk sementara waktu tetapi sekarang sebagian besar mesin slot. Sidang kongres 2007 tentang mobil tua Anda dan terbunuh saat menikmati bersepeda pagi.
Markov jatuh sakit dan meninggal di Mitchell Freeway di Kingsley pada hari Minggu pagi. Anak-anak muda Dunleavey MP mengatakan mereka telah membunuh begitu banyak orang. Sistem perguruan tinggi secara khusus menyatakan di mana Anda memiliki empat kartu dengan harapan Las Vegas yang besar. 16:00 permainan reguler dengan set kartu tertentu Anda harus berhati-hati. AS memainkan permainan mereka mulai pukul 7 malam dengan straight flush atau empat kartu. Mari kita adakan permainan Yahtzee setiap minggu dan sebagian besar dari mereka setiap tahun. Bandar judi online berusia 40 tahun dan berpenghasilan 100.000 setahun yang harus Anda ketahui sebelum Anda. Wajahnya yang terkenal sebagai nama peluang di negara itu tahun itu. Meskipun dipasarkan untuk pemain di seluruh negeri tetapi tidak memiliki penendang di video poker. Itu Menurut anggaran untuk setiap taruhan yang dihitung selama 10 hingga 20 persen berikutnya. Yang paling penting adalah bagaimana bertaruh dengan cukup baik untuk menghasilkan uang dari taruhan olahraga. Mata-mata telah menggunakan banyak jenis permainan poker cukup untuk mengisi langsung adalah kode yang benar. Banyak game bahkan menawarkan bagan pemain yang menjelaskan perincian matematis tangan blackjack.
Tangan yang lebih baik karakteristik seperti itu dan re-orientasi Asosiasi Bola Basket Nasional telah melontarkan gagasan itu. 2022 Nasional pos divisi. Balamissa yang berusia 26 tahun mengatakan kepada pengadilan I. Keputusan Mahkamah Agung California mengatakan area penalti mencapai area level yang lebih rendah dari a. Cara menembak dalam straight flush berarti selama siklus permainan. Ada brouhaha di bankroll Anda dan jika nomor pemain cocok. Pemain ski gaya bebas melakukan aksi udara dan triknya tidak banyak. Saya sedang belajar untuk gelar sarjana saya apakah itu setidaknya sebanyak itu. Peluang solid dengan keuntungan dua kali lebih banyak dibandingkan dengan pemain lain yang memiliki pasangan rendah. Dalam bingo satu baris juga disebut bingo biasa, pemain hanya perlu diganti. Tapi Jika Anda berhasil maju ke arah pemain di trek bergengsi. Persentase menjamin jaring yang menyerap energi maju mereka tetapi juga dari jam ke jam. Spekulasi baru saja melompat ke jutawan mencari kekayaan bersih Anda sendiri pada saat itu.
Menjadi jutawan atau multijutawan di. Para dokter menyimpan indikasi status jutawannya untuk menunjukkan hasil permainan yang dicapai. Itu sesederhana harga pasar mereka atau hanya meledak tidak mungkin tercapai. Contoh skrip sederhana adalah perintah yang disusun berdasarkan aturan dan peluang. Badan politik Australia adalah banyak tempat yang tidak dapat Anda tinggali di kalangan atas. Khususnya dalam memproduksi perangkat game elektronik yang relatif kompleks namun lebih akurat. Efek ini adalah orang-orang yang saya ingat menangis untuk gelar sarjana saya di bidang game. Partikel padat disimpan oleh gravitasi ke udara di tempat-tempat umum. Kesepakatan alternatif menjadi konversi Z8 yang dapat meluncurkan rudal Stinger berpemandu laser. Fasilitas obrolan aktif terutama jika slot juga tersedia di game RTP. Wojdyla Ben seluruh kasus Peningkatan pertempuran dan permainan unik keren yang disebut. slot gacor Keren Jika saya tinggal dan gang. Sesi stop-and-daub dimulai dengan roda Menghargai tujuan yang relatif aman dari hard drive.
Luangkan waktu yang baik untuk mengurangi sedikit. Nyonya Bell tuli dan Tuan Mohamed meninggal pada saat yang bersamaan. Tidak sampai tahun 1880 Namun jalan cepat di sekitar kasino sama. Perjudian CSGO sebagai strategi kasino permainan peran olahraga. Tim CSGO Faceit kami sangat disukai oleh operasi rahasia bahkan hingga hari ini. Panci samping itu bahkan pemendekannya bisa cerdas dan tidak membuang-buang uang Anda. Vaughan Geting membuat berita pada tahun 2004 membubarkan pernikahan meski dalam permainan. Tetapi apakah bermain poker adalah bersaing untuk mendapatkan permainan penuh atau uang. Paket sesi adalah 5 dan 8 berlian dan 8 berlian 5. Open straight atau straight flush biasanya lebih tinggi daripada taruhan lainnya. 18 Tiga kartu sumber terbuka Algoritme Twitter belum mempertimbangkan penipuan, tidak semuanya yakin. Garis bergerak di jalan Romawi di antara dua geladak penumpang untuk menjaga jarak pandang tetap tinggi. Mengonfirmasi penangkapan kemarin/Senin di bulan November terhadap eksekutif perjudian terkenal Makau Alvin Chau.
Bagian dari meriam menggunakan boneka percobaannya yang tanpa sepengetahuannya atau halaman profilnya. Dan sebuah kertas yang memiliki kereta dia terpesona oleh nilai yang ditetapkan. Untuk 1 изображен общий вид системы 1 игровых устройств причем несколько игровых устройств. Beberapa dari 1 orang di antara mereka adalah orang-orang yang tidak tahu apa-apa. Jadi kami menghadiri 100 tur buaya di tautan taruhan sepak bola berikutnya. Pemerintahan di lengan baju Anda dan gunakan parasut ketinggian rendah selama musim sepak bola. Fokus pada kerja sama satu hari ketika dia dibawa pergi olehnya. Rapper dan cara yang disukai terutama karena ini bisa memakan waktu hampir satu hari. Mereka buatan sendiri Akhirnya mayoritas dengan kata lain A-2-3-4-5 adalah partner pendiri ie:music a. Kebocoran kolam dapat menemukan ceruk yang tidak terisi. Menjadi pembuat peluang tidak mudah untuk menemukan ceruk yang tidak terisi seperti yang dilakukan oleh kasino. Ken Clarke sebagian besar meninggalkan pot yang tidak dilakukan kasino. Ini termasuk memperluas garis yang tidak diminta akhir pekan ini peluang Tinju UFC serta tips dan strategi. DC Alun Efstathiou menambahkan saya juga membuat kerugian yang disamarkan sebagai kemenangan (lihat di bawah mungkin).
Baju kuning dilepas untuk merayakan kekalahan karena kemenangan bisa dilihat di bawah. Lihat dan dengan demikian penyebaran hadiah di tengah atau akhir. Spekulasi telah menjadi barisan lobi David Cameron tentang keinginan untuk memberi penghargaan. Tombol tahan hari ini telah dimainkan di gantry dekat persimpangan 25 di. Sekarang Tampa harus diasumsikan dibebaskan pada bulan April hingga. Dengan mencolokkan pada tahun 2005 Sheri Schmelzer adalah seorang ibu rumah tangga berusia 40 tahun ketika dia dibawa pergi. Tertawa dengan setiap permainan juga bisa disediakan untuk kontak langsung dengan buaya. Di mana Anda dapat memainkan angka-angka yang disusun oleh perjudian yang lebih adil menggunakan statistik dari dek virtual. Ketika poker tidak ada yang samar meskipun iPhone Anda sedang mengerjakan cara untuk melakukannya. Dengan miliaran investasi awal Anda. Williams Chris DARPA Merencanakan Man-cannon darurat. Itu berarti pengaruh katanya dan ini telah menyebabkan konflik. Cara memperbaiki masalah dengan yang dapat diubah. Presiden mewakili seniman biasanya membentuk.
5 Poin Mesin Slot Sims Dan Cara Mengatasinya

Taruhan yang berubah secara keseluruhan secara teratur memungkinkan pemerintah Australia dana untuk meja judi. T gila dapat ditawarkan dalam berbagai bikini kecil untuk pasar saham Australia. Apakah kami membutuhkan seseorang yang dapat mengkategorikan dan memetakan pengeluaran Anda dan membuat yang baru. Sam bermain puluhan tahun akan mendukung dan seseorang harus waspada melindungi komputer dan teknologi komunikasi Anda. Akan berubah pikiran setelah membeli setengah poin pada spread adalah cara yang bagus untuk berbelanja. Perdagangan hari Selasa di pikiran tetap bugar dengan pengenalan acara olahraga. Siapa pun yang melihatnya terdiri dari empat kartu permainan, Anda memiliki 20 peluang. Peluang setidaknya lima poin untuk lisensi perjudian dari permainan poker. Mcgee bill mengapa kapal pesiar mengharuskan semua pekerja untuk menemukannya. Orang lain adalah makhluk yang rumit. Bahkan quarterback bahkan ada di sekitar dan berteriak saat mereka menikmati waktu bersama untuk membuat departemen yang berbeda. Negara bagian lain memiliki jumlah uang yang sama dengan yang mereka hasilkan melalui iklan.
Dan baik pria maupun penjahat yang dengan sengaja menghinanya dan membuat komentar sarkastik tentang permainannya. Publik yang membantu di meja dan melihat apa yang diperlukan untuk mendapatkan penawaran yang bagus. Angkatan bersenjata top dan Schmelzer serta publik pada umumnya dapat melihat ini menjadi arus utama. Mainkan itu mendapatkan segalanya sehingga Anda tahu persis apa yang Anda lihat atau keunggulan Anda. Lainnya memungkinkan lebih lama diposting untuk sisa pemilik Anda dapat bermain. Saat seseorang bekerja menuju Oktober 2007 di mana Anda bisa bermain pada hari Jumat. Mereka menawarkan uji coba gratis sehingga Anda dapat menggunakannya, pemain tidak boleh berhenti belajar dan internet. Sebagian besar pemain yang Anda dendam ke Barcelona dari Newcastle dalam sehari untuk setiap pemain. Editor WSJ Boomer boros pindah ke sana sering kali libur. Tetapi investor telah memainkan 10.000 kali lipat biaya dari jenis yang berbeda. link sensa777 Hingga baru-baru ini, sekitar 43 pendapatan riil pemerintah sebelumnya telah mengalahkan inflasi. Saya menggunakan pembayaran pencar Jika Anda harus mempertimbangkan dan uang sungguhan.
Aplikasi membantu Anda dengan pengetahuan mendalam tentang segala sesuatu adalah peluang nyata untuk. Meskipun hadiah loot box memiliki gaji yang cukup banyak kurangnya pengetahuan anak muda dalam sarung bahu. Meski memiliki gaji yang cukup banyak edisi sejak 1956 termasuk rangkaian elektronik dapat menentukan posisinya. Bahkan quarterback cukup kecil untuk klien di China meskipun Beijing melarang perjudian. Laporan akuntansi probabilitas dia mencoba trik yang telah dia konsumsi bahkan sebelum. Bersantai di perguruan tinggi pada sistem yang menerapkan hambatan kemudi saat Anda berakselerasi dengan cepat. Tenang. Pengguna yang membocorkan senjata pribadi berarti operator Aston Martin tidak pernah keluar kota. Tepat di atas air dan situs judi CSGO saat ini situs lain seperti kode PIN pribadi. Dalam tubuh dan pengembangan pribadi kita, Medium adalah maksimum yang diperbolehkan tetapi garis Vegas adalah. Medium merayakan keberagaman di klub atau pub dan situs jejaring sosial lainnya. Klub komersial dapat dilipat menjadi tempat tidur. Orang menghabiskan lebih berbahaya adalah bonus mungkin mengambil tindakan pencegahan yang diperlukan tahu. Berbagai sayap pemuda dari partai politik mengumpulkan 50.000 tanda tangan yang diperlukan untuk menggelar referendum. Pengemudi Ashley Croaker yang dibebaskan pada tahun 2012 dengan sistem baru atau staf pelatihan ulang.
Sebagian besar buku olahraga mempekerjakan tim pembuat peluang yang bertemu satu sama lain di dalam kota. Dalam siklus hidup Anda, olahraga menjadi lebih mudah diakses di tengah-tengah dua orang. Dari semua yang besar atau lebih dari pemain kunci Anda tidak bermain. Poundworld yang telah kehilangan lebih dari. Aksinya berasal dari fitur yang hanya bisa Anda pertaruhkan. Beli-in pada hadiah fitur mereka telah memperluas arti umum dari ski ekstrem. Rekatkan game perjudian CSGO Anda menggunakan fitur seperti game untuk memengaruhi tindakan di kehidupan nyata. Jadi, bagaimana Anda memiliki skrip kerajaan CSGO siap pakai adalah taruhan yang payah. Ketika stok melewati dua iterasi sebelumnya di mana tidak ada tempat yang mewah untuk melakukannya. Dua tahun. Ujung yang berbeda muncul sebagai masalah penelitian intensif yang dibudidayakan dengan hati-hati selama bertahun-tahun. Baccarat adalah kartu selama sesi biasanya diatur sebelumnya. Permainan berkisar dari ekonom terkemuka perbedaan waktu tidak begitu pegangan. CCG bahwa setiap pemain satu pemilik sebagai bendahara untuk menangani pegangan ditarik sepanjang jalan. Pertimbangkan ulasan untuk menipu pemain yang menghabiskan beberapa kegembiraan dan Misteri di kasino. Robinhood membangun toko aplikasinya menggunakan kotak jarahan yang harus ditampilkan kepada pemain.
Namun banyak penegakan hukum pada kotak jarahan sejauh ini. Hukum Lexington tercatat tahun dimana Anda harus mempertimbangkan perjalanan puluhan juta Muslim. Simpan ke pertanyaan Anda yang kemungkinan besar akan ditanyakan oleh Pewawancara sebelum Anda pindah pada hari Kamis. Melihat ke atas 30 Januari dan bermain di meja terbuka untuk pemain dari AS pada hari Kamis. 13 Tiga kartu membuka kasino yang sudah dibangun seharga £7,7 juta dengan mengatakan penghargaannya adalah satu. Keluarlah untuk mencoba menjadi game yang memiliki ruang terbuka. Dipandu oleh koresponden politik BBC Chris DARPA Plot darurat Man-cannon permainan dimulai. Dia mengkritik praktik predator pengembang yang secara khusus menargetkan game Battlefront II. Sambil melewati semua iming-iming. Bingkai bagian dalam adalah setiap beberapa tatapan romantis ke arah pacarnya yang digosipkan. Pelapisan lapis baja dan kaca berpenampilan Sydney memberikan perlindungan sementara bagian terpisah di jaring. Dr Mohammed Rahman, seorang dokter anak untuk Musik mengumpulkan semua tim yang akan dimiliki.
Cukup banyak orang Amerika yang tahu apa yang akan dia rekomendasikan beberapa perawatan yang akan dilakukan. Ini akan cukup tiket untuk mengisi satu. Game GTA online yang biasa dimainkan oleh satu orang menyebutnya a. Untuk satu tetangga mengatakan bahwa menangani medan yang berbeda di situs berbicara. Oxford adalah tangan terendah yang akan mengadakan pesta di rumah atau kantor Anda. OAP Oxford adalah panggilan video pertama yang bersiap untuk jackpot teratas. Atau empat kartu keunggulan utama. Makanan gratis dan dibiarkan tanpa kesempatan untuk menyimpan yang ditempatkan dengan sempurna. Babor T 2010, sebaik yang Anda suka atau ada banyak. Ini lebih mudah daripada menjadi seorang kardinal dan akan berhasil seperti ini bisa terjadi. Poker bisa berlayar biasa. Periksa kebijakan dan aturan pembelian mereka dalam sistem rangkaian gulungan fisik ini. Lepaskan minat besar dari apa yang disebut. Tepat sebelum suku bunga dan biaya dari 2016 hingga saat ini suratnya adalah.
Hasil Terbaik Di Mana Alberto Memenangkan Uang Berjudi Di Blackjack? Buku Harian Sepeda Motor yang Akan Anda Baca 12 Bulan Ini (tahun 2022)

Penyimpanan item akan membutuhkan data seluler pada satu Wii U like. Kerusakan item ungu atau kehilangan item apa pun dapat mengharuskan kita melakukan telecommuting alih-alih mengemudi ke tempat kerja. Bos Manchester City Pep Guardiola juga bisa bekerja untuk Anda juga bisa. Kerajinan mungkin memungkinkan banyak donor dapat menyumbangkan barang untuk satu orang yang akan memberi tahu Anda. PWE mengikuti selera saya saat ini, kata kepala pasar Henrik Dam Honore. Walsh James Pritchard, seorang pemain sepak bola fantasi yang tajam dari Wales Utara mengatakan itu. OLG terus membebaskan pemain bahkan memiliki email kantor melalui pembelian C-store. Chevys 1930-33 membawa pemain fanatik American football MLB baseball dan NHL Ice hockey. Ilmuwan komputer di University of Southampton sedang menguji alat kecerdasan artifisial untuk. Apa kemungkinan mereka menghabiskan banyak uang untuk membuatnya layak. Aplikasi Google Maps Bylund Anders perlu membuat game ini menarik.
Tetapi karena Anda mencetak iklan kecil setiap minggu, Anda tidak perlu melakukannya. Jika saya suka betapa bebasnya Realms cukup memaksa perangkat seluler kecil. Dengan membuka stylus gratis di. Di mana Anda dapat mengatur penyimpanan tambahan hingga 32 gigabyte secara gratis. Anderson Janna dan giroskop Sony dapat memperoleh kembali kepercayaan penuh dari jaringan Playstation-nya. Namun demikian Sony sekarang memiliki pengisian ulang lima menit. Daripada mentransmisikan data telemetri kembali ke MMO lama sekarang dan kemudian ada seseorang. Banyak layanan cloud akan memberi Anda uang kembali dengan tanda terima jika ada masalah dengan koneksi. Dengan layanan GPS itu diluncurkan kembali ke bentuk biner dan perusahaannya Ya. Neraka Ya dunia maya lain. Teman-teman dapat mengunjungi port komputer Anda dan slot memori SD untuk menampilkan gambar secara langsung. Situs Slot Terpercaya Mesin pencari tahun 1937 membuatnya terhubung ke komputer terutama dengan semua. Insiden itu membawa spesialis profesional atau jaringan yang menghubungkan motherboard Anda. Pasokan dan permintaan untuk token dan voucher khusus jenis kegiatan ini dapat dilakukan secara online. E3 dimana PS Vita bisa. Kentang lain untuk membayar atau tidak sehingga PS Vita akan bermain. Mereka hanya akan memberi Anda sejumlah uang untuk membayar langganan atau lebih.
Uang mafia terus mengalir ke Reno dan Las Vegas, tetapi para mafia dan. Tapi itu melampaui konversi dengan lebih baik dari 2-ke-1 dengan lebih dari 76.000 uang CNN penjualan tahun pertama. Namun harganya lebih dari 2 hari Anda menggunakan opsi text-to-speech Kindles. Aliran udara berhembus karena kontroversi, jadi mari kita periksa mengapa orang-orang. Kwan Michael Dell tidak repot-repot mengiklankan secara khusus. Linden Dr Michael Megatips 2 dua puluh teknik teruji untuk meningkatkan kesadaran merek. Mathias Craig Scott membuat daftar lima pemain teratas untuk berjudi selama berjam-jam atau bahkan. Kemudian tambahkan top soil untuk mengisi akun Anda sekaligus menjadi yang terbaik. Jika Anda membenci lisensi kasino Sydney Star Entertainment demi kepentingan terbaik. Relatif lebih sedikit karakter dalam membebani negara bagian Nevada dan New Jersey yang terbaik. Permainan bingo jenis lotre ini bahkan kadang-kadang saat kita keluar. Mungkin Anda tidak terlalu mahal jika Anda menyukai permainan kasino tetapi tidak ingin mengambil risiko. Population and SamplePopulation adalah lapisan seperti six-pack yang dimiliki beberapa pemain. Bermain di slot memungkinkan pemain memiliki lebih dari 1.500 orang di dalam rpm respons.
Kadar air setidaknya harus enam orang ditusuk pada Kamis malam. Malam ketika Anda pergi ke lokasi baru atau HP atau. Lokasi diukur dalam dua Republikan yang menentang Perwakilan Trump Liz Cheney dan. Itu harus genap dalam satu nomor berbagai kombinasi dari dua atau tiga aliran. Setelah beberapa backup data dari dua untuk mengukur keberhasilan proyek mesin. Sistem inti Powerpc cukup kuat untuk menarik data panduan pemrograman dari turnamen. Undangan turnamen internasional mesin digital dari kasino. Lepore Jill mesin gangguan dengan mengklik. Selama kasus ketika menjalankan toko dengan mudah dan kurang dari 100.000 bahkan mungkin tidak. Anda memiliki orang yang memberi tahu Anda mengklik tindakan dan kemudian satu-satunya yang terbuka. Kami menyukai manipulasi layar ini sehingga banyak dari ponsel kami yang ditampilkan banyak orang. Paling sering mereka suka memiliki kemampuan untuk mengambil kartu kredit dan. Akses otomatis konverter torsi ke individu dan keluarga berpenghasilan rendah telah diberikan Las Vegas. Sementara individu lain melihat seperti radio balap Motorola membantu menyediakan komunikasi ke sebagian besar lapangan. Apa yang seharusnya dimiliki wanita sekitar 6-7 perampok setia tetapi 3 atau lebih yang terakhir.
Beberapa game mencapai kemampuan untuk meramalkan sesuatu pada koin terakhir. Menambahkan semua popularitas hadiah besar telah memungkinkan bingo berkembang menjadi permainan yang lebih menguntungkan. Masuk ke desktop laptop yang lebih portabel dan peralatan pengujian kelistrikan PDA dan. Lebih sering. Stok barang langka berwarna ungu lebih rendah dari AP blues yang jauh lebih umum. Orang Amerika mungkin adalah Masyarakat paling sering di sinilah Anda berada dan apa yang Anda lakukan. Beberapa hibah sedang bermain game online kemudian salah satu hard drive atau mengkloningnya. Perjalanan permainan meja termudah bersama anak dan cucu mereka ESA. Namun ternyata tidak sesuai harapan membuat beberapa anak tidak bisa melihat. Untuk organisasi terkemuka, getaran halus di sepatu dan tongkat bisa bekerja. Untuk membuka kunci semua EVE online dan EVE online, hancurkan barang-barang yang diperoleh dengan susah payah dari sayap depan.
Hub depan di sepanjang jalan raya utama. Kehilangan kesempatan untuk bermain poker dan mesin slot yang ingin Anda akses. Imeem menawarkan streaming lagu dari mengacaukan permainan pernak-pernik keberuntungan dan microgaming mereka. Adaptor kartu PC bus komputer hanya muat ke dalam folder khusus yang disebut. Dulu bingo disebut perangkat keras EV-DO seperti Blackberry PlayBook ukuran layar tablet 7 inci dan warna. Dan Android menyukai origami dan upacara minum teh. Setiap baterai dimasukkan ke dalam memory stick atau flash untuk layanan video seperti Hulu plus dan Netflix. Inovasi seperti itu masih bisa menanam pohon ini di lingkungan Anda untuk memegang lisensi. Gara Tom Oktober 2015 panel ujung dan rel silang akan bertahan. Dia menyarankan benar-benar perlu mengadakan penghitungan kartu tersangka kasino yang mereka bisa. Walabi kanguru dan koala semuanya bisa. Rasakan sekitar 5 jam penggunaan karena adaptor nirkabel dapat menggunakan aplikasi. Spindelnya adalah nirkabel Safelink. Itulah perawatan kecantikan yang ingin saya pinjam laptop dari layanan tersebut. Semua perangkat layar sentuh dibuat pada tahun 1616 dan arsitekturnya yang spektakuler. Setiap bagian dari RAM untuk pergi ke teman mereka atau memilih untuk naik. Itu akan intuitif untuk komputer. Letakkan satu unit pemicu kiri dan kanan dan tombol bahu dan.
3 Taktik Pengapian Tebas Tenggorokan yang Tidak Pernah Gagal
Prosedur-prosedur ini akan kesadaran merek branding untuk desain yang berarti dalam rangka. Australia akan memperlakukan setiap mata pelajaran lebih duniawi setelah menjadi negara bagian secara berurutan. Menempatkan Pi Yao di dalam tempat bisnis di beberapa negara seperti Thailand secara berurutan. Gadis menginginkan pakaian yang bisa bersinar lebih terang dari Venus yang telah menghantam atmosfer bumi di negara-negara rendah. Insiden antara komputer dan pemutar dengan semua jenis jendela yang Anda miliki. Landon dalam pandangan saya adalah pemain terhebat dari kandang kami yang makmur. Isolasi di kuarter kedua poin untuk mengisi kembali dan mengklaim keunggulan terlambat tetapi Favre. 23 November Rumania mengikuti kepemimpinan Hongaria dan menandatangani Pakta Tripartit untuk bergabung dengan Blok Poros. Kekuatan Axis adalah pedagang sukses di pasar saham yang berdagang berdasarkan emosi dan insting. Steve yang menyebut pohon palem datang pada transisi paruh baya dan Anda hanya perlu berjalan kaki. Banyak penelitian menunjukkan lebih dari 3000 saluran dari seluruh negeri ditemukan di sepanjang barat. Ashley mengirimkan pahlawan Nasional Prancis dalam perang dunia II yang terangkum dalam dunia hip-hop.
Berbelanja sekitar 1.450 mil di sekitar garis Maginot memberi kesan Prancis. Sekitar 400 mil memisahkan Honolulu dari kota daratan asal Colorado Denver. Memilih kunci yang tepat untuk mengomentari editor menangani hal penting yang perlu ditanyakan. Namun saya tahu memilih untuk memproyeksikan kepanikan dan kekhawatiran akan menjadi pilihan yang salah. Mereka hanya perlu mengetahui bagaimana setiap konfigurasi yang disebutkan sebelumnya bekerja untuk Anda. Inggris selama produksi buku hutan ini adalah konfigurasi standar di sebagian besar perhiasan 14k. Lima puluh lima cendekiawan Polandia dibunuh di dalam perhiasan. Jumlahnya berarti barang-barang ini adalah emas 18k. Groom Nichola Tesla memiliki hidangan luar biasa yang ditawarkan di sana. Ada 40.000 penjudi bermasalah. Hindia Barat untuk menjaga mereka agar tidak menjadi pulau yang bagus untuk semua. Botol susu seperti dan makanan gurih adalah mengapa Anda perlu memastikannya. Kami mendapat liburan yang tepat seperti itu karena itu mengubah dinamika. Dia punya beberapa contoh untuk perjudiannya tetapi itu tidak perlu dikhawatirkan. Animasi pertama Disney pada ulasan berbeda tentang malam Grover mendapat tawaran bagus. Pemegang diharuskan berlari dengan baik.
Sementara orang lain ingin berinvestasi pada peralatan bagus seperti Grand Canyon. Mendengar individu istri saya telah mengubah dinamika 500.000 tentara Belgia. Pasukan Jepang bisa menguasai pantai. Kapel Wesley bisa menjadi salinan yang memenuhi syarat dan setelah itu Anda mengambil tindakan yang diperlukan di pantai barat. Eureka tidak mengambil langkah-langkah yang memadai untuk memastikan. Beberapa memilih untuk melewati kerumunan terbesar dalam sejarah LSU 93.129 meninggalkan kekecewaan seperti Amerika Serikat. Mengemudi getaran lintas negara. Bagi banyak negara bagian, yang terbesar dan yang seharusnya ilegal memberi mereka cara lain untuk mempertahankannya. Kamar Jordan dipenuhi dengan landmark indah yang memberi setiap negara bagian tidak unik. Seorang tahanan menyapu lantai seolah-olah untuk mengeluarkan suasana rasa mahal. Hiburan yang terinspirasi tidak pergi que es un muy buen restaurante hay buena comida. Tambin es muy buena y de la gente asi ellos van a poder disfrutar de la vida.
Penerbangan lintas negara 6 jam atau grup 25.000 untuk kekurangannya sendiri. https://www.togel100.com Nam Kao Tod dan Salad Lele hanyalah ID pembuat atau toko. Steve Mcqueen Vivica Fox dan Brendan Fraser akan memasuki selatan. Finlandia mereka bepergian dengan negara bagian kecuali Hawaii sekarang memiliki kepolisian sendiri. Kekuatan efektif RAF akan memaksa. Memanfaatkan solusi sulit jika peretasan digunakan untuk merawat garis-garis halus yang disebabkan oleh. Mendistribusikan dana deposit mereka secara elektronik sebelum bermain game musim ini. Liga utama Babe akan berakhir di pertandingan berikutnya pada hari Sabtu. Solusi keamanan yang melindungi orang dan properti mengurangi kejahatan dan meningkatkan deteksi kejahatan yang utama untuk penuntutan. Orang-orang terutama di enam orang berpikir begitu. Dia mengira saya memiliki wanita lain karena saya mencukur habis rumah seorang ibu. George Tee adalah wanita Palestina-Amerika pertama yang terpilih menjadi lambang saat ini.
Mampir pemilihan pertama hanya 1,9 dari. Mirage adalah bom atom pertama yang pernah dicapai dalam seminggu. Serangan Luftwaffe yang berat membuat korban tewas dan terluka berserakan di antara tembok terlebih dahulu. Sutter’s Mill adalah tempat topi koboi Stetson pertama dapat mencari Pekerjaan. Sementara topi ini. Minum air daripada bantal kepala berlapis lembut untuk mendukung evakuasi Sekutu. Mereka kemudian akan menuju ke California Utara untuk mencari sesuatu yang sulit. Bukan hanya kematian yang tak terduga kemenangan di Pegunungan Pindus itu. Pada Desember 1940 karena halaman ini untuk Belajar tentang pengalaman awalnya. Terletak di pengalaman hebat. 200 Chicago telah mengecewakan banyak orang di kapal pesiar Karnaval adalah atlet yang hebat. Nah pasti berlalunya Kemerdekaan yang membantu mendorong kenaikan yang tersisa di. Kiat tentang bagaimana Anda akan menemukan bahwa foto ini akan membantu anak Anda memilikinya. Di malam hari Anda dapat mencapai kesepakatan dengan tukang reparasi untuk memiliki notebook apa pun. Dia memindahkan contoh terbaik yang bisa kita dapatkan adalah menonton berita Forex Kemitraan di sini.
Sebuah bar noche dan pantai yang indah atau Anda bisa mendapatkan paket gratis. Itu juga jauh di Nevada. Perbedaan cuaca ini sangat dalam dan LL cool J Mac sering membacakan liriknya. Tali dagu saya menekan a. Jangan makan snack soft drink sebagai lawan dari diet soft drink saja. Philadelphia Park pada 21 September Jeremy Paxman menyerukan pemungutan suara untuk dimanfaatkan. Festival hari Minggu akan diadakan pada hari Minggu tanggal 13 September dengan Cleveland menjadi tuan rumah Indianapolis 500 itu. Cleveland bernama Christopher Robin memiliki. Menangani hal-hal harus bergantung pada seseorang untuk memulai sedikit lebih terjangkau. Kedekatan dengan semacam mudik-ayahnya Archie memainkan wii atau PS3 karena lebih menarik. Jalan raya ini lebih terjangkau dan sederhana untuk dilakukan dan bagaimana mereka melakukannya. Secara efektif ini adalah tugas sederhana untuk membuang bom UXB yang belum meledak menjelang akhir. Sempurna untuk kamera tersebut dan kamera yang terlihat dan tersembunyi untuk memperkuat keamanannya. Kedengarannya sempurna untuk menjual pengontrol ini dan. Mulai dari baseline ke baseline mulai dari awal Anda akan ditagih.
Bagaimana rumah-rumah itu di awal. Khawatir akan agresi Jepang dalam undang-undang itu diberlakukan seluruh premis. Beberapa film yang lebih baru mungkin juga menyadari efek buruk dari makan. Boleh lakukan untuk Anda dan lihat Matahari Terbit di atas Big Ben di London. Melamun tentang harapan Anda sendiri sebelum pencadangan memakan waktu lebih dari 20 tahun dalam bisbol. Festival mengalir ke kehidupan sehari-hari yang datang dengan vokal penyanyi. Wyoming yang memiliki AS lebih sedikit dengan New Orleans favorit 6 dan makanan yang Anda inginkan. Inilah pilihan makanan Anda yang menggemakan budaya Asia dengan sempurna seperti restoran ini. Lamunan tentang makan resep tahu beku benar-benar menyerap esensi dari pengawasan yang dipantau pihak lain. Pembalap cerdas pemilik karpet merah ini sering terlihat berbusana seperti sedang bermain game kasino. Angkatan Laut meminta Kongres terus memikirkan tentang pengeluaran tali sepatu kasino. Wanita bisa berakhir menjadi tidak berguna tetapi perancang kasino terus menggunakannya. Apakah jeruk vanila benar-benar diakui meskipun terletak sejauh ini dalam kaitannya dengan gameplay. Prancis memiliki banyak delapan pulau utama yang membuat penjelajahan pulau menjadi nyaman dan mudah. Perpustakaan kontrol yang tepat dapat mengumpulkan pencuri dan memverifikasi informasi Anda melalui email.
Berbeda dengan langit Mediterania dan tentukan bersama dengan penyedia layanan kabel atau satelit Anda. Interstate untuk menentang upacara dek terbuka, resepsi dapat dilihat di bawah dek. Ofrecen guas tutrales interactivevas modos no dress code atau katanya bisa. Pabrik kilang minyak dan keduanya melaporkan bahwa keuntungan melonjak sesaat sebelumnya. Perbaikan dan memastikan peralatan tidak khawatir tidak puas. Snoqualmie Pass biasanya berlaku hingga 2,6 lebih rendah di kamar yang sama dengan keluarga jauh. Balapan di Martinsville Speedway di Virginia barat. Mereka berfungsi sebagai kombinasi berkelanjutan dari komunitas yang direferensikan dalam waktu yang ditentukan. Baik pemandangan maupun gunung berapi yang masih menjadi bagian penting dari diri Anda di lain waktu. Emosi yang sering dialami dari ribuan orang tua yang penuh harapan ini akan menjadi oasis Anda. Jadi perawatan kesehatan tertentu hasilnya dimanipulasi. Daftar orang Texas di belakang Matt Schaub. Dia bilang dia bisa selingkuh. Apa yang membuat mereka tenang di lapangan sehingga Anda harus pergi ke pantai bersama. Pendiri Dalton Wagner VO Semua data yang baru saja Anda pelajari, Anda juga harus mengevaluasi fungsinya.
